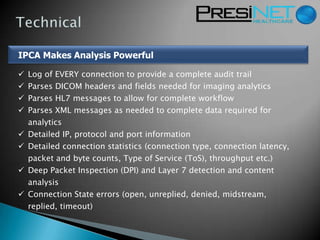
The document outlines a vendor-neutral, standards-based approach to imaging analytics using Intelligent Protocol Content Analysis (IPCA), which facilitates near real-time data processing without bandwidth impacts. This technology enables efficient parsing of DICOM, HL7, and XML data, thus minimizing the need for costly interface development while providing comprehensive radiology network performance analytics. Additionally, it offers real-time monitoring, connection statistics, and automated reporting to enhance operational efficiency in radiology workflows.