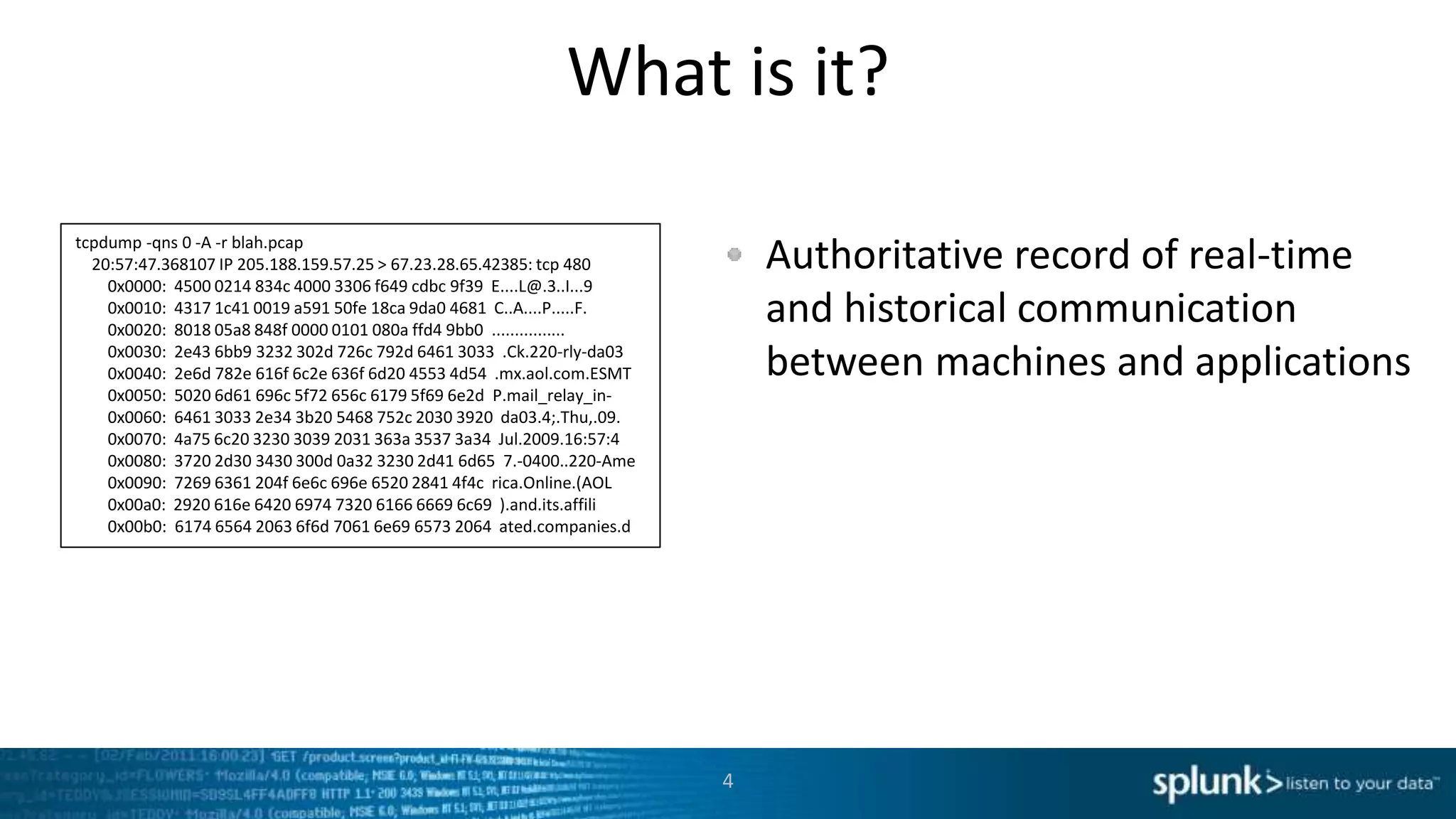
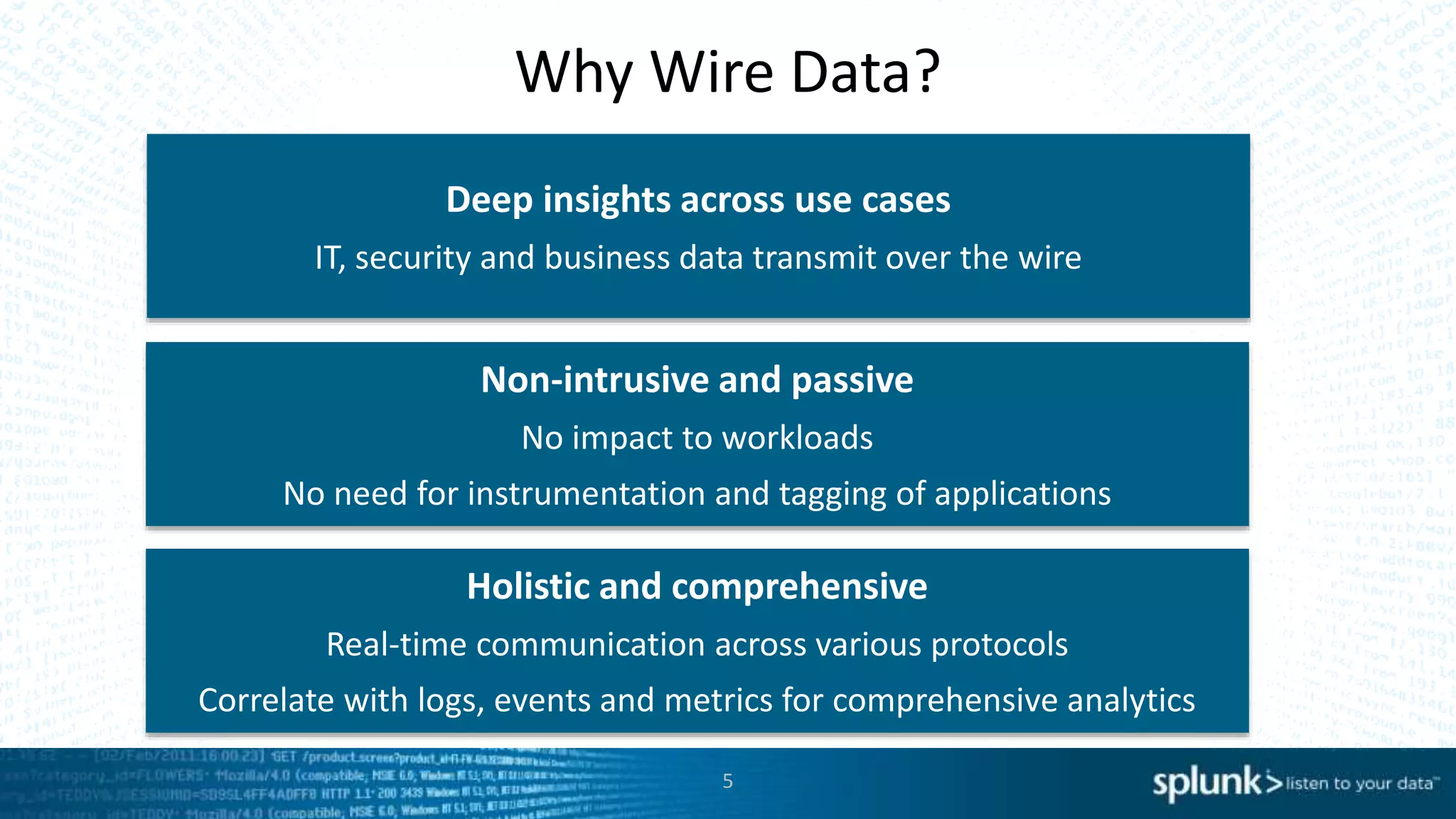
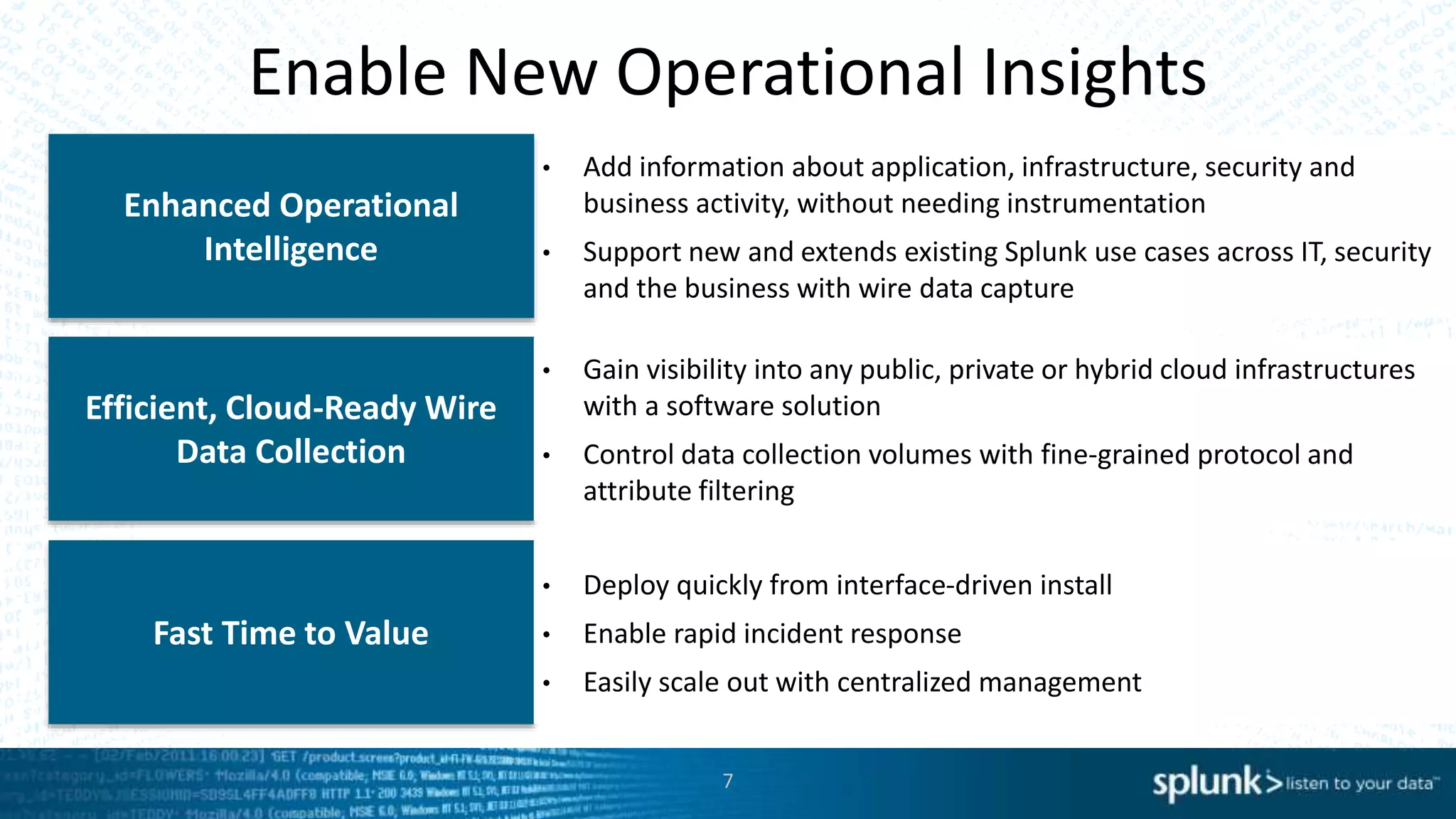
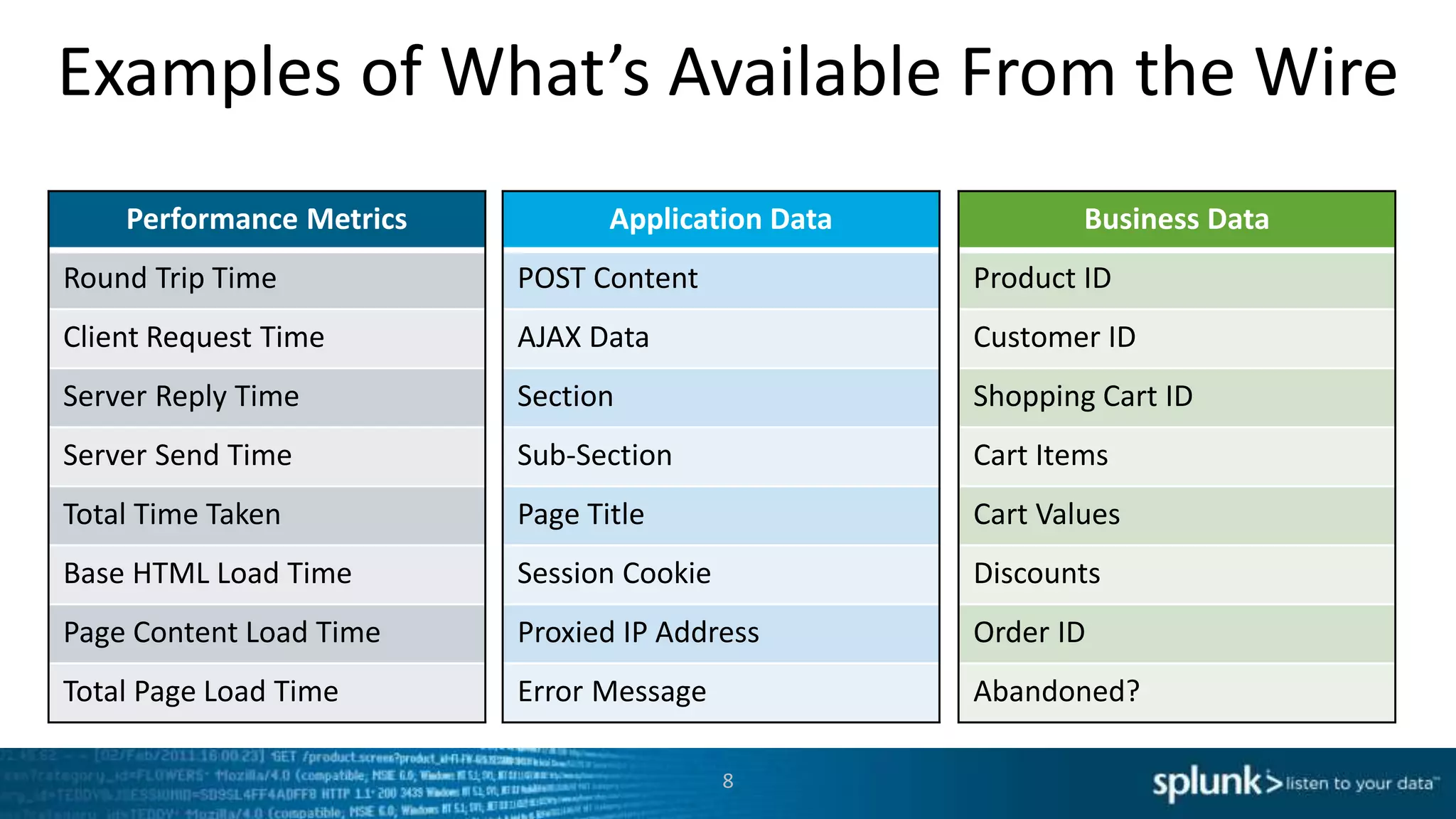
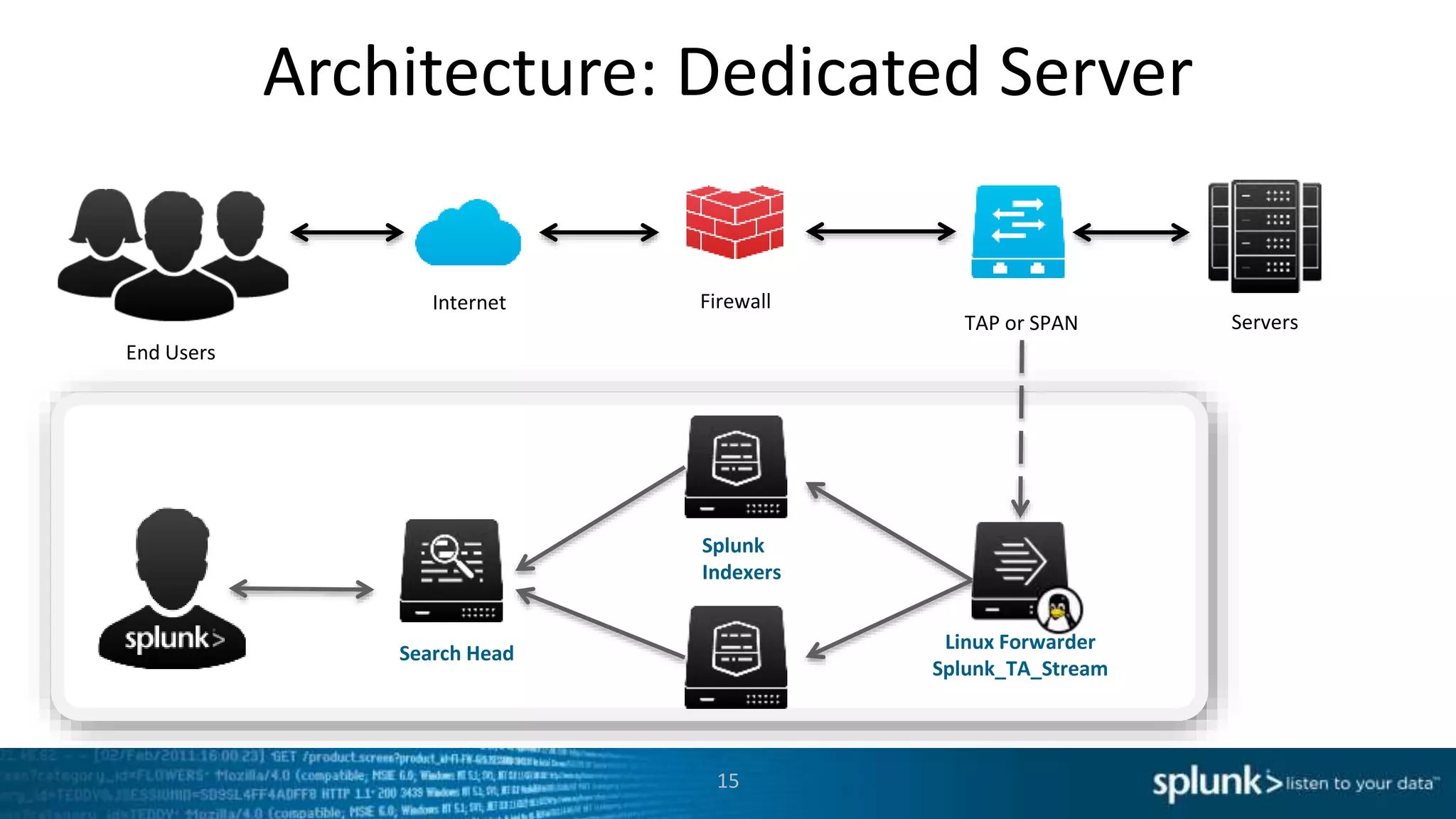
