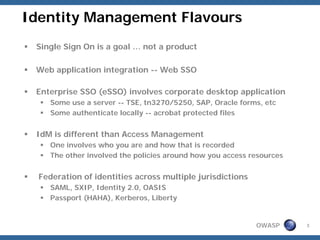
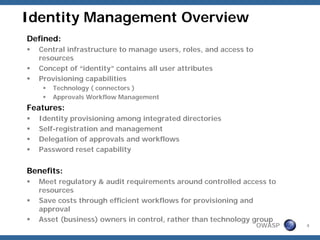
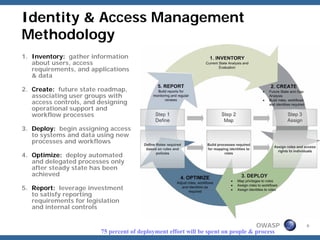
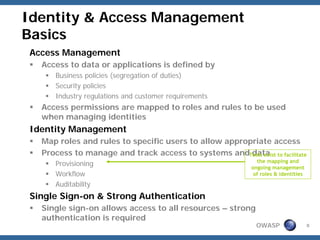
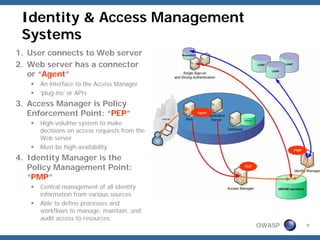
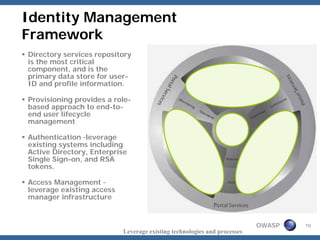
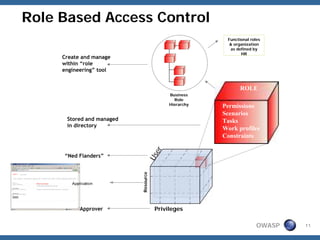
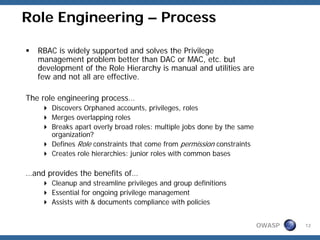
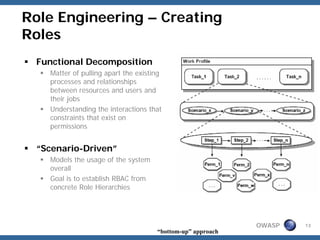
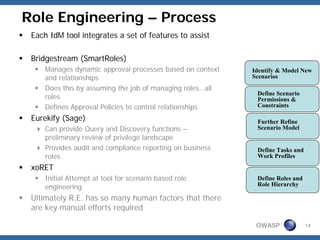
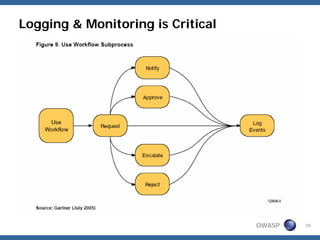
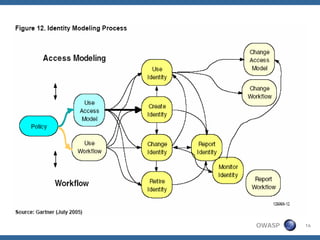
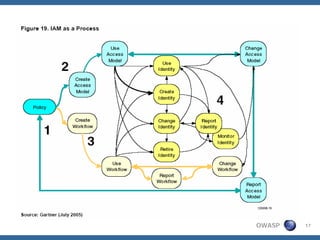
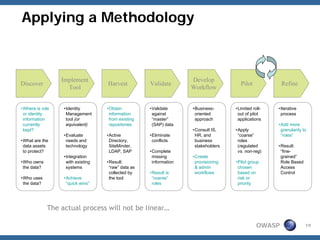
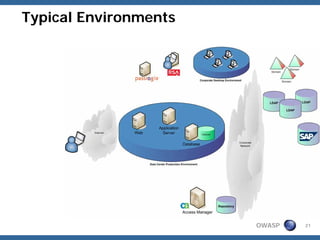
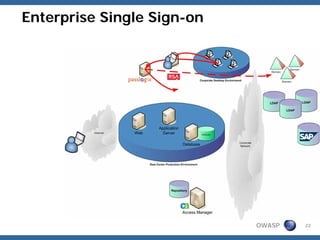
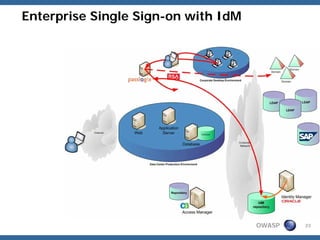
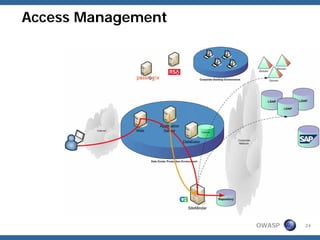
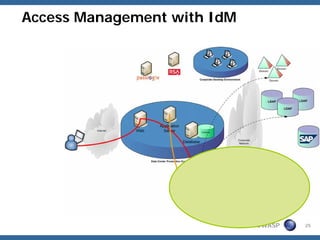
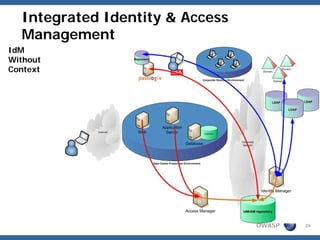
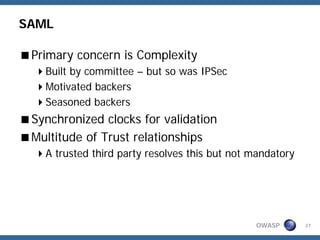
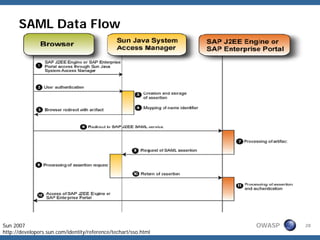
The document provides an overview of identity management basics. It discusses key concepts like single sign-on, enterprise SSO, identity management, access management, and federation of identities. It outlines an identity and access management methodology of inventorying, creating, deploying, and optimizing access. Role-based access control is also summarized, including how roles map to user permissions and are defined through a role engineering process involving functional decomposition and scenario-driven approaches.