Rachel O'Connell is a research consultant who has studied effective age verification techniques. Her presentation discusses how age verification and identity management are reaching a tipping point due to emerging technologies and data sources. These include electronic IDs, mobile IDs, trust frameworks, and personal data empowerment tools. In the future, a variety of data sources could be accessed and permissioned to verify attributes like age for business purposes. This would allow underserved groups like minors to participate more in the digital economy while protecting privacy and enabling new social contracts and regulatory systems.



![ELECTRONIC ID
•
•
•
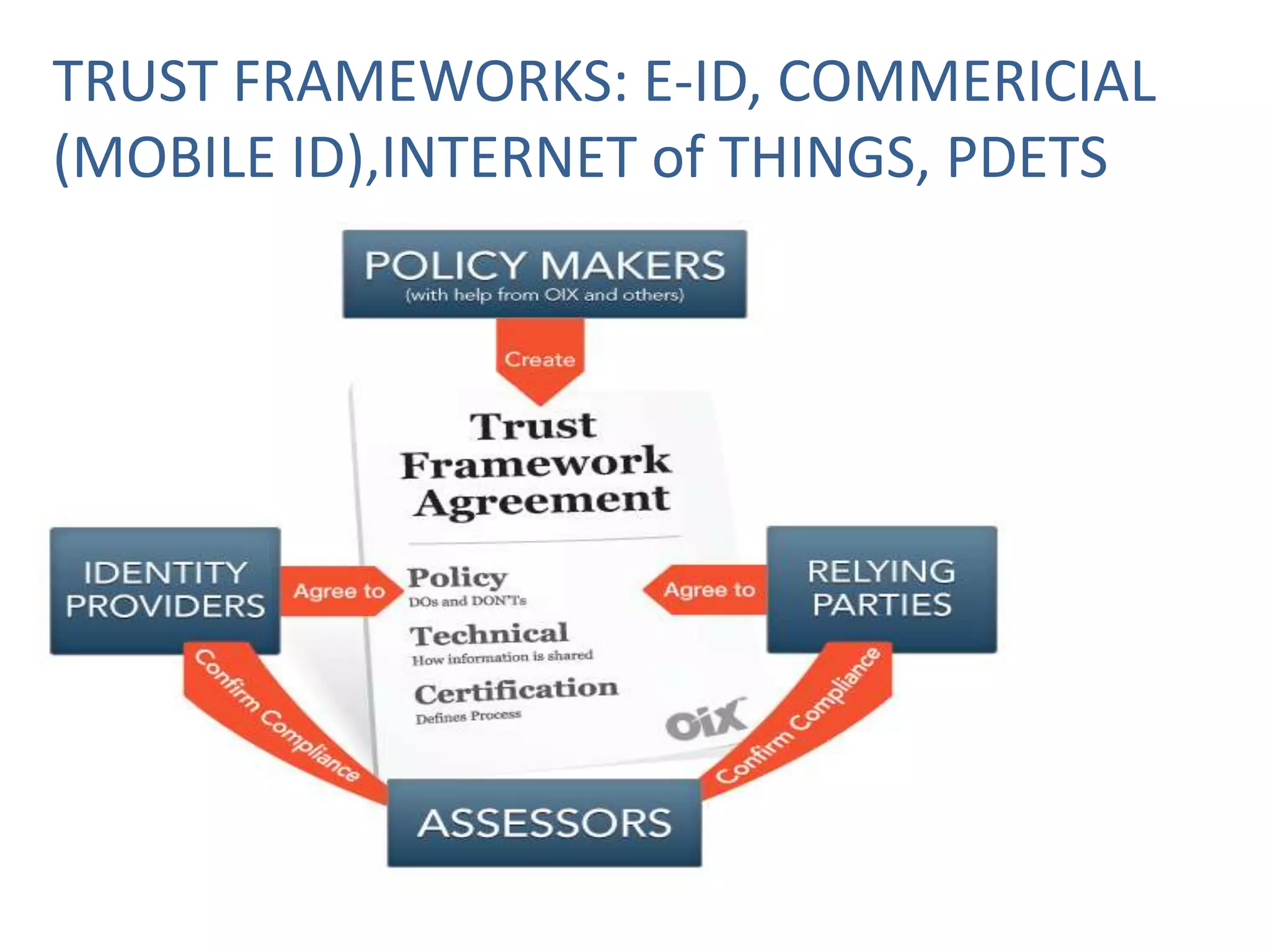