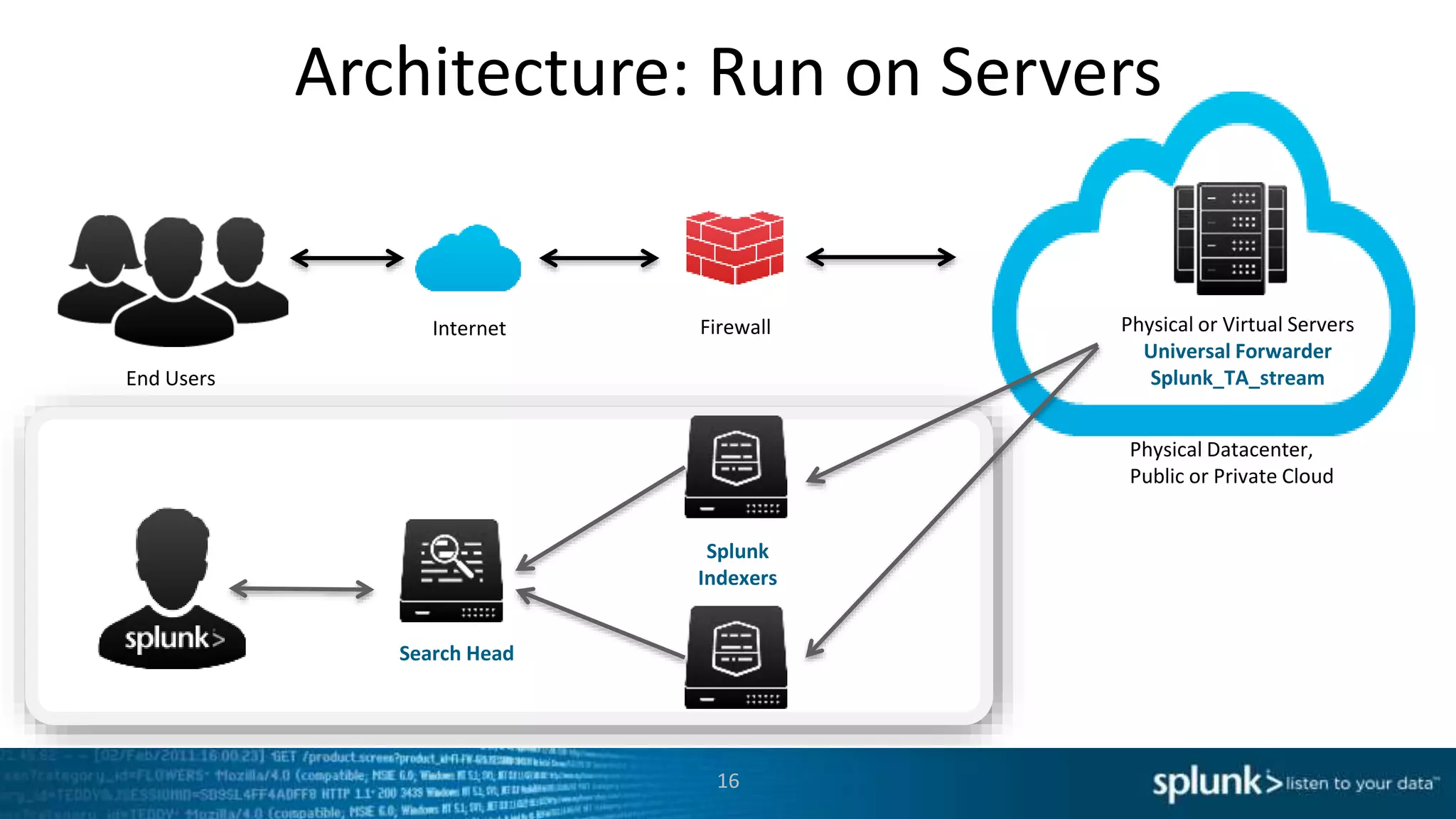
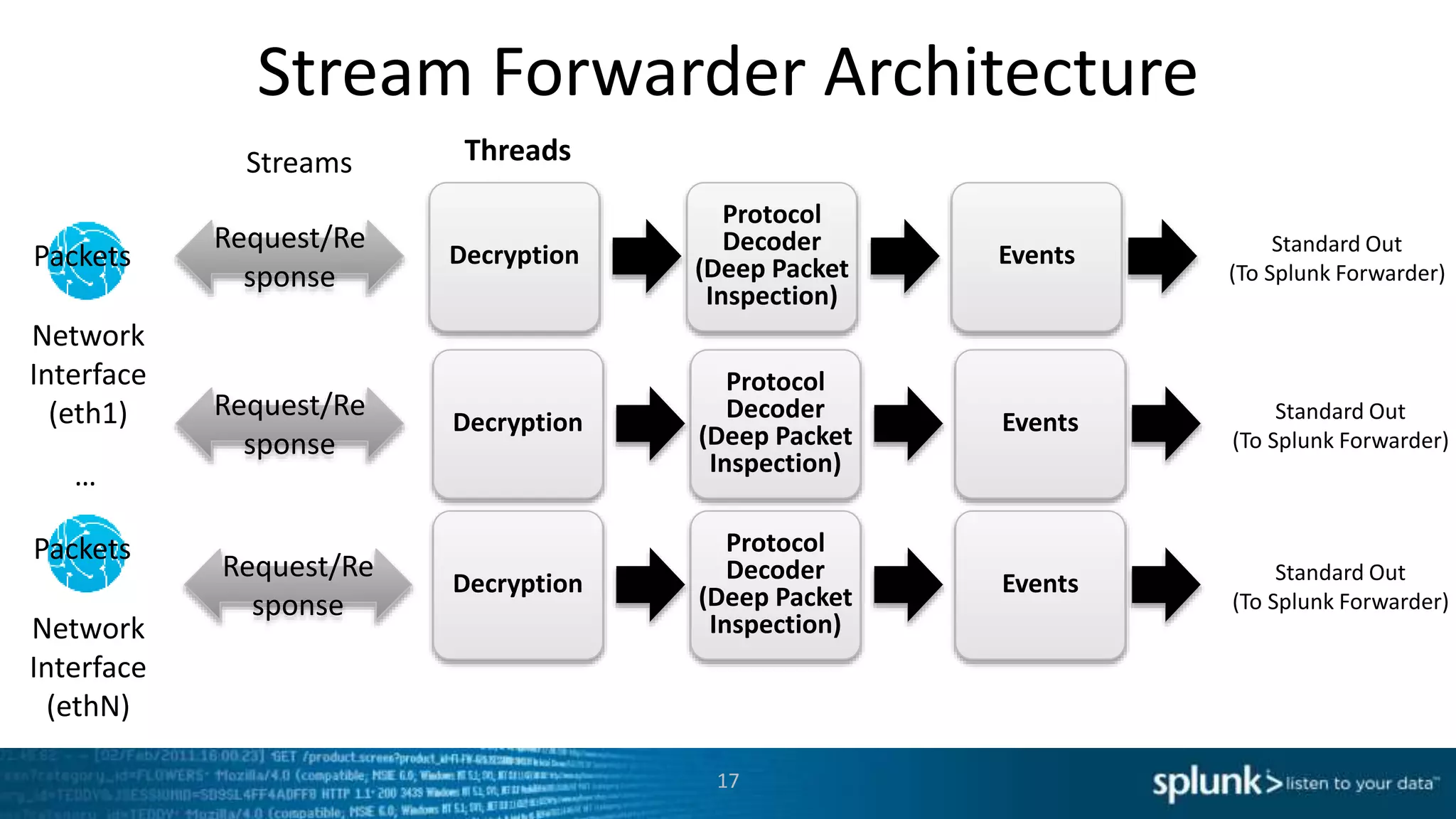
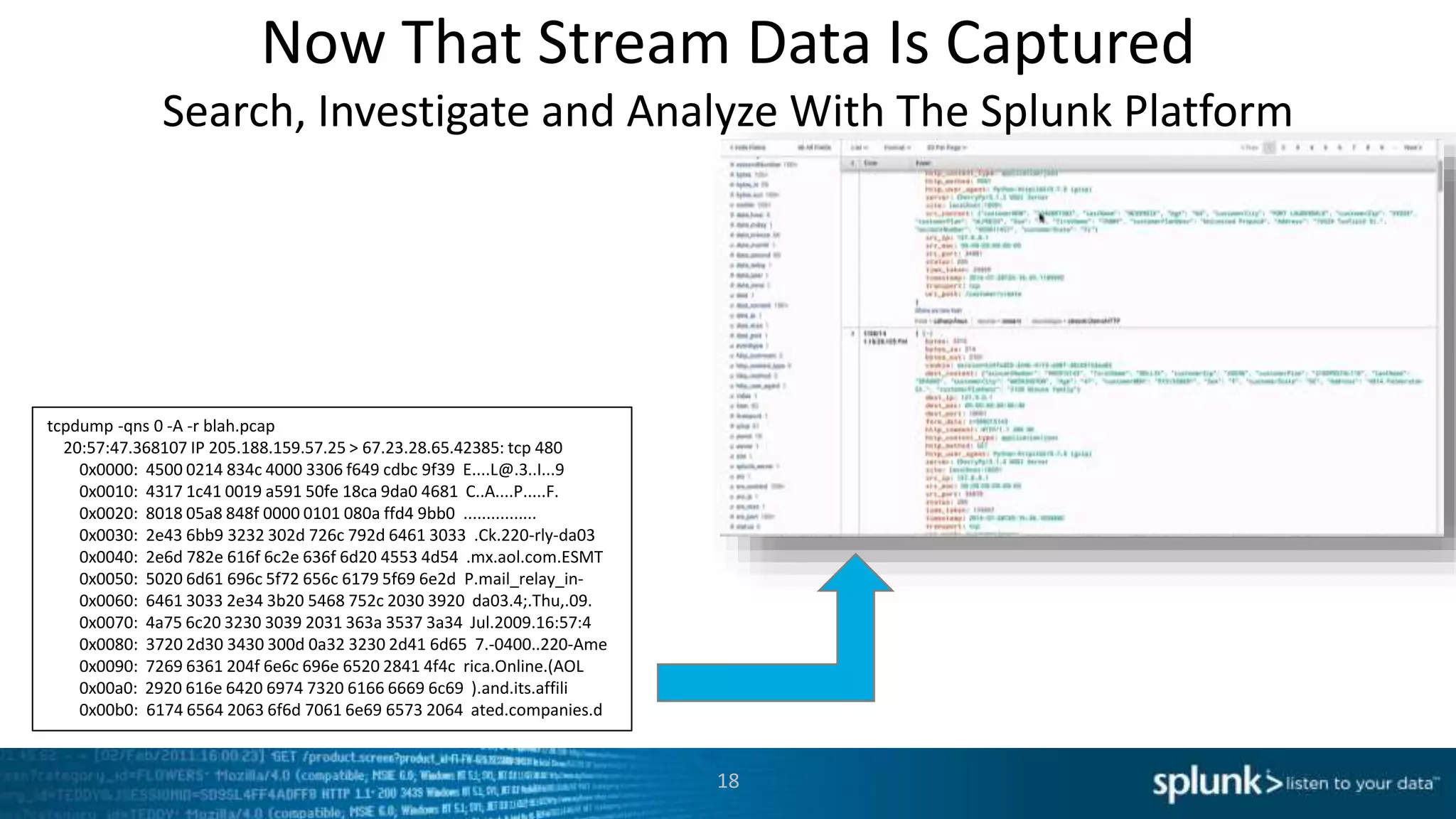
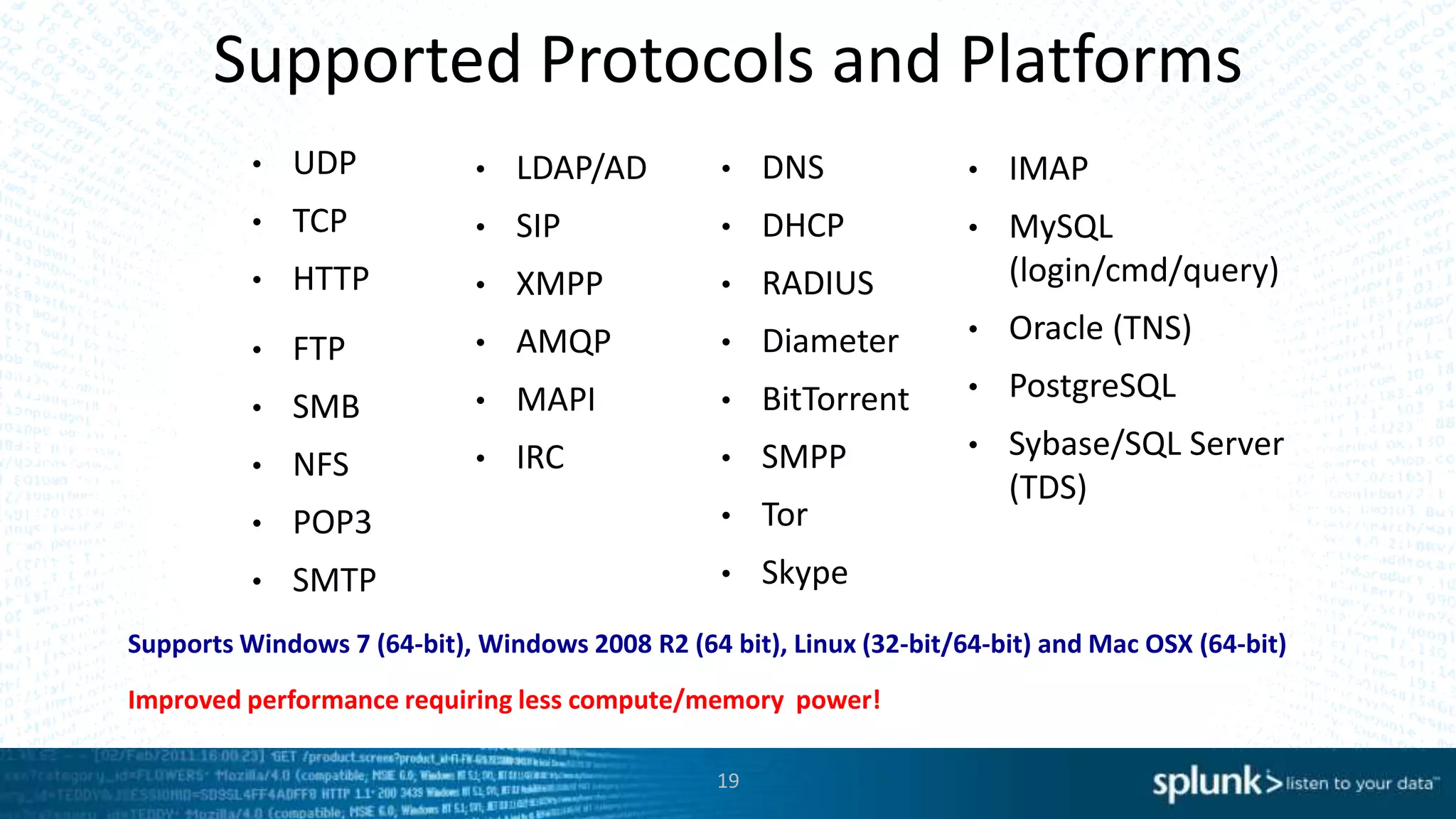
