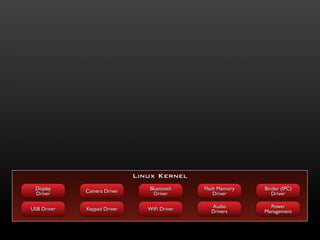
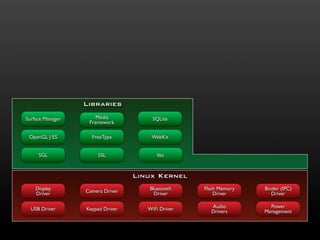
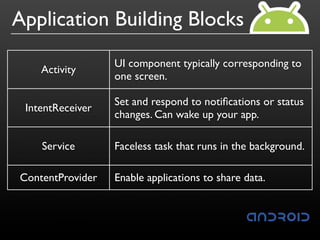
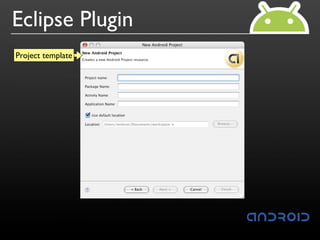
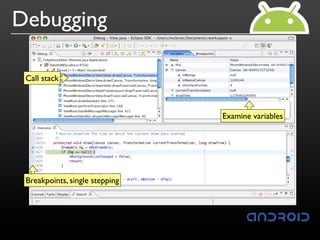
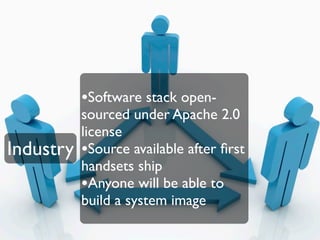
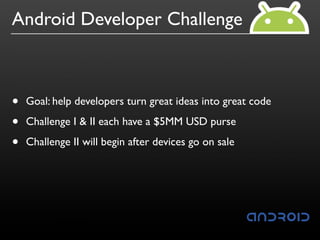
This document provides an introduction and overview of the Android mobile operating system. It discusses Android's open source nature, its components including the Linux kernel and Dalvik virtual machine, the developer tools and SDK, and how developers can build applications and integrate with, extend, and replace existing Android components. The document also provides an update on the latest Android news including the announcement and early SDK releases, the Android Developer Challenge program, and upcoming SDK and device releases.