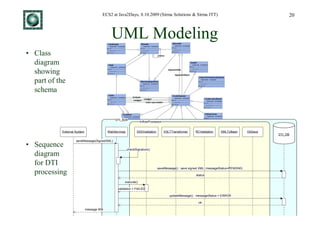
The document discusses an export control system project called ECS2 that was implemented for the Bulgarian government using open source tools and a business process management system (BPMS). It provides an overview of the project goals, challenges with the previous system, and the technologies selected for ECS2 including the JBoss application server, JBoss Messaging, jBPM BPMS, and frameworks like JSF, Hibernate and Seam.



![ECS2 at Java2Days, 8.10.2009 (Sirma Solutions & Sirma ITT) 27
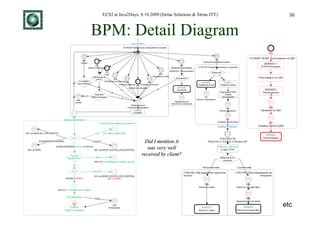
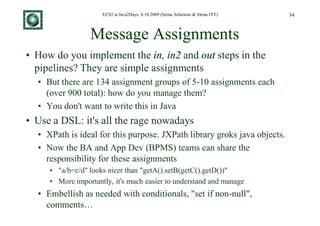
Business Process Modeling
CO02 - Process Arrival at Office of Exit part II
• TAXUD provides
global process
diagrams like this
• Coupled with (from FSS)
state transition
diagrams like • The boxes are
that (from "EBP": linear atomic
DDNXA) processing
IE507[ MRN Unknown ] ^IE502
AER IE503( Negative Respons e )
IE501
Requested ^IE521
IE524 AER
Created Diversion
Rejected
IE507 IE503( Positive Respons e )
IE501
Arrived Goods [ Control ] ^IE561 Under [ CNTRL_RES= B1 ] Goods not
Elsewhere Presented at Exit Control ^IE518.IE522 allowed to Exit
[ No control ]
Goods ready to [ CNTRL_RES=A1 or A2 or A4 ]
be released
IE547[ other than the firs t
one ] ^IE548
[ Storing=Yes ] ^IE525
Goods held for IE547( covering part of Goods released for
storing the m ovem ent )[ Firs t immediate leave (partial)
Received ] ^IE548
[ Storing=No ] ^IE525
IE590[ First IE590 received AND IE547 for the
IE547( for the whole m ovement ) ^IE548
s pecific IE590 has been received ]
Goods released for • Ambiguities,
im mediate leave IE547 ^IE548 Partially IE590[ other than the firs t
Exited or last received ] discrepancies and
IE590 ^IE518(A1 or A2
or A4)
Exited
IE590[ Last IE590 Received AND All IE590s
received for the corres ponding IE547 ] ^IE518
bugs exist](https://image.slidesharecdn.com/alexievmitevbukev2010-egovbpm-110428011826-phpapp02/85/Implementing-complex-e-Government-solutions-with-open-source-and-BPM-Architecture-of-Export-Control-System-phase-2-ECS2-27-320.jpg)
![ECS2 at Java2Days, 8.10.2009 (Sirma Solutions & Sirma ITT) 37
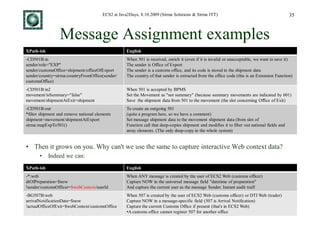
Rules & Conditions public class C060 extends Rules {
private String kindOfPackValue;
private String errorDescriptionStr;
• Do you want to write rules in Java? public boolean isRuleValid(Document doc) {
ruleName = "C060";
Don't!
