ISACA Pune Chapter June 17th 2017 - Narendra Bhati
- 3. Something About Me Narendra Bha; – OSCP, CEH Senior Security Analyst Suma SoK Pvt. Ltd. – Pune Email - narendra.bha5@websecgeeks.com Blog - h-p://websecgeeks.com • Having Four Years of Experience and have been working in Suma SoP Pvt. Ltd. as Senior Security Analyst • Spoke at OWASP Pune Chapter 18th Feb 2016 on Advance Web Applica5on A-acks "Dive into the Profound Web a-acks". • Found various cri5cal vulnerabili5es on Portals like Google, Facebook, Apple, LinkedIn, MicrosoP, Yahoo and more • Holds more then 12 CVE & 3 Zero days vulnerabili5es • Maintaining my own blog where I put my exploits and research- h-p://websecgeeks.com ISACA Pune Chapter Monthly Lecture Mee5ng June 2017
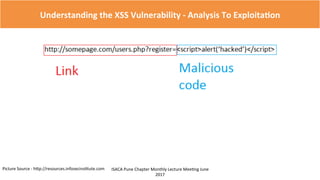
- 4. Understanding the XSS Vulnerability - Analysis To Exploita;on ISACA Pune Chapter Monthly Lecture Mee5ng June 2017 What Is XSS (Cross Site Scrip5ng) According to OWASP XSS (Cross Site Scrip5ng) a-acks are a type of injec5on, in which malicious scripts are injected into otherwise benign and trusted web sites In simple words, Execu;ng our own JavaScript into the browser What Is JavaScript It’s a client side scrip5ng which is mostly used to control Client Side objects Ex. Restrict the user to enter only email in email text box by applying a JavaScript code. Impact Of XSS • An a-acker can control/modify the Web Page content. • Hijacking the user SESSION ID • Redirect Users other malicious website.
- 18. Understanding the XSS Vulnerability - Analysis To Exploita;on ISACA Pune Chapter Monthly Lecture Mee5ng June 2017 Understand The Context In Reflec;on 1.Analysis Context In Reflec5on What Is Context? Contexts are the loca5ons where user input is placed. There are different types of contexts, lets discuss them in detail. 1. HTML Context 2. A-ribute Context 3. Script Context 4. URL Context 5. Other contexts(We will discuss later)
- 25. Understanding the XSS Vulnerability - Analysis To Exploita;on ISACA Pune Chapter Monthly Lecture Mee5ng June 2017 Lets Trigger The XSS 1.Analysis 2.Detec5on 3.Exploit Reflec5on Filtra5on Trigger XSS 3 Steps To Find XSS – Lets Apply Those Steps To Find XSS
- 34. Understanding the XSS Vulnerability - Analysis To Exploita;on ISACA Pune Chapter Monthly Lecture Mee5ng June 2017 Impact Of The XSS • Phishing A-acks • Redirect User To Malicious Website • Session Hijacking • DDOS A-ack • Rest Depends On A-acker Methodology.