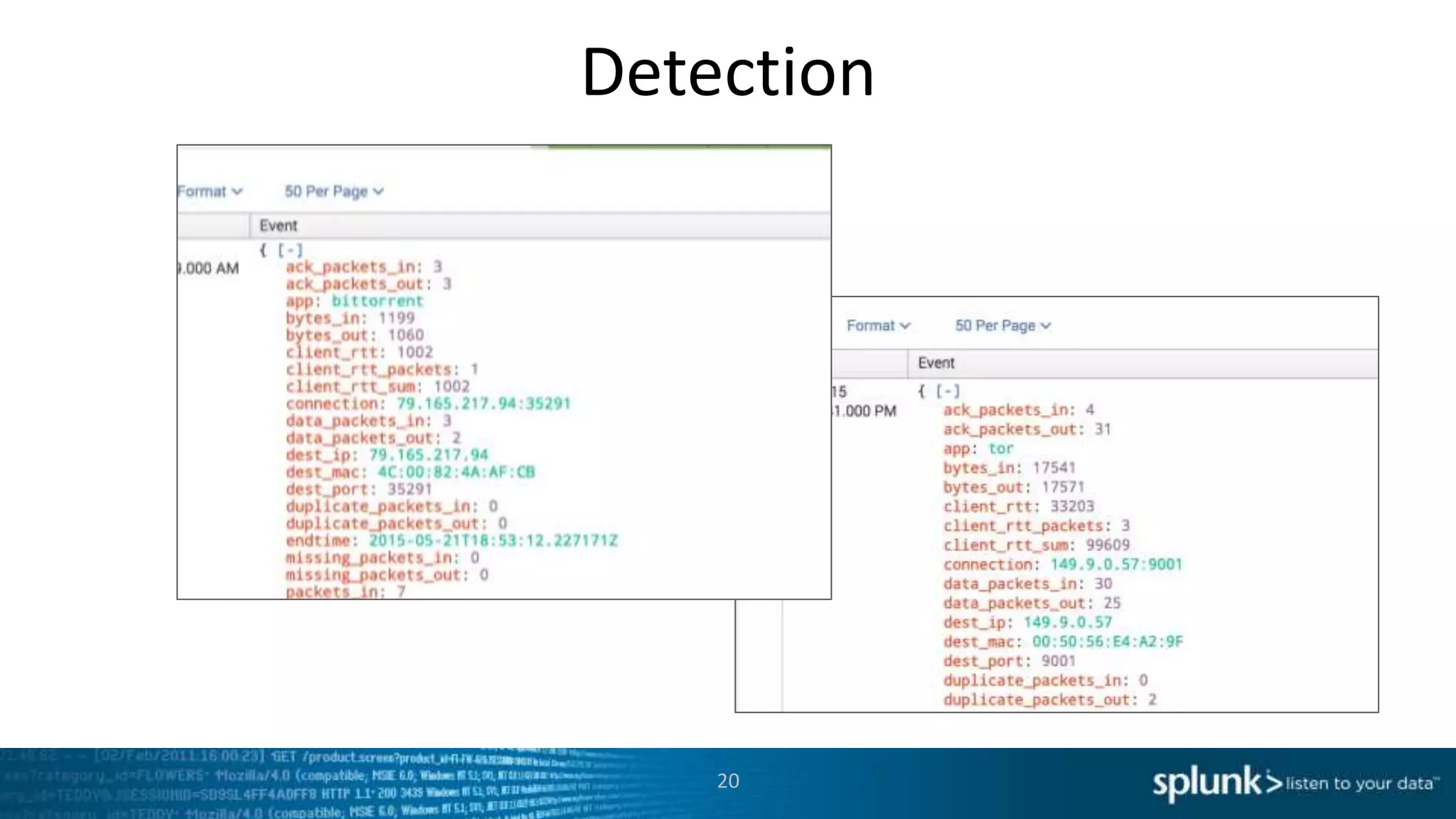
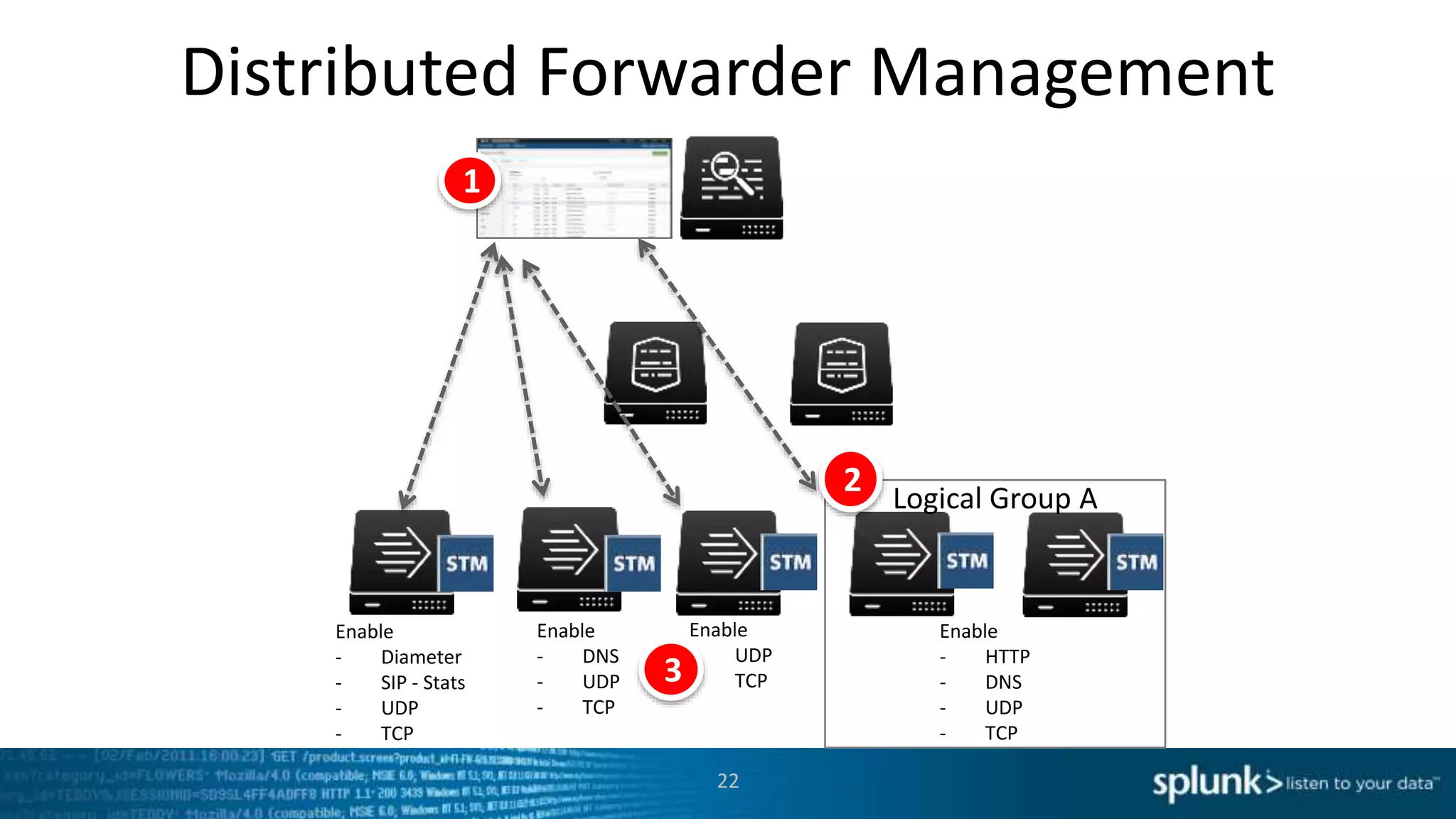
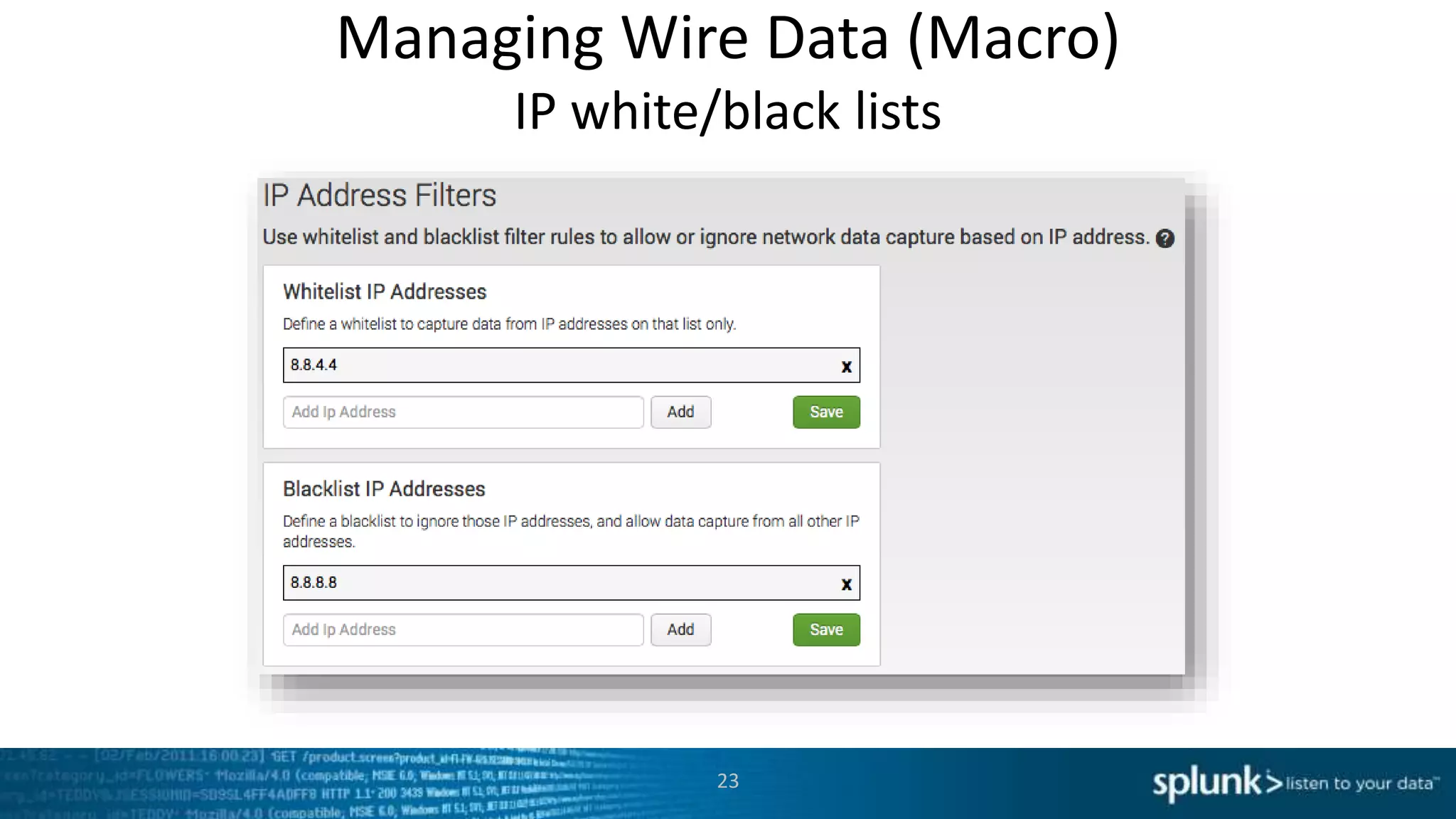
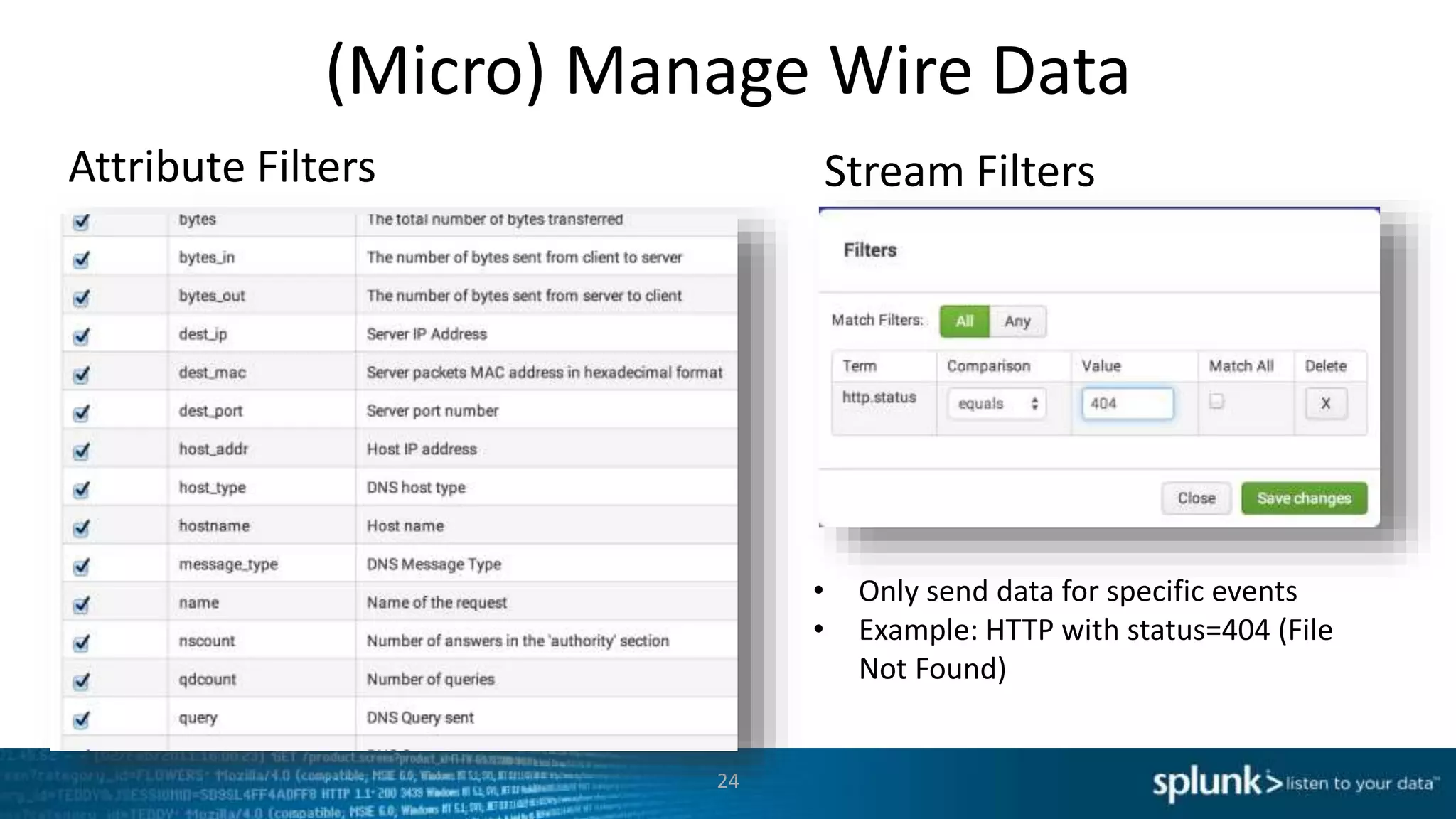
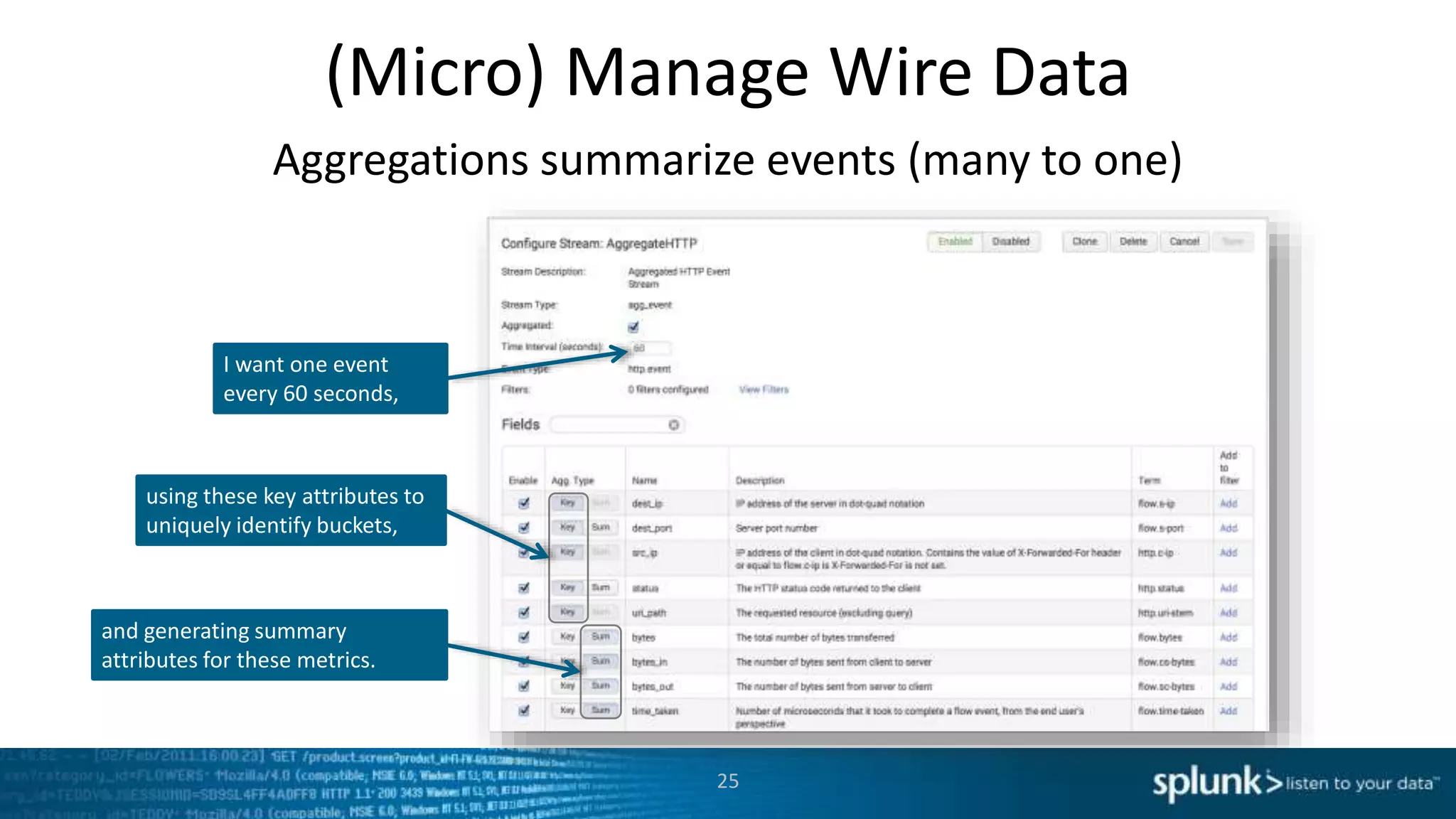
