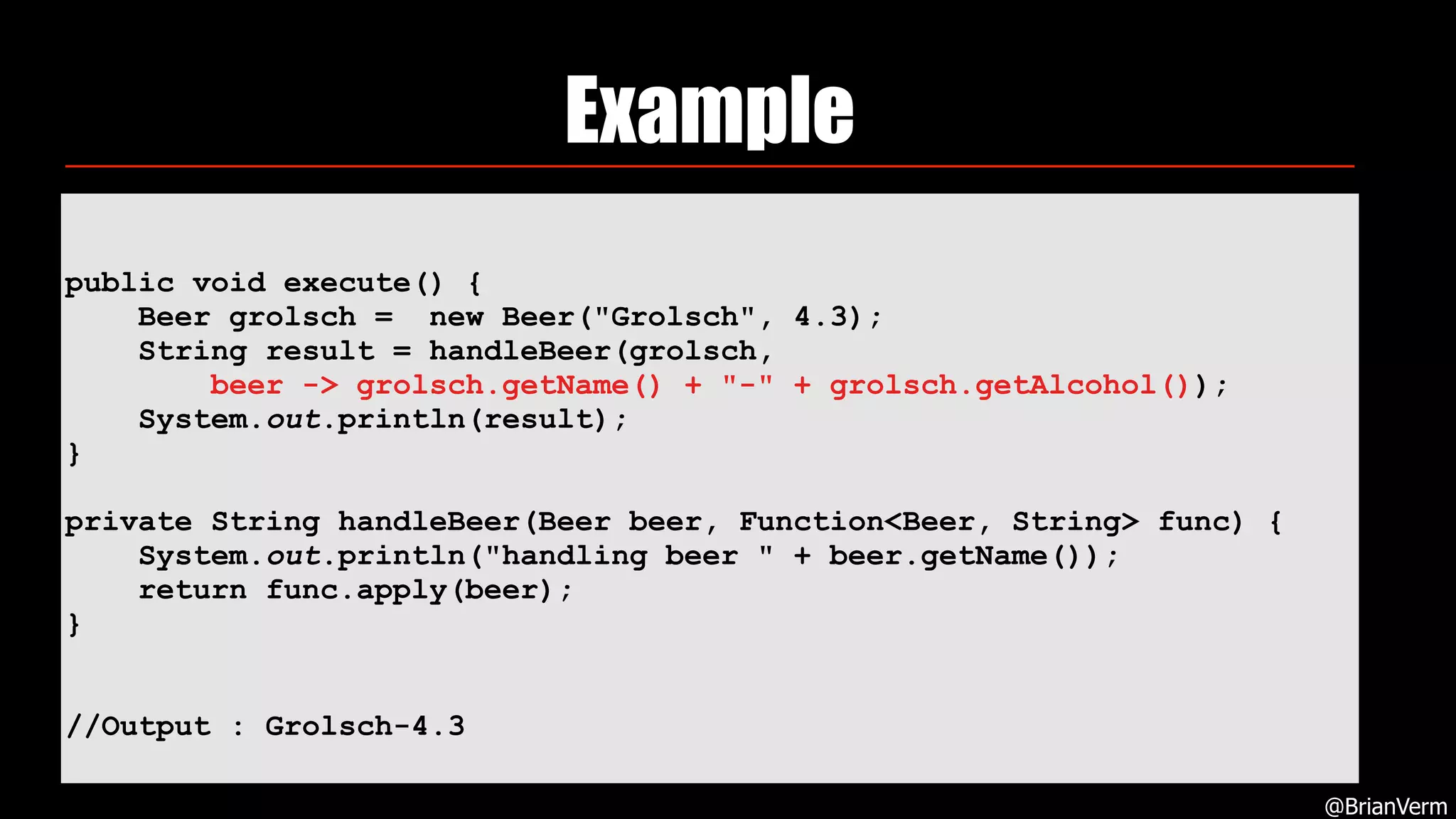
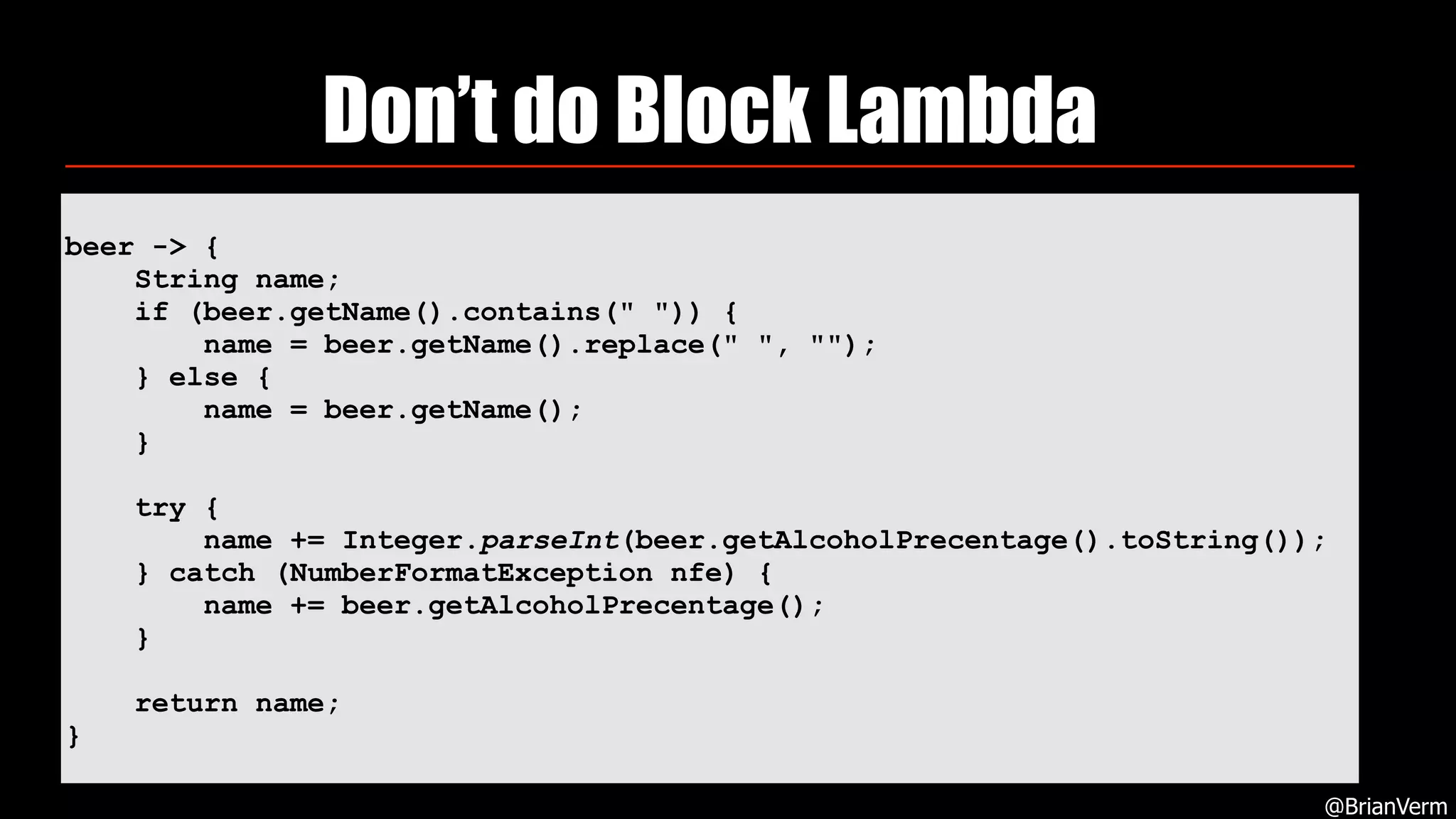
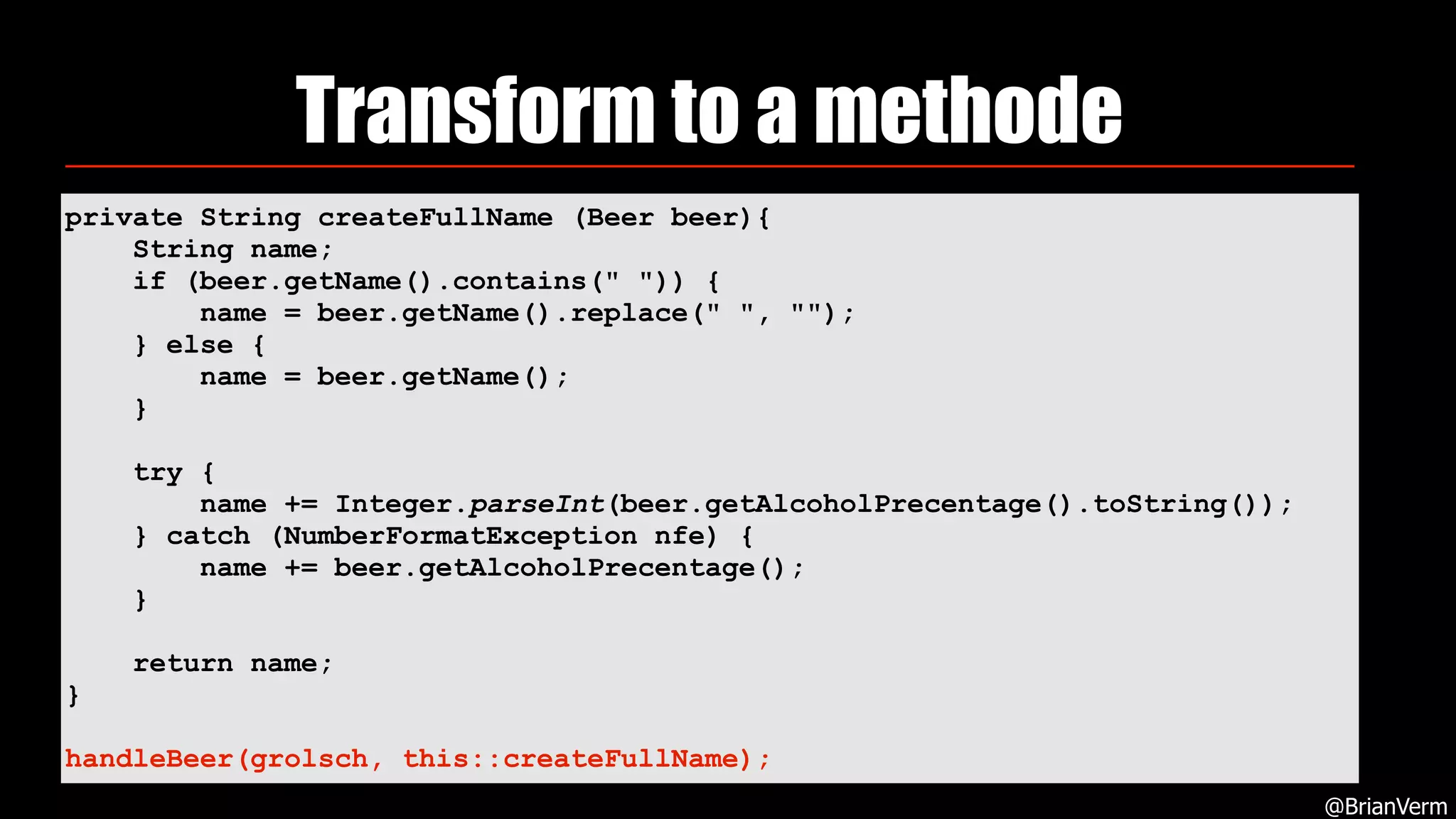
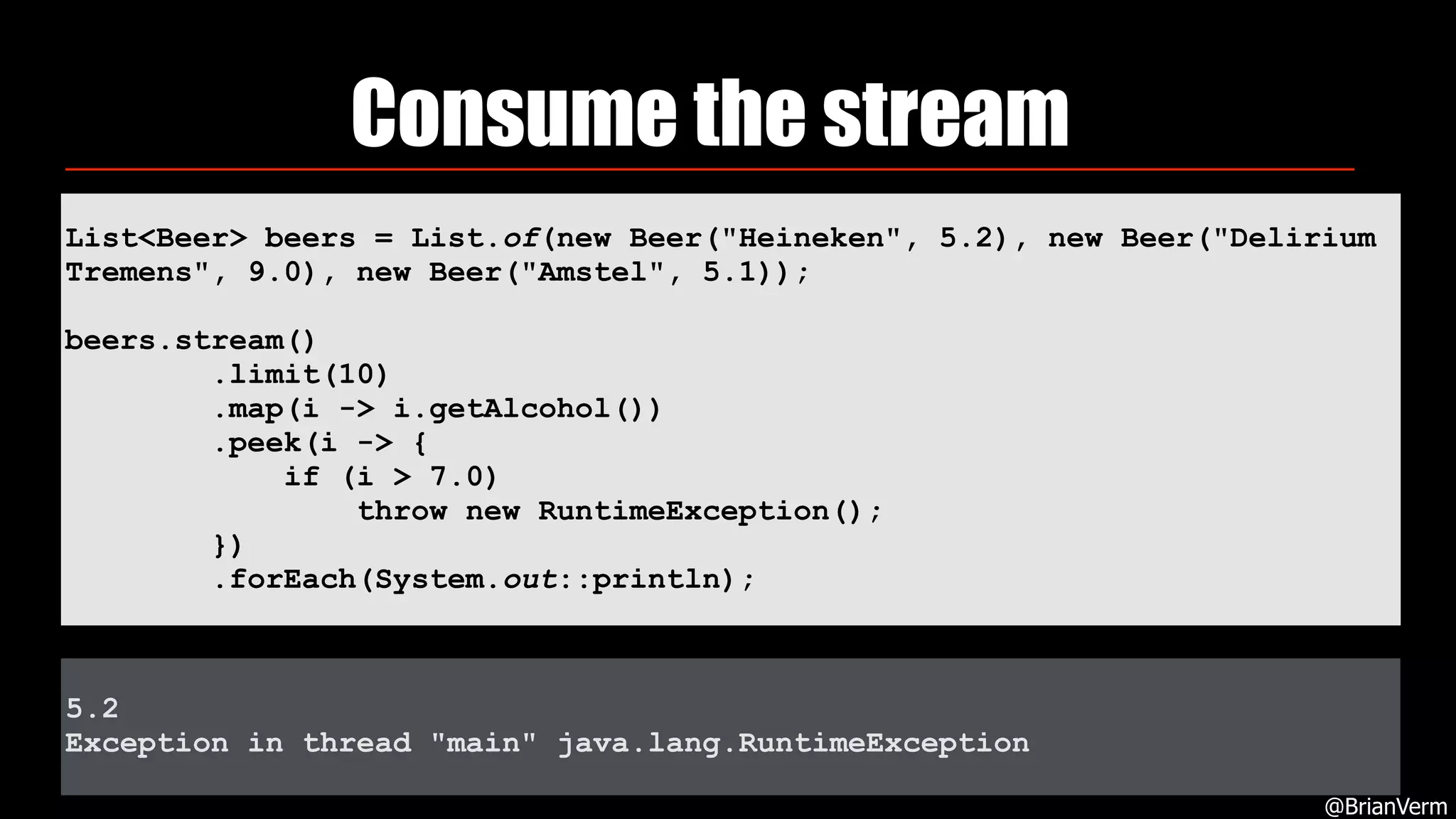
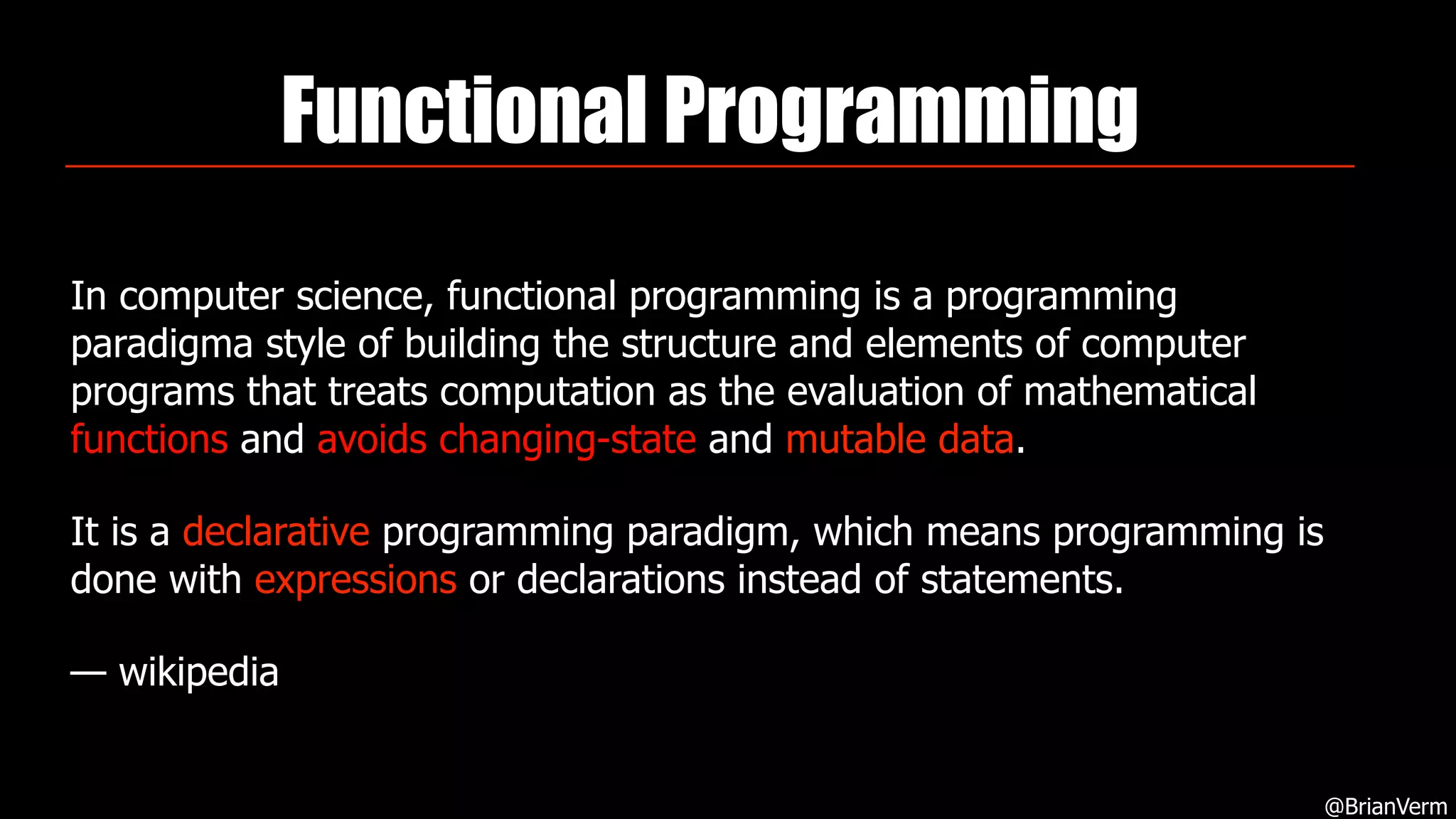
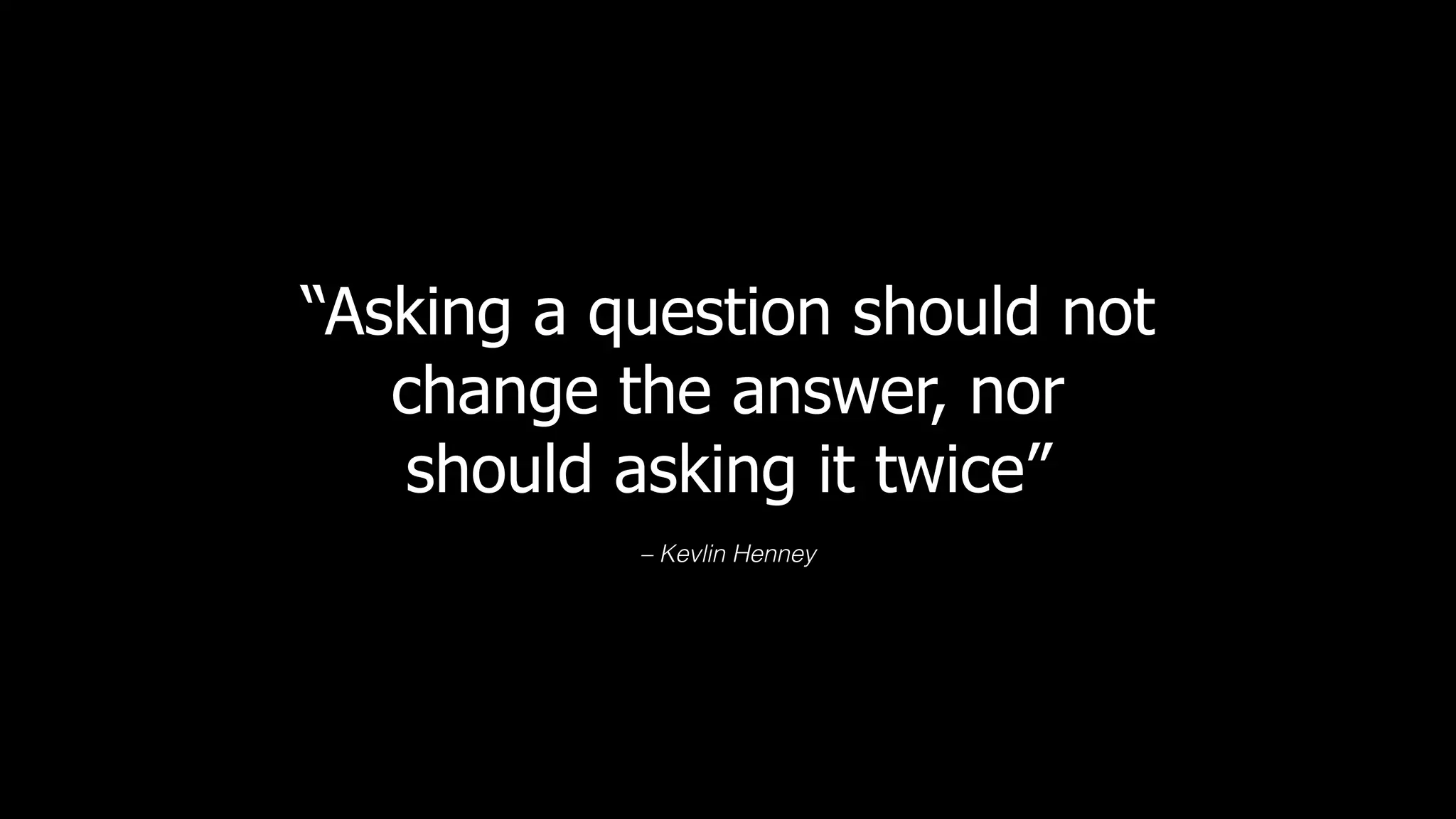