NodeList listOfGDS = doc.getElementsByTagName("GOOITEGDS");
int numberOfGDS = listOfGDS.getLength();
String tags[] = {"NumOfPacGS24", "NumOfPieGS25", "MarNumOfPacGS21"};
String description[] ={"Number Of Packages", "Number Of Pieces", "Marks and Numbers of Packages"};
int id[] = new int[3];
• The same rule is implemented in 60
for (int k= 0; k < tags.length; k++) {
FieldsInfo info = new FieldsInfo();
info.setTagName(tags[k]);
info.setTagDescription(description[k]);
fieldInfo.addElement(info); // add a FieldsInfo object to the fieldInfo Vector
lines of dense Java in the Standard
}
for (int i = 0; i < numberOfGDS; i++) {
Node GDSNode = listOfGDS.item(i);
NodeList listPackages = ((Element) GDSNode).getElementsByTagName("PACGS2");
Transit Testing Application (STTA) by
int numberOfPackages = listPackages.getLength();
for (int j = 0; j < numberOfPackages; j++) {
Node packagesNode = listPackages.item(j);
Intrasoft
kindOfPackValue = getTagValue((Element) packagesNode, "KinOfPacGS23");
if (kindOfPackValue != null) {
if (kindOfPackValue.equals("VQ") || kindOfPackValue.equals("VG") ||
kindOfPackValue.equals("VL") || kindOfPackValue.equals("VY") ||
kindOfPackValue.equals("VR") || kindOfPackValue.equals("VO")) {
• Furthermore, our rules can be used both id[0] = FieldsInfo.NOT_USED;
id[1] = FieldsInfo.NOT_USED;
id[2] = FieldsInfo.OPTIONAL;
errorDescriptionStr = "Since the GOOITEGDS(" + (i + 1) + ").PACGS2(" + (j + 1) + ").KinOfPacGS23 " +
"has a value of '" + kindOfPackValue +
for offline validation, and GUI }
"' which indicates BULK ('VQ', 'VG', 'VL', 'VY', 'VR', 'VO'), the GOOITEGDS(" +
(i + 1) + ").PACGS2(" + (j + 1) + ").";
else if (kindOfPackValue.equals("NE") ||
interaction kindOfPackValue.equals("NF") ||
kindOfPackValue.equals("NG")) {
id[0] = FieldsInfo.NOT_USED;
id[1] = FieldsInfo.REQUIRED_NON_ZERO;
id[2] = FieldsInfo.OPTIONAL;
errorDescriptionStr = "Since the GOOITEGDS(" + (i + 1) + ").PACGS2(" + (j + 1) + ").KinOfPacGS23 " +
• The STTA rules can be used only for }
"has a value of '" + kindOfPackValue +
"' which indicates UNPACKED ('NE', 'NF', 'NG'), the GOOITEGDS(" + (i + 1) +
").PACGS2(" + (j + 1) + ").";
validation and returning error (906) else {
id[0] = FieldsInfo.REQUIRED;
id[1] = FieldsInfo.NOT_USED;
id[2] = FieldsInfo.REQUIRED;
errorDescriptionStr = "Since the GOOITEGDS(" + (i + 1) + ").PACGS2(" + (j + 1) + ").KinOfPacGS23 " +
"has a value of '" + kindOfPackValue + "', the GOOITEGDS(" + (i + 1) +
").PACGS2(" + (j + 1) + ").";
}
((FieldsInfo) fieldInfo.elementAt(0)).setIdentification(id[0]);
((FieldsInfo) fieldInfo.elementAt(1)).setIdentification(id[1]);
((FieldsInfo) fieldInfo.elementAt(2)).setIdentification(id[2]);
checkField((Element) packagesNode, fieldInfo); // check if fields exist in doc
if (errorPointer != null) {
for (int x = 0; x < errorPointer.size(); x++) {
error = new RuleError();
error.setErrorType(15);
error.setErrorReason(this.toString());
error.setOriginalAttribOfNode("N/A");
error.setRuleName(this.toString());
error.setErrorPointer("GDS(" + (i + 1) + ").GS2(" + (j + 1) + ")." +
((FieldsInfo) errorPointer.elementAt(x)).getTagDescription());
error.setErrorDescription(errorDescriptionStr + (String) errorDescriptionList.get(x));
