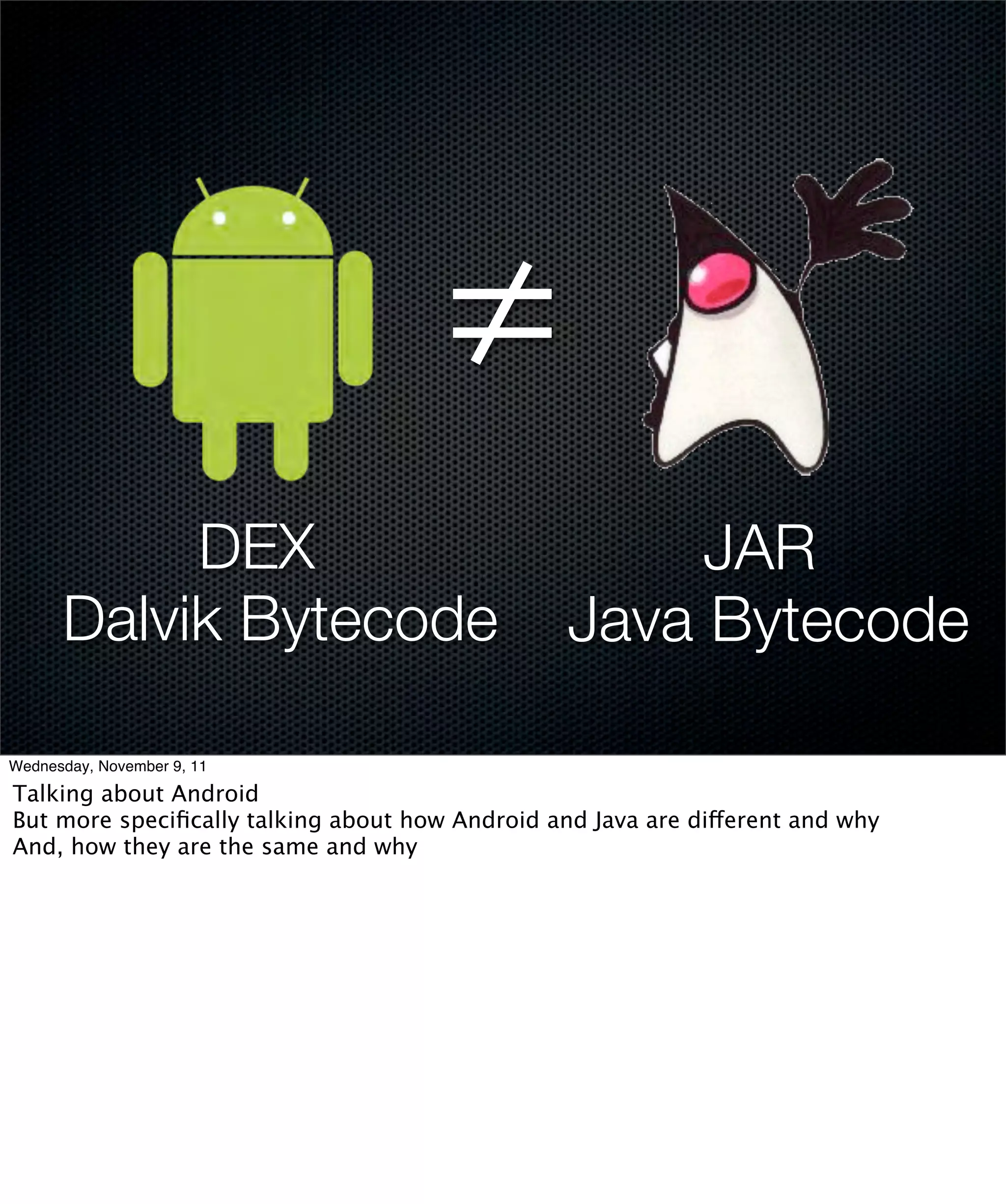
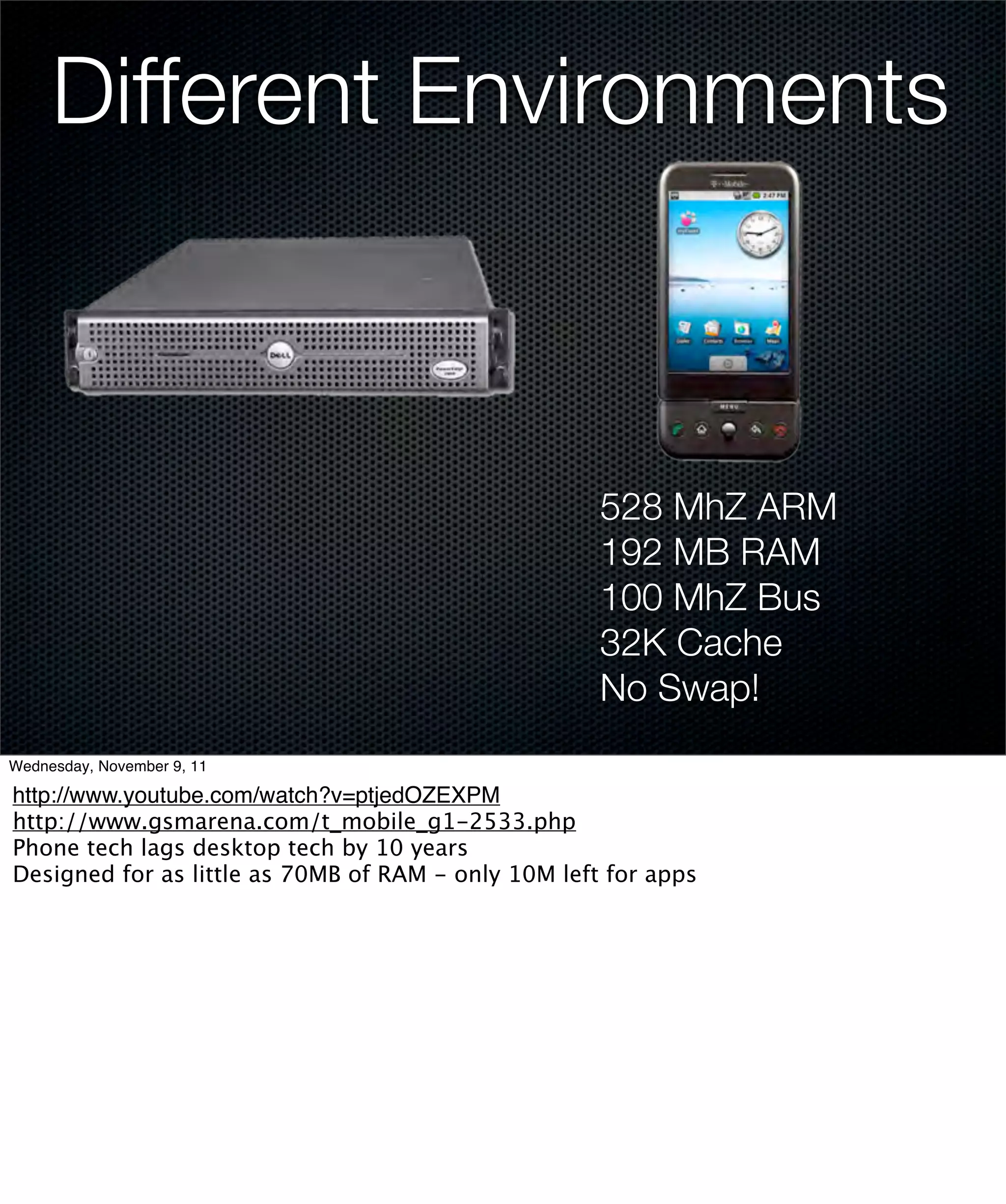
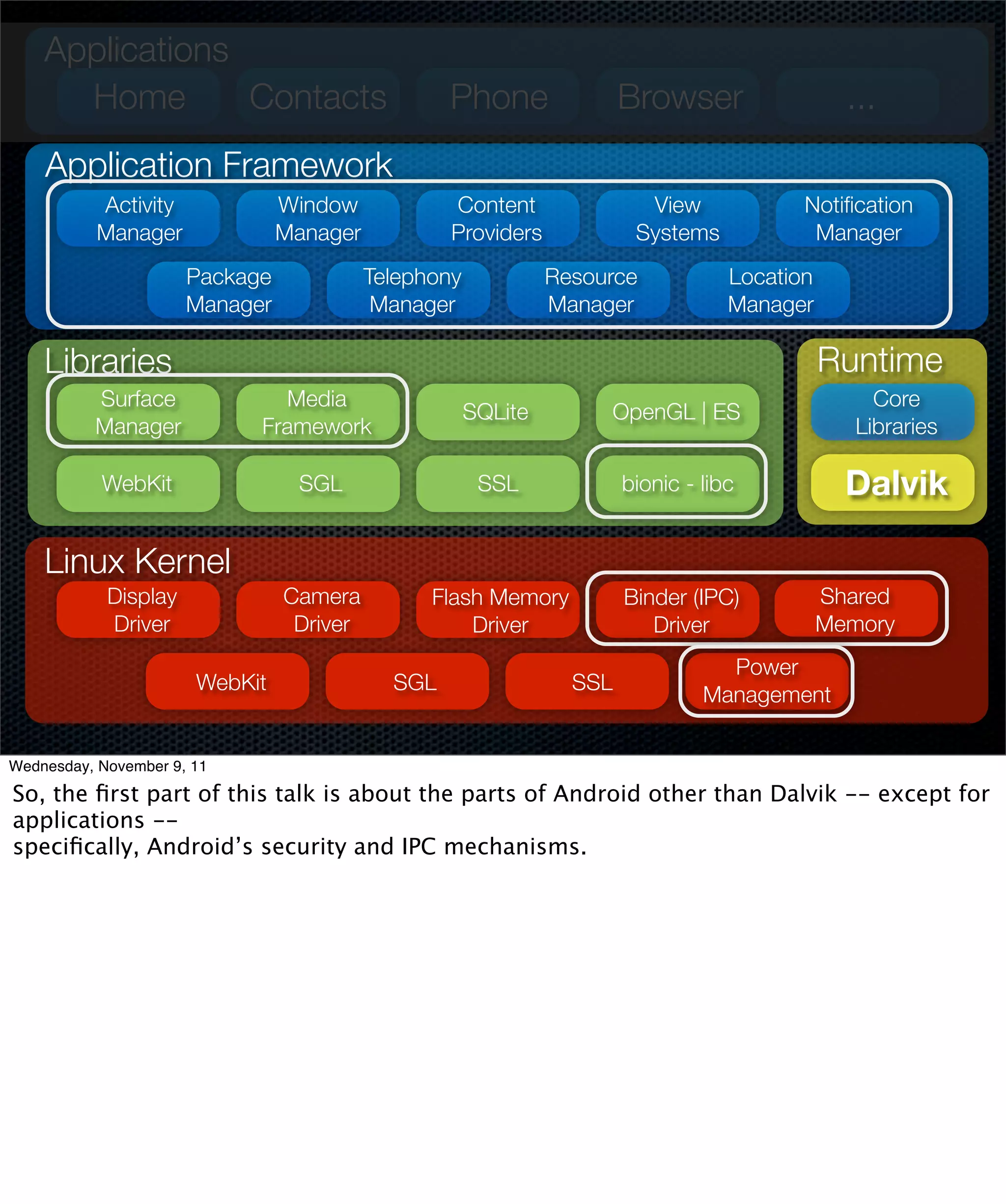
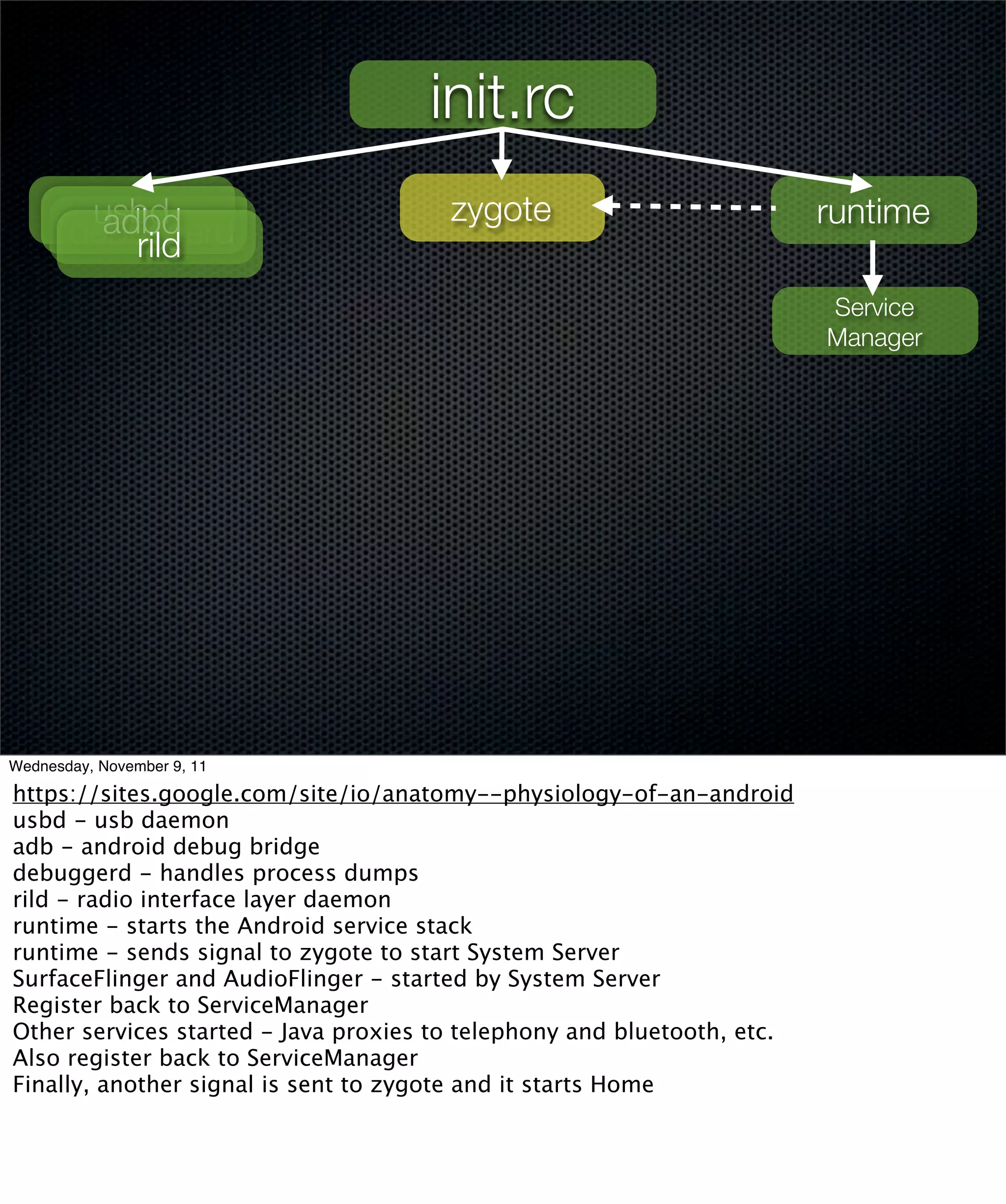
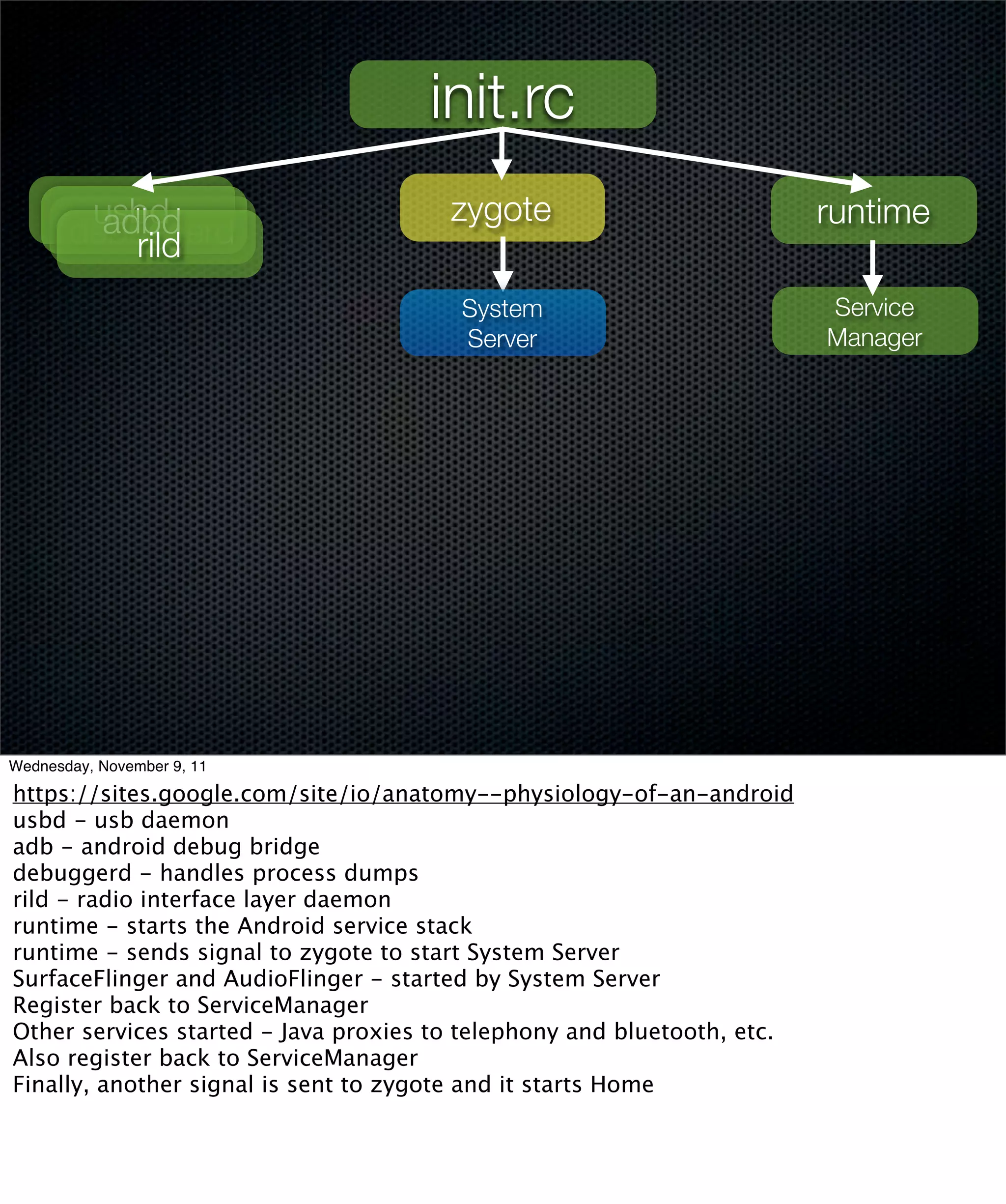
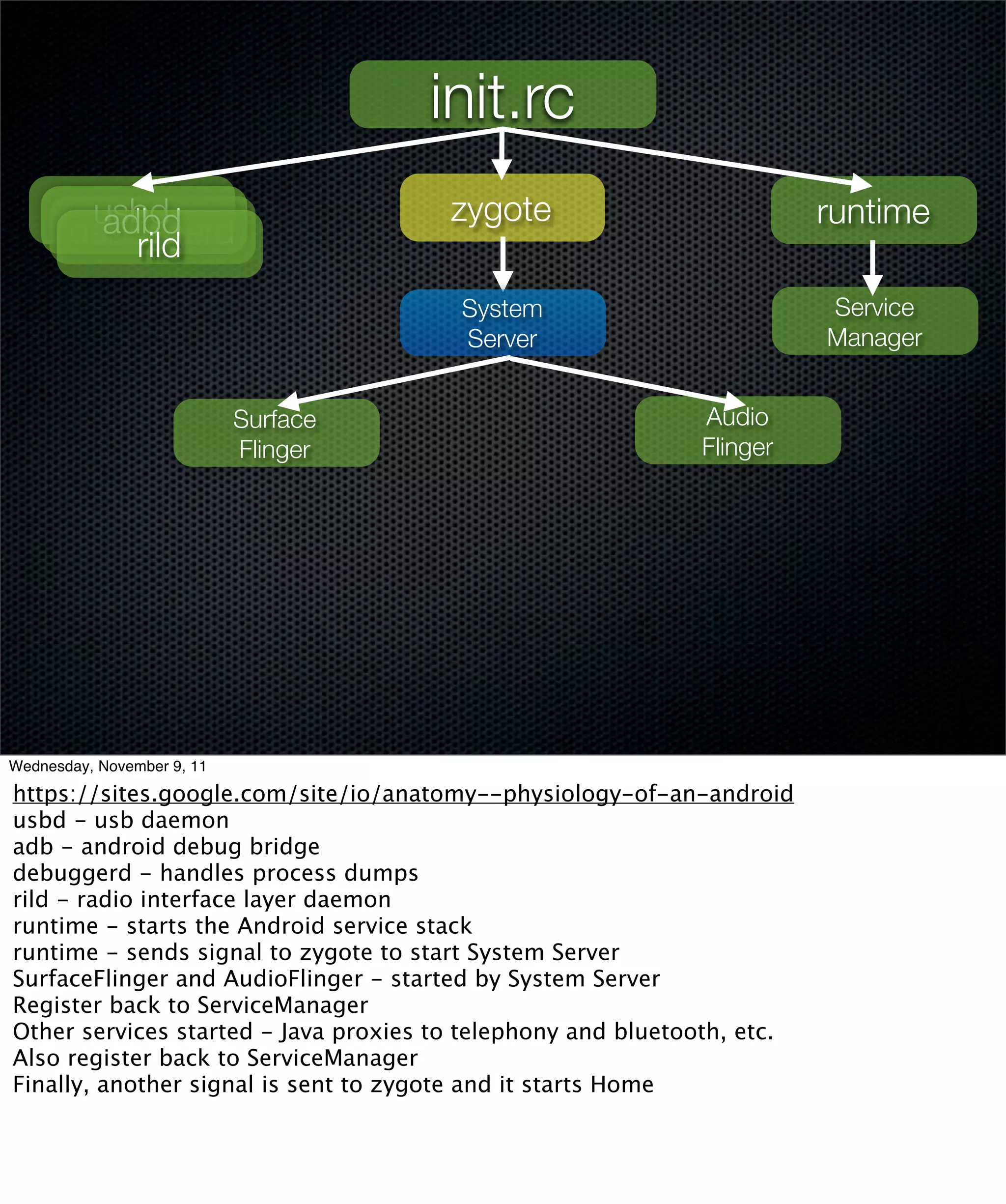
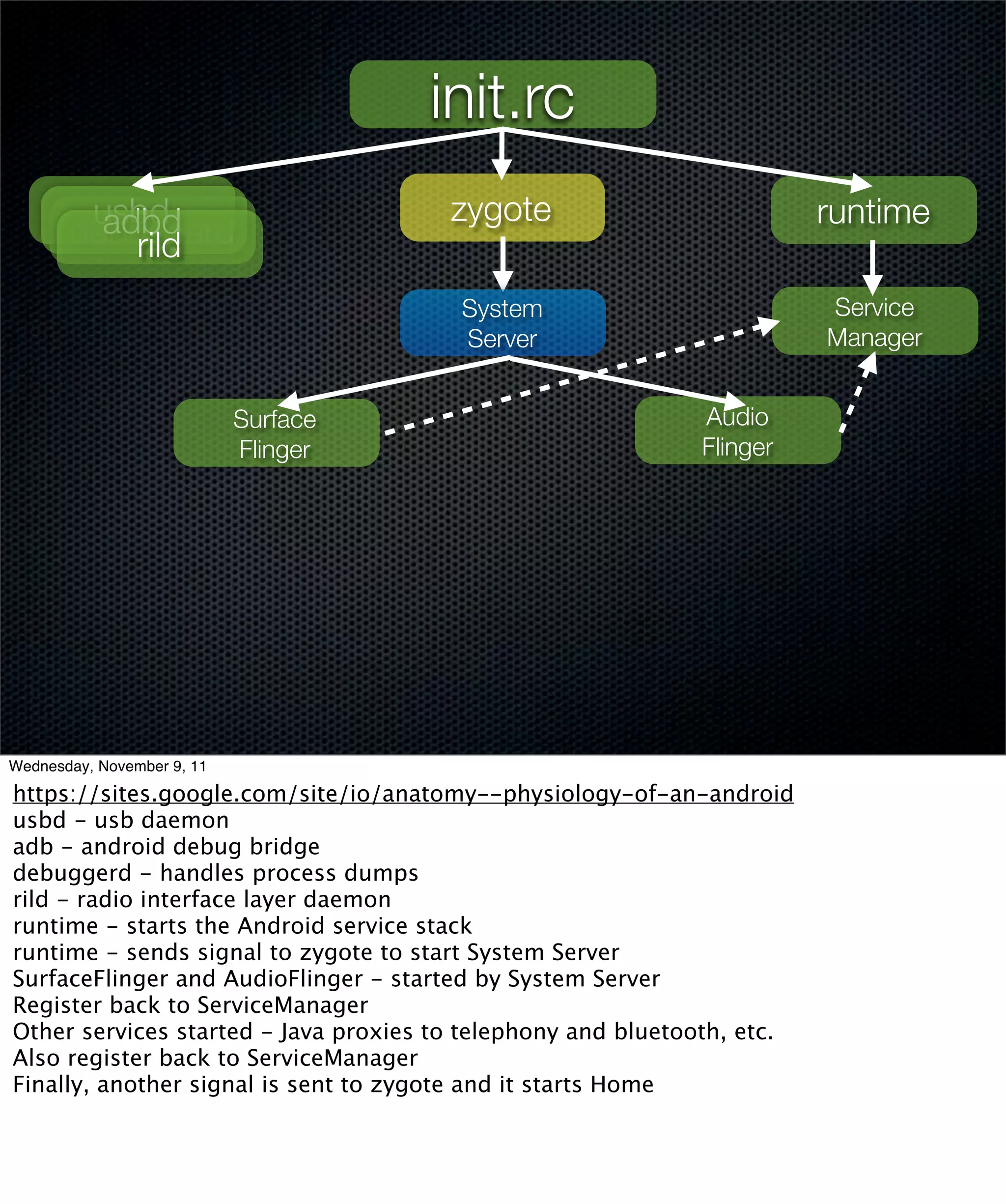
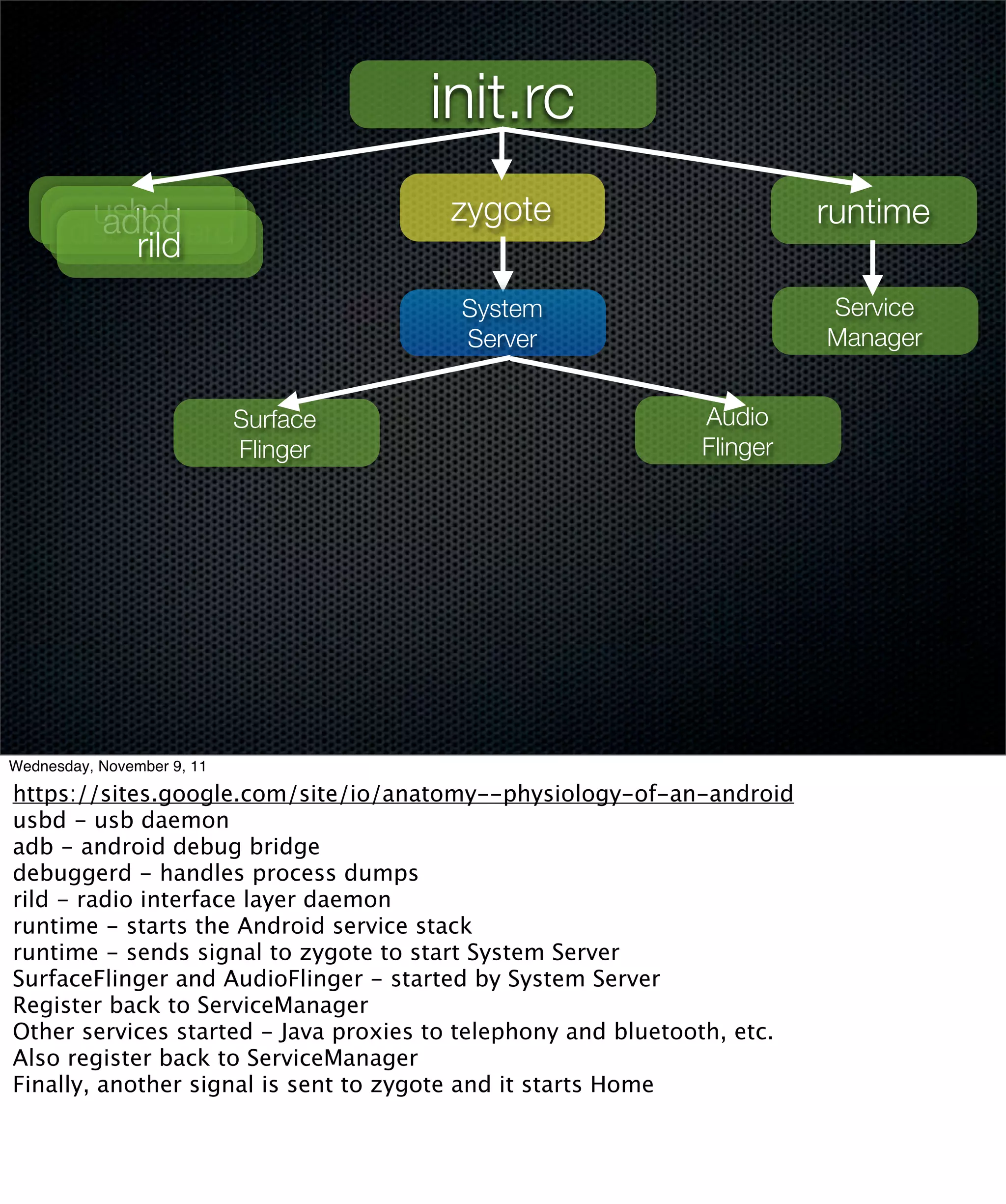
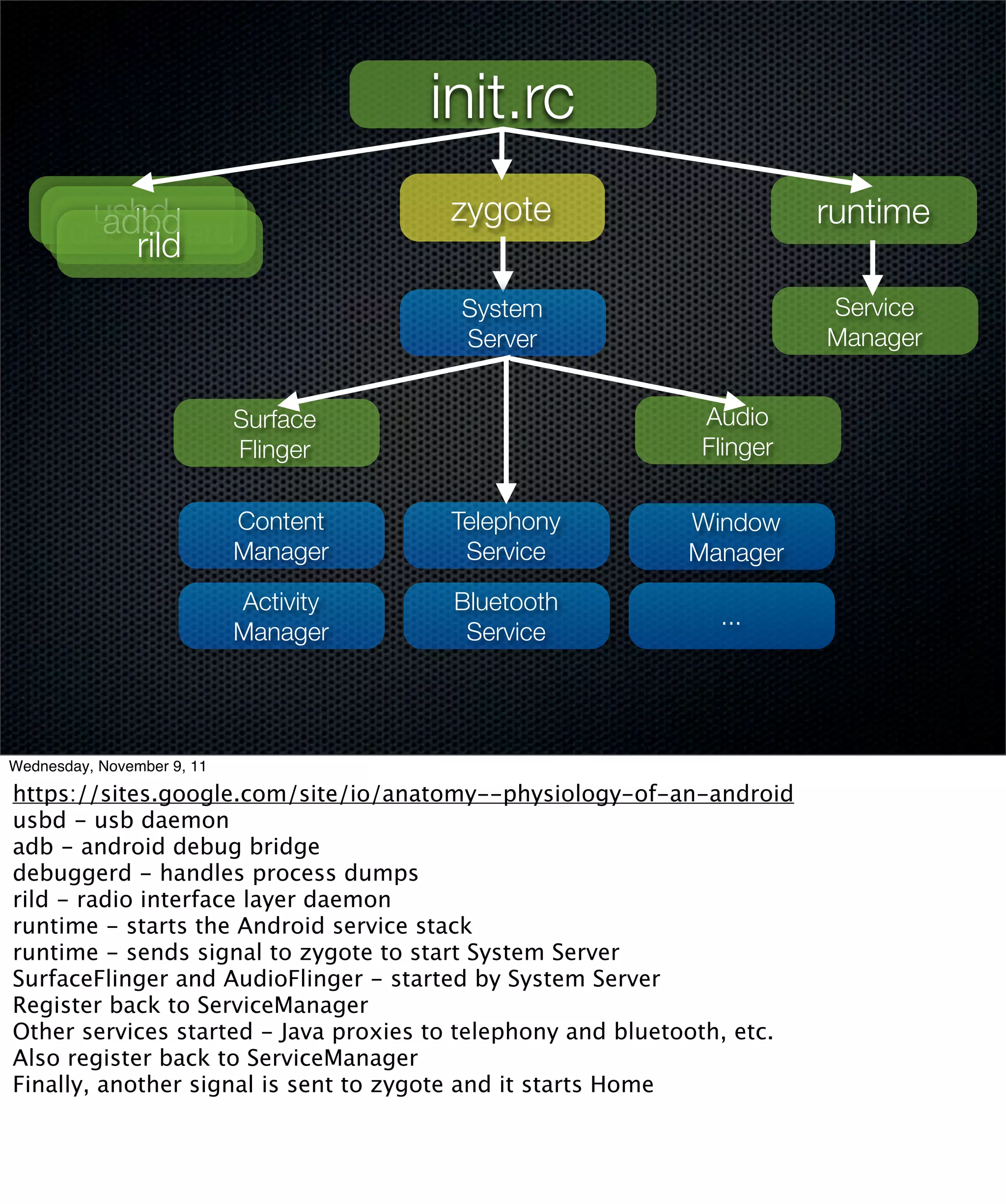
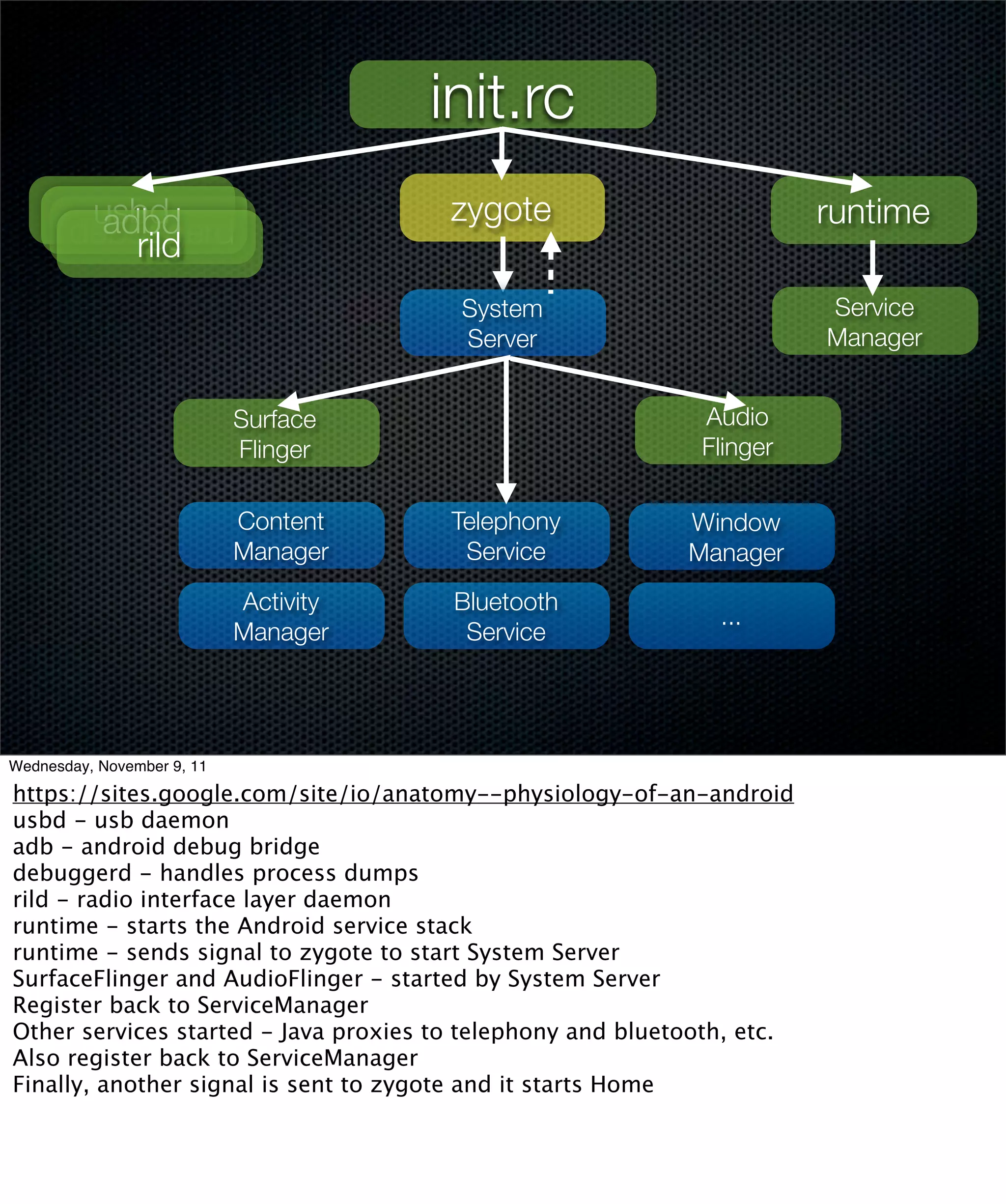
