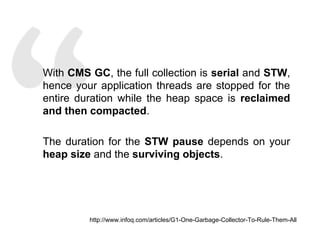
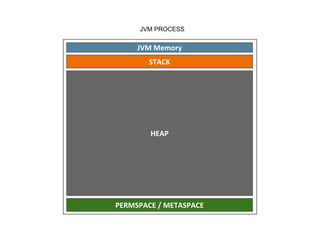
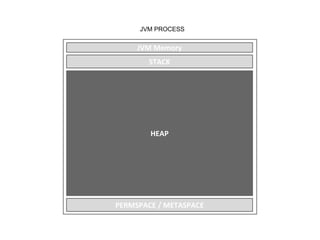
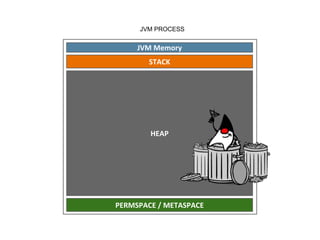
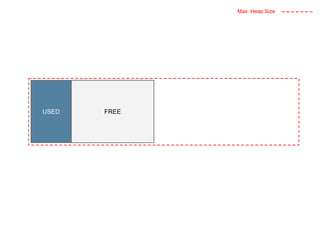
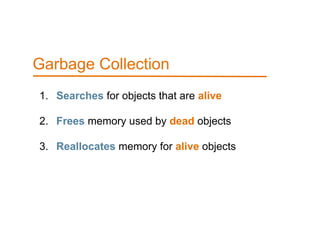
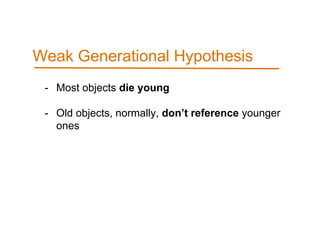
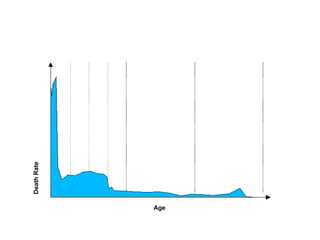
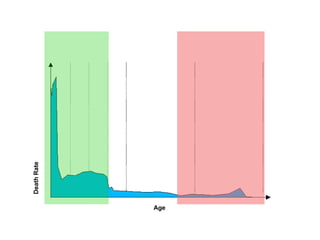
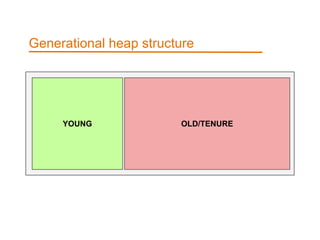
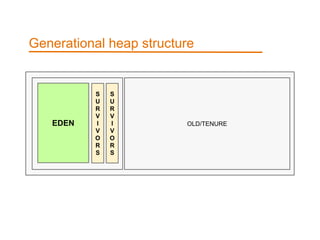
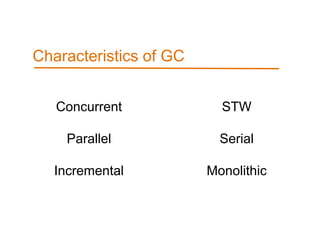
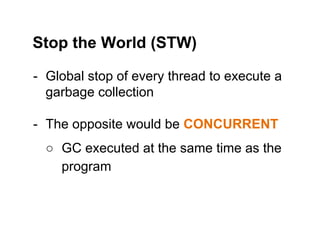
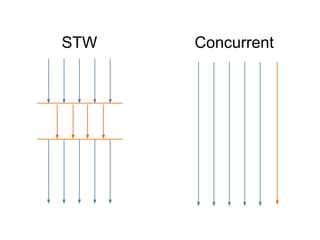
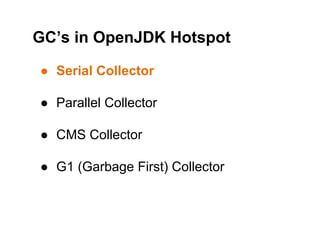
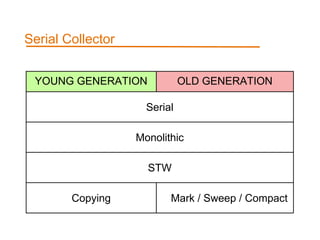
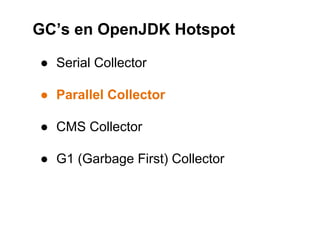
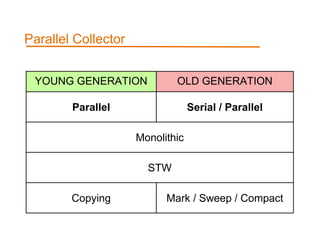
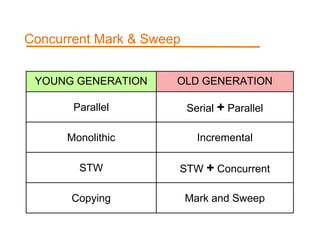
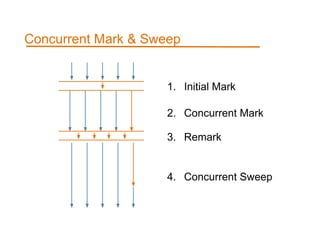
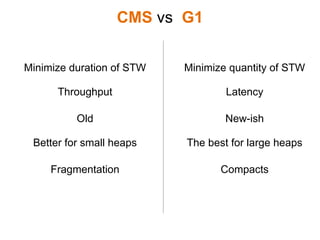
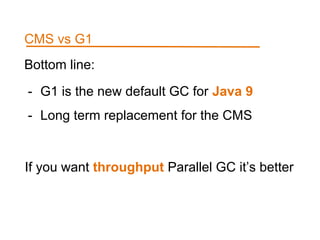
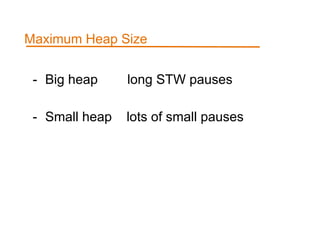
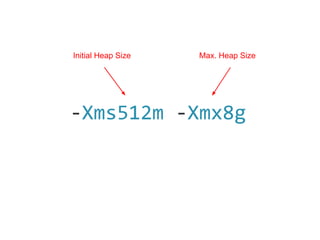
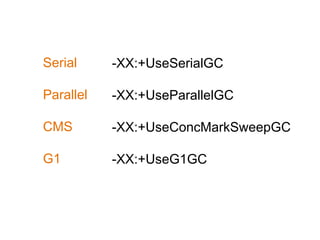
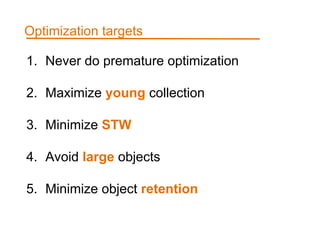
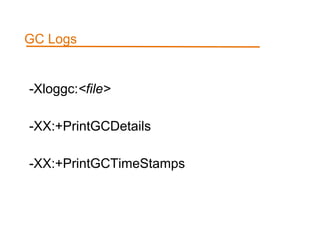
The document discusses garbage collection in Java, covering exceptions like OutOfMemoryError and various types of garbage collectors (e.g., CMS, G1). It explains the structure of the JVM's memory, the generational hypothesis, and characteristics of different collectors. Additionally, it provides configuration options and optimization strategies for managing memory efficiently in Java applications.