1. Common mistakes with Functional Java include doing too much in a single lambda, using block lambdas when a method would be better, mutating objects within streams, and not consuming streams.
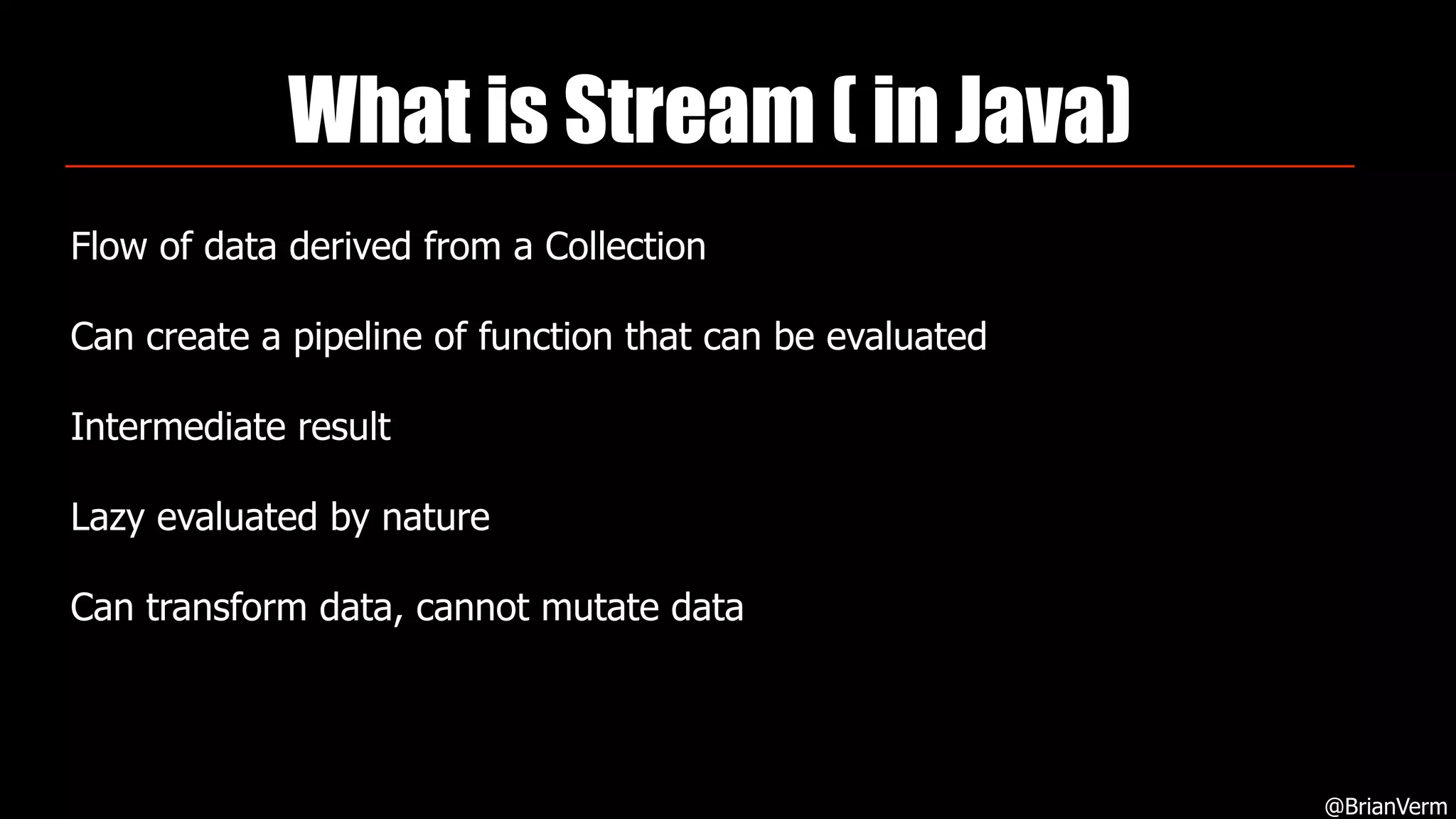
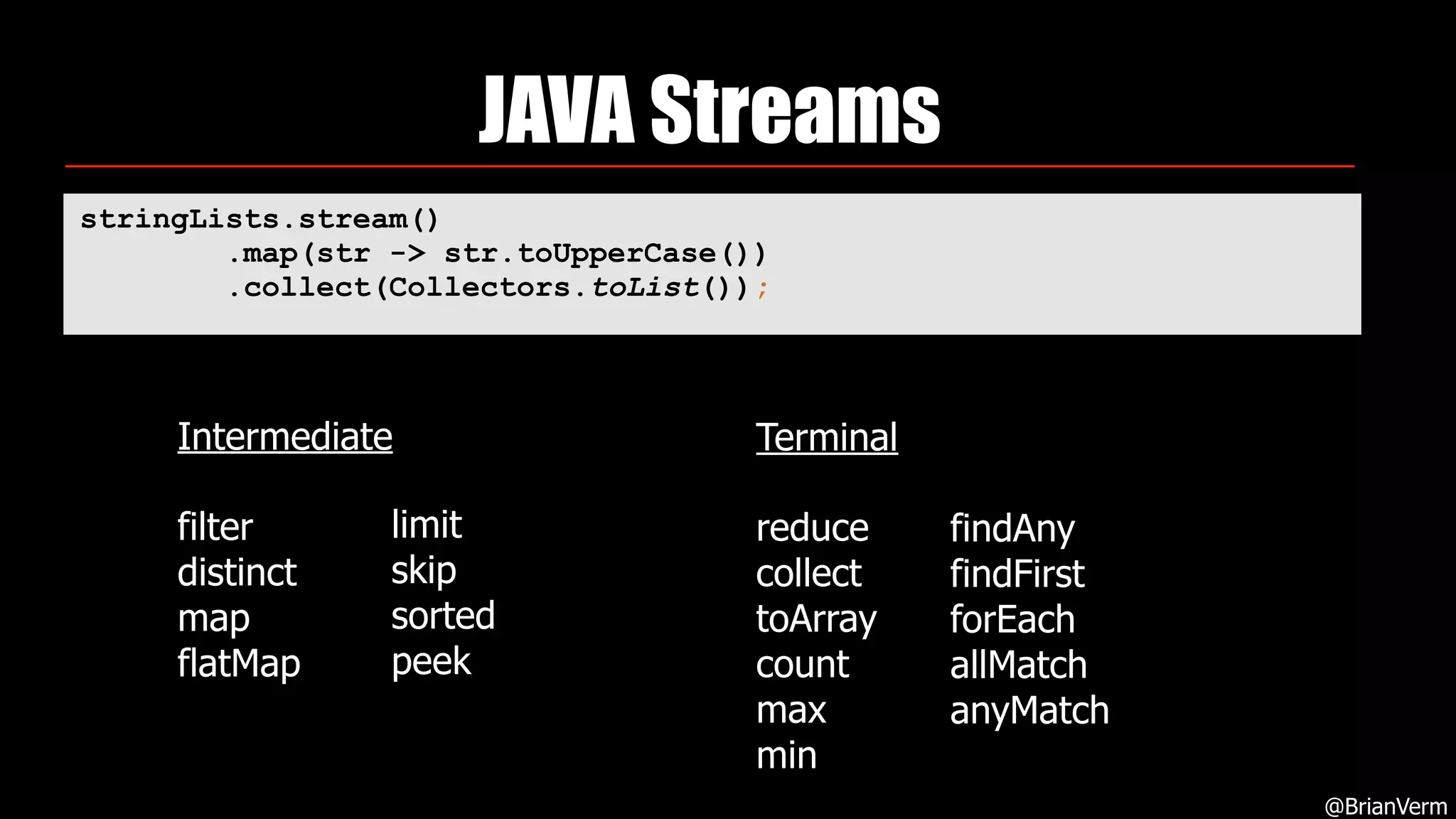