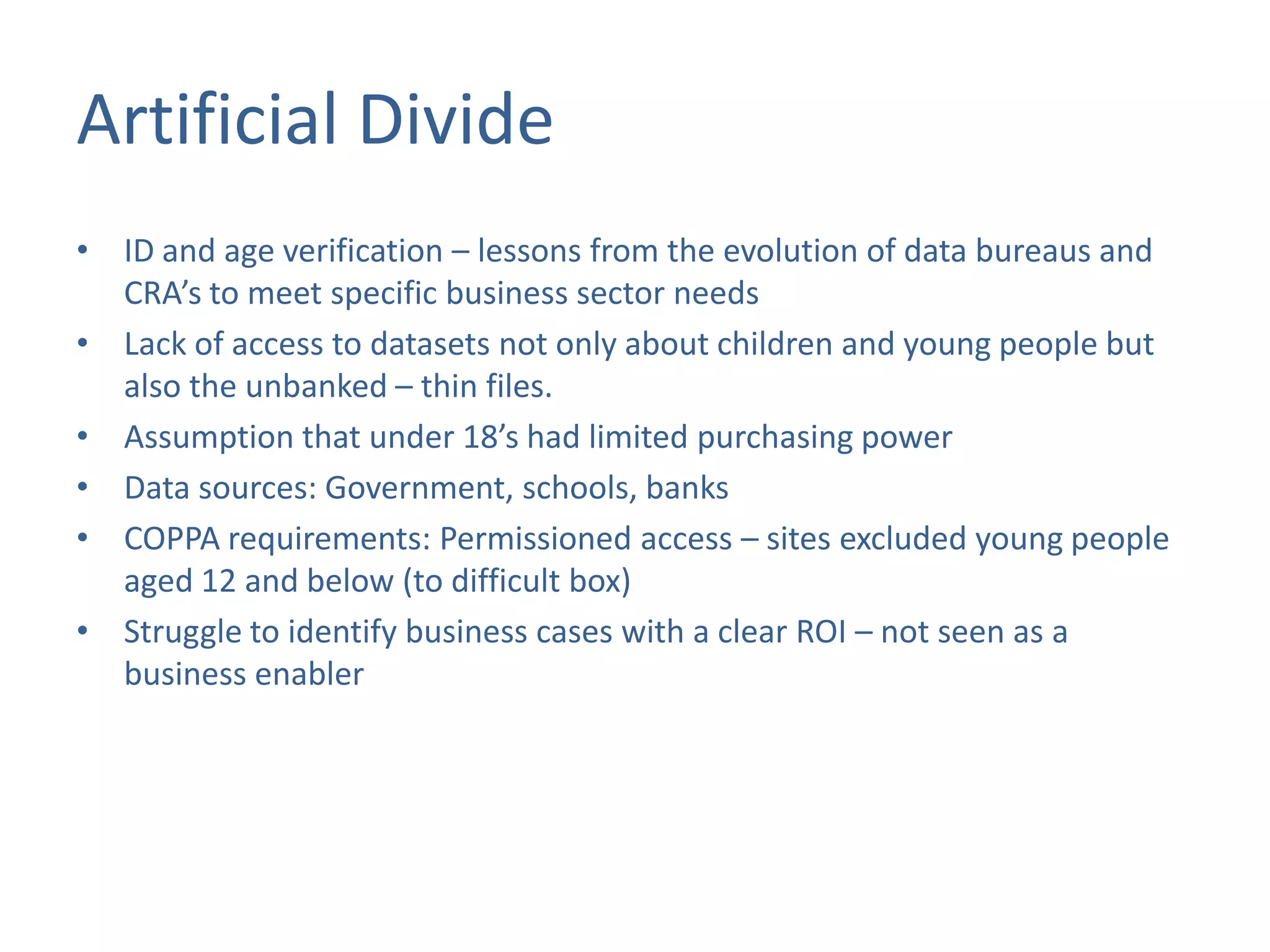
Electronic identity ecosystems are a key enabler of the
“digital economy”
NSTIC aims to enable “Individuals and organizations [to]
utilize secure, efficient, easy-to-use, and interoperable
identity solutions to access online services in a manner that
promotes confidence, privacy, choice, and innovation.”
•
Provide scalable, privacy preserving, commercially viable,
privacy preserving permissioned use of attributes.
STORK
•
Proposed regulation
•
Alpha project – retailers
•
Reducing the barriers to permissioned use of age
attributes](https://image.slidesharecdn.com/ageverification-reachingatippingpoint-131022055735-phpapp01/75/Age-Verification-Reaching-a-Tipping-Point-9-2048.jpg)