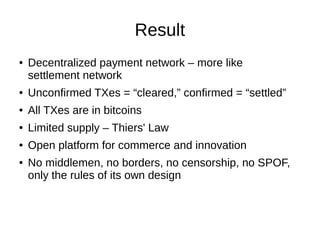
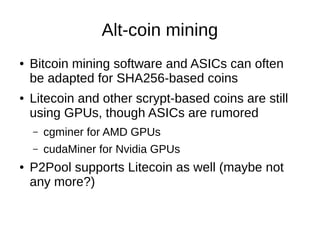
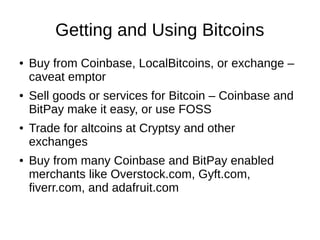
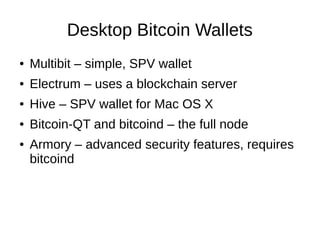
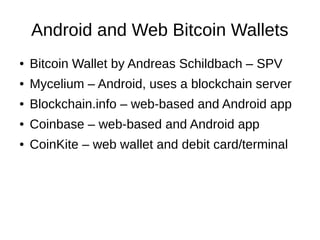
The document discusses decentralized digital currencies, focusing on Bitcoin and its underlying technology, including concepts like public ledgers, blockchain, and peer-to-peer networks. It covers the mechanics of transactions, mining, and the significance of decentralization in providing a secure and private payment network. Additionally, it touches on altcoins, mining practices, and different wallet options for handling cryptocurrencies.
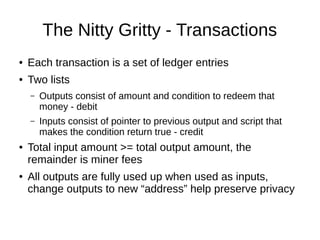
![Transaction Diagram
By Matthäus Wander (Own work) [CC-BY-SA-3.0 (http://creativecommons.org/licenses/bysa/3.0)], via Wikimedia Commons
http://commons.wikimedia.org/wiki/File%3ABitcoin_Transaction_Inputs_and_Outputs.png](https://image.slidesharecdn.com/bitcoin-fredericksburglug-140224124756-phpapp02/85/Fredericksburg-LUG-Bitcoin-slides-6-320.jpg)
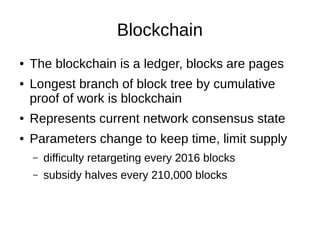
![Blockchain Diagram
By Matthäus Wander (Own work) [CC-BY-SA-3.0 (http://creativecommons.org/licenses/bysa/3.0)], via Wikimedia Commons
http://commons.wikimedia.org/wiki/File%3ABitcoin_Block_Data.svg](https://image.slidesharecdn.com/bitcoin-fredericksburglug-140224124756-phpapp02/85/Fredericksburg-LUG-Bitcoin-slides-9-320.jpg)