Embed presentation
Download as PDF, PPTX





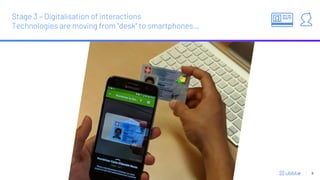

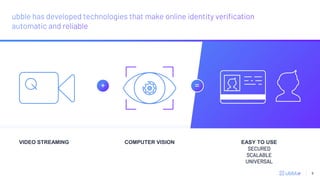


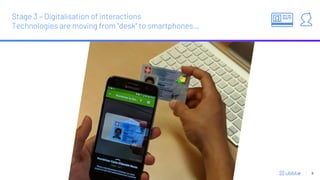
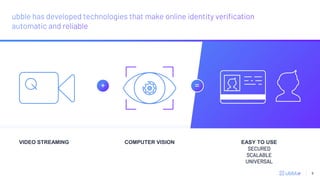
Identity fraud is a growing problem that costs societies billions each year. Traditional identity verification methods rely on trained agents but new technologies are aiming to automate the process using AI and computer vision. One company, Ubble, has developed an identity verification system using video streaming, computer vision, and AI to automatically verify identities in a way that is easy to use, secure, scalable, and universal without the need for an in-person agent.