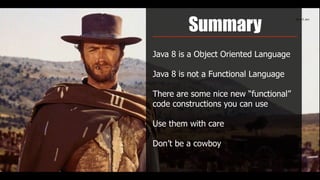
This document provides an overview and summary of key features in Java 8, including:
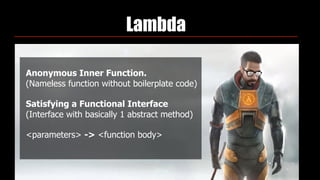
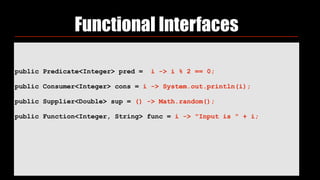
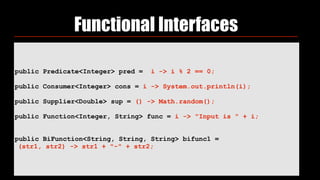
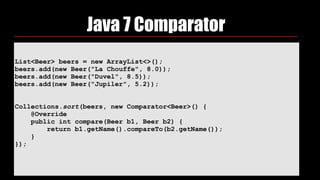
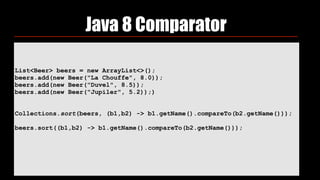
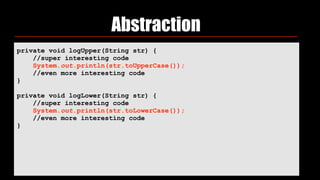
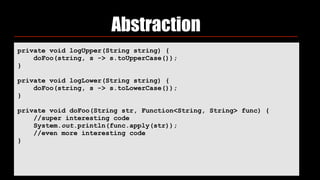
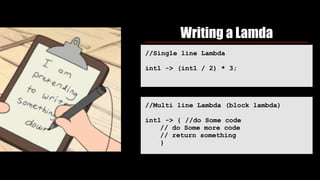
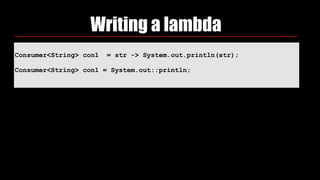
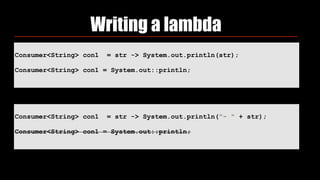
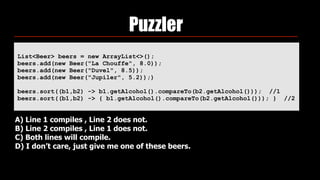
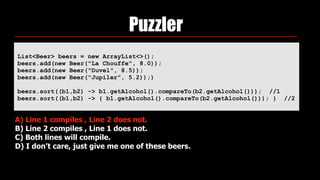
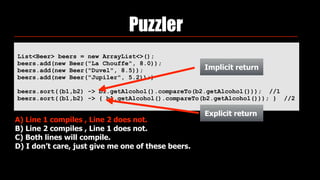
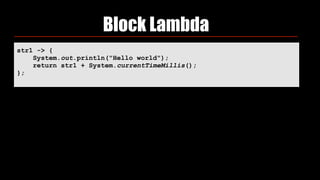
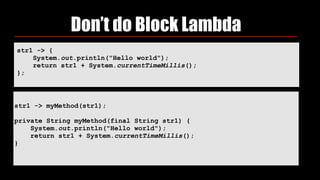
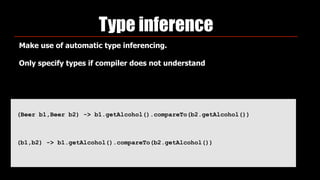
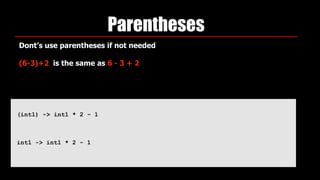
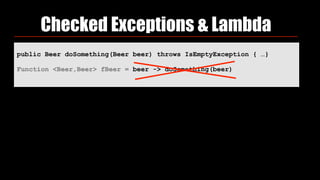
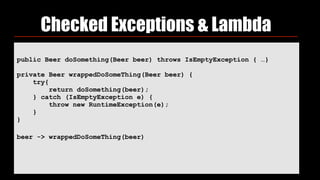
- Lambda expressions which allow implementation of functional interfaces in a more concise way
