Report
Share
Download to read offline
Recommended
KeyLoggers - beating the shit out of keyboard since quite a long time

KeyLoggers - beating the shit out of keyboard since quite a long timen|u - The Open Security Community
Recommended
KeyLoggers - beating the shit out of keyboard since quite a long time

KeyLoggers - beating the shit out of keyboard since quite a long timen|u - The Open Security Community
More Related Content
What's hot (19)
Ransomware- What you need to know to Safeguard your Data

Ransomware- What you need to know to Safeguard your Data
Viewers also liked
Viewers also liked (6)
Similar to Keyboard collector
Similar to Keyboard collector (20)
Is data secure on the password protected blackberry device

Is data secure on the password protected blackberry device
Recently uploaded
Recently uploaded (20)
Swan(sea) Song – personal research during my six years at Swansea ... and bey...

Swan(sea) Song – personal research during my six years at Swansea ... and bey...
Enhancing Worker Digital Experience: A Hands-on Workshop for Partners

Enhancing Worker Digital Experience: A Hands-on Workshop for Partners
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi

FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
The Codex of Business Writing Software for Real-World Solutions 2.pptx

The Codex of Business Writing Software for Real-World Solutions 2.pptx
Azure Monitor & Application Insight to monitor Infrastructure & Application

Azure Monitor & Application Insight to monitor Infrastructure & Application
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Keyboard collector
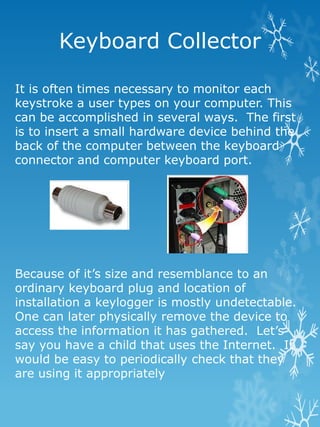
- 1. Keyboard Collector It is often times necessary to monitor each keystroke a user types on your computer. This can be accomplished in several ways. The first is to insert a small hardware device behind the back of the computer between the keyboard connector and computer keyboard port. Because of it’s size and resemblance to an ordinary keyboard plug and location of installation a keylogger is mostly undetectable. One can later physically remove the device to access the information it has gathered. Let’s say you have a child that uses the Internet. It would be easy to periodically check that they are using it appropriately
- 2. Children need to know that the Internet is a very public place and once you write it, there is a record. Keystrokes are saved as text. Another example would be an employer that needs to know what’s going on when they aren’t present. Worst case scenario is an attacker that sneaks one in and out and now has access to your bank accounts, credit card numbers, etc.. The second kind of keylogger, software keyloggers, are programs that are downloaded. Often times a software keylogger is unknowingly downloaded and installed as a Trojan or by a virus. As shown below a software keylogger silently records all keystrokes, including passwords and sensitive information like a hardware keylogger.
- 3. This information can be secretly transmitted to a remote location, it is not necessary to physical access a user’s computer. Keyloggers also hide themselves so that a user cannot easily detect them, Windows task manager won't show a keylogger running. From a practical sense, having a keylogger in place, troubleshooting a failure on a computer might be easier if you have detailed information on what the user did immediately prior to the situation.