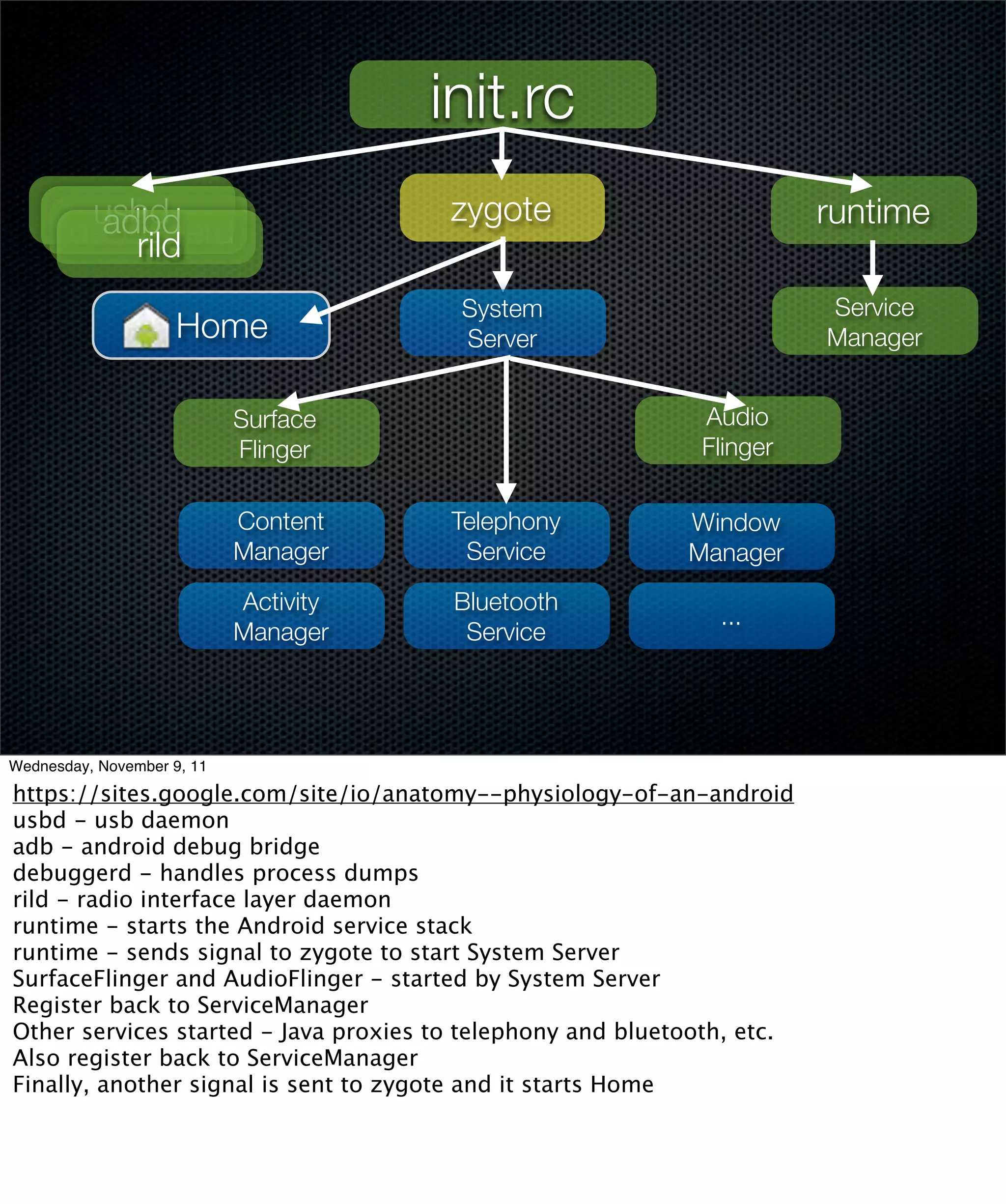
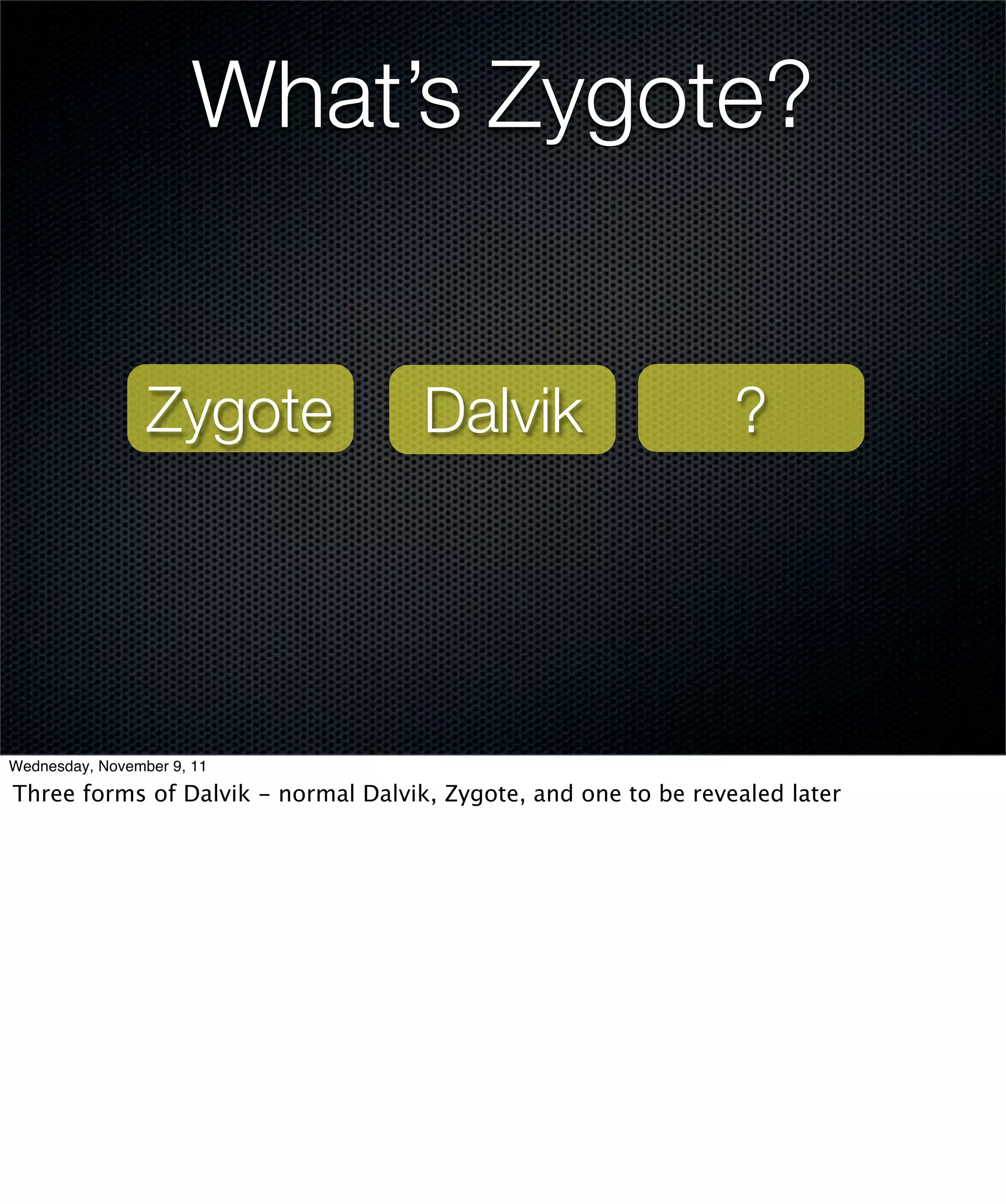
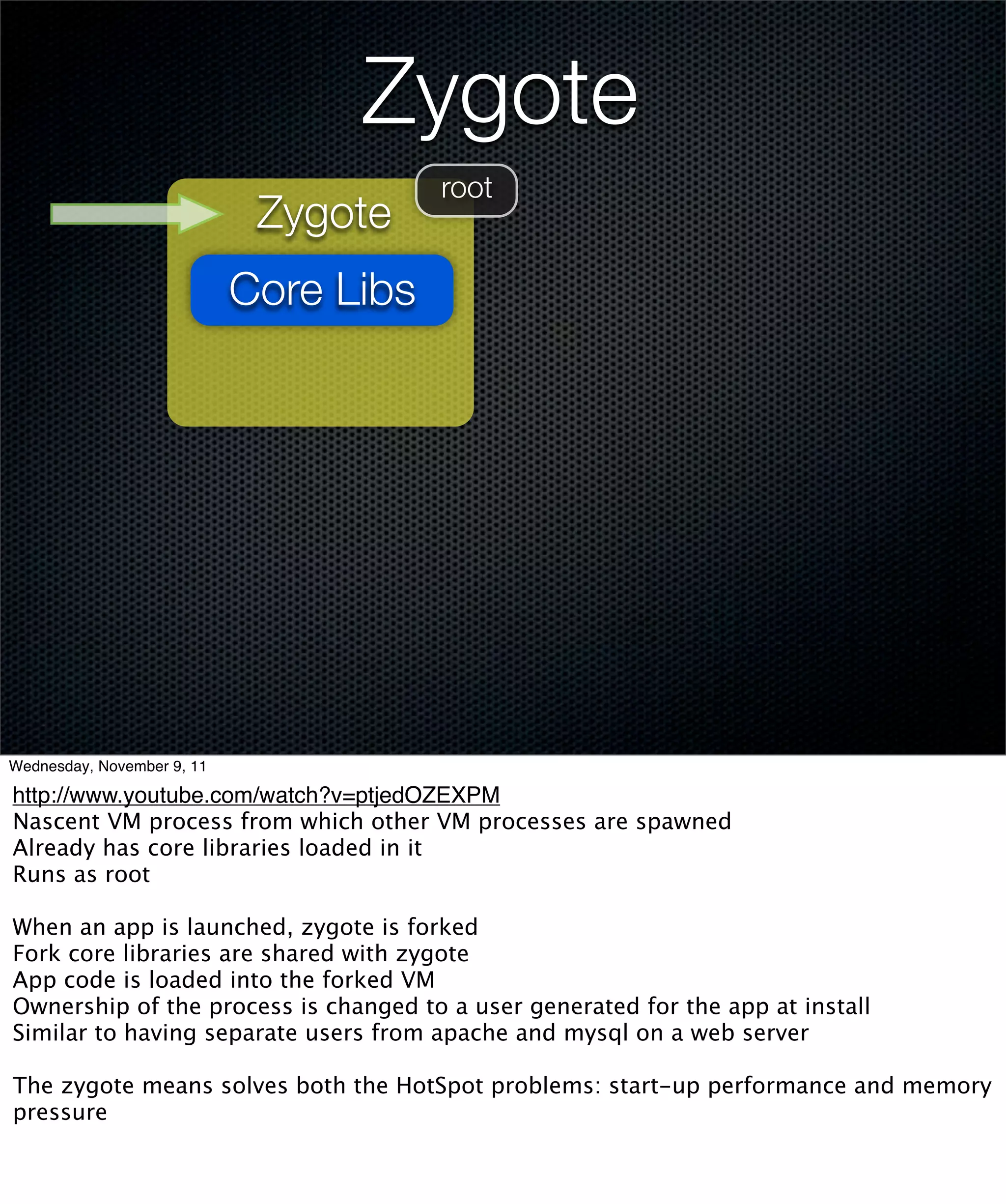
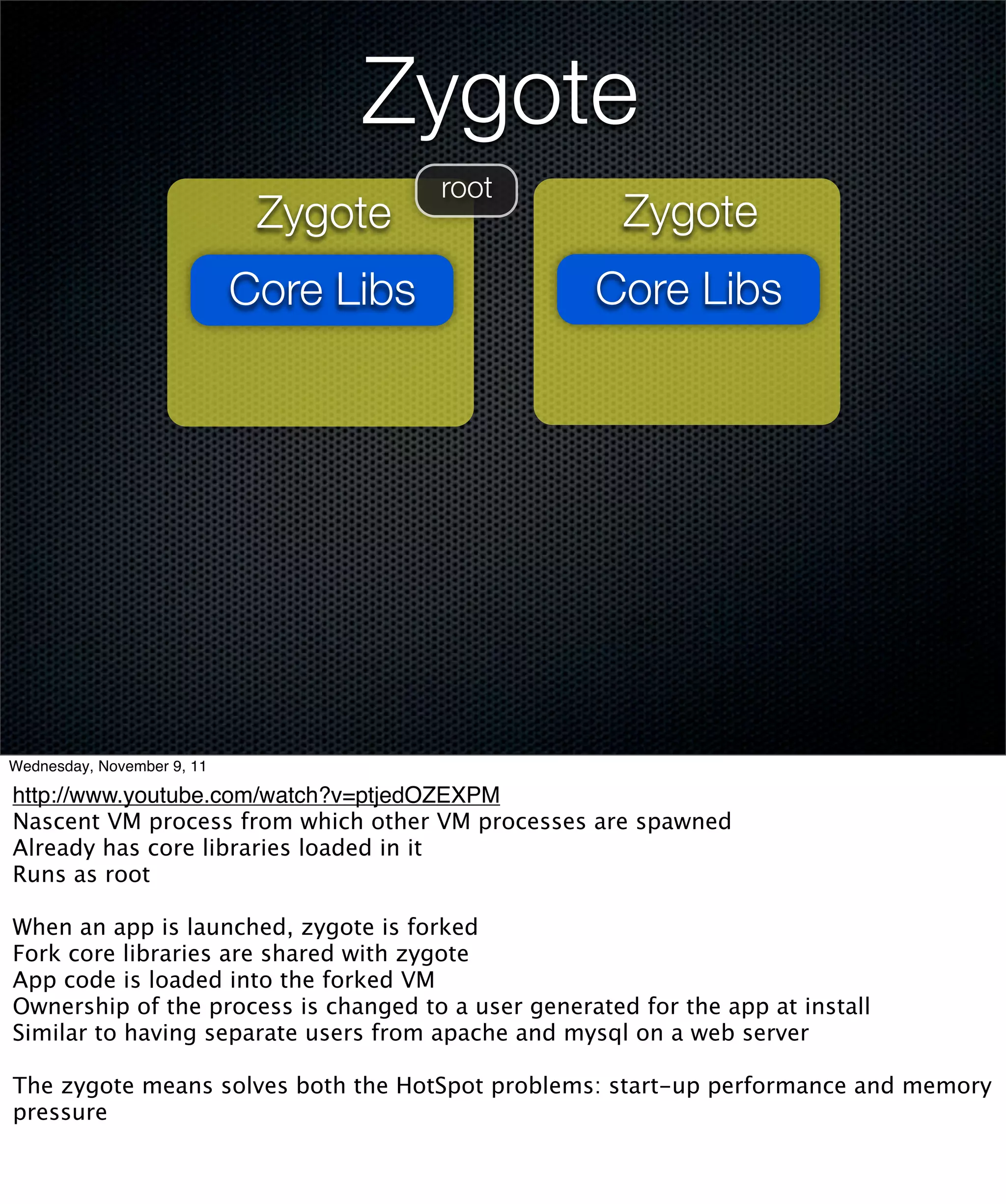
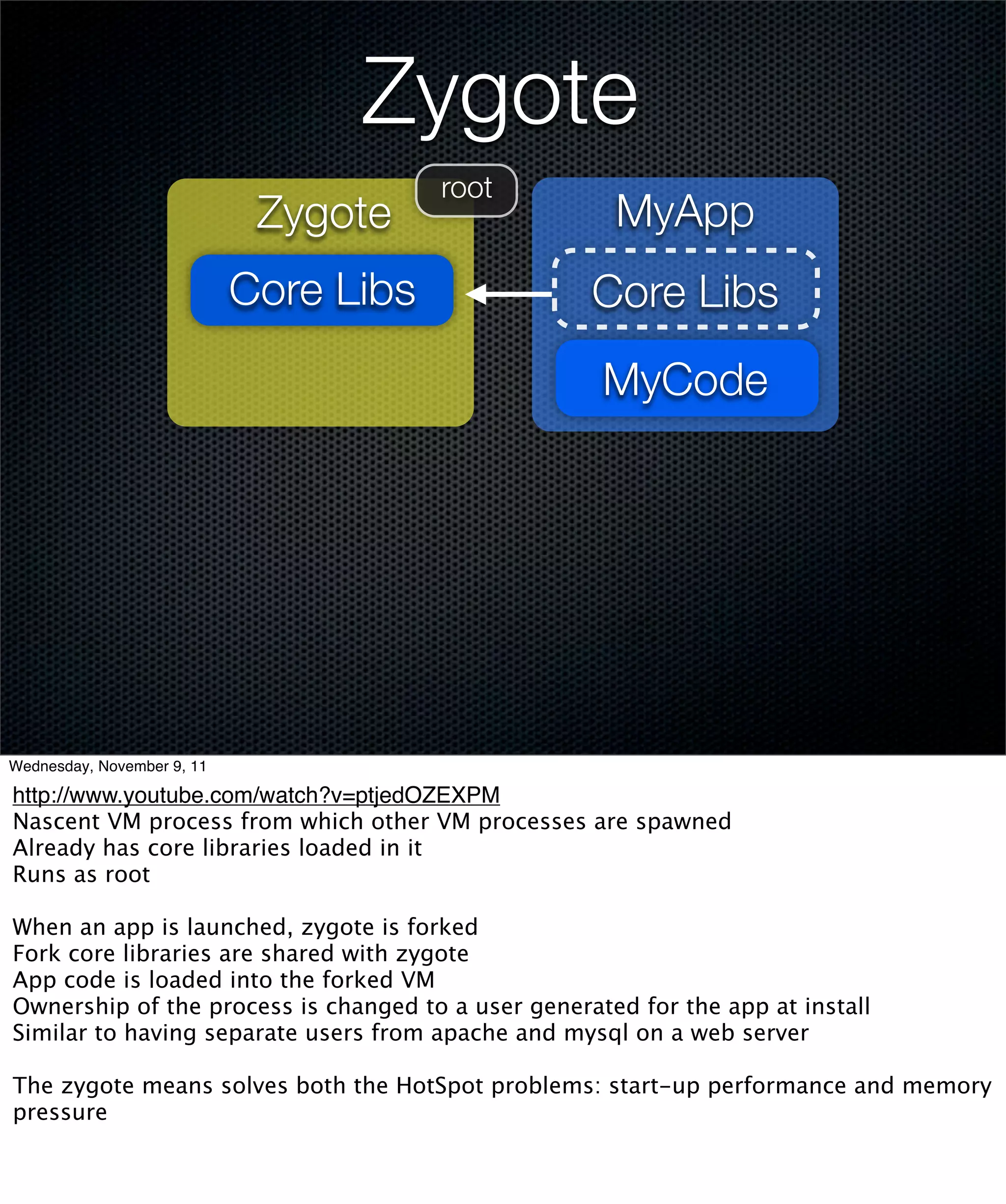
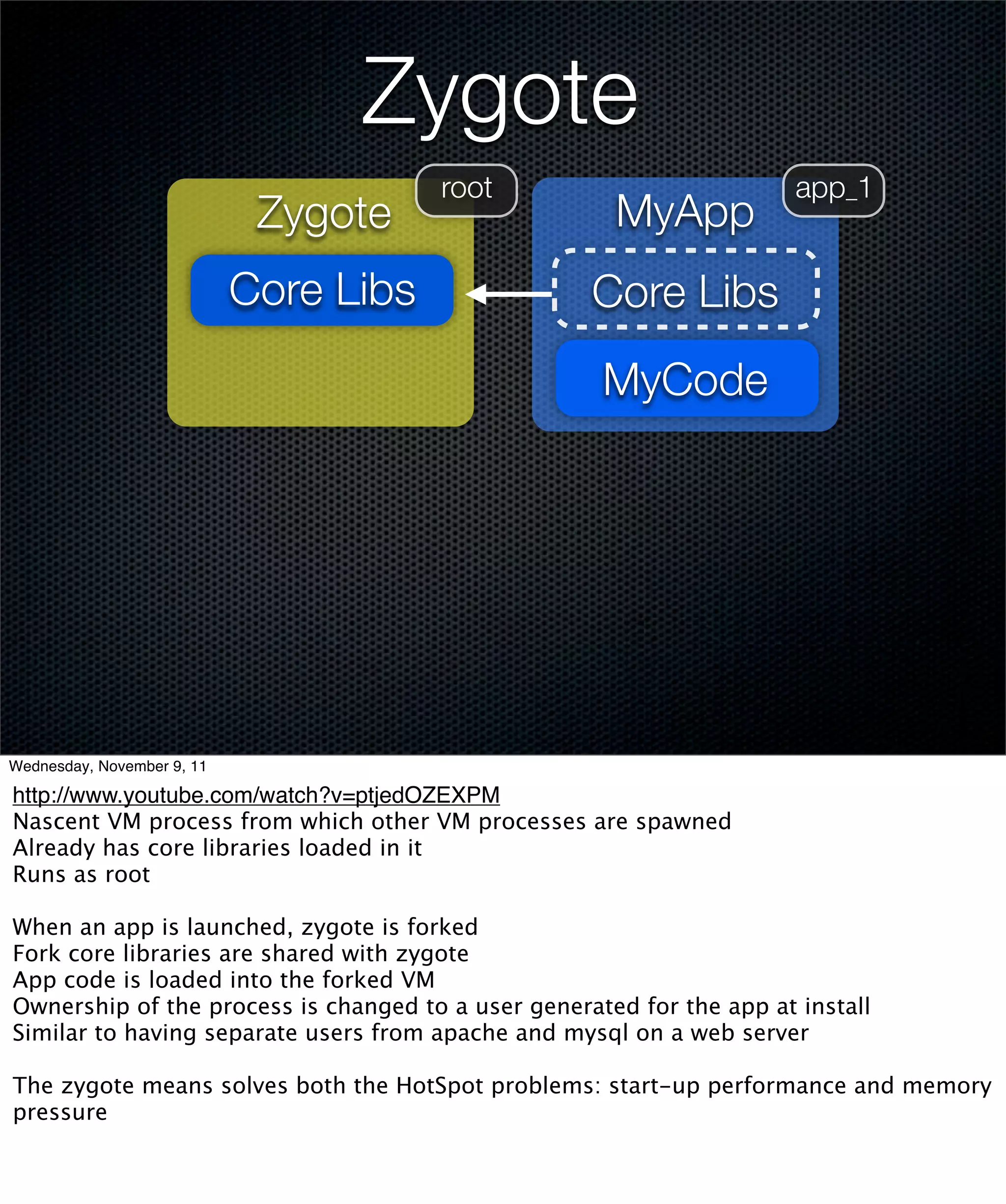
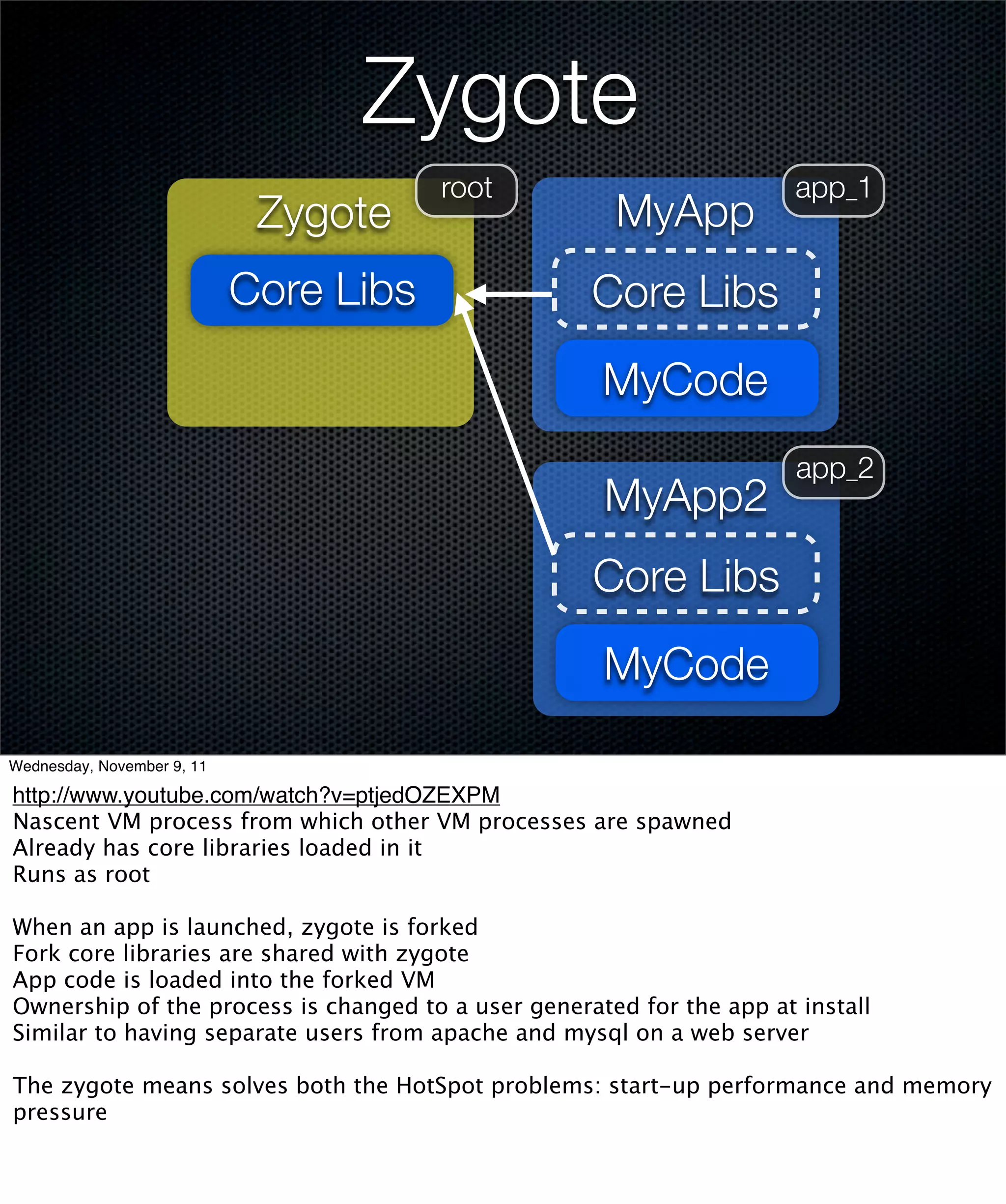
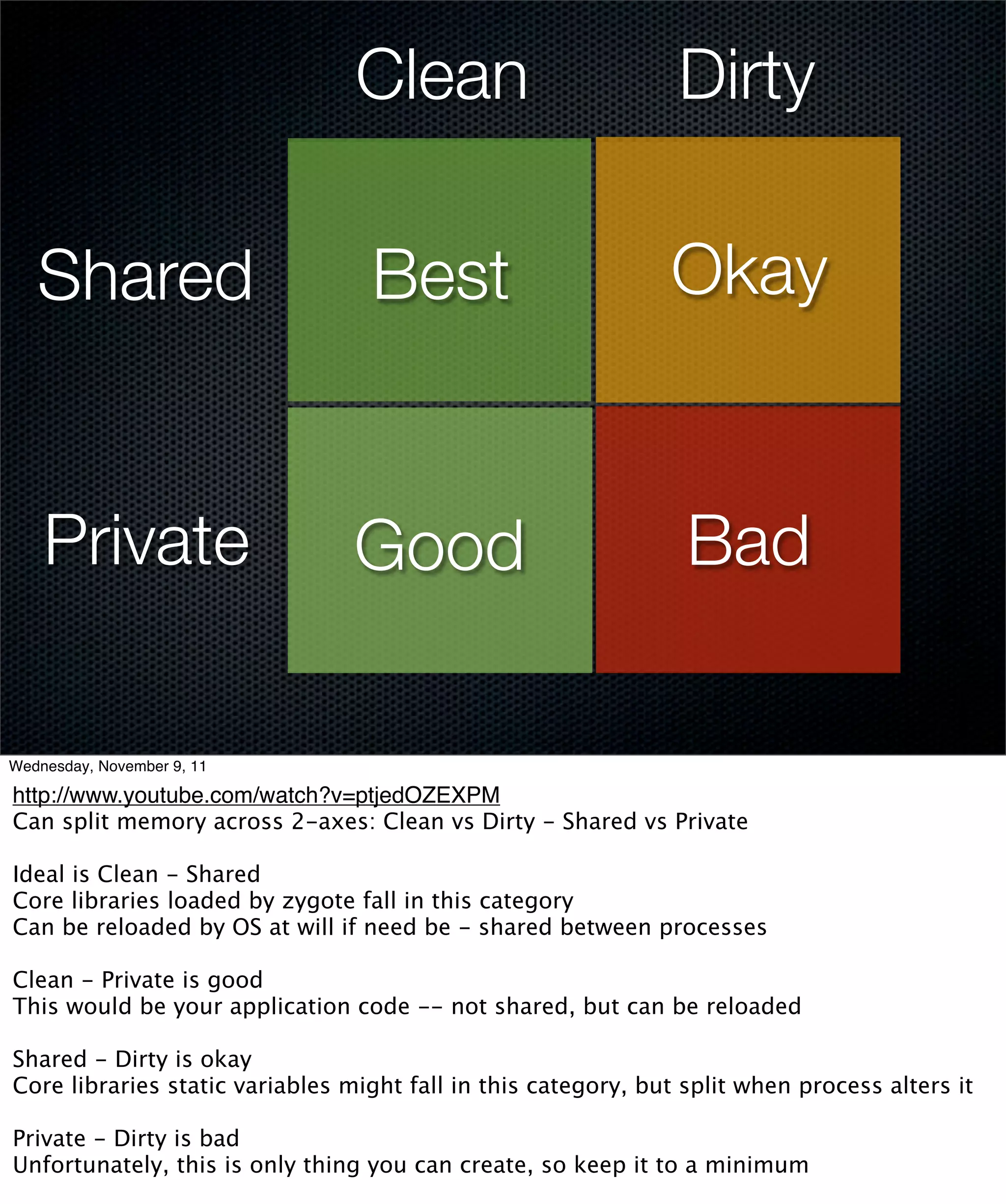
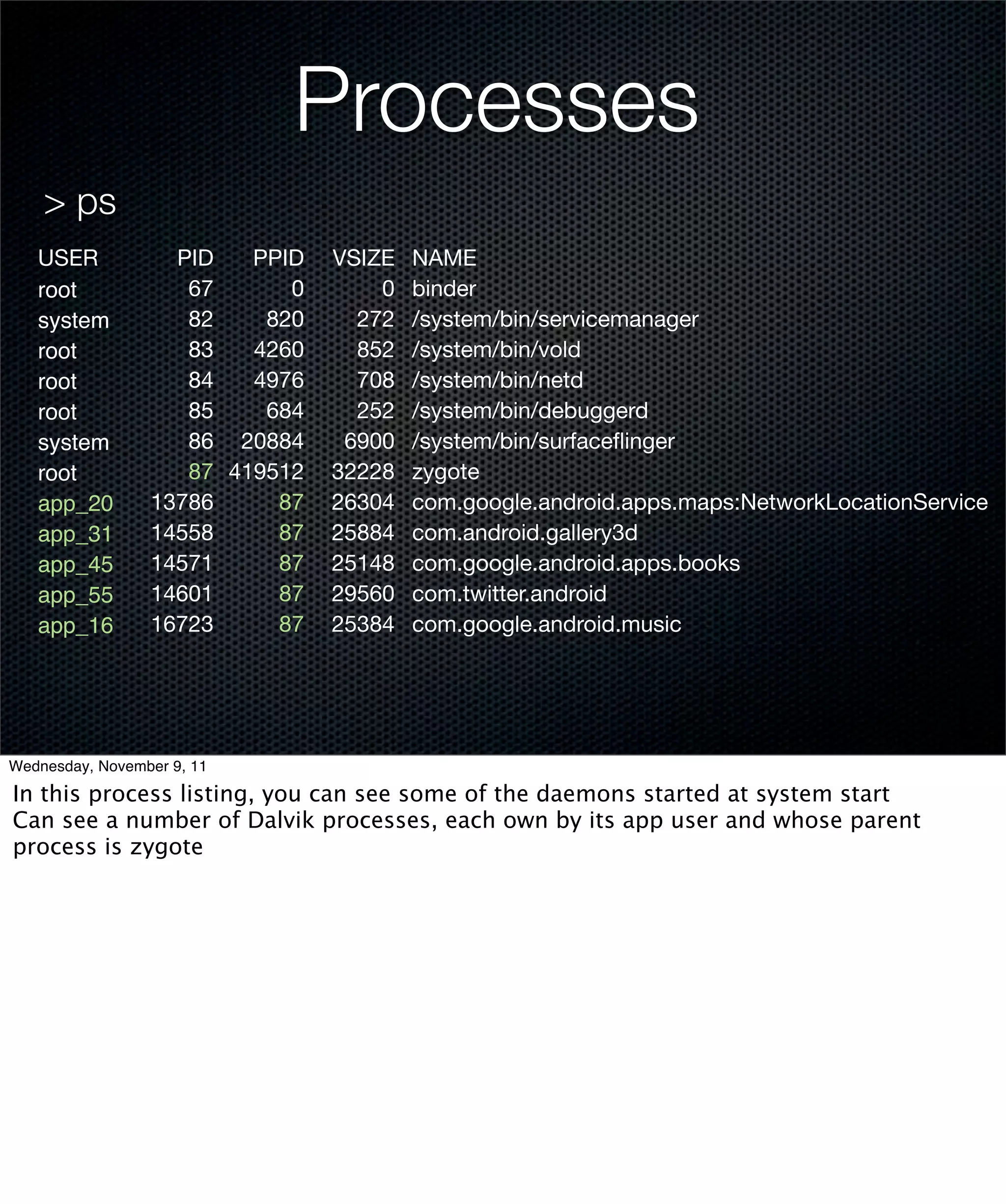
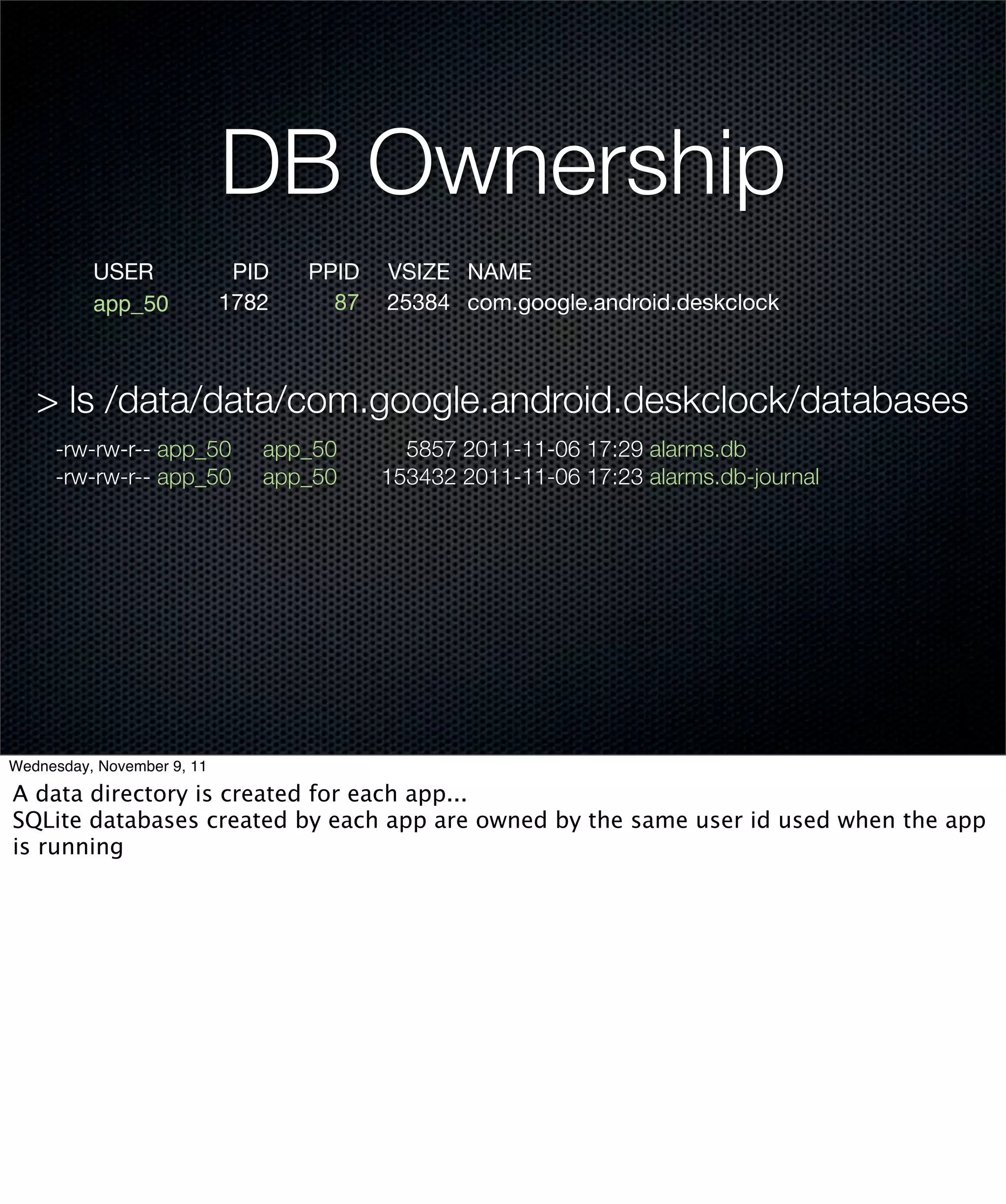
