REST – Beyond the hype
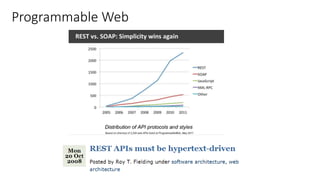
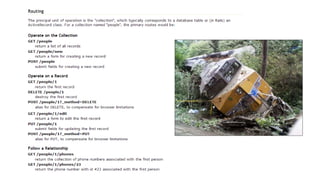
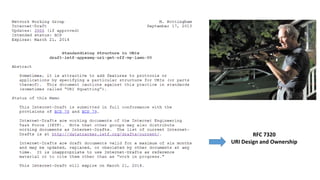
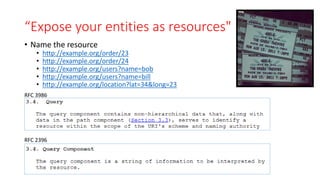
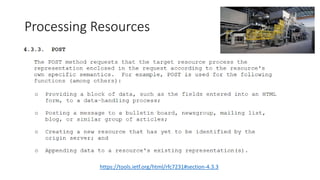
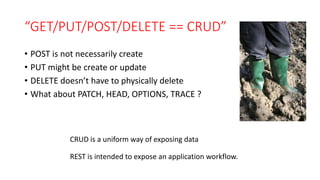
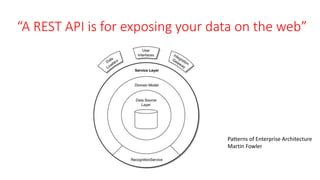
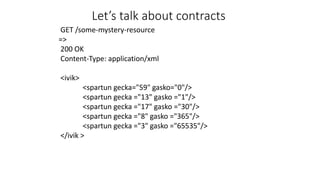
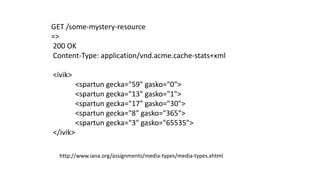
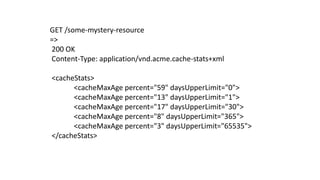
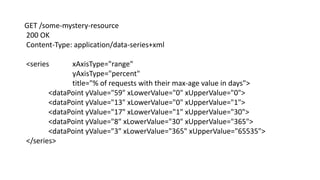
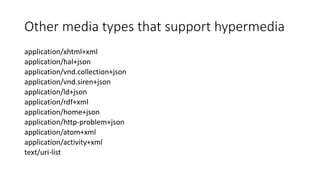
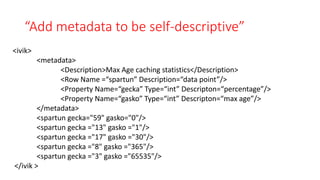
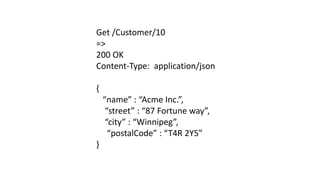
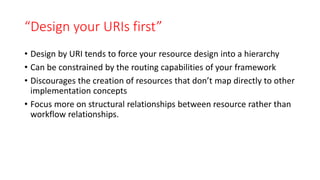
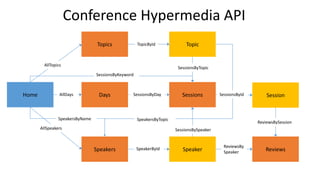
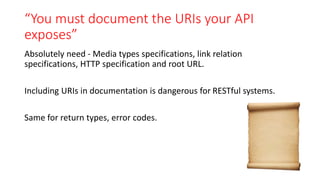
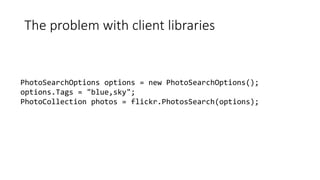
The document discusses REST and common misconceptions about RESTful API design. It begins with a brief history of REST and considerations of alternatives like SOAP. It then addresses how the rise of frameworks led to prescriptive but incorrect "rules" for REST. The bulk of the document dispels common myths and "lies" told about RESTful design, focusing on proper use of URIs, resources, media types, and use of hypermedia. It emphasizes that REST is an architectural style and not a rigid set of rules.