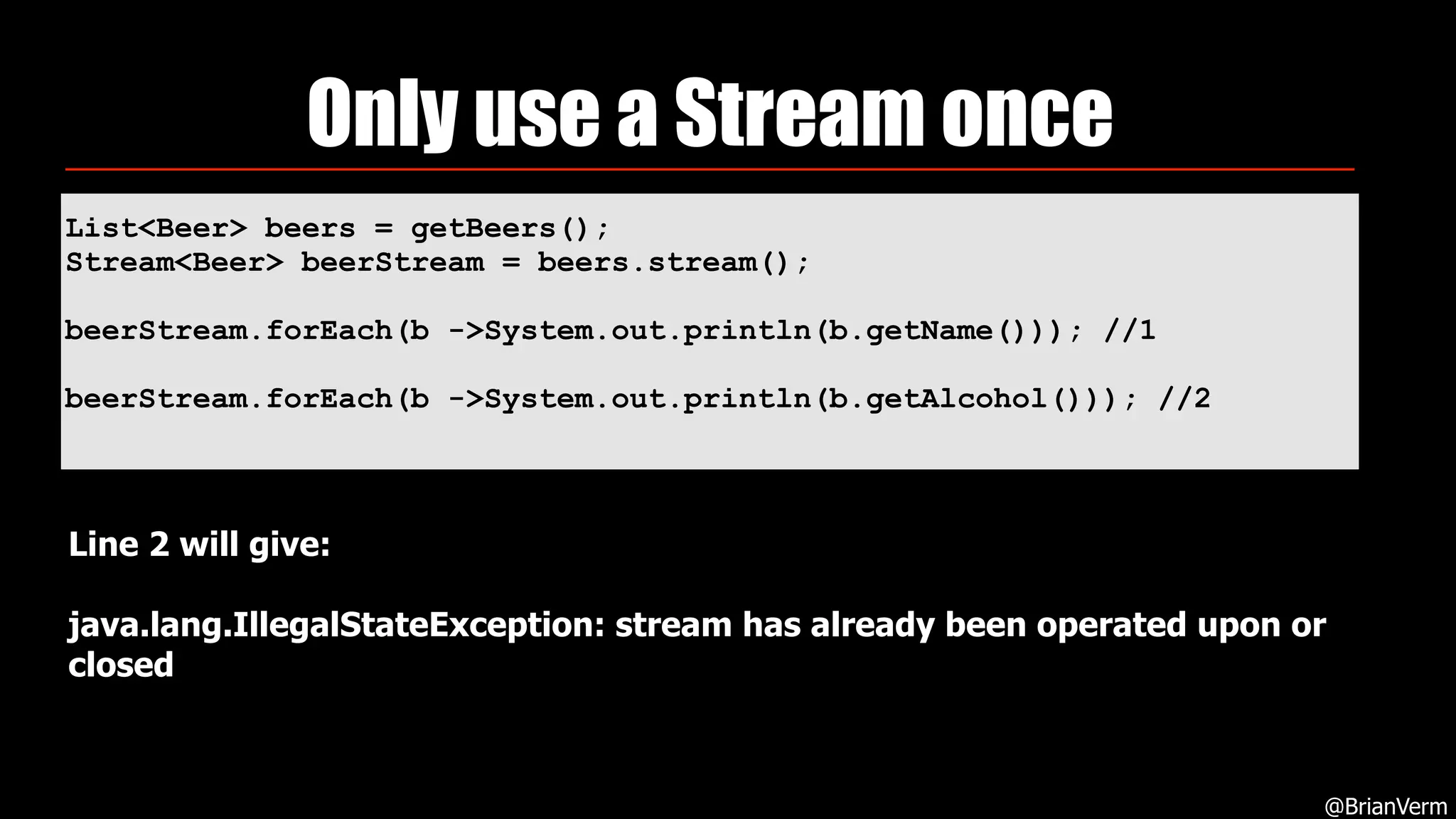
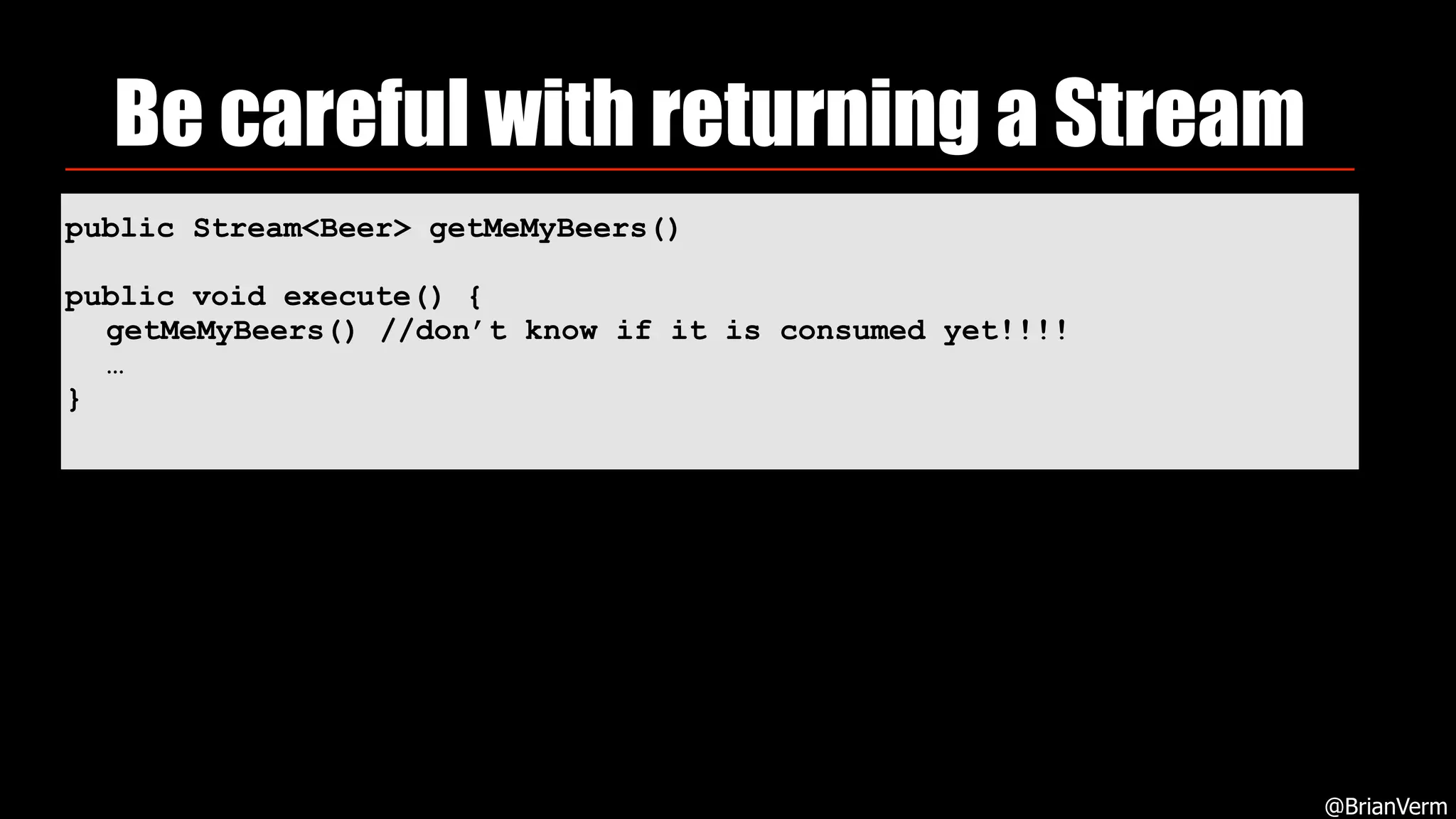
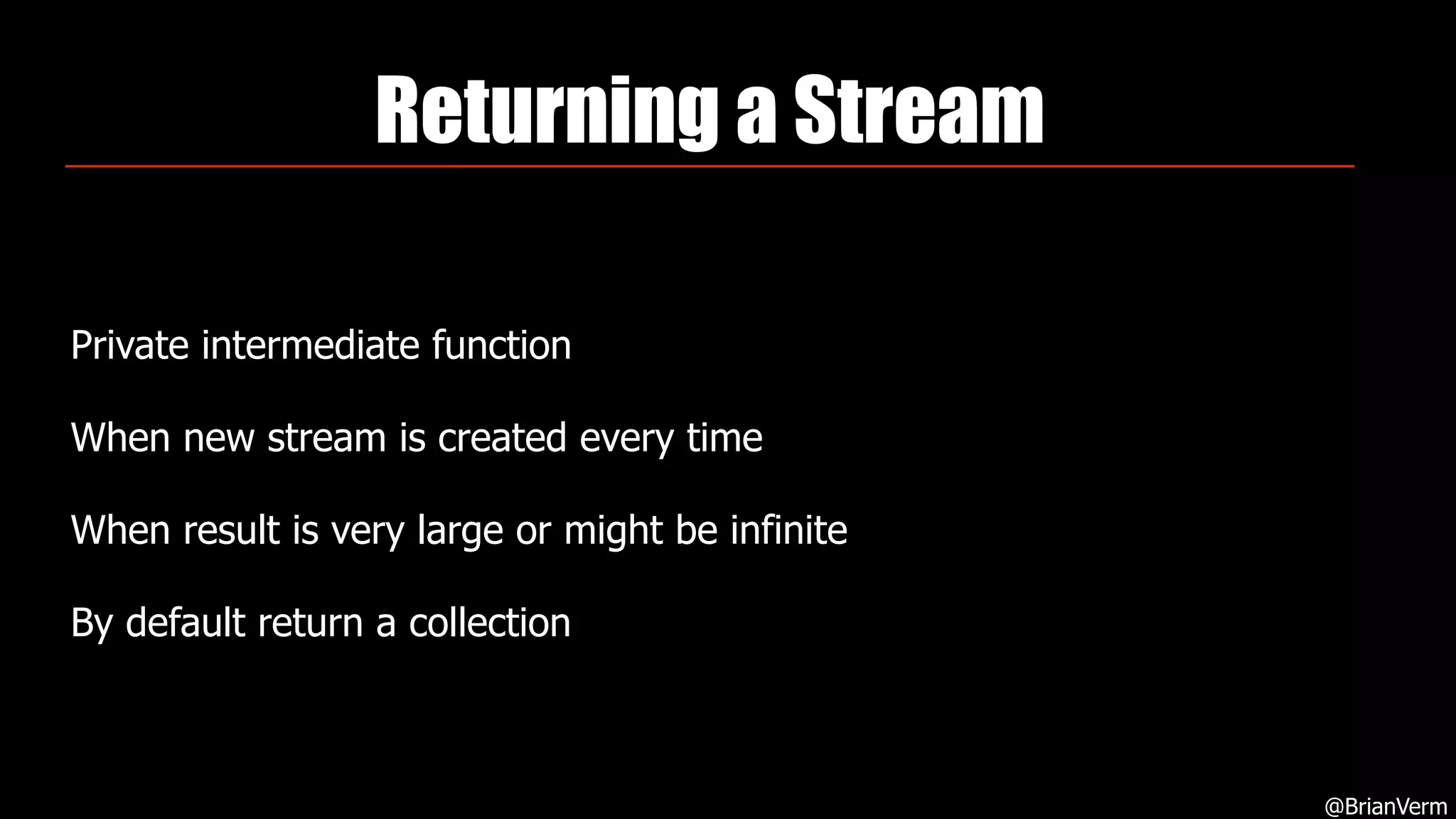
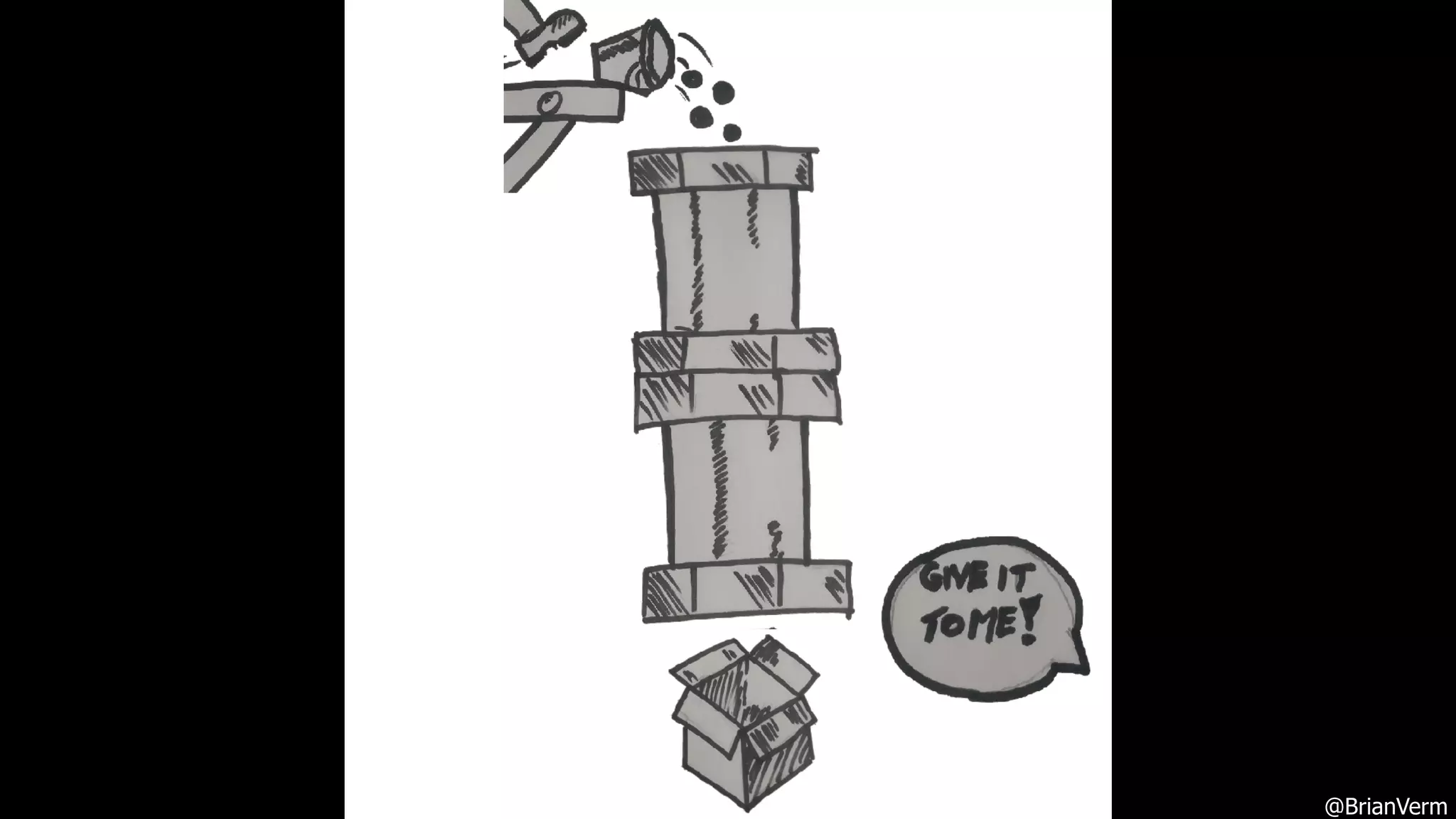
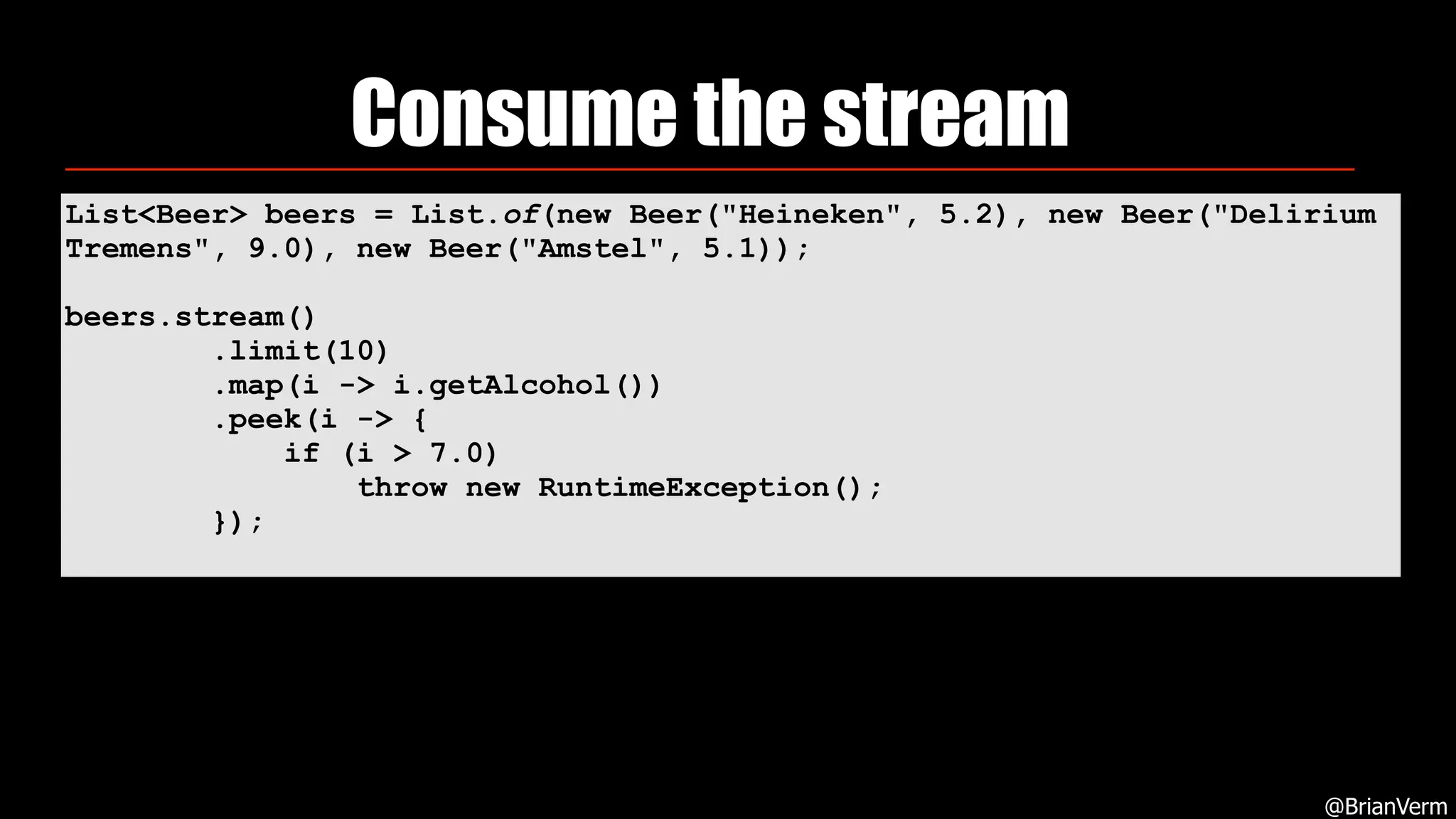
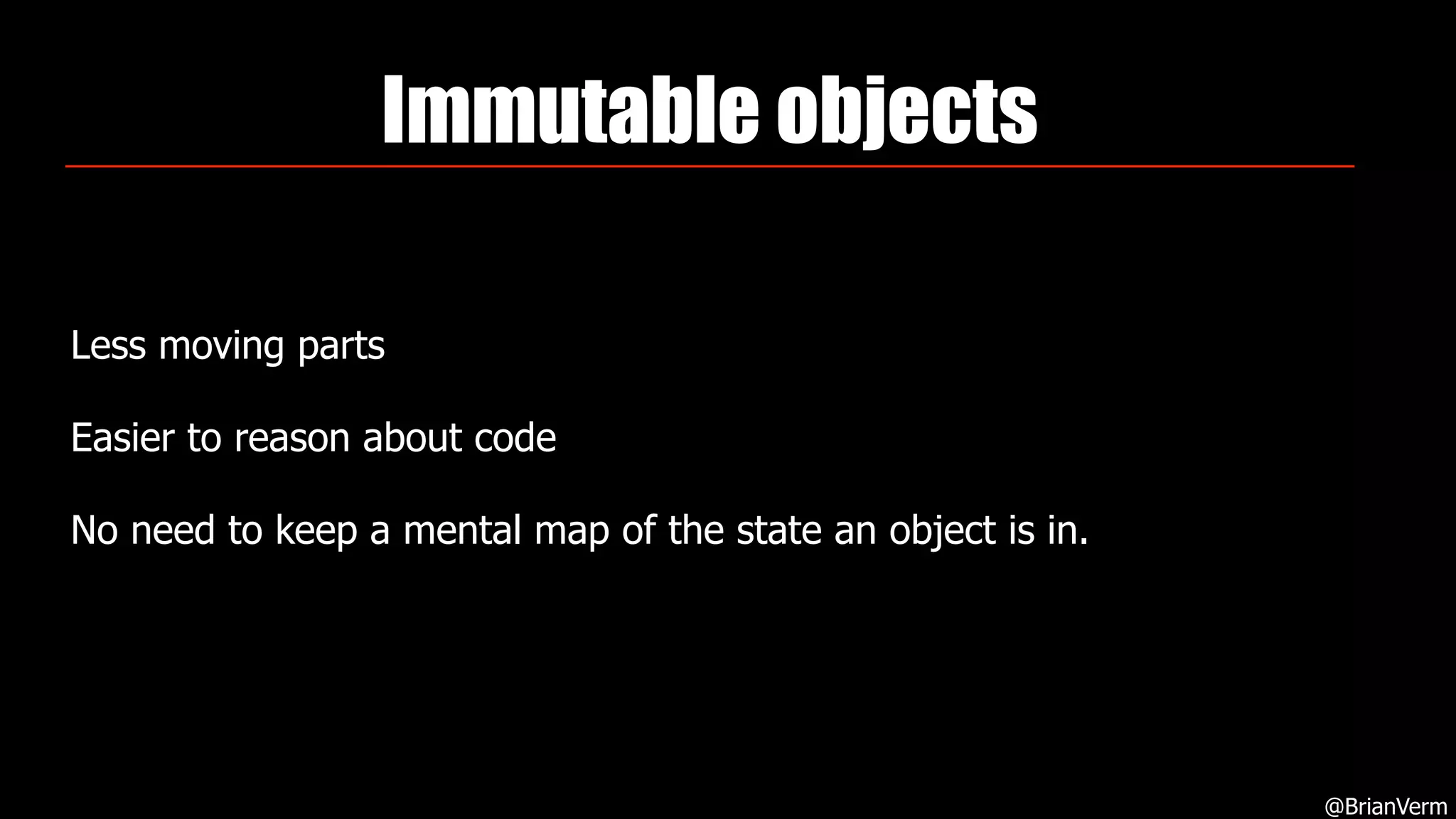