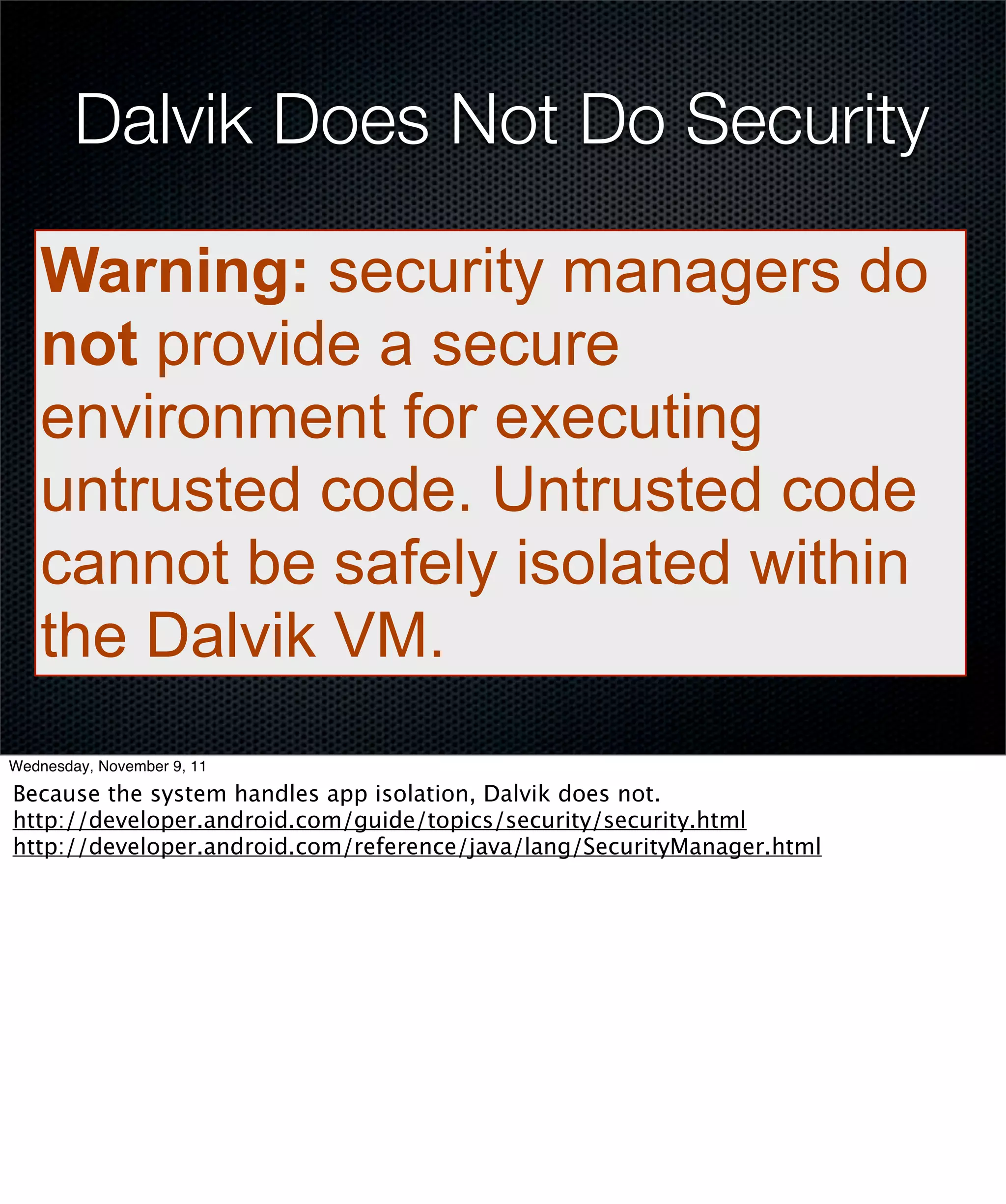
The document discusses the Dalvik Virtual Machine (VM) in Android, comparing it with the Java virtual machine and highlighting their differences and similarities. It covers the Android architecture, including its application framework, security mechanisms, and power management strategies. The Zygote process in Dalvik, which improves app startup time