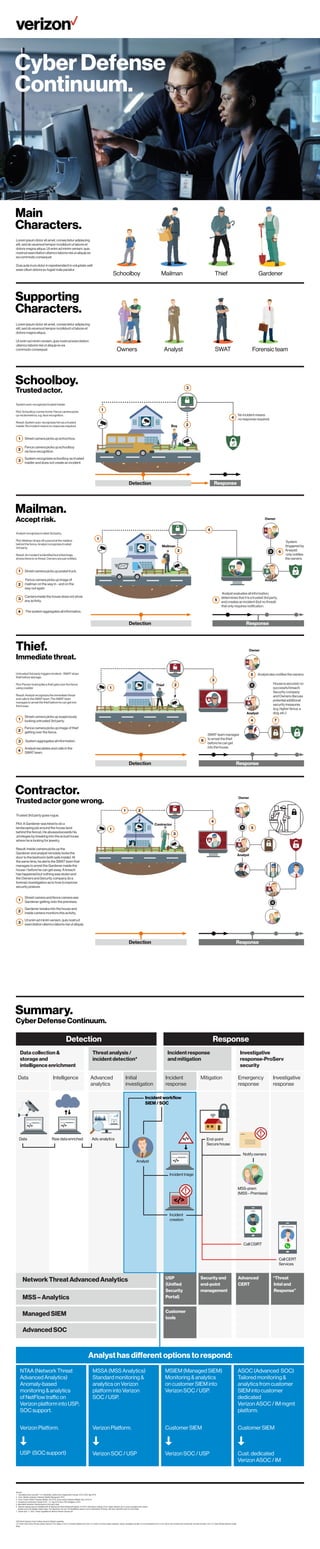
The document describes various cybersecurity scenarios detected and responded to by a home security system. In the first scenario, a schoolboy returns home and is recognized by fence cameras through facial recognition as a trusted individual, so no incident report is created. In the second scenario, a mailman drops off a package and is also recognized as trusted, so owners are just notified of his presence. In the third scenario, an untrusted individual scales the fence and is seen as an immediate threat, so the analyst calls in SWAT who arrests the person before they can enter the home.