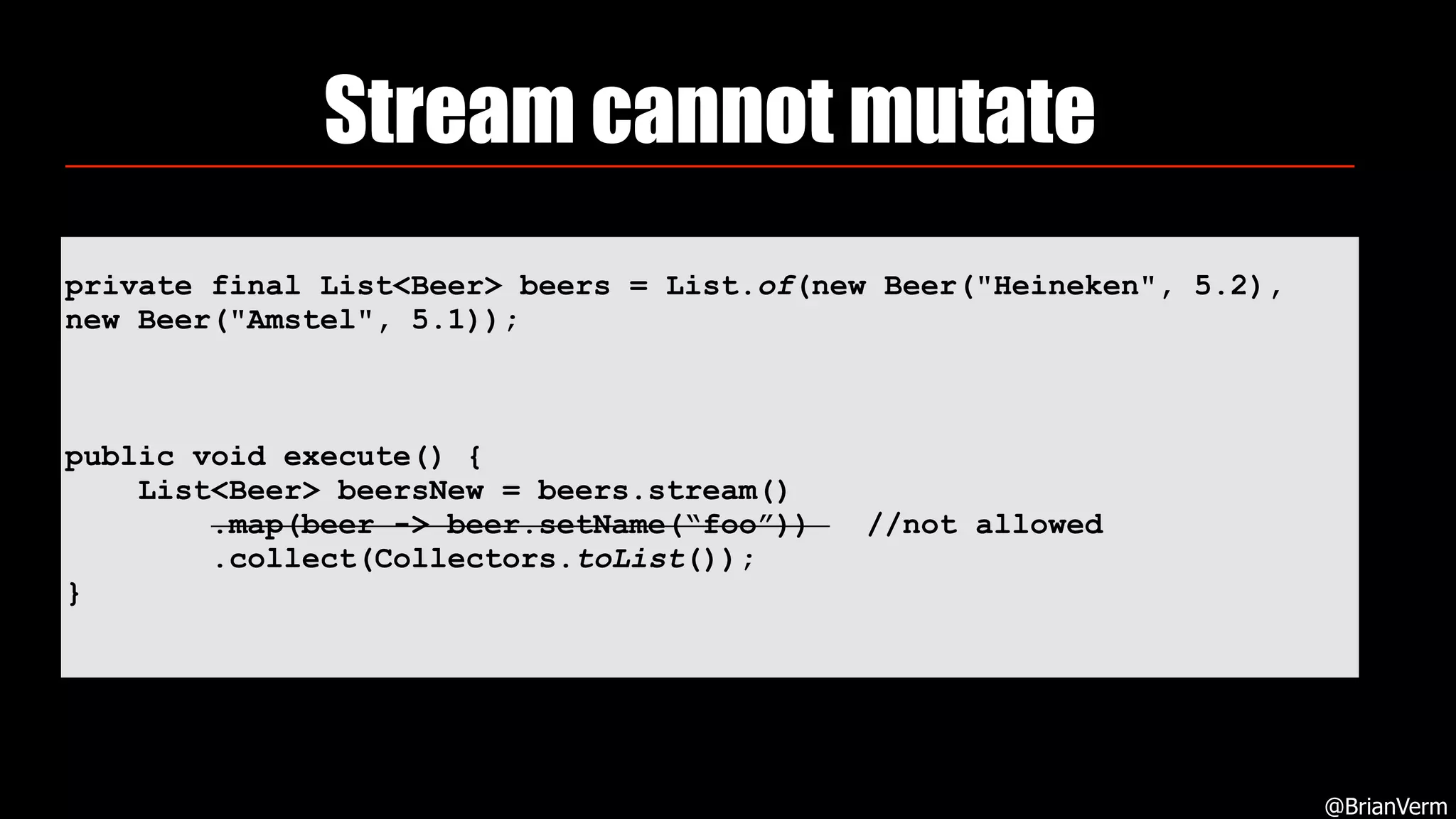
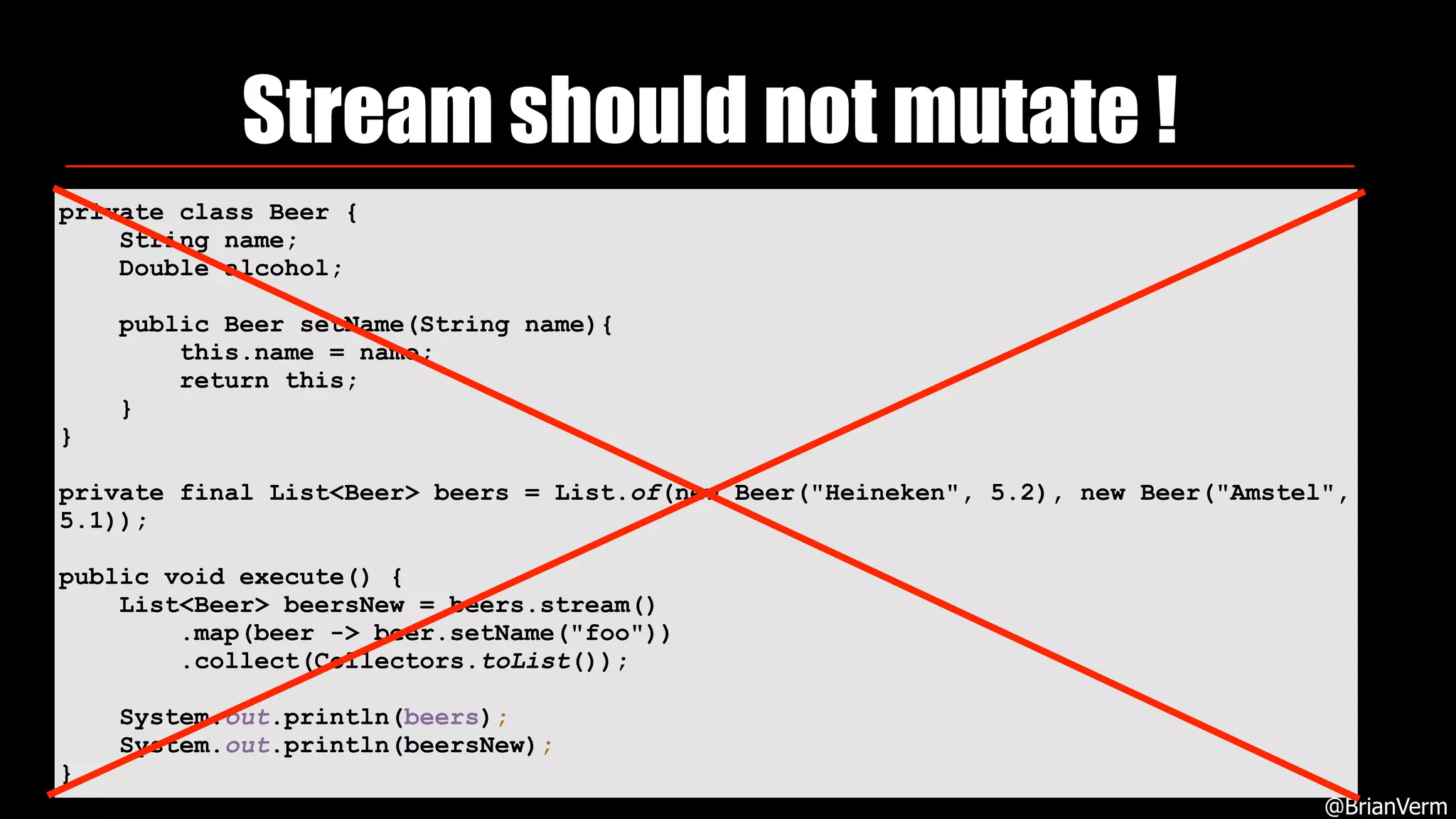
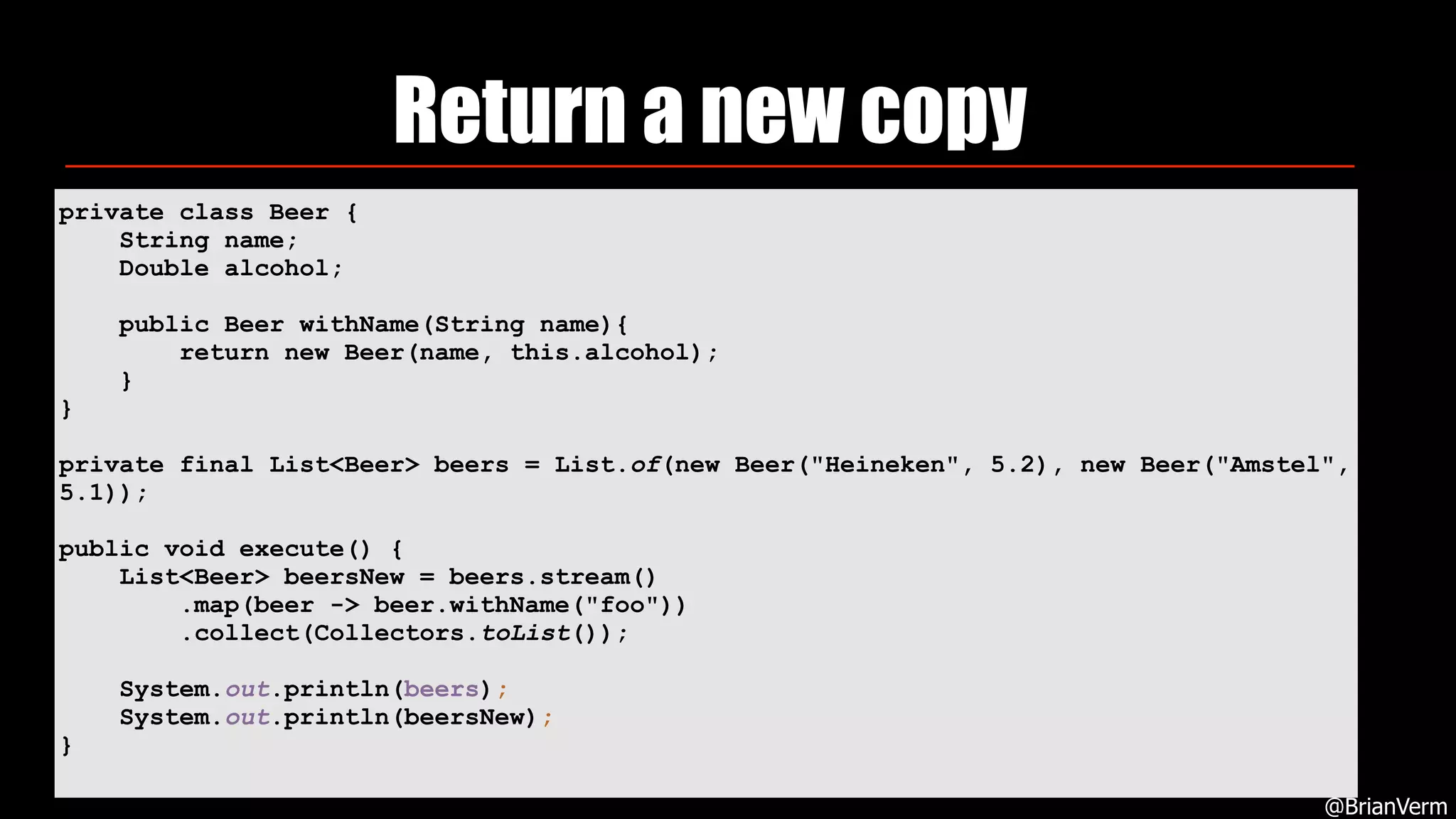
2. Streams are lazy and should not be reused or mutate objects. It is better to return new copies of objects from streams.