![[GC [PSYoungGen: 578424K->8793K(630784K)]
1007570K->444386K(1155072K), 0.0185270 secs]
[Times: user=0.06 sys=0.00, real=0.02 secs]
[GC [PSYoungGen: 580697K->15128K(636928K)]
1016290K->459169K(1161216K), 0.0236090 secs]
[Times: user=0.08 sys=0.01, real=0.02 secs]
[GC [PSYoungGen: 450179K->6893K(635904K)]
894221K->465458K(1160192K), 0.0249430 secs]
[Times: user=0.07 sys=0.02, real=0.02 secs]
[Full GC [PSYoungGen: 6893K->0K(635904K)]
[ParOldGen: 458564K->454236K(816128K)] 465458K->454236K(1452032K)
[PSPermGen: 171991K->171852K(344064K)], 2.5341620 secs]
[Times: user=8.48 sys=0.01, real=2.53 secs]](https://image.slidesharecdn.com/jbcn2016garbagecollectors-wtf-1-160618101430/85/Jbcn-2016-Garbage-Collectors-WTF-127-320.jpg)
![[GC [PSYoungGen: 578424K->8793K(630784K)]
1007570K->444386K(1155072K), 0.0185270 secs]
[Times: user=0.06 sys=0.00, real=0.02 secs]
[GC [PSYoungGen: 580697K->15128K(636928K)]
1016290K->459169K(1161216K), 0.0236090 secs]
[Times: user=0.08 sys=0.01, real=0.02 secs]
[GC [PSYoungGen: 450179K->6893K(635904K)]
894221K->465458K(1160192K), 0.0249430 secs]
[Times: user=0.07 sys=0.02, real=0.02 secs]
[Full GC [PSYoungGen: 6893K->0K(635904K)]
[ParOldGen: 458564K->454236K(816128K)] 465458K->454236K(1452032K)
[PSPermGen: 171991K->171852K(344064K)], 2.5341620 secs]
[Times: user=8.48 sys=0.01, real=2.53 secs]
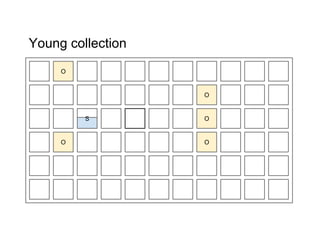
Young Generation collection
Full GC (STW)](https://image.slidesharecdn.com/jbcn2016garbagecollectors-wtf-1-160618101430/85/Jbcn-2016-Garbage-Collectors-WTF-128-320.jpg)