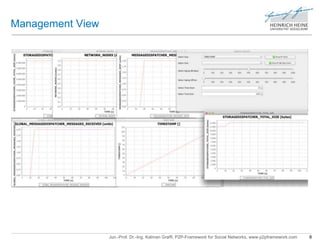
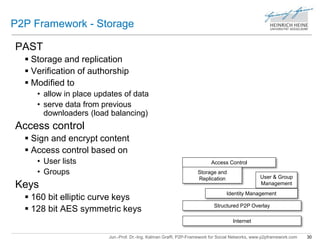
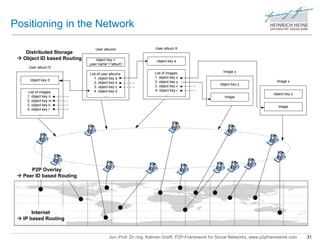
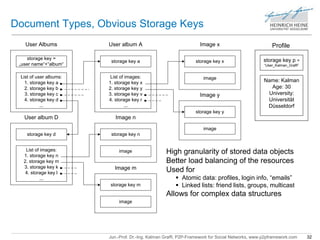
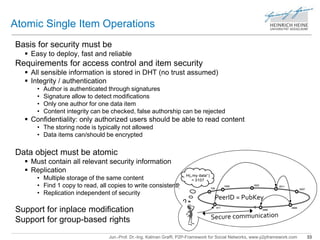
The document outlines the p2p framework for social networks developed by Jun.-Prof. Dr.-Ing. Kalman Graffi, focusing on building a secure, user-centric online social network platform. It highlights the platform's functionalities including user interaction, modular design through plugins, and security measures like encrypted communication and access control. The framework aims to combine research innovation with practical applications to improve peer-to-peer interaction and data management in social networking settings.
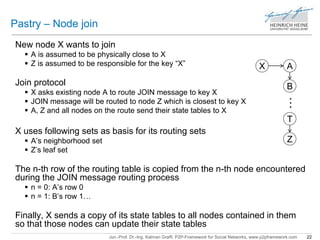
![Replication Extension of Pastry: PAST
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 34
Idea
Store objects also on k further nodes in leaf set
Remember Key-based Routing (KBR):
• nodehandle [] replicaSet (key k, int max rank)
– Returns an ordered set of peers of magnitude (max rank)
on which replicas of the object with key k can be stored
– The nodes which become roots for the key k when the local node fails
• update(nodehandle n, bool joined)
– Upcall: informs that node n has either joined or left the local neighbor set
If responsible peer fails
• New responsible node (is in replicaSet)
– Is informed of peer leave by update upcall
– Answers to lookups for new objects it is responsible for
– Calls new replicaSet and deployes replicas (if needed)](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-34-320.jpg)
![Example of Distributed Access Control
SharedItem
objectID Header
Privileged users
Payload
Signed CryptedItem
objectID Key list
userID A – key A
userID B – key B
userID C – key C
…
3
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 40
Byte array
containing
encrypted
SharedItem
Symmetric Key
Pub
User A
Encrpyted
with
Symmetric Key
Pub
User B
Encrpyted
with
Pub
User A
Pub
User B
[userID A] =
[userID B] =
1
extract
Serialized and encrypted with
symmetic key
2
userIDs
are public
keys
wrap symmetric key
with public key
4
5
Signature](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-40-320.jpg)
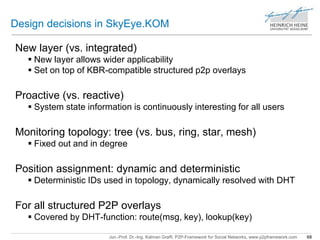
![Reliable structured p2p overlay
“Key-based Routing” – operations
• boolean isMyKey(Key K)
• void route(key K, Message M, node hint)
Building a tree topology
Introduce new overlay layer
• With own ID space ([0,1[)
Create tree topology in new overlay
• Using routing of p2p structured overlay
Concept of new layer
Decouples from specific p2p overlay
Unified ID space [0,1]
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 69
Assumptions](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-69-320.jpg)
![Example: Test 3 – Results
Amount of Nodes Available and Used Storage
60000
50000
40000
30000
20000
10000
Storage Dispatcher Size
Used Storage
Available Storage
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 76
125
100
75
50
25
0
Nodes
Global network nodes
0 60 120 180 240
Nodes
Time [m]
0
0 60 120 180 240
Data [MB]
Time [m]](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-76-320.jpg)
![Example: Test 3 – Results
Load – Messages Load – StorageItems
Social Network Load - Messages
25000
20000
15000
10000
5000
Social Network Load - StorageItems
Groups created
Photo albums created
Photos uploaded
Login items created
Profiles created
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 77
14000
12000
10000
8000
6000
4000
2000
0
Group Messages sent
Wall Posts sent
Wall Comments sent
Friend Requests sent
0 60 120 180 240
Units
Time [m]
0
0 60 120 180 240
Units
Time [m]](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-77-320.jpg)
![Example: Test 3 – Results
Photos Plugin Wall Plugin
12000
10000
8000
6000
4000
2000
Wall Plugin
Wall posts send
Wall posts commented
Walls requested
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 78
90000
80000
70000
60000
50000
40000
30000
20000
10000
0
Photos Plugin
0 60 120 180 240
Units
Time [m]
Albums created
Photos uploaded
Albums stored
Photos stored
0
0 60 120 180 240
Units
Time [m]](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-78-320.jpg)
![Example: Test 3 – Results
Groups Plugin Login Plugin
700
600
500
400
300
200
100
Login Plugin
Login Items created
Login Items stored
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 79
14000
12000
10000
8000
6000
4000
2000
0
Groups Plugin
Groups Items created
Group Items stored
Group Messages sent
0 60 120 180 240
Units
Time [m]
0
0 60 120 180 240
Units
Time [m]](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-79-320.jpg)
![Example: Test 3 – Results
Storage per Node Replication Count
Storage Used per Node
Maximum Storage Used per Node
Mean Storage Used per Node
Minimum Storage Used per Node
1e+06
100000
10000
1000
100
10
Replication Count
Overall Replications
Maximum Replications per Node
Mean Replications per Node
Minimum Replications per Node
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 80
600
500
400
300
200
100
0
0 60 120 180 240
Data [MB]
Time [m]
1
0 60 120 180 240
Units
Time [m]](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-80-320.jpg)
![Example: Test 3 – Results
Bandwidth – Messages Traffic
Bandwidth - Messaging
60
50
40
30
20
10
Bandwidth - Storage
Bandwidth - Data sent
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 81
2500
2000
1500
1000
500
0
Bandwidth - Messages sent
0 60 120 180 240
messages/sec
Time [m]
0
0 60 120 180 240
KB/sec
Time [m]](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-81-320.jpg)
![Example: Test 3 – Results
Amount of Errors Memory Usage
FreePastry Errors
900
800
700
600
500
400
300
200
100
Memory Usage
Maximum memory used by an instance
Mean memory used by an instance
Minimum memory used by an instance
Jun.-Prof. Dr.-Ing. Kalman Graffi, P2P-Framework for Social Networks, www.p2pframework.com 82
6000
5000
4000
3000
2000
1000
0
0 60 120 180 240
Errors
Time [m]
Pastry errors
Decryption errors
PAST errors
0
0 60 120 180 240
Memory [MB]
Time [m]](https://image.slidesharecdn.com/2013kalman-140910040238-phpapp01/85/LibreSocial-P2P-Framework-for-Social-Networks-Overview-82-320.jpg)