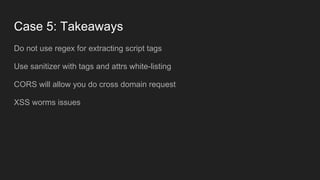
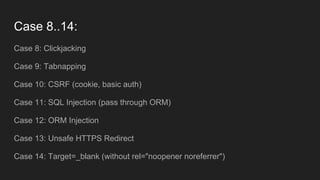
Viktor Turskyi discusses the importance of information security in software development, highlighting the risks often underestimated by businesses. He emphasizes practical cases, JavaScript demos, and real-life applications rather than theoretical tools or reports. Turskyi believes that understanding security enhances a developer's skills and makes the work enjoyable.