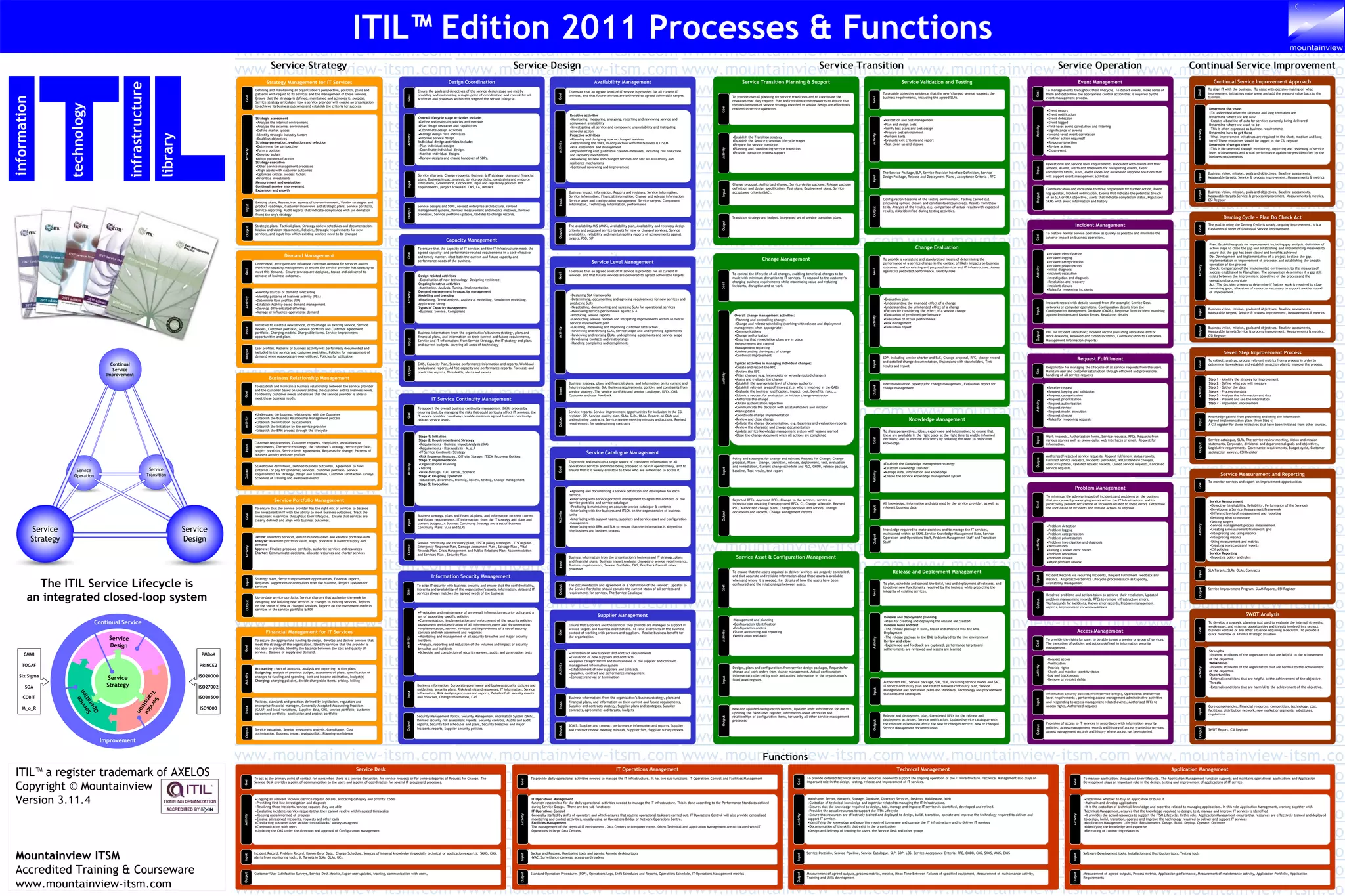
The document is a list of the website www.mountainview-itsm.com repeated over 100 times. It appears to be promoting the services offered on that website related to IT service management training and courseware. The website is described as providing accredited training and courseware on ITIL, its processes and functions based on the ITIL service lifecycle perspective.