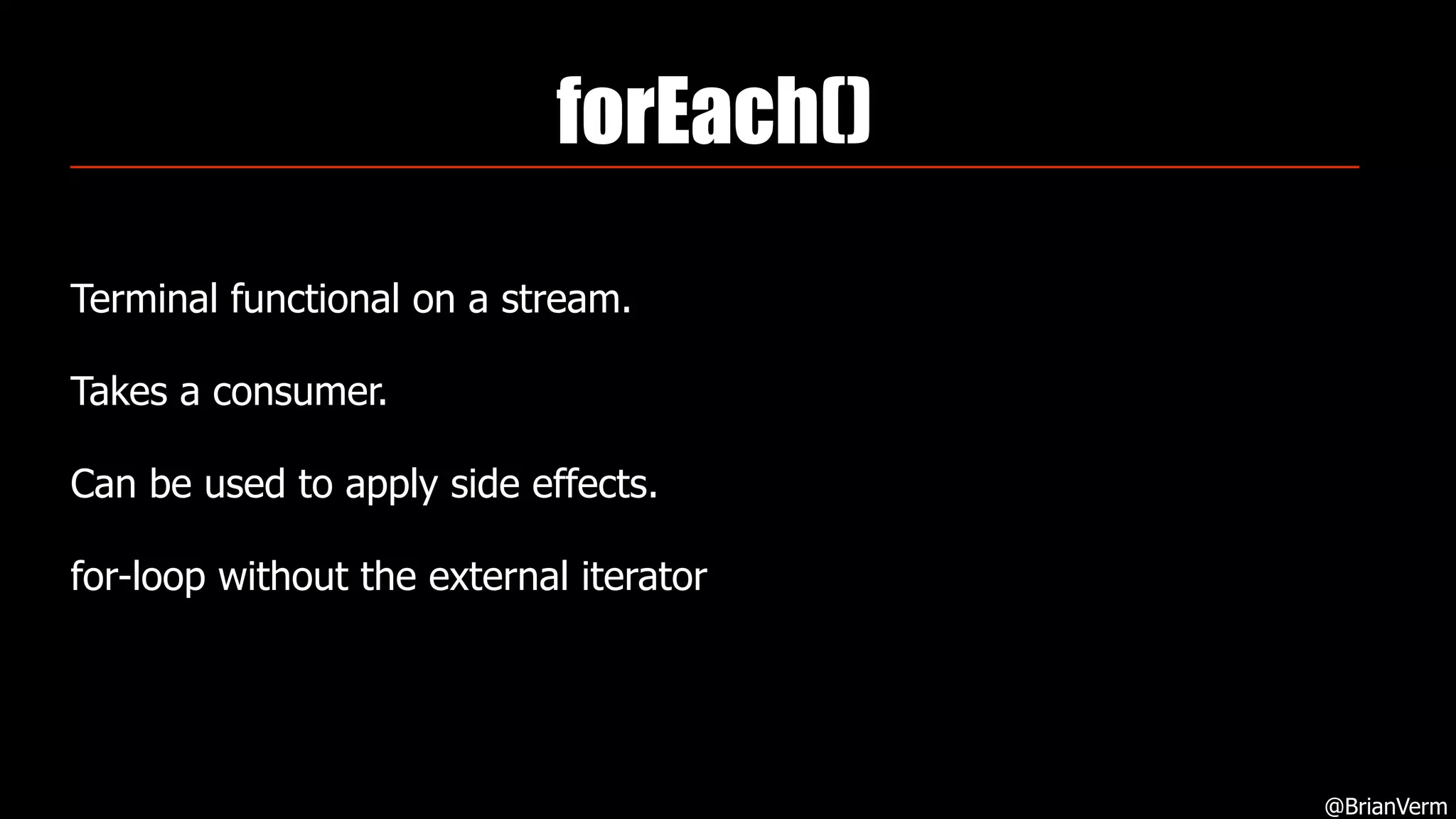
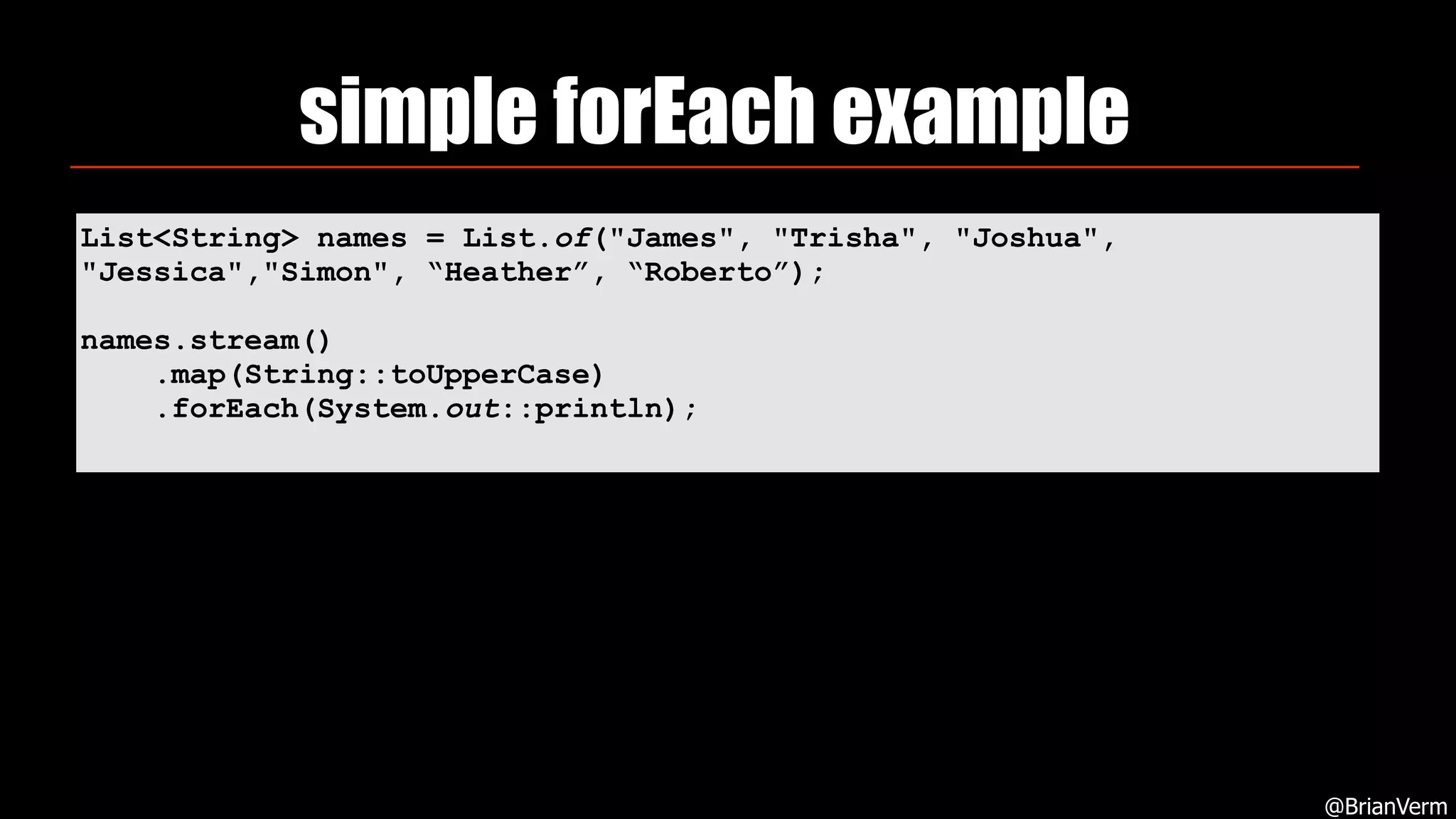
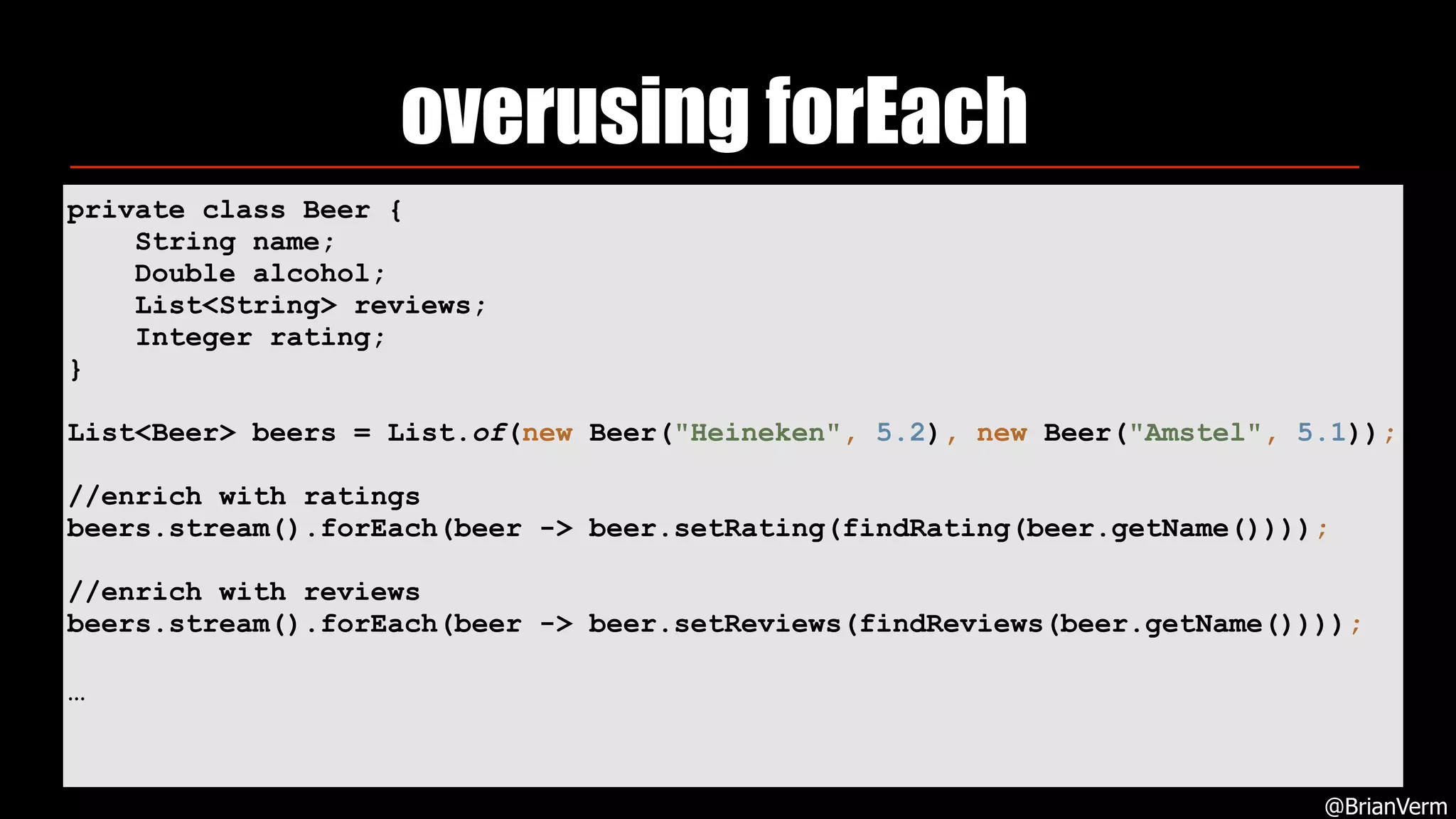
3. Overusing forEach can indicate an opportunity to use more functional techniques.
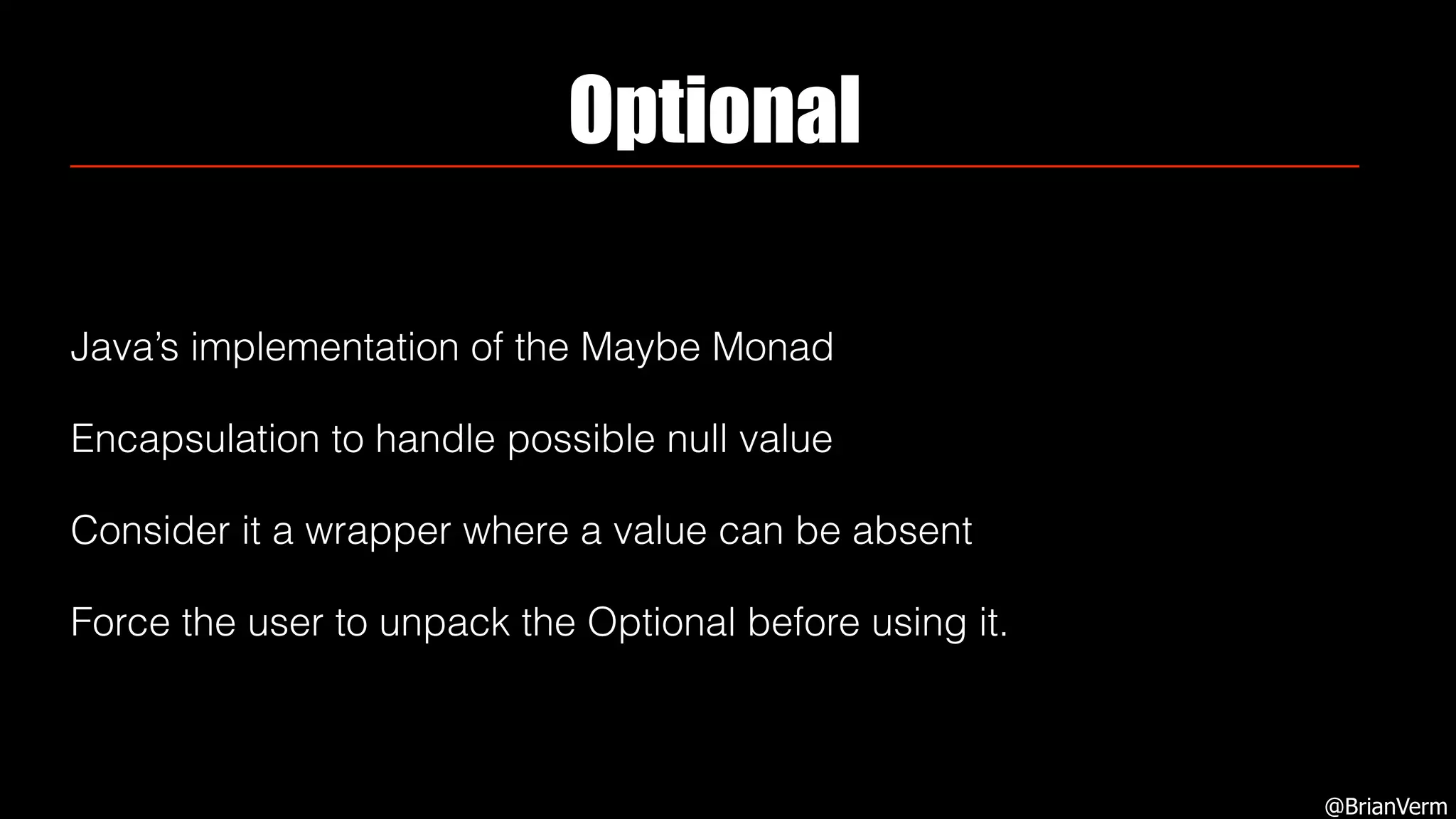
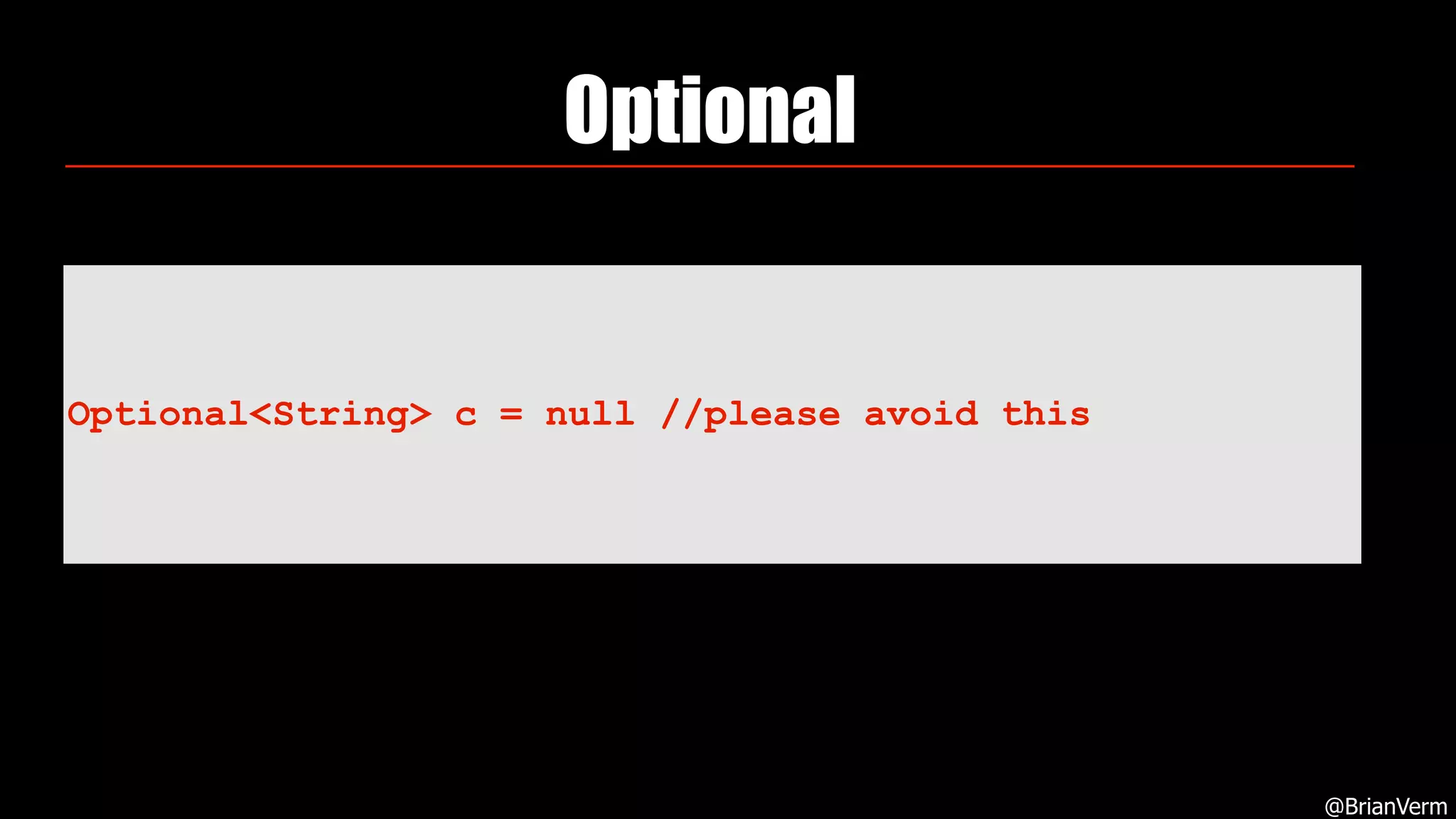
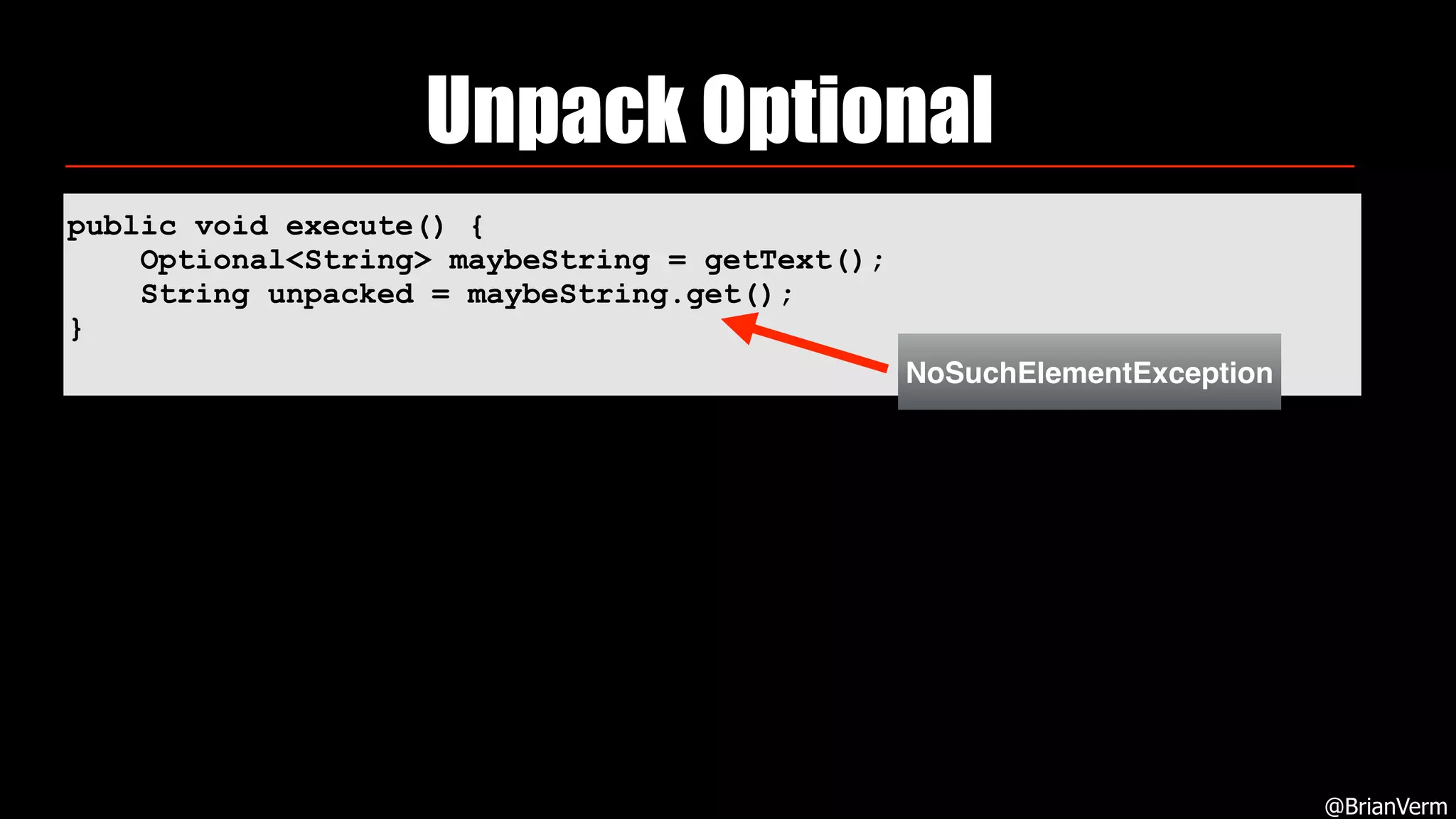
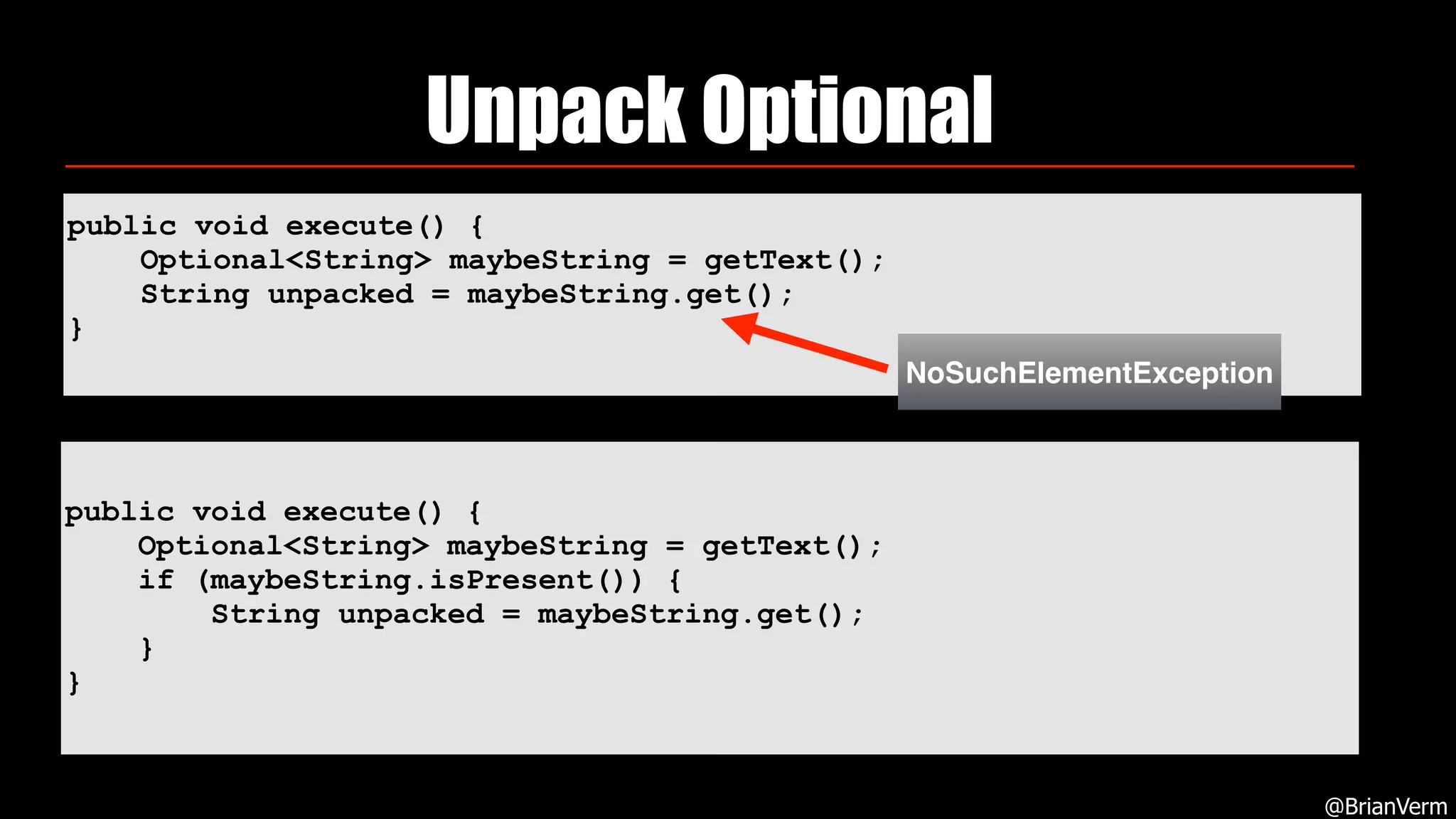
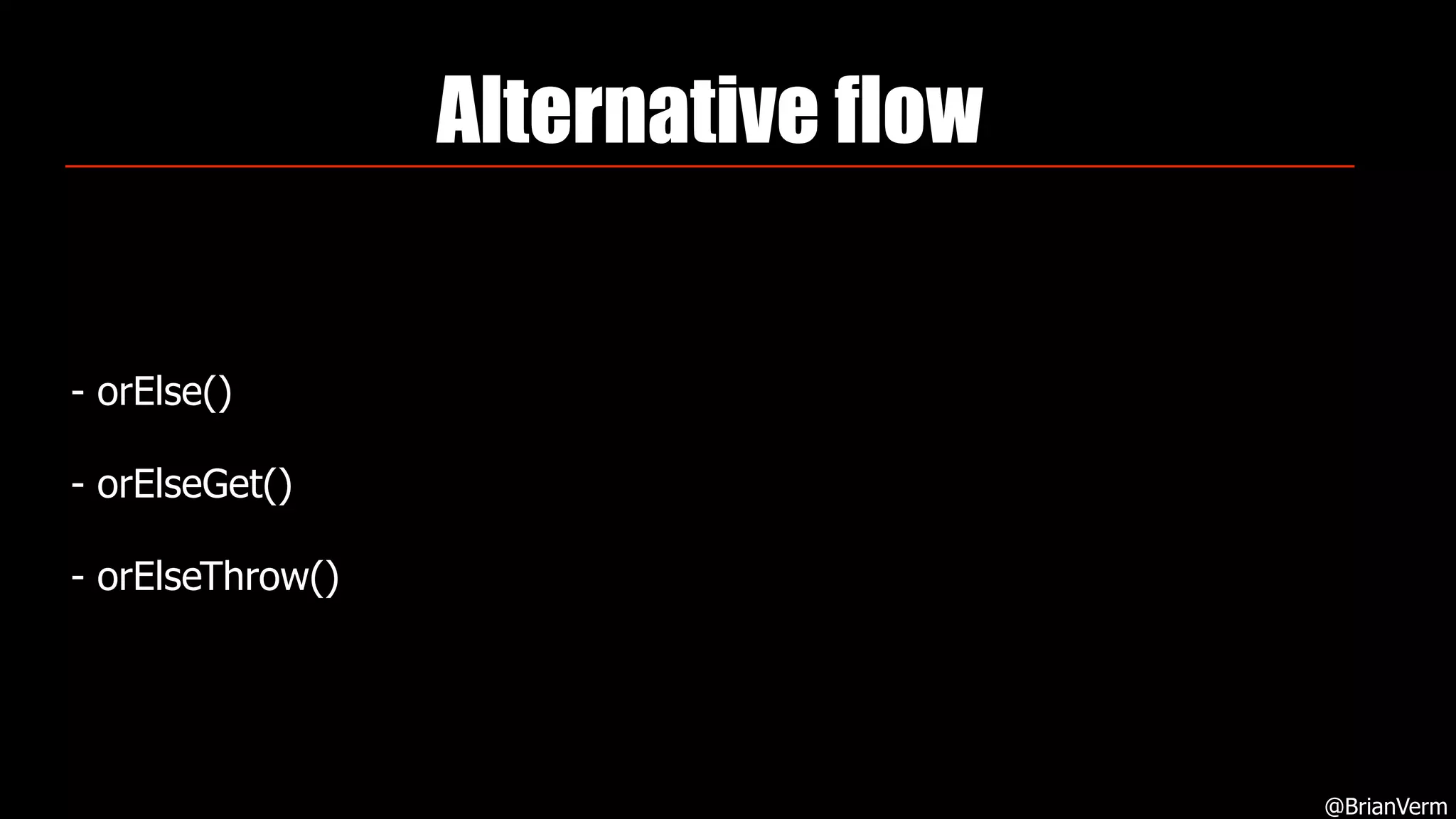
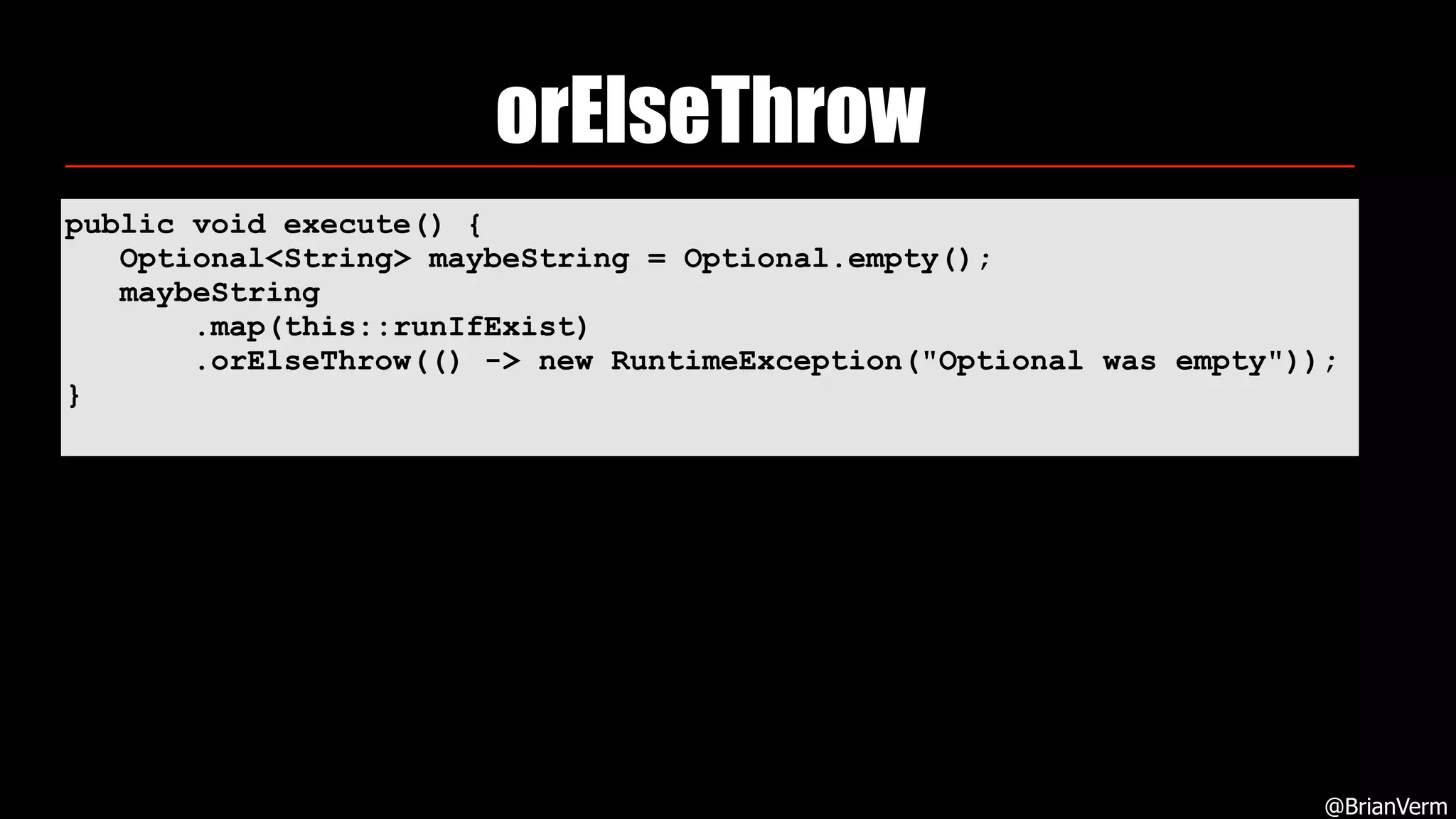
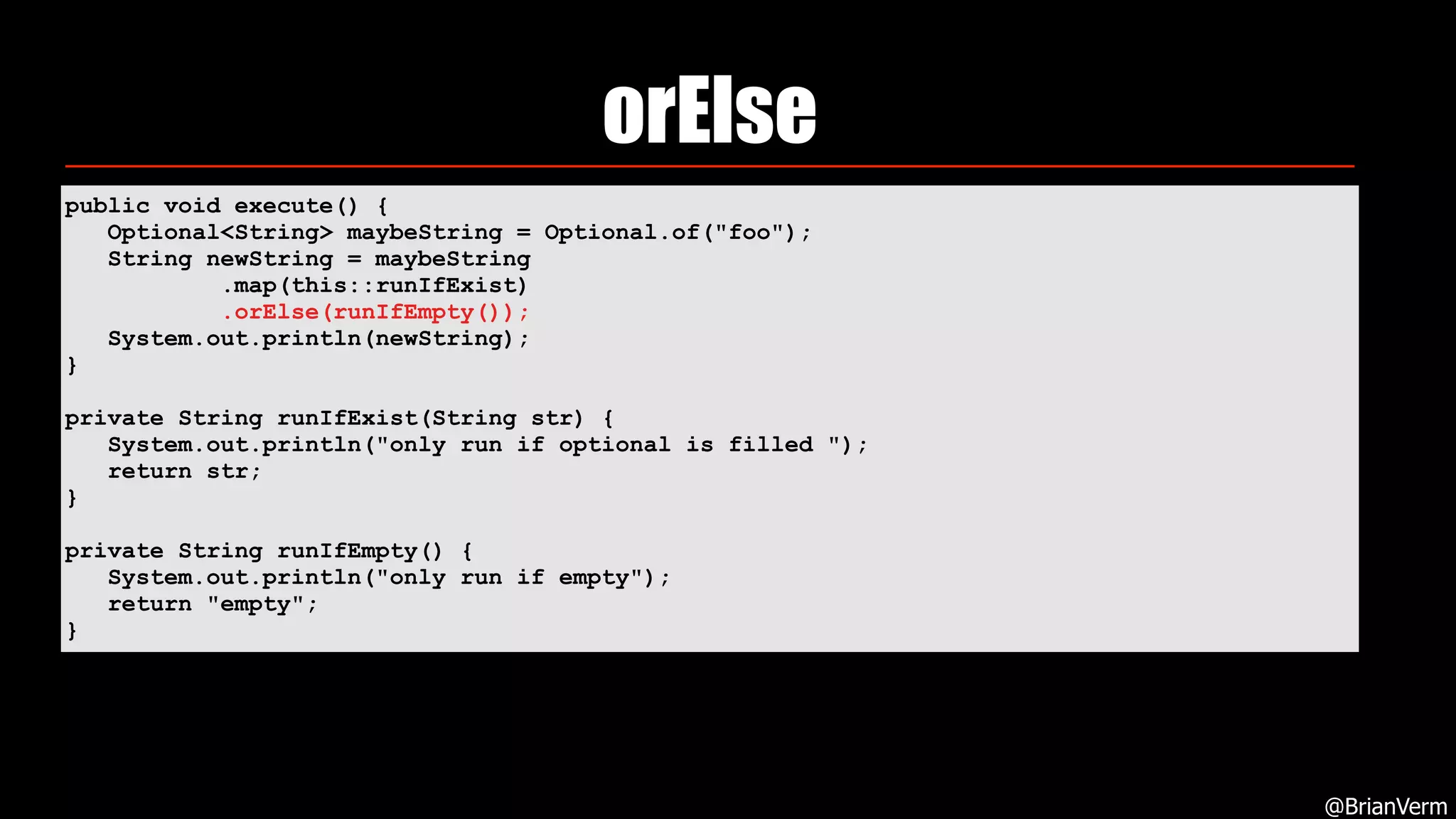
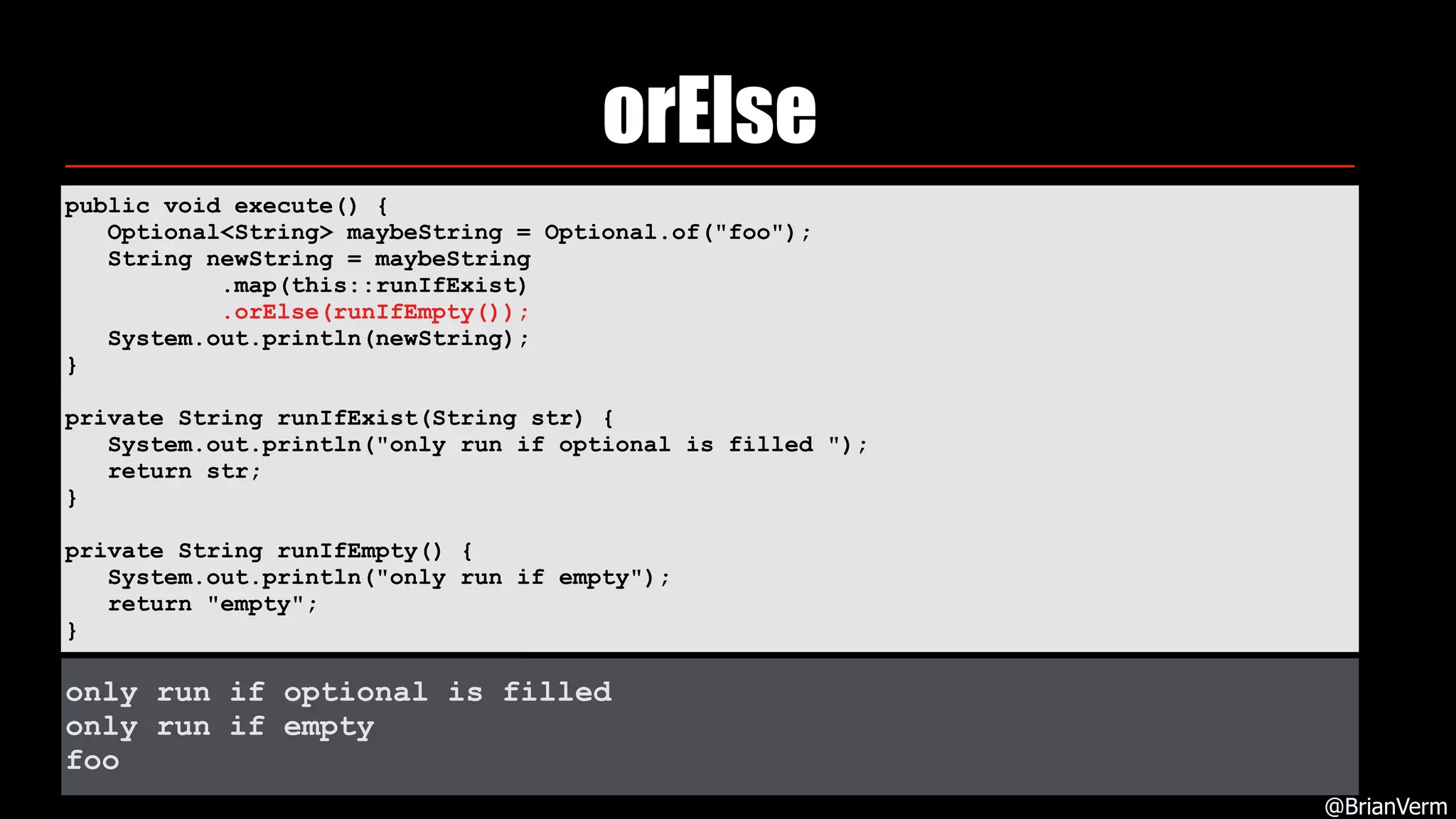
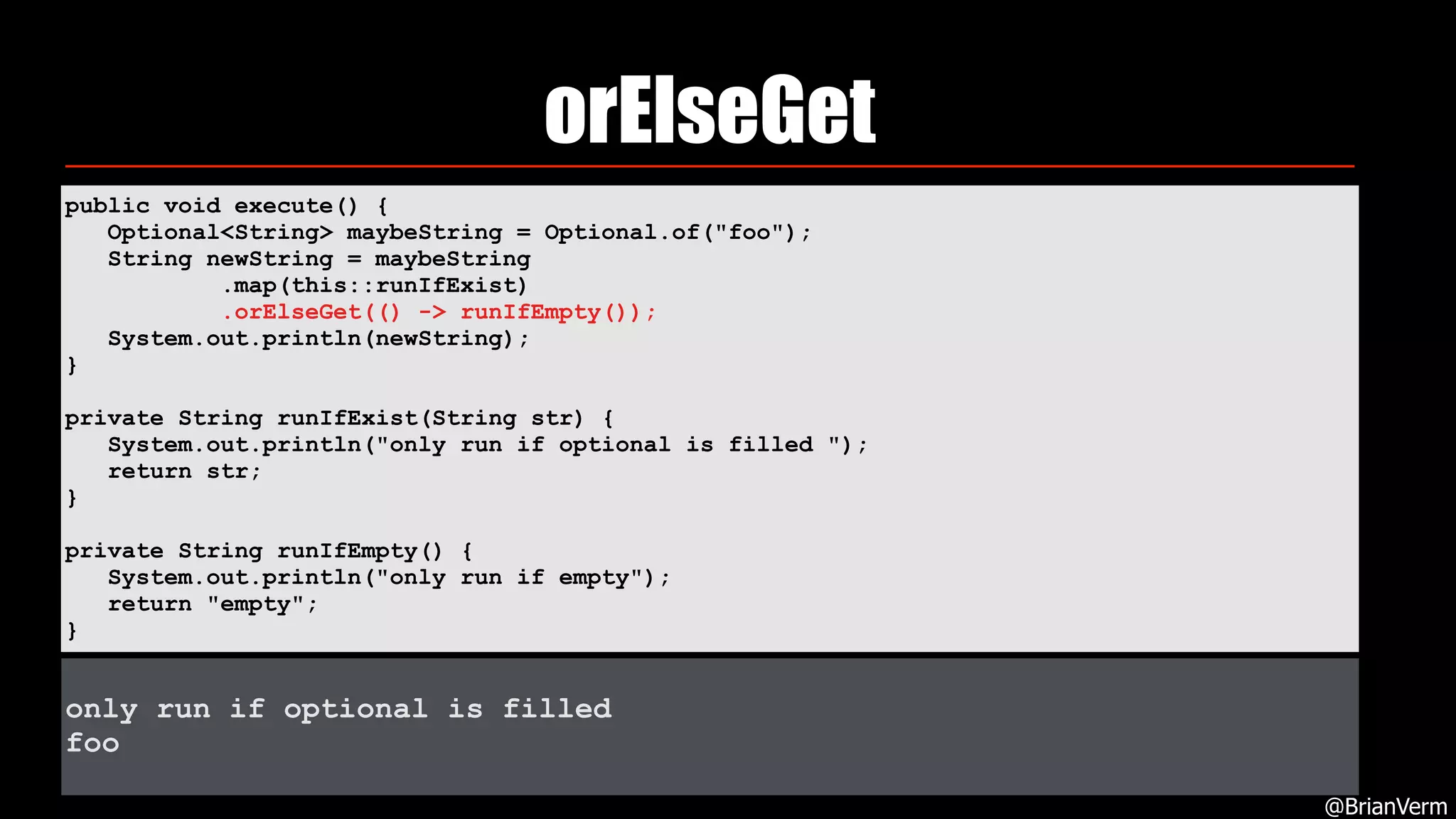