- Default methods which allow extension of interfaces without breaking existing implementations
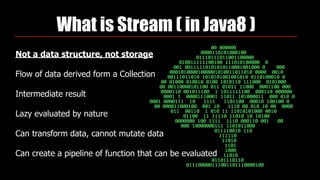
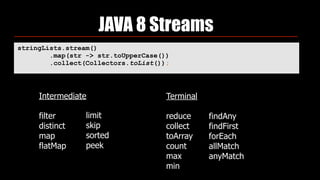
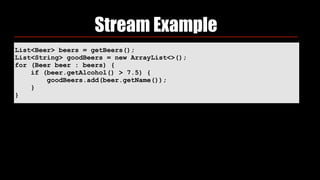
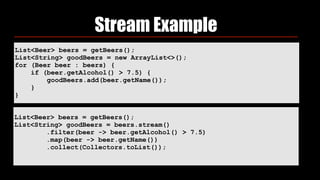
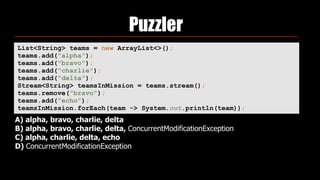
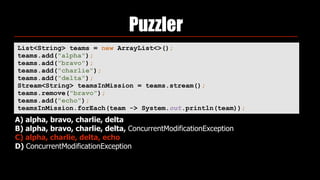
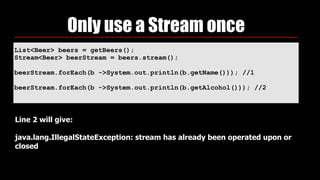
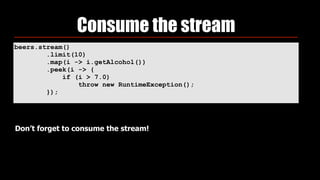
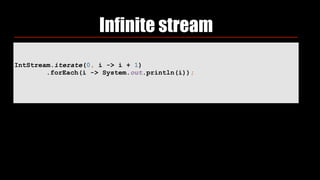
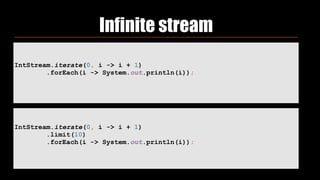
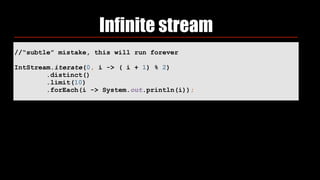
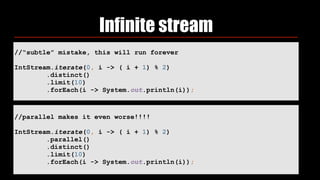
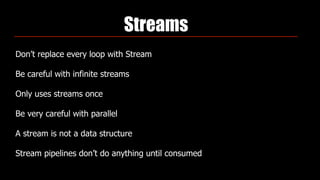
- Streams API which supports functional-style operations on streams of elements
- Date and time API improvements with new java.time package
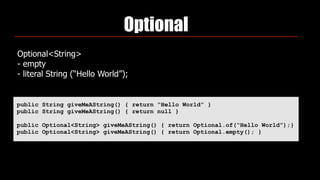
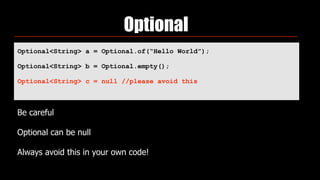
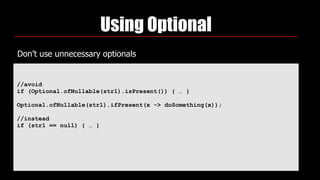
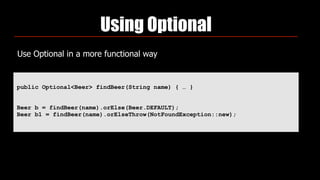
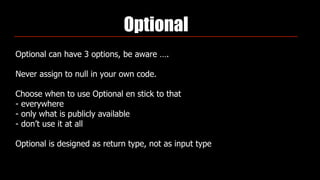
- Optional as a container class for nullable values