errors.addElement(error);
}
errorPointer.removeAllElements();
}
}
} // for loop for packages
} // for loop for good items
return (!(errors.size() > 0));
} // is rule valid method
}](https://image.slidesharecdn.com/alexievmitevbukev2010-egovbpm-110428011826-phpapp02/85/Implementing-complex-e-Government-solutions-with-open-source-and-BPM-Architecture-of-Export-Control-System-phase-2-ECS2-37-320.jpg)
![ECS2 at Java2Days, 8.10.2009 (Sirma Solutions & Sirma ITT) 38
•
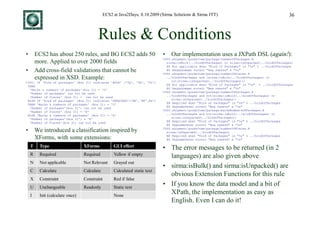
Rules Used for Validation and GUI
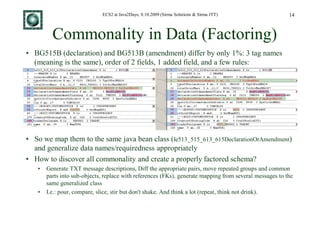
Consider this rule: C010:IF first digit of "Transport mode at border" (box 25) = 2, 5 or 7
THEN "Nationality crossing border" (box 21) is Optional ELSE Required
C010.shipment/nationalityOfMeansOfTransportCrossingBorder.R
• The implementation is simple (nothing for "Opt") not(sirma:RexexpMatch(../transportModeAtBorder,"^[257].*
EN Required when "Transport mode at border" does not start with 2, 5 or 7
BG Задължително когато "Вид транспорт на границата" не започва с 2, 5 или 7
• While editing: box 25 doesn't start with [257] so the field is Required (yellow). In this way the user can
see all erroneous fields at a glance. AJAX implementation: submits&receives only the changes.
• If the user hovers over the field, its tooltip gives error description (red text) and all details about the field
(tag name, box number, description, format, even codelist)
• If an incoming message has this defect, the same rule implementation returns appropriate error message
• Bilingual ErrDes handled
• CD906A doesn't have ErrDes, so we map
to OriAttVal](https://image.slidesharecdn.com/alexievmitevbukev2010-egovbpm-110428011826-phpapp02/85/Implementing-complex-e-Government-solutions-with-open-source-and-BPM-Architecture-of-Export-Control-System-phase-2-ECS2-38-320.jpg)
![ECS2 at Java2Days, 8.10.2009 (Sirma Solutions & Sirma ITT) 41
GUI: Features
• Hired a Usability consulting company (still most of the ideas are our own)
• Context-dependent "navbars" show important info
• User, office, role
• Number of movements per state in the current office, which are Quick Search links (from CL9058)
• Currently selected movement (sticks even if you switch office type), with links to its data
• Available actions (local and global); the most important ones are color-coded
• Bold shows the current context ("breadcrumb")
• Full type, length, regexp, requiredness, CL, R&C validation (yellow: required unfilled, red:
erroneous). JSF validators are generated from message definitions and R&C metamodel
• Tooltip gives all details about each field (tag, name, description, box number, error)
• Electronic signatures (PKI certificates) used for
trader access and document signing
• The same business data forms are used in ECS2 Web and DTI Web.
• The navbars ("chrome") vary per user kind (customs officer, trader) and roles/permissions
• Goods Pager: efficiently handles up to 999 goods, add item [+], direct jump, erroneous list](https://image.slidesharecdn.com/alexievmitevbukev2010-egovbpm-110428011826-phpapp02/85/Implementing-complex-e-Government-solutions-with-open-source-and-BPM-Architecture-of-Export-Control-System-phase-2-ECS2-41-320.jpg)