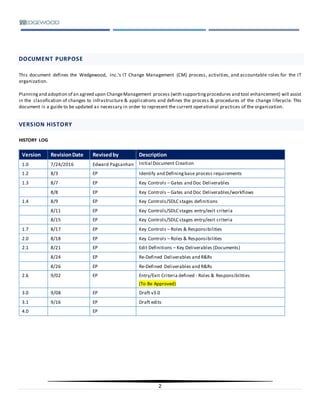
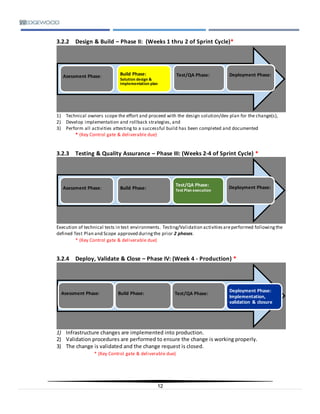
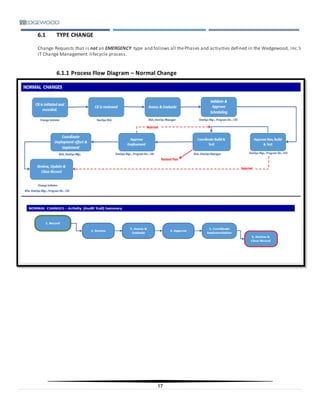
The document defines Wedgewood Inc.'s IT change management process, activities, and roles. It establishes a framework for managing infrastructure changes through standardized methods and procedures. The objectives are to improve service/support quality, reduce risks and costs from changes, and achieve compliance. Key aspects include a change advisory board, four-phase change lifecycle of initiate/assess, design/build, test, and deploy/validate/close, and roles such as change manager and project sponsors.