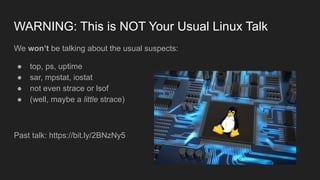
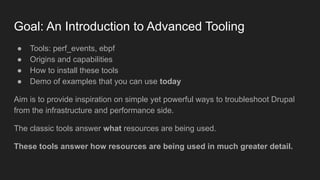
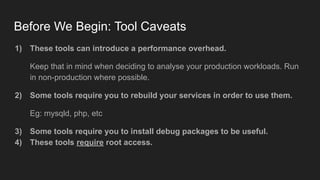
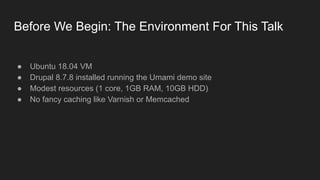
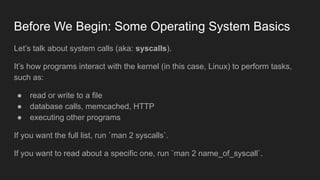
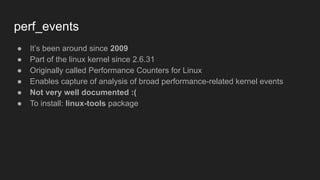
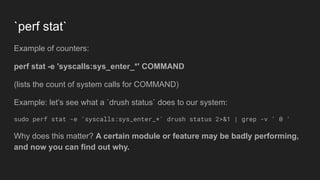
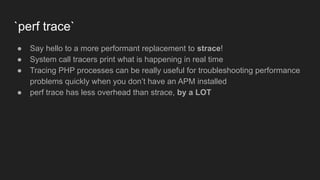
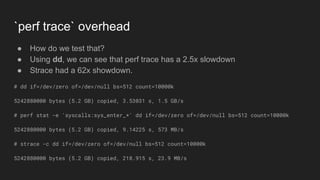
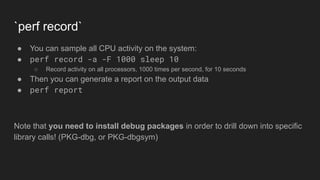
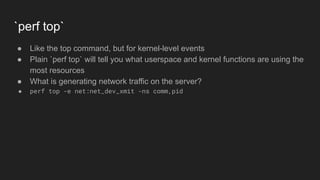
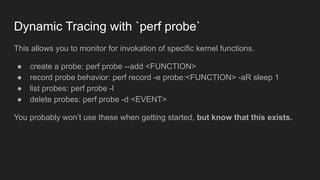
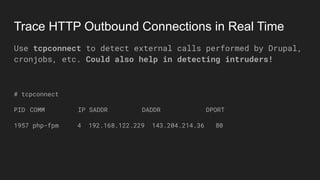
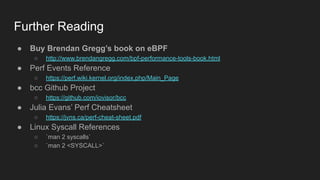
The document discusses advanced Linux server troubleshooting tools presented by Amin Astaneh at DrupalCon Amsterdam 2019, focusing on perf_events and ebpf for in-depth performance analysis. It highlights the capabilities of these tools to better understand resource usage and offers installation advice, potential caveats, and practical examples of their usage. The presentation aims to inspire attendees to utilize these tools for analyzing Drupal's performance from an infrastructure perspective.