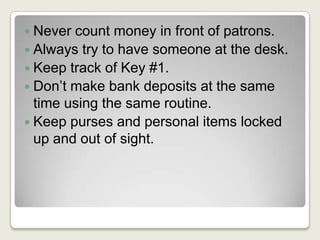
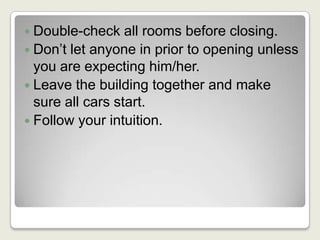
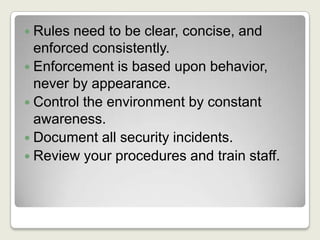
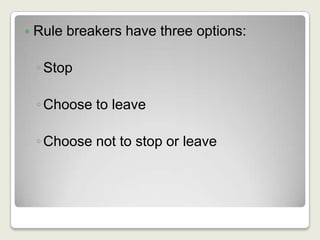
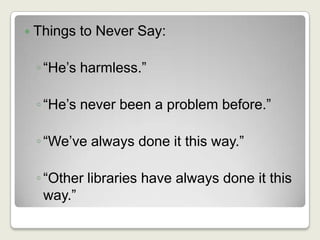
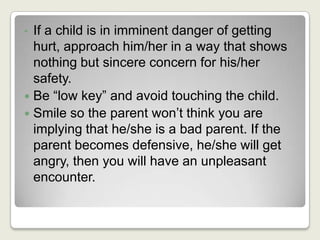
The document outlines essential safety and security practices for library staff, emphasizing awareness as the primary deterrent against incidents. It provides guidelines for handling various situations involving patrons, enforcing rules, and managing security breaches while maintaining a welcoming environment. Additionally, it highlights the importance of training staff and clear communication regarding behavioral expectations.