and memory efficiency, is also explained as a critical component of the Android ecosystem.
![Service List
> service list
0 sip: [android.net.sip.ISipService]
1 phone: [com.android.internal.telephony.ITelephony]
2 iphonesubinfo: [com.android.internal.telephony.IPhoneSubInfo]
3 simphonebook: [com.android.internal.telephony.IIccPhoneBook]
4 isms: [com.android.internal.telephony.ISms]
5 samplingprofiler: []
6 diskstats: []
Wednesday, November 9, 11
Service listing shows some of the services that you could see in the previous diagram](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-27-2048.jpg)
![Array
int[] xs = {20, 30, 0, 50};
JVM Bytecode Dalvik Bytecode
iconst_4 // 0x04 const/4 v0, 0x04
newarray int new-array v0, v0, [I
dup fill-array-data
iconst_0 // 0x00 v0, :array_8
bipush 0x14 nop
iastore :array_8
dup 0x14 0x00 0x00 0x00
iconst_1 // 0x01 0x1e 0x00 0x00 0x00
iastore 0x00 0x00 0x00 0x00
dup 0x32 0x00 0x00 0x00
iconst_3 // 0x03
bipush 0x32
iastore
astore_1 // 01
Wednesday, November 9, 11
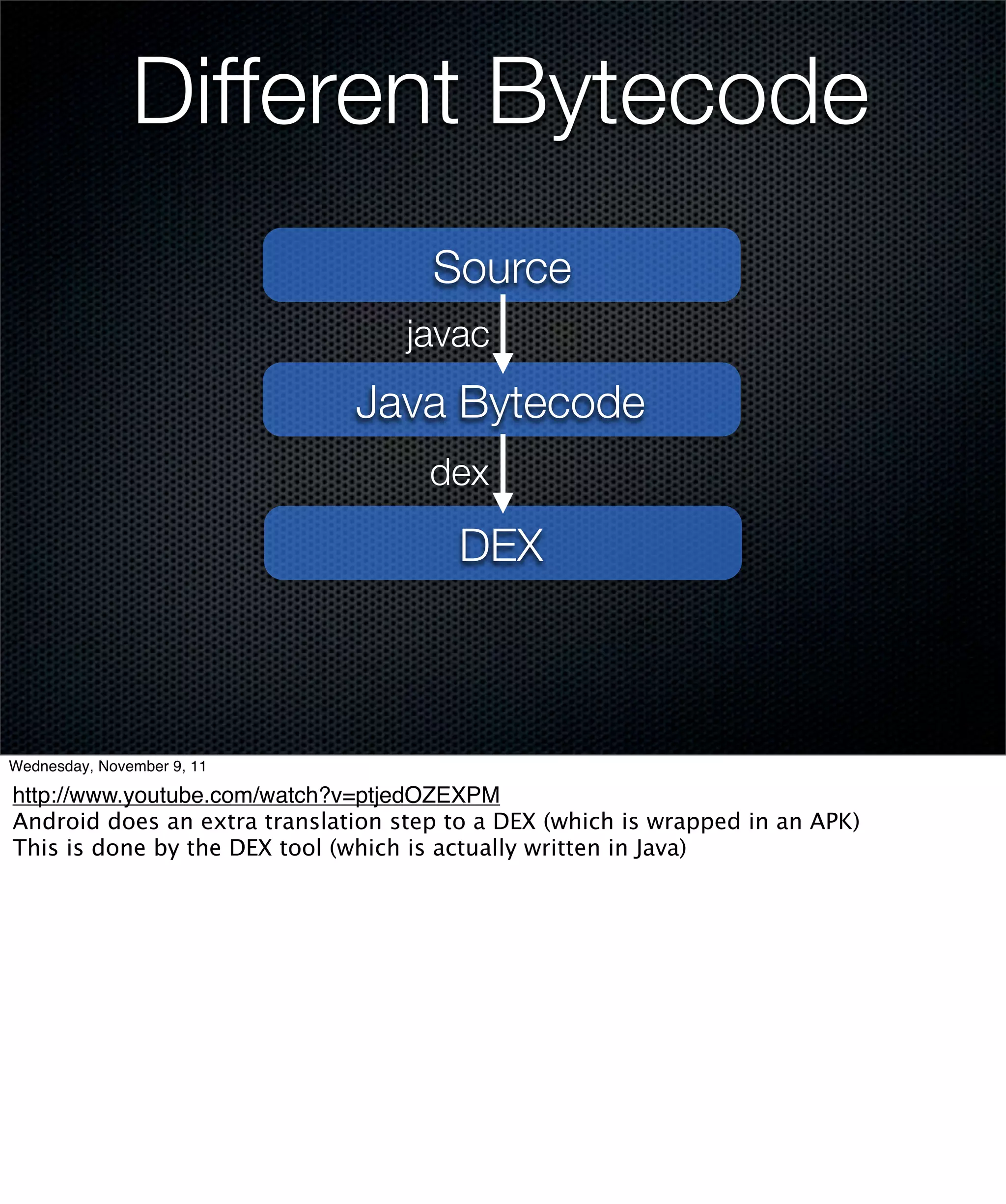
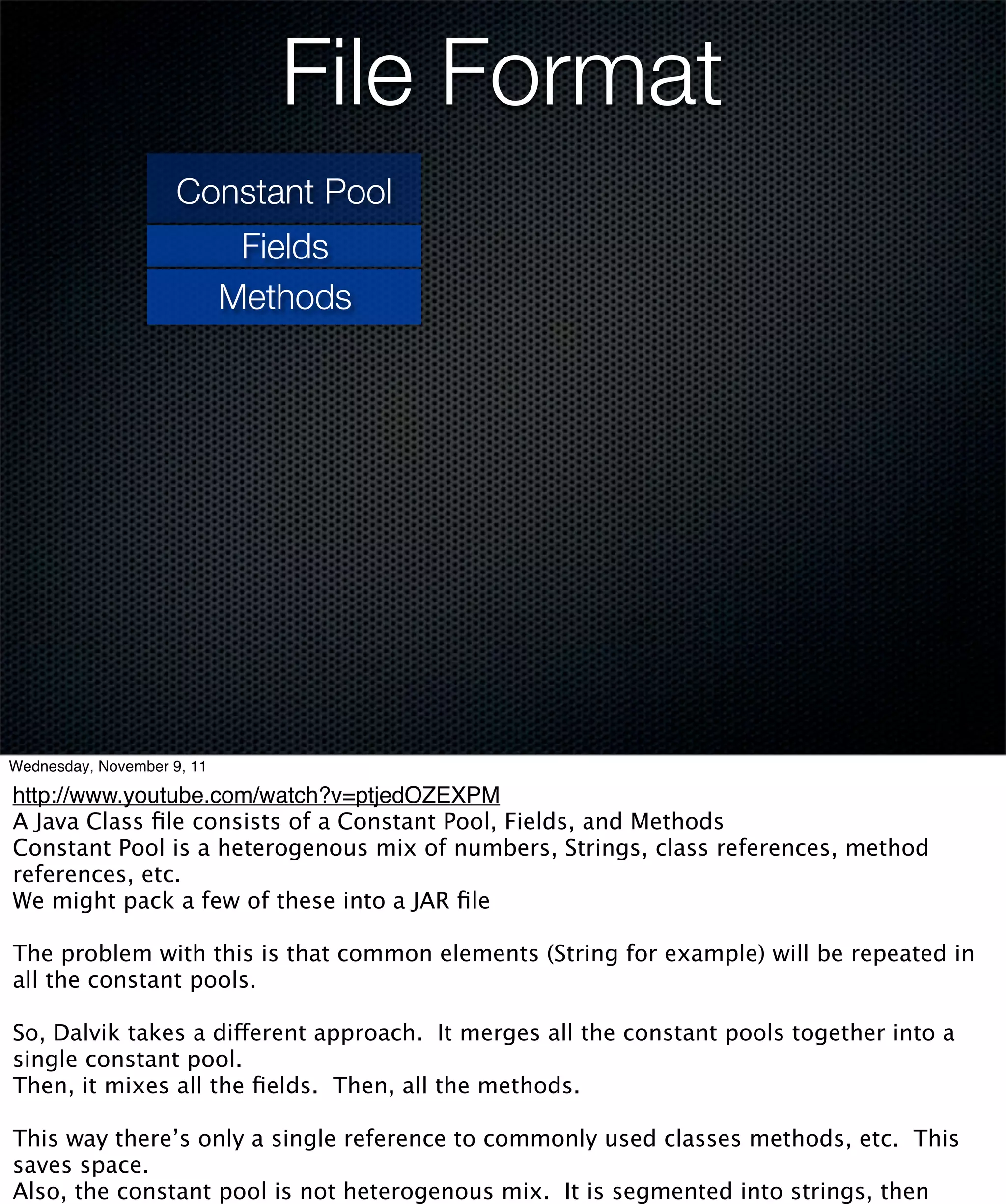
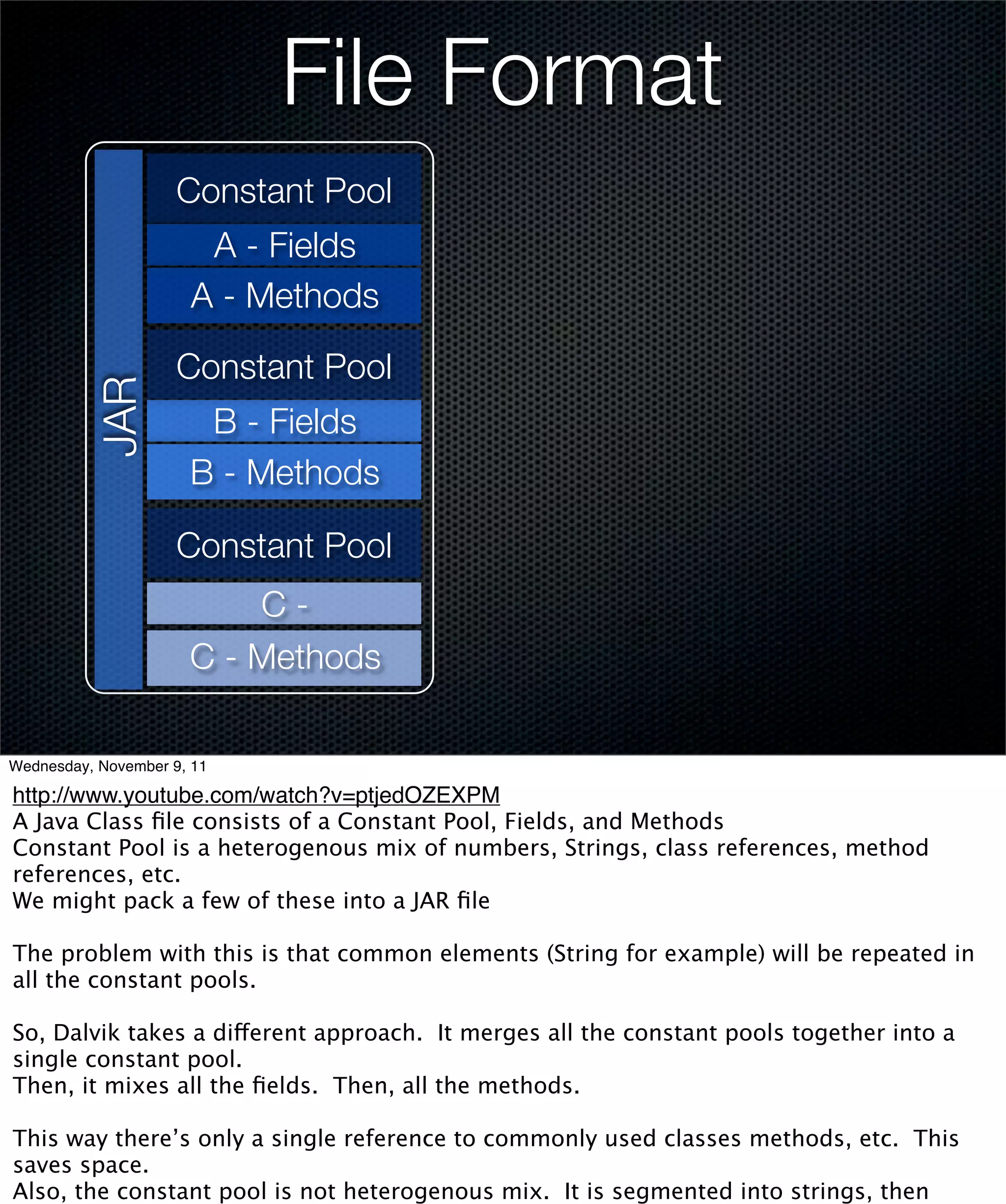
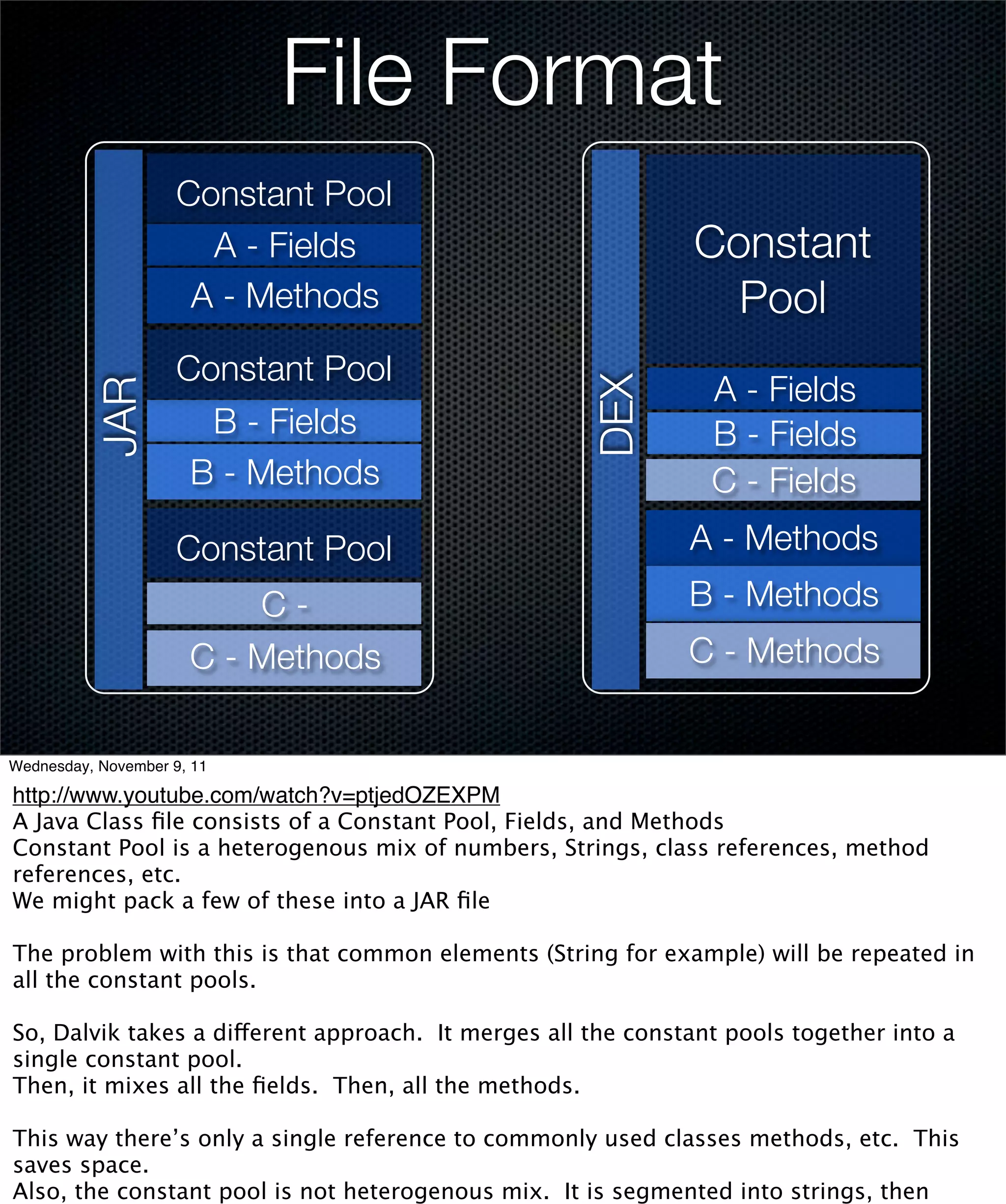
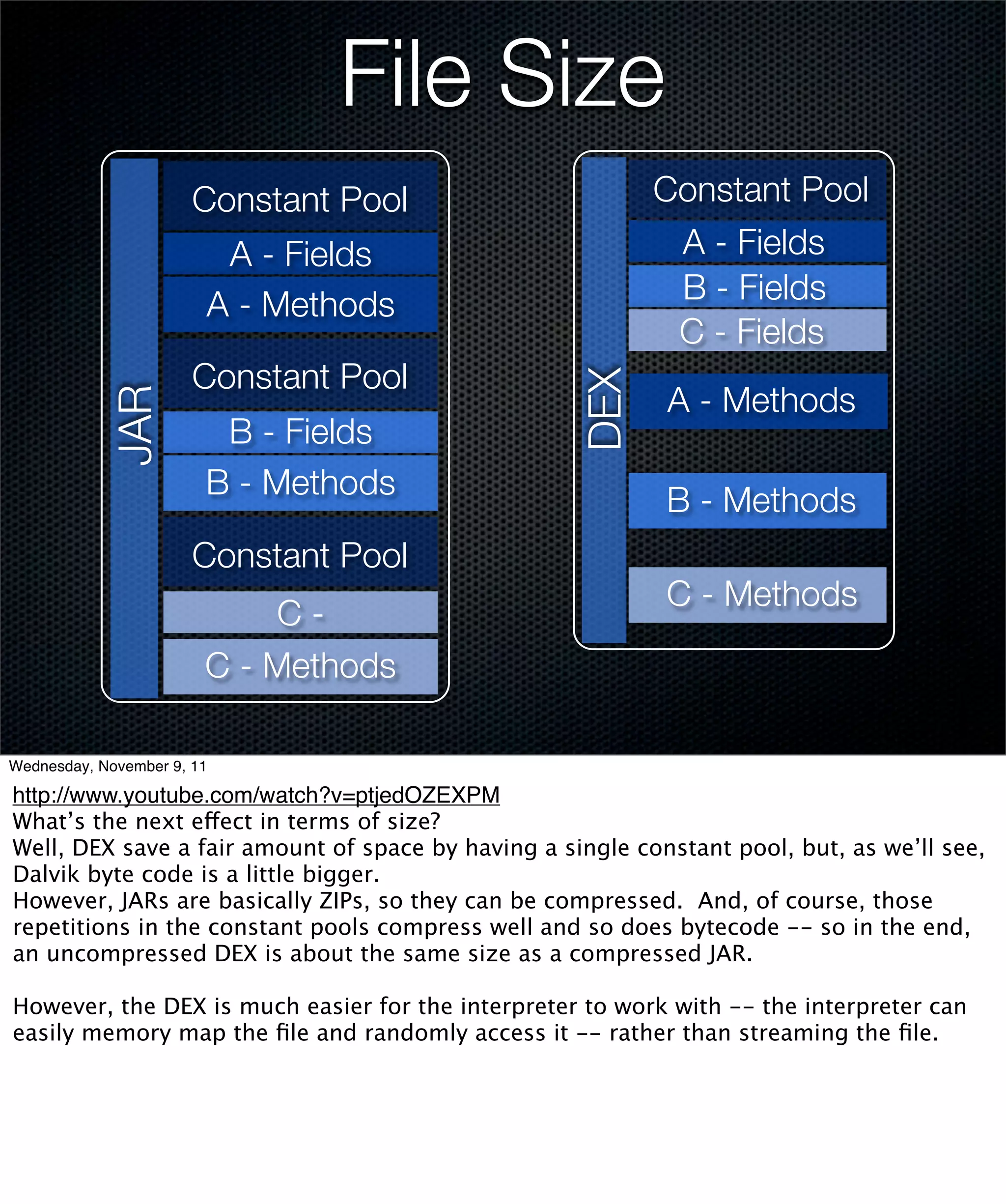
http://www.youtube.com/watch?v=ptjedOZEXPM
Arrays are particularly inefficient in Java, consider the example above...
For every element, Java adds a dup, an index load, a value push onto the stack, and an
array store.
At best, 4 bytes per element. bipush - immediately pushes it to 5 and gets worse from
there.
For large ints, have to jump to constant pool for the value which provides poor cache
usage.
