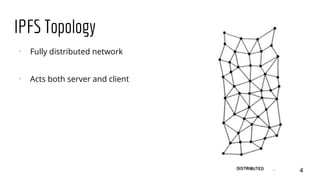
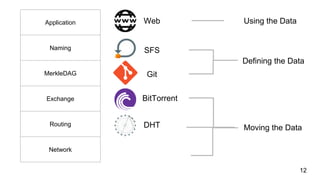
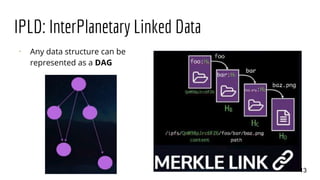
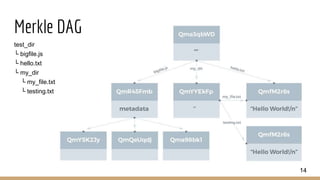
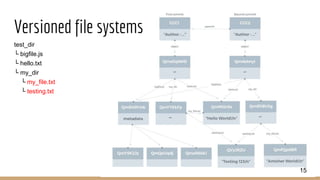
IPFS is a protocol designed to create a permanent and decentralized method of storing and sharing files faster, safer and more openly. It aims to replace HTTP and build a better web for all. IPFS uses a fully distributed network where each client acts as both client and server. It allows for distributing high volumes of data with high efficiency unlike HTTP which downloads from a single source. Any data structure can be represented as a directed acyclic graph (DAG) in IPFS.