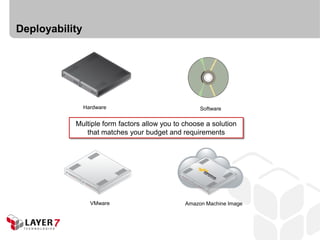
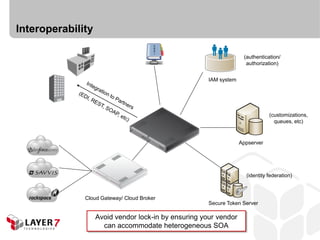
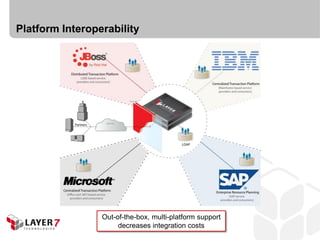
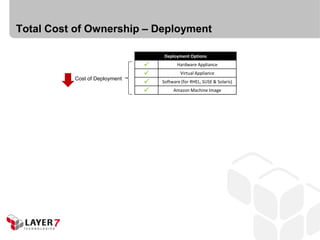
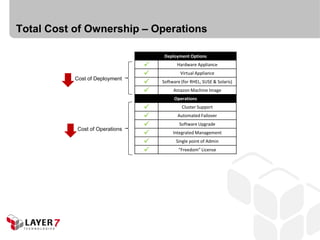
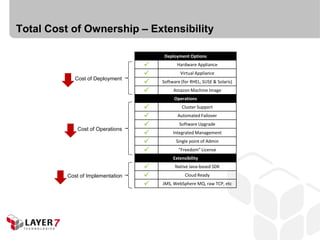
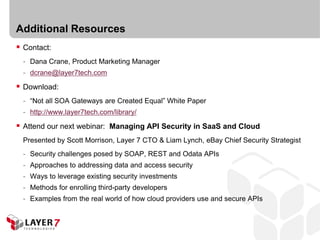
The document discusses considerations for selecting a Service-Oriented Architecture (SOA) gateway, highlighting key functionalities such as deployability, interoperability, extensibility, and manageability. It details various use cases and the importance of avoiding vendor lock-in, while emphasizing total cost of ownership related to deployment and operations. Additional resources are provided for further insights into SOA gateways and API management.

![SOA Gateway Use Cases
SOA
- Runtime governance (security, policy enforcement and lifecycle management)
- Enterprise application integration
- Sharing sensitive information between businesses/governments
- Business rule enforcement (such as SLAs; contract-defined limits [# of downloads/day])
Web
- API management
Cloud
- Identity federation (including SSO to SaaS applications)
- Integrating enterprise applications with cloud-based services](https://image.slidesharecdn.com/howtobuyasoagateway-110223182058-phpapp02/85/How-to-Choose-A-SOA-Gateway-from-Layer-7-4-320.jpg)