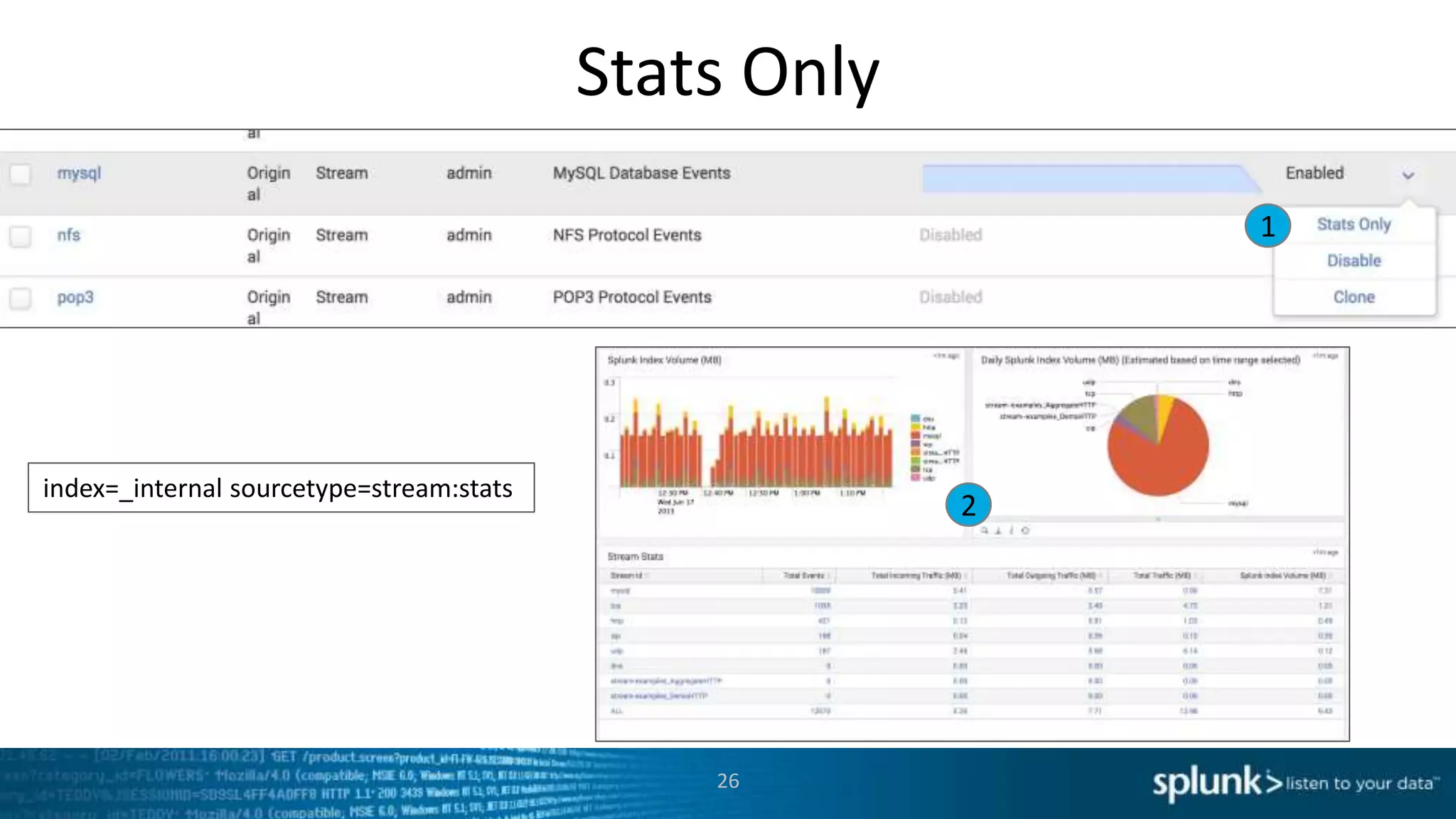
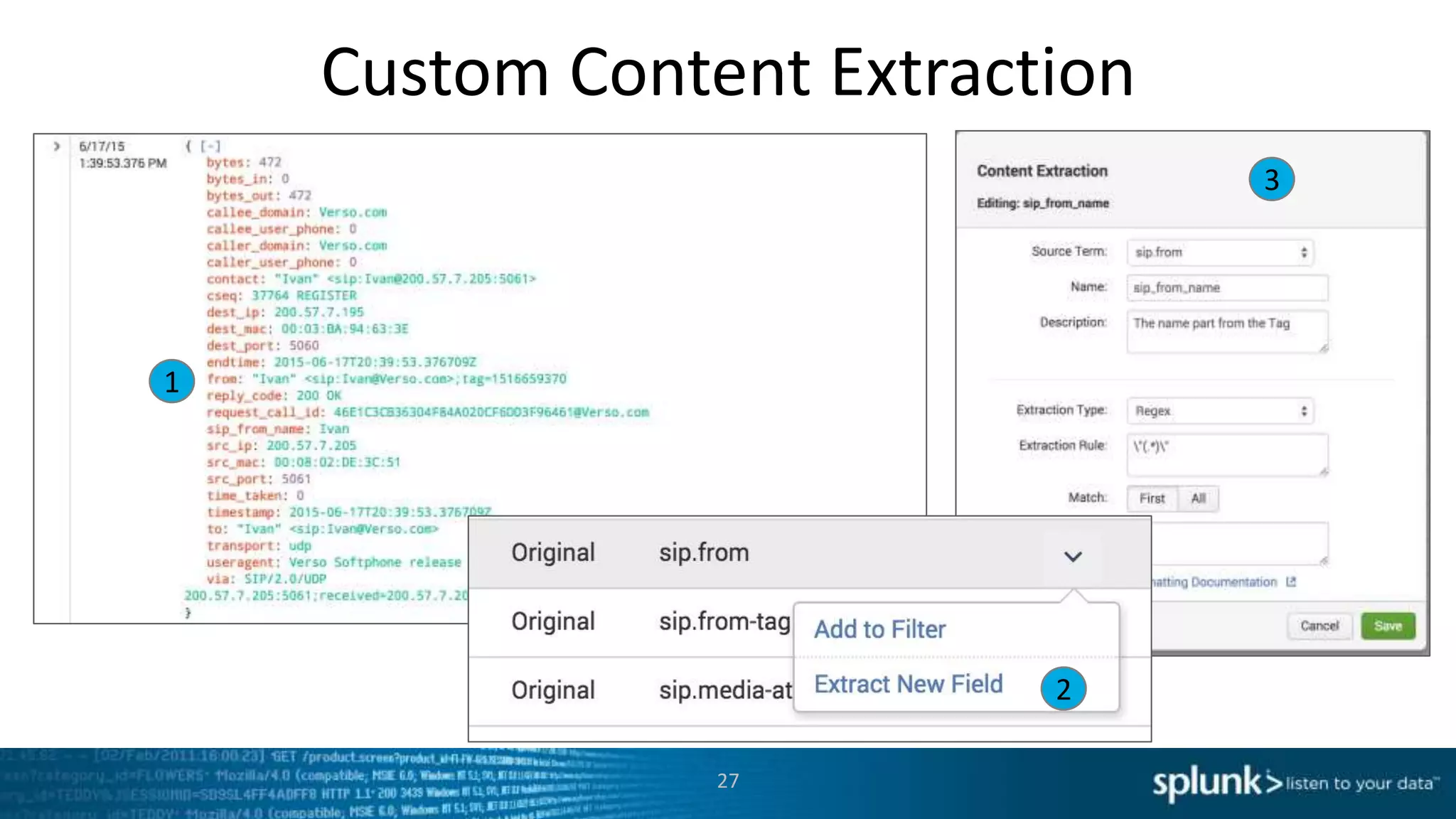
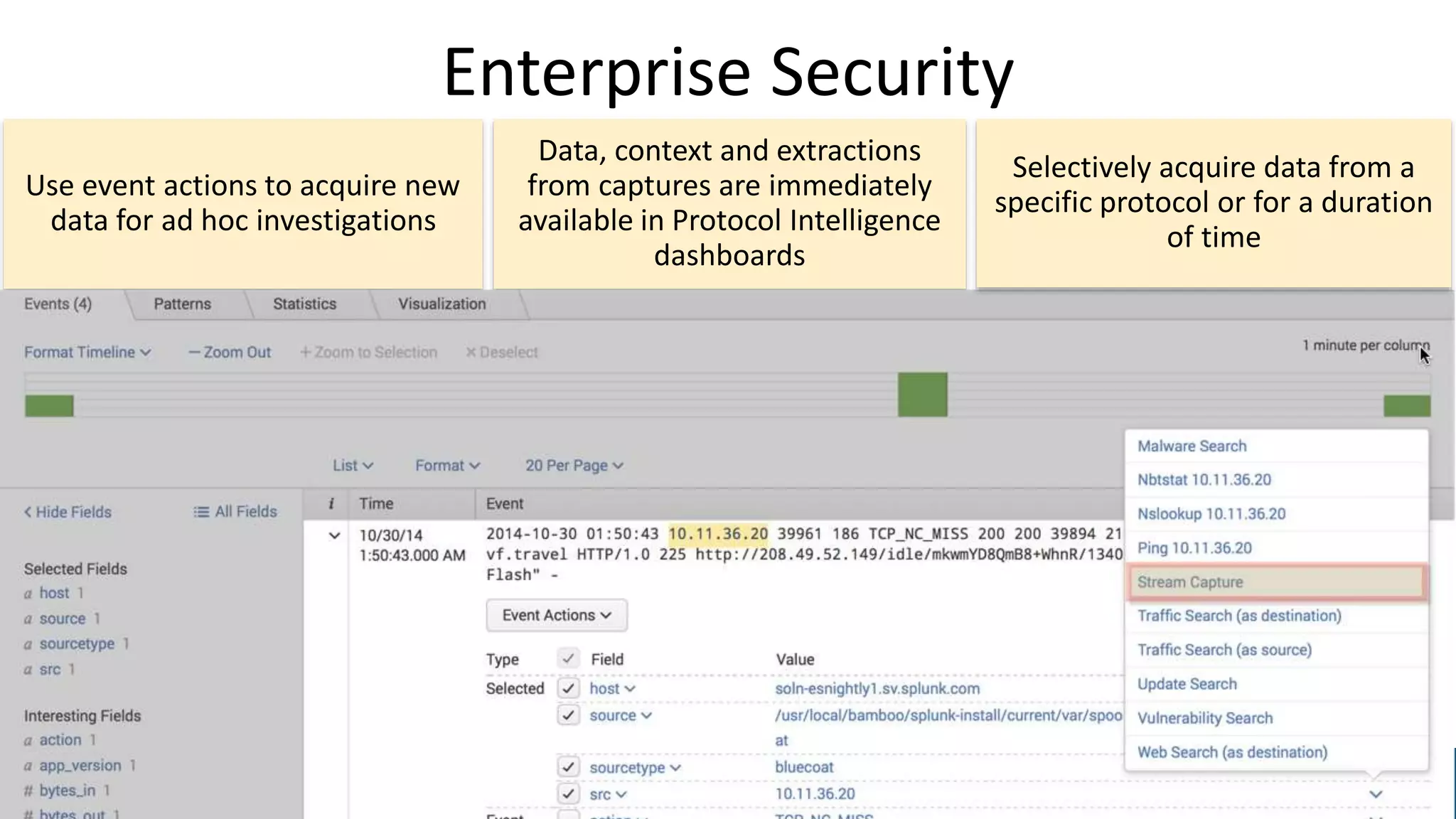
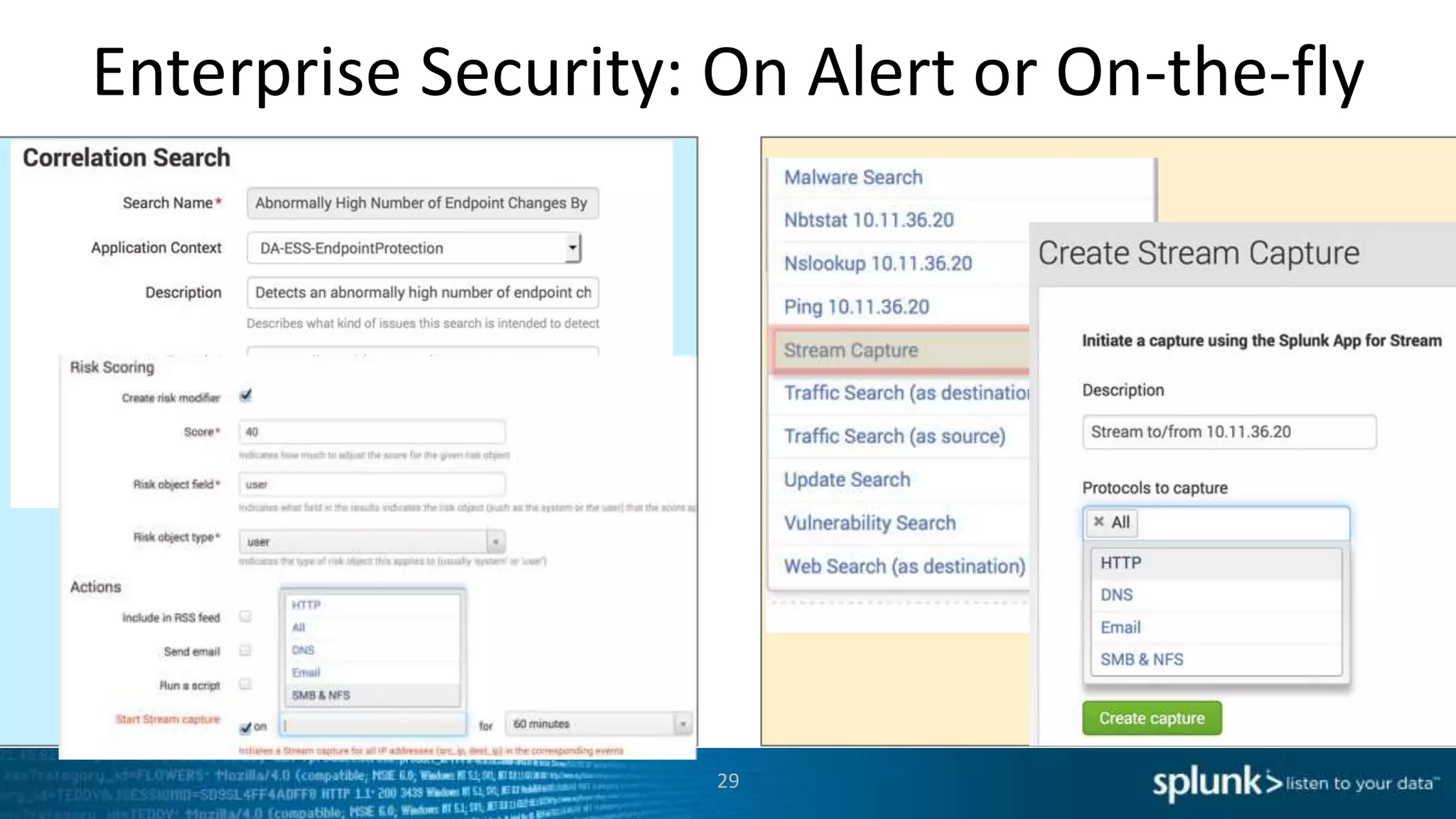
