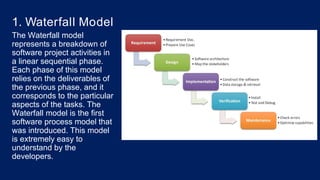
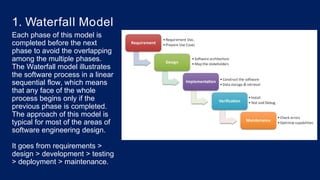
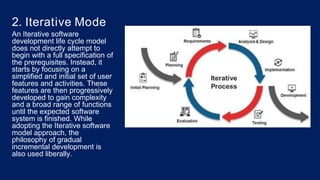
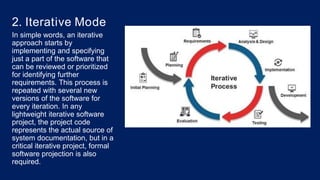
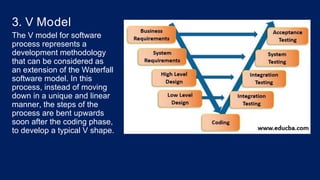
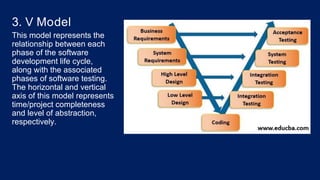
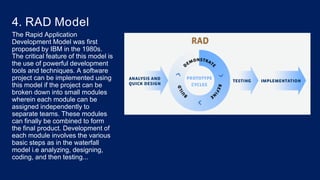
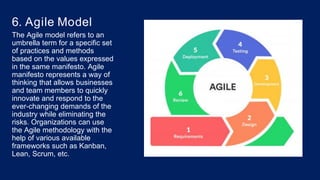
The document discusses different software process models used in software development. It describes the waterfall model as a linear sequential process moving from requirements to design to development and so on. The iterative model develops software incrementally in iterations to add more features. The V model maps each development phase to a testing phase. Other models discussed include RAD, spiral and agile models.