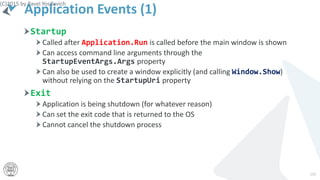
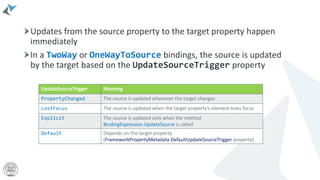
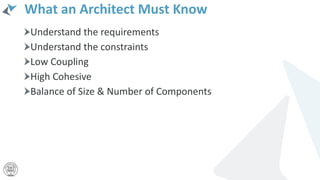
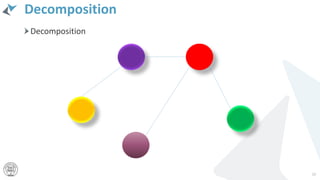
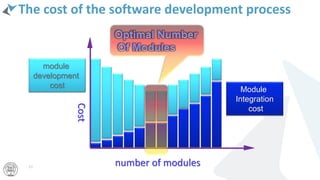
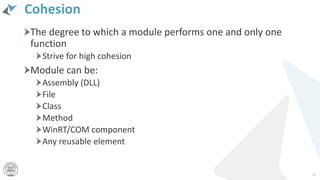
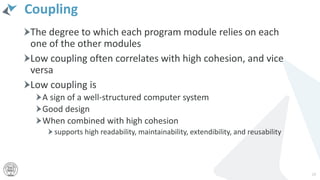
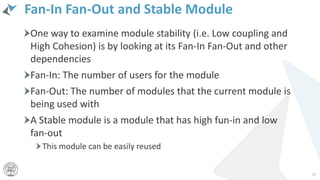
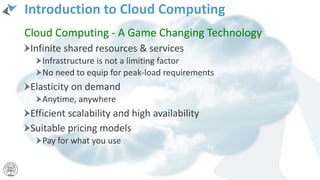
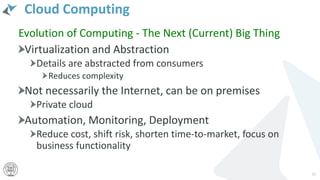
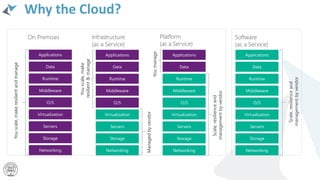
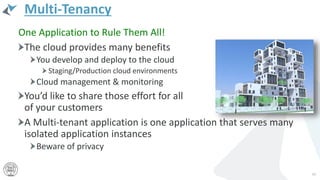
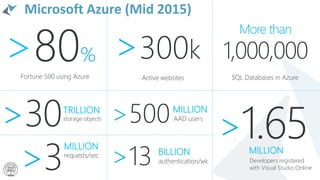
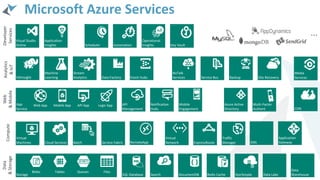
The document is a comprehensive guide to Microsoft Azure and Windows 10 development, outlining cloud concepts, Azure infrastructure, and app development practices. It emphasizes the benefits of cloud computing, modern architecture principles, and the importance of high cohesion and low coupling in software design. Additionally, it discusses tools like Azure App Service and various Azure services that facilitate building scalable applications across different platforms.















































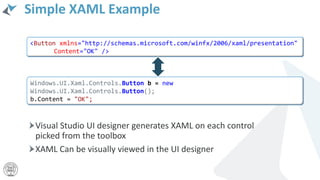

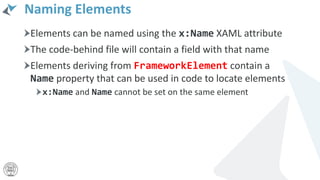
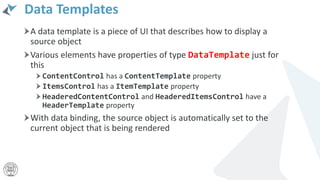
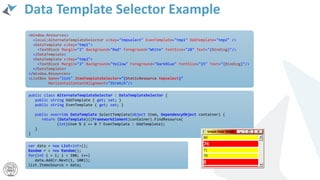
![Parsing and Using XAML
Visual Studio compiles the XAML file to BAML (Binary XAML) and
embeds it as a resource
The BAML is parsed at runtime and the object tree created by the
InitializeComponent method of the parent’s element class
[GeneratedCodeAttribute("Microsoft.Windows.UI.Xaml.Build.Tasks"," 14.0.0.0")]
[global::System.Diagnostics.DebuggerNonUserCodeAttribute()]
public void InitializeComponent()
{
if (_contentLoaded)
return;
_contentLoaded = true;
Uri resourceLocator = new Uri("ms-appx:///MainPage.xaml");
Application.LoadComponent(this, resourceLocator,
ComponentResourceLocation.Application);
{](https://image.slidesharecdn.com/introductiontothemicrosoftazurecloud-230217001604-79275b14/85/Introduction-to-the-Microsoft-Azure-Cloud-pptx-148-320.jpg)