Android simply has fill-array-data which takes an offset. Data is held close to the code
for better cache utilization. And, that extra nop that’s to align the data on a 4-byte
boundary to make the load that much more efficient.](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-78-2048.jpg)
![int sum = 0;
for (int i=0; i<array.length; ++i) {
sum += array[i];
}
return sum;
const/4 v1, 0x00
const/4 v0, 0x00
array-length v3, v0
if-ge v1, v3, :cond_c
return v2 aget v3, v0, v1
add-int/2addr v2, v3
add-int/lit8
v1, v1, 0x01
Wednesday, November 9, 11
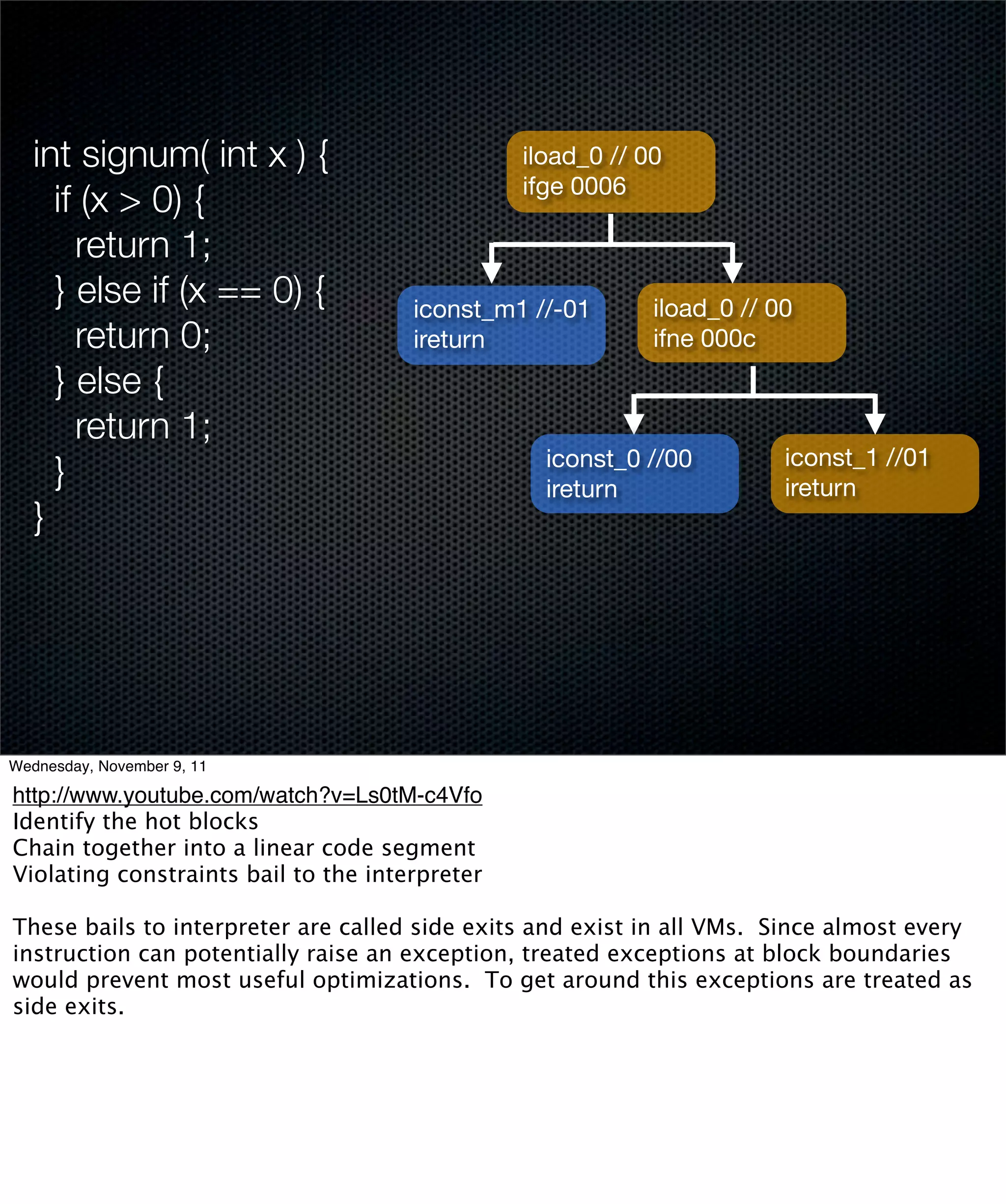
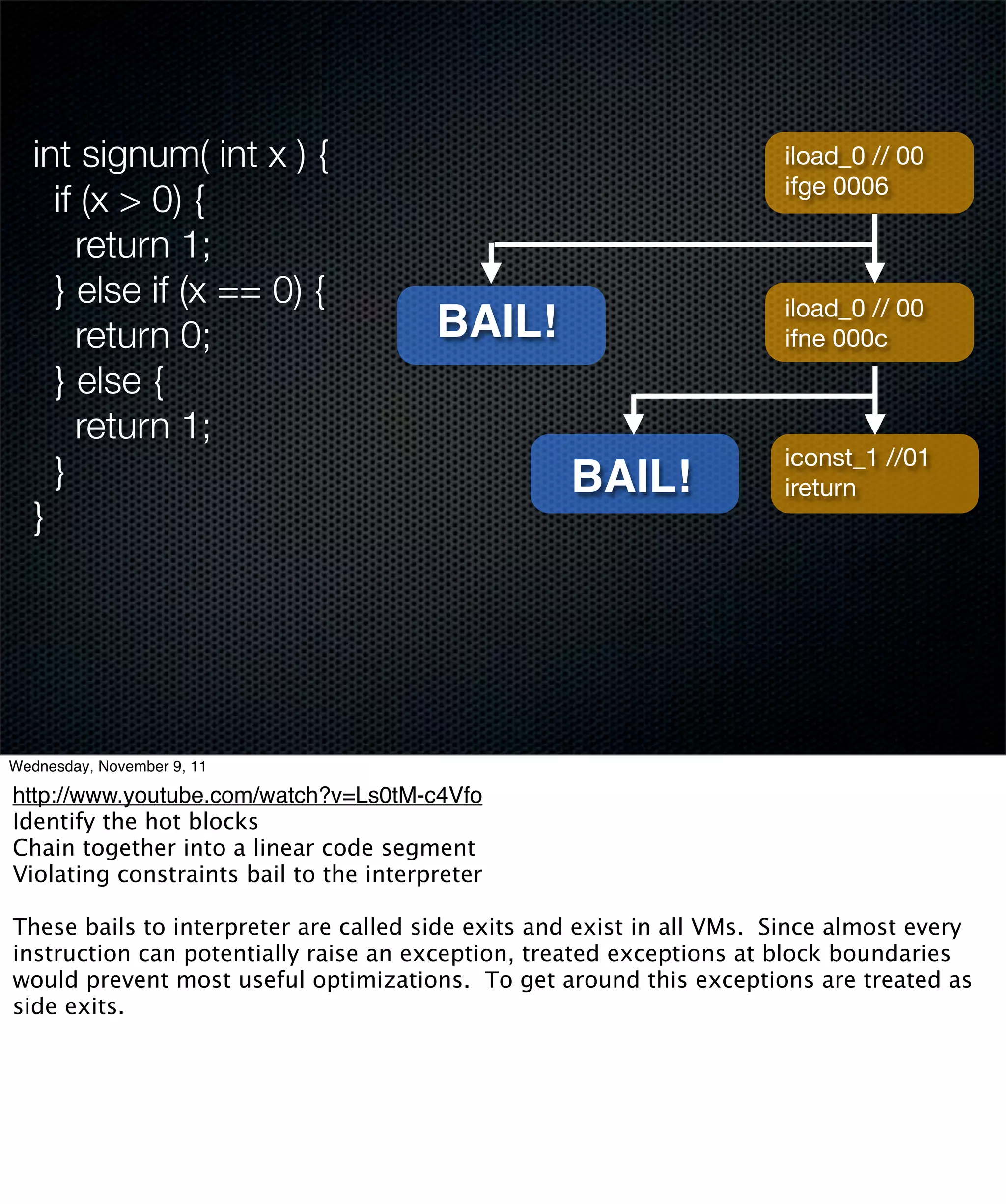
http://www.youtube.com/watch?v=Ls0tM-c4Vfo
Keep count for each trace head (i.e. first line of block)
If a block reaches the threshold, hand over for translation
Once compilation is complete, the interpreter starts routing to the generated machine
code
However, not all blocks may be compiled, so control has to return to the interpreter
Eventually, all hot blocks are compiled to machine code -- only the infrequently
executed blocks, the initialization and return continue to be interpreted](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-94-2048.jpg)
![int sum = 0;
for (int i=0; i<array.length; ++i) {
sum += array[i];
} Compiler
return sum;
const/4 v1, 0x00
1
const/4 v0, 0x00
array-length v3, v0
10
array-length v3, v0
if-ge v1, v3, :cond_c if-ge v1, v3, :cond_c
return v2 aget v3, v0, v1
10 aget v3, v0, v1
add-int/2addr v2, v3
add-int/2addr v2, v3
add-int/lit8
10
v1, v1, 0x01
Wednesday, November 9, 11
http://www.youtube.com/watch?v=Ls0tM-c4Vfo
Keep count for each trace head (i.e. first line of block)
If a block reaches the threshold, hand over for translation
Once compilation is complete, the interpreter starts routing to the generated machine
code
However, not all blocks may be compiled, so control has to return to the interpreter
Eventually, all hot blocks are compiled to machine code -- only the infrequently
executed blocks, the initialization and return continue to be interpreted](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-95-2048.jpg)
![int sum = 0;
for (int i=0; i<array.length; ++i) {
sum += array[i];
} Compiler Translation
return sum; Cache
const/4 v1, 0x00
1
const/4 v0, 0x00
array-length v3, v0
10 array-lengthv3,v3, v0
array-length v0
if-ge v1, v3, :cond_c if-ge v1, v3, :cond_c
if-ge v1, v3, :cond_c
return v2 aget v3, v0, v1
10 aget v3, v0, v1
add-int/2addr v2, v3
add-int/2addr v2, v3
add-int/lit8
10
v1, v1, 0x01
Wednesday, November 9, 11
http://www.youtube.com/watch?v=Ls0tM-c4Vfo
Keep count for each trace head (i.e. first line of block)
If a block reaches the threshold, hand over for translation
Once compilation is complete, the interpreter starts routing to the generated machine
code
However, not all blocks may be compiled, so control has to return to the interpreter
Eventually, all hot blocks are compiled to machine code -- only the infrequently
executed blocks, the initialization and return continue to be interpreted](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-96-2048.jpg)
![int sum = 0;
for (int i=0; i<array.length; ++i) {
sum += array[i];
} Compiler Translation
return sum; Cache
const/4 v1, 0x00
1
const/4 v0, 0x00
array-length v3, v0
10 array-lengthv3,v3, v0
array-length v0
if-ge v1, v3, :cond_c if-ge v1, v3, :cond_c
if-ge v1, v3, :cond_c
return v2 aget v3, v0, v1
10 aget v3, v0, v1
add-int/2addr v2, v3
add-int/2addr v2, v3
add-int/lit8
10
v1, v1, 0x01
Wednesday, November 9, 11
http://www.youtube.com/watch?v=Ls0tM-c4Vfo
Keep count for each trace head (i.e. first line of block)
If a block reaches the threshold, hand over for translation
Once compilation is complete, the interpreter starts routing to the generated machine
code
However, not all blocks may be compiled, so control has to return to the interpreter
Eventually, all hot blocks are compiled to machine code -- only the infrequently
executed blocks, the initialization and return continue to be interpreted](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-97-2048.jpg)
![int sum = 0;
for (int i=0; i<array.length; ++i) {
sum += array[i];
} Compiler Translation
return sum; Cache
const/4 v1, 0x00
1
const/4 v0, 0x00
array-length v3, v0
10 array-lengthv3,v3, v0
array-length v0
if-ge v1, v3, :cond_c if-ge v1, v3, :cond_c
if-ge v1, v3, :cond_c
return v2 aget v3, v0, v1
10 aget v3, v0, v1
add-int/2addr v2, v3
add-int/2addr v2, v3
add-int/lit8
10
v1, v1, 0x01
Wednesday, November 9, 11
http://www.youtube.com/watch?v=Ls0tM-c4Vfo
Keep count for each trace head (i.e. first line of block)
If a block reaches the threshold, hand over for translation
Once compilation is complete, the interpreter starts routing to the generated machine
code
However, not all blocks may be compiled, so control has to return to the interpreter
Eventually, all hot blocks are compiled to machine code -- only the infrequently
executed blocks, the initialization and return continue to be interpreted](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-98-2048.jpg)
![int sum = 0;
for (int i=0; i<array.length; ++i) {
sum += array[i];
} Compiler Translation
return sum; Cache
const/4 v1, 0x00
1
const/4 v0, 0x00
array-length v3, v0
10 array-lengthv3,v3, v0
array-length v0
if-ge v1, v3, :cond_c if-ge v1, v3, :cond_c
if-ge v1, v3, :cond_c
return v2 aget v3, v0, v1
10 aget v3, v3, v0, v1v1
aget
v0,
add-int/2addr v2, v3 add-int/2addr v2, v3
add-int/2addr v2, v3
add-int/lit8
10
v1, v1, 0x01
Wednesday, November 9, 11
http://www.youtube.com/watch?v=Ls0tM-c4Vfo
Keep count for each trace head (i.e. first line of block)
If a block reaches the threshold, hand over for translation
Once compilation is complete, the interpreter starts routing to the generated machine
code
However, not all blocks may be compiled, so control has to return to the interpreter
Eventually, all hot blocks are compiled to machine code -- only the infrequently
executed blocks, the initialization and return continue to be interpreted](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-99-2048.jpg)
![int sum = 0;
for (int i=0; i<array.length; ++i) {
sum += array[i];
} Compiler Translation
return sum; Cache
const/4 v1, 0x00
1
const/4 v0, 0x00
array-length v3, v0
10 array-lengthv3,v3, v0
array-length v0
if-ge v1, v3, :cond_c if-ge v1, v3, :cond_c
if-ge v1, v3, :cond_c
return v2 aget v3, v0, v1
10 aget v3, v3, v0, v1v1
aget
v0,
add-int/2addr v2, v3 add-int/2addr v2, v3
add-int/2addr v2, v3
add-int/lit8
10
v1, v1, 0x01
Wednesday, November 9, 11
http://www.youtube.com/watch?v=Ls0tM-c4Vfo
Keep count for each trace head (i.e. first line of block)
If a block reaches the threshold, hand over for translation
Once compilation is complete, the interpreter starts routing to the generated machine
code
However, not all blocks may be compiled, so control has to return to the interpreter
Eventually, all hot blocks are compiled to machine code -- only the infrequently
executed blocks, the initialization and return continue to be interpreted](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-100-2048.jpg)
![int sum = 0;
for (int i=0; i<array.length; ++i) {
sum += array[i];
} Compiler Translation
return sum; Cache
const/4 v1, 0x00
1
const/4 v0, 0x00
array-length v3, v0
10 array-lengthv3,v3, v0
array-length v0
if-ge v1, v3, :cond_c if-ge v1, v3, :cond_c
if-ge v1, v3, :cond_c
return v2 aget v3, v0, v1
10 aget v3, v3, v0, v1v1
aget
v0,
add-int/2addr v2, v3 add-int/2addr v2, v3
add-int/2addr v2, v3
add-int/lit8
10 add-int/lit8
v1, v1, 0x01 v1, v1, 0x01
Wednesday, November 9, 11
http://www.youtube.com/watch?v=Ls0tM-c4Vfo
Keep count for each trace head (i.e. first line of block)
If a block reaches the threshold, hand over for translation
Once compilation is complete, the interpreter starts routing to the generated machine
code
However, not all blocks may be compiled, so control has to return to the interpreter
Eventually, all hot blocks are compiled to machine code -- only the infrequently
executed blocks, the initialization and return continue to be interpreted](https://image.slidesharecdn.com/android-nejug-reduced-111109215741-phpapp02/75/Inside-Android-s-Dalvik-VM-NEJUG-Nov-2011-101-2048.jpg)