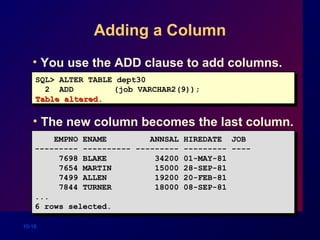
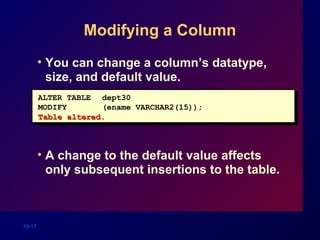
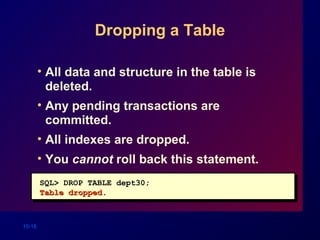
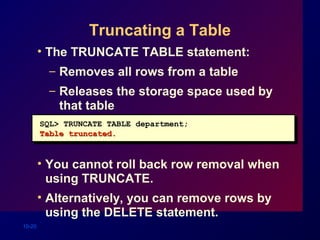
This document discusses how to create and manage database tables in Oracle. It describes how to create tables with columns of different data types, alter table definitions by adding or modifying columns, drop and rename tables, and add comments to tables. The key database objects like tables, views, indexes and sequences are also introduced. Common SQL statements used for managing tables like CREATE TABLE, ALTER TABLE, DROP TABLE, COMMENT and more are explained with examples.




![10-5
The CREATE TABLE Statement
• You must have :
– CREATE TABLE privilege
– A storage area
• You specify:
– Table name
– Column name, column datatype, and
column size
CREATE TABLE [schema.]table
(column datatype [DEFAULT expr][, ...]);](https://image.slidesharecdn.com/les10-130703010735-phpapp01/85/SQL-WORKSHOP-Lecture-10-5-320.jpg)





![10-12
Creating a Table
by Using a Subquery
• Create a table and insert rows by
combining the CREATE TABLE statement
and AS subquery option.
• Match the number of specified columns
to the number of subquery columns.
• Define columns with column names and
default values.
CREATE TABLE table
[(column, column...)]
AS subquery;](https://image.slidesharecdn.com/les10-130703010735-phpapp01/85/SQL-WORKSHOP-Lecture-10-12-320.jpg)

![10-14
The ALTER TABLE Statement
Use the ALTER TABLE statement to:Use the ALTER TABLE statement to:
• Add a new column
• Modify an existing column
• Define a default value for the new column
ALTER TABLE table
ADD (column datatype [DEFAULT expr]
[, column datatype]...);
ALTER TABLE table
MODIFY (column datatype [DEFAULT expr]
[, column datatype]...);](https://image.slidesharecdn.com/les10-130703010735-phpapp01/85/SQL-WORKSHOP-Lecture-10-14-320.jpg)