4. With Optionals, always unpack values before using them and consider alternative flows like orElse and orElseGet.


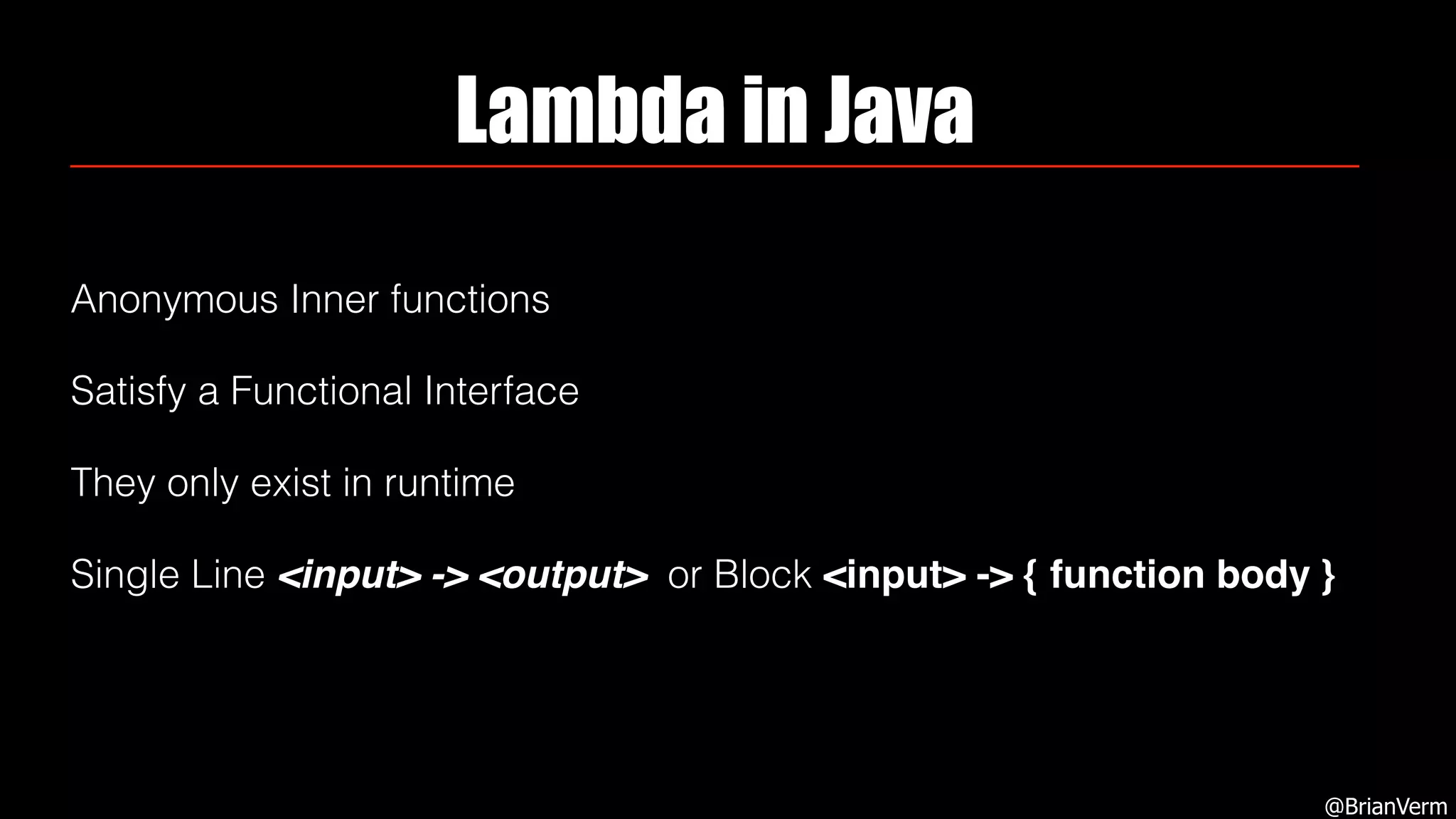
![Lambda Expression
In computer programming, a lambda expression is a function definition
that is not bound to an identifier. Anonymous functions are often:[1]
• arguments being passed to higher-order functions, or
• used for constructing the result of a higher-order function that
needs to return a function.
@BrianVerm](https://image.slidesharecdn.com/commonmistakesfunctionaljavadevoxx-181115155030/75/Common-mistakes-functional-java-devoxx-7-2048.jpg)






