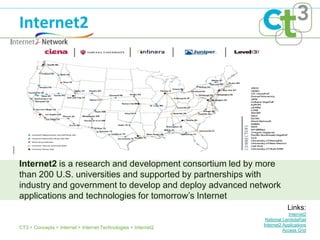
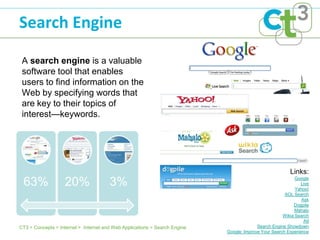
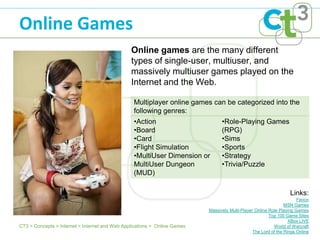
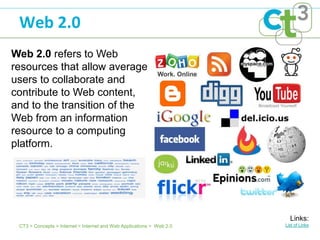
The document discusses various Internet and web technologies. It describes how the Internet is a network of networks that provides services globally. It then discusses several key Internet technologies that enable information sharing over the Internet, including protocols like TCP/IP, hardware like routers, and software for various functions. Finally, it outlines several popular Internet and web applications for activities like searching, communications, education, news, and entertainment.