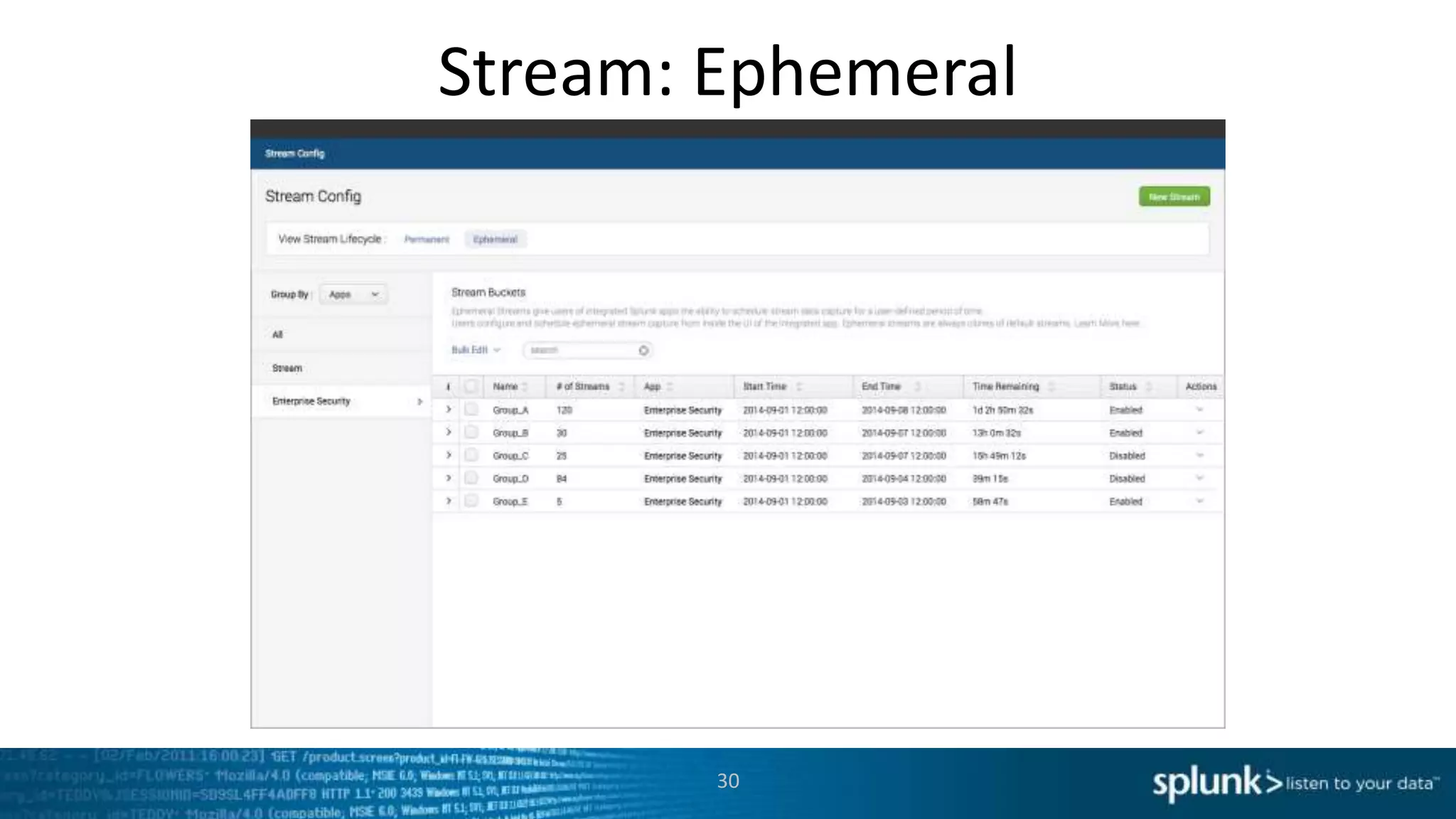
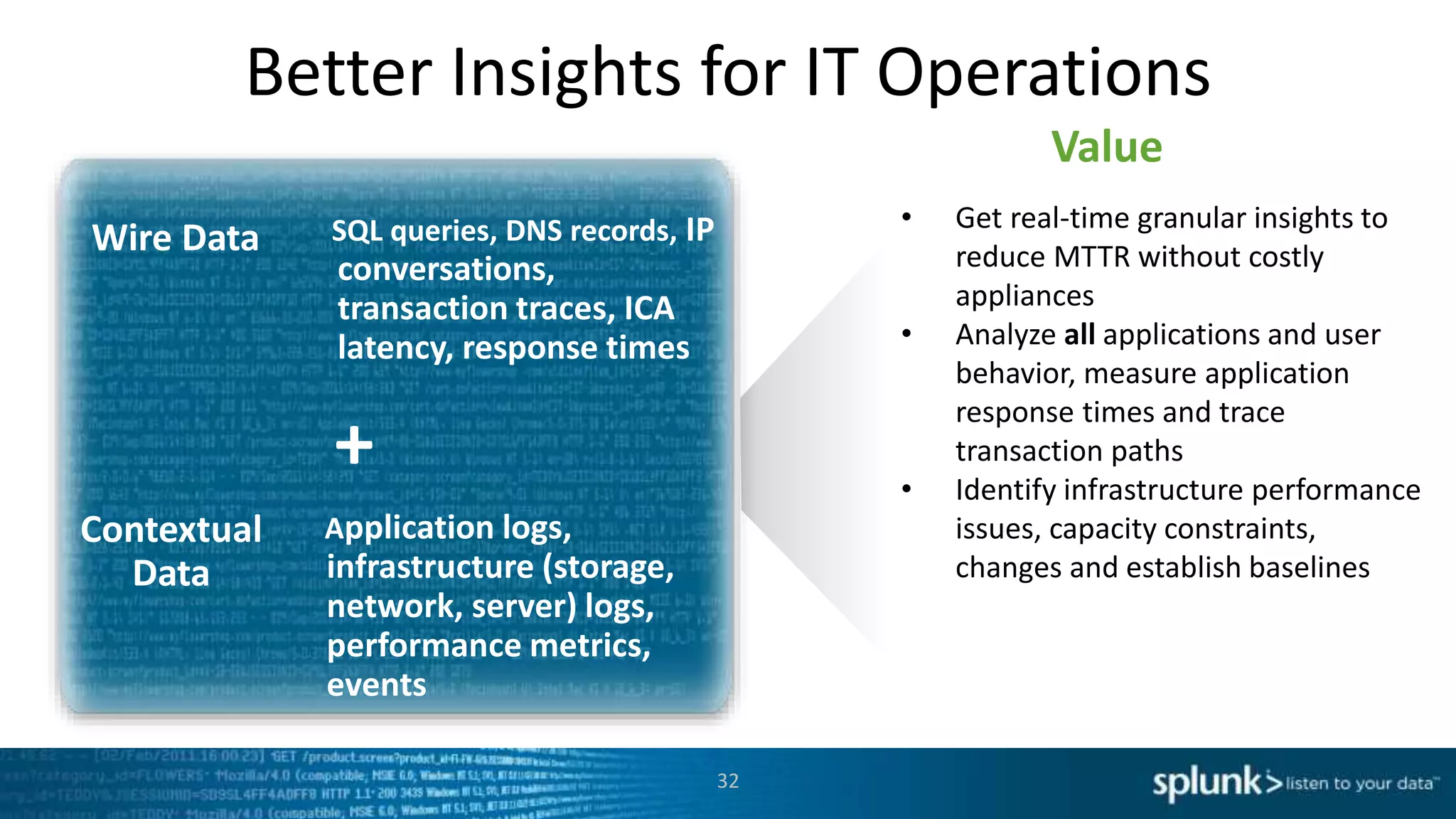
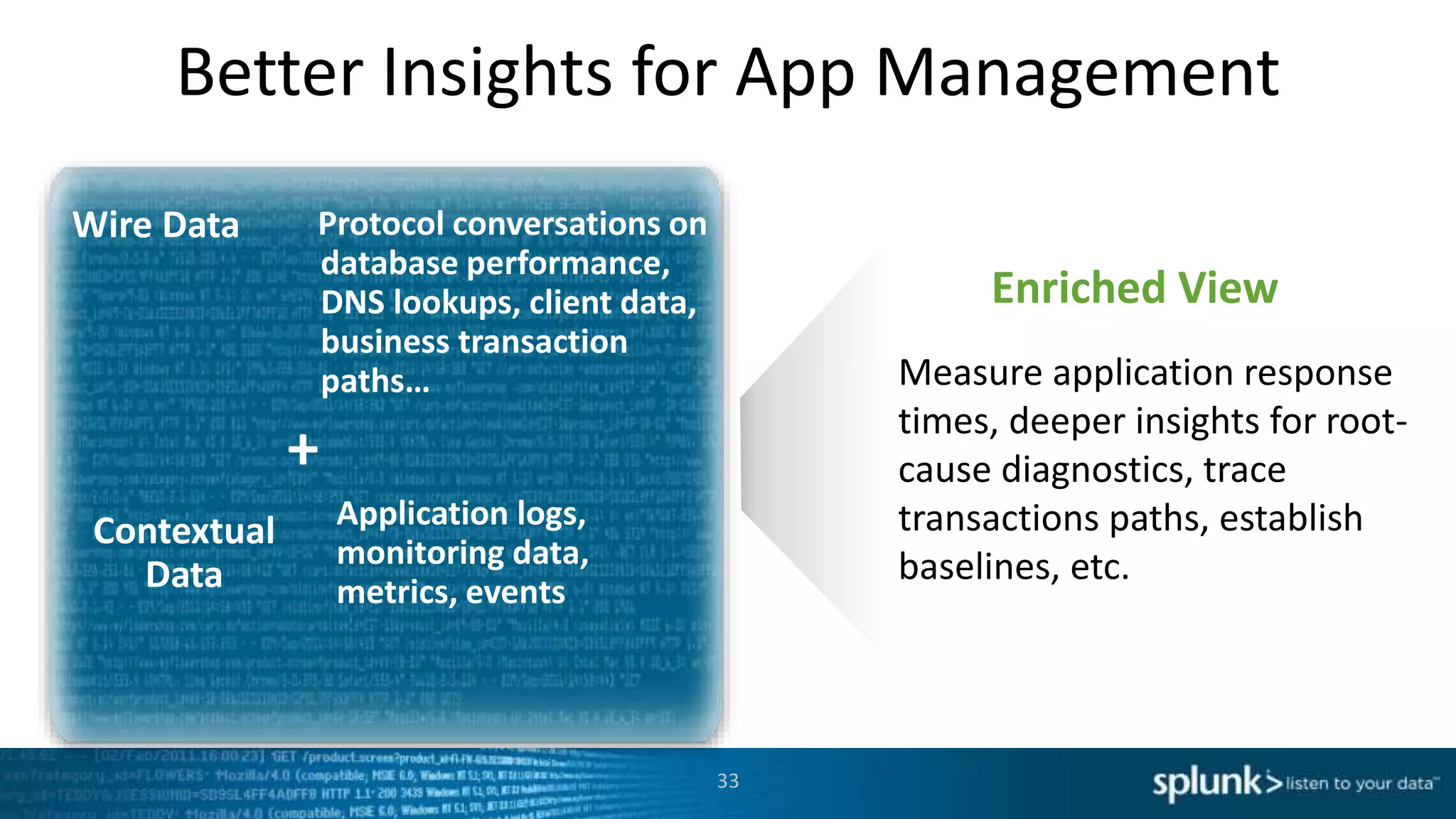
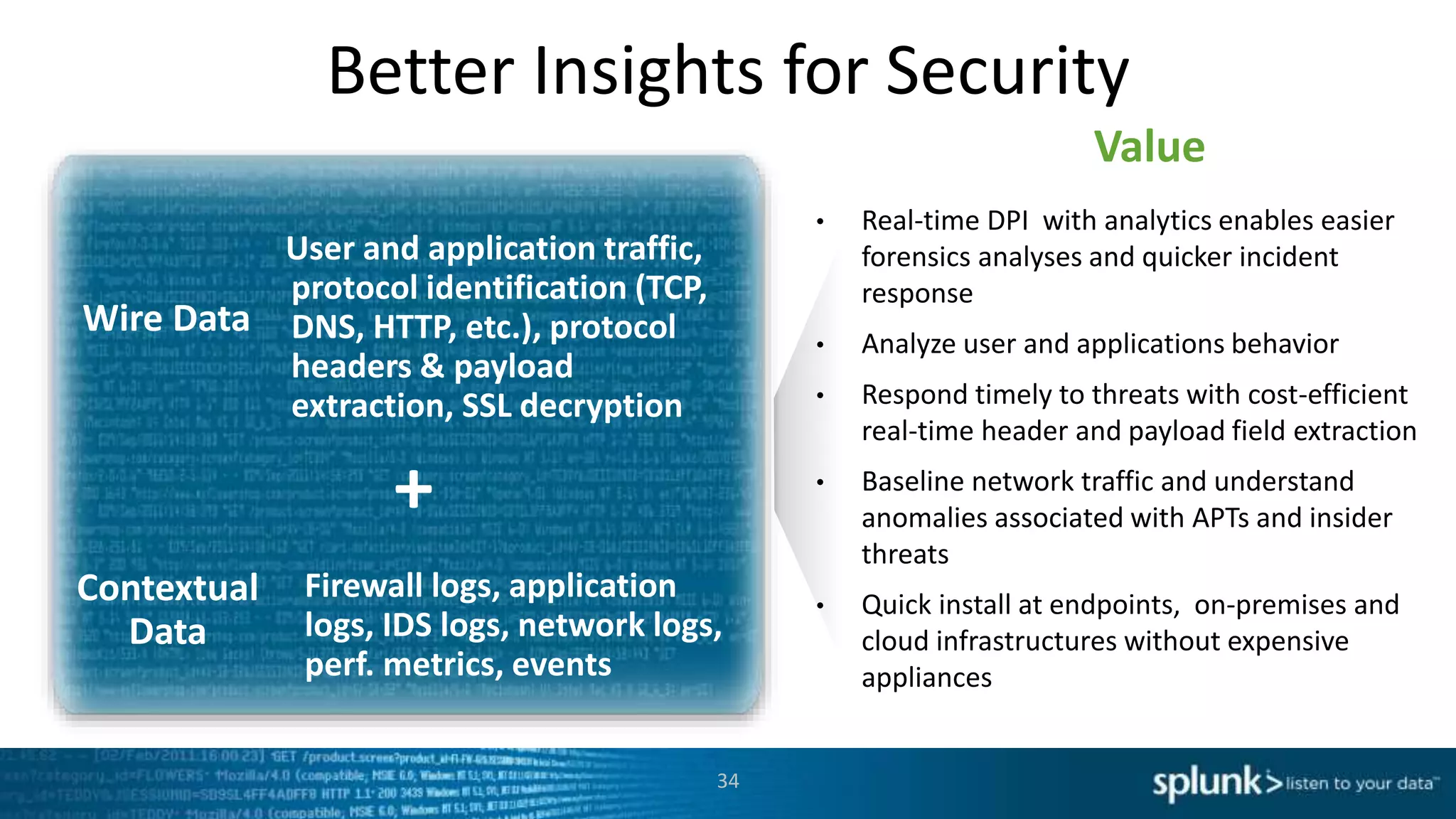
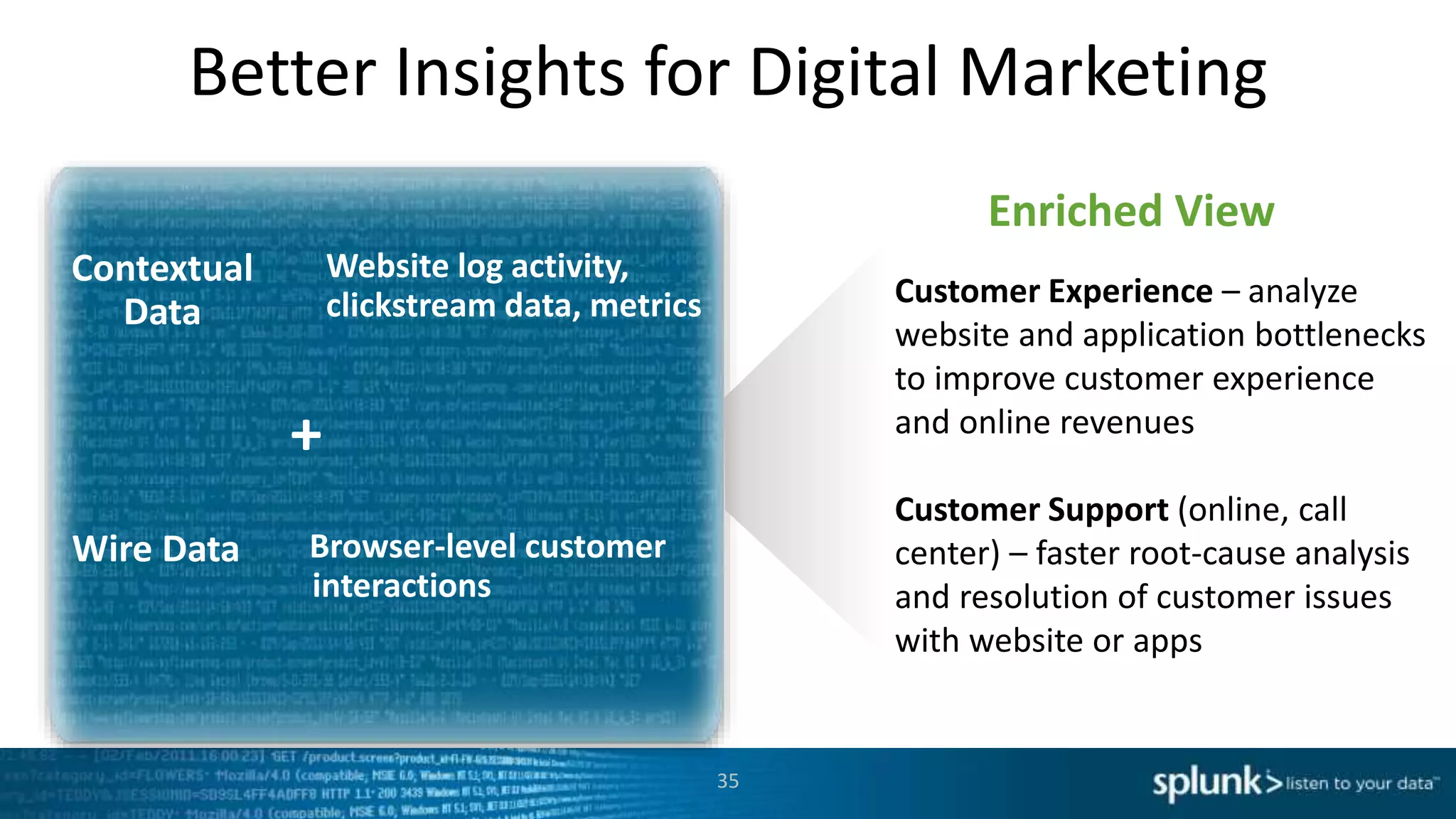
Wire data provides deep insights across IT, security and business use cases by capturing the communications transmitted over the wire between machines and applications in real-time. The Splunk App for Stream enables new operational intelligence by indexing this wire data without needing instrumentation. It provides enhanced visibility, efficient cloud-ready collection, and fast time to value through interface-driven deployment. Key features include protocol decoding, attribute filtering, aggregations, and custom content extraction for analysis in Splunk.