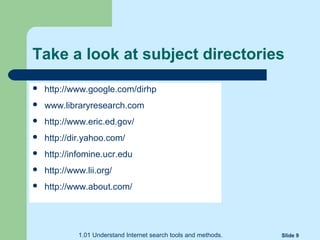
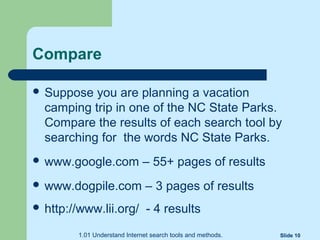
This document discusses different types of internet search tools, including search engines and subject directories. It describes how individual search engines like Google use "spiders" to match keywords to webpages, while meta-search engines compile results from multiple search engines. Subject directories are maintained by humans to categorize and describe information within specific subjects. They provide a more reliable search than engines but fewer results. Examples are provided of popular search engines and subject directories to compare results.