![Either type
@BrianVerm
private Either<Exception, String> canGoWrong(Integer input) {
if (input > 10) {
return Either.Left(new RuntimeException("larger then 10"));
}
return Either.Right("["+input+"]");
}
List<Either<Exception, String>> canGoWrongs = IntStream.range(0,12)
.mapToObj(i -> canGoWrong(i))
.collect(Collectors.toList());](https://image.slidesharecdn.com/commonmistakesfunctionaljavadevoxx-181115155030/75/Common-mistakes-functional-java-devoxx-73-2048.jpg)
![Either type
@BrianVerm
private Either<Exception, String> canGoWrong(Integer input) {
if (input > 10) {
return Either.Left(new RuntimeException("larger then 10"));
}
return Either.Right(“["+input+"]");
}
List<Either<Exception, String>> canGoWrongs = IntStream.range(0,12)
.mapToObj(i -> canGoWrong(i))
.collect(Collectors.toList());
canGoWrongs.stream()
.map(e -> e.mapRight(s -> s.toUpperCase()))
.flatMap(o -> o.map(Stream::of).orElseGet(Stream::empty))
.forEach(System.out::println);](https://image.slidesharecdn.com/commonmistakesfunctionaljavadevoxx-181115155030/75/Common-mistakes-functional-java-devoxx-74-2048.jpg)