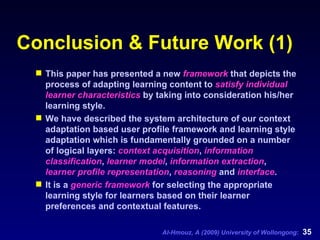
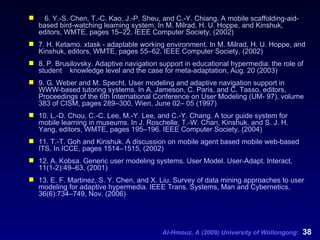
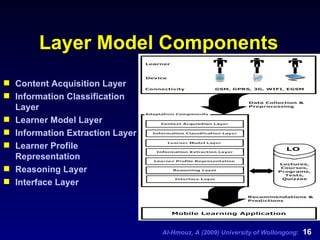
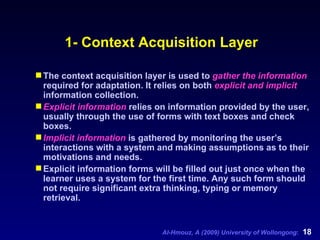
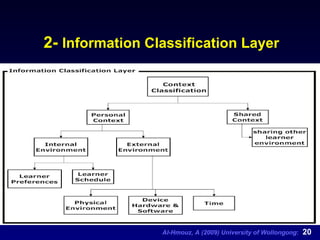
This document presents a machine learning-based framework for adaptive mobile learning (m-learning) aimed at personalizing the learning experience based on user-specific profiles and contextual information. The framework consists of several layers, including context acquisition, information classification, and learner model layers, which work together to adapt learning content and enhance the interaction between the user and the system. The authors also outline future work that includes ongoing implementation and evaluation of the system's effectiveness.
![Ahmed Al-Hmouz, Jun Shen & Jun Yan School of Information Systems & Technology, University of Wollongong Wollongong, New South Wales, Australia aa998 @uow.edu.au , [email_address] , [email_address] A Machine Learning based Framework for Adaptive Mobile Learning International Conference on Web-based Learning (ICWL): August 19th, 2009 RWTH Aachen University, Aachen, Germany](https://image.slidesharecdn.com/al-hmouz-090822183634-phpapp02/85/ICWL-2009-1-320.jpg)
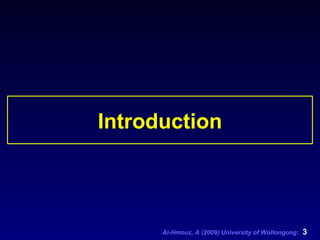
![Introduction (1) Electronic learning (e-learning) continues to grow rapidly but most e- learning technology involves wired infrastructures. Mobile learning (m-learning) is “any sort of learning that happens when the learner is not at a fixed, predetermined location, or learning that happens when the learner takes advantage of learning opportunities offered by mobile technologies” [1]. It is believed that the emerging wireless and mobile networks will provide new applications in m-learning. With the rapid evolution of mobile devices such as PDAs, Table PCs and smart phones, pervasive (or ubiquitous) systems are becoming increasingly popular.](https://image.slidesharecdn.com/al-hmouz-090822183634-phpapp02/85/ICWL-2009-4-320.jpg)
![Introduction (2) Given the rapid use of mobile technologies for facilitating the learning process anywhere and anytime, learners are able to use idle time, for example, when waiting for public transport, in between lectures, and travelling to and from university. This time can therefore be used more efficiently in terms of learning [2]. The awareness of learning context is important. A learning system should adapt the learning process in response to context change. The main goal for context-aware mobile learning application is to sense the mobile learner’s situation (environment) and respond to it [3]. Most current learning contents were designed for use with desktop computers and high-speed network connections. They usually contain rich media data such as image, audio, and video.](https://image.slidesharecdn.com/al-hmouz-090822183634-phpapp02/85/ICWL-2009-5-320.jpg)
![Related Work (1) Martin designed a system for recommending activities for learners; this process is dependent on the learner’s personal attributes, actions and the current context (location, time, available devices) [4]. Ogata and Yano designed a context-aware language learning support system for learning Japanese polite expressions [5]. The MOBIlearn project is an interactive model in which data is collected from sensors, and translated to appropriate services. In Mobile scaffolding-aid-based bird-watching learning system, an outdoor learning system is proposed, meaning that a learner with higher learning efficiency will gain less support from the system [6].](https://image.slidesharecdn.com/al-hmouz-090822183634-phpapp02/85/ICWL-2009-8-320.jpg)
![Related Work (2) Ketamo have implemented an m-learning environment (xTask) that adapts to different user devices (PC, PDA and WAP devices) [7]. Few of the m-learning researchers have tackled the problems of adaptation of learning tasks and personalization of course content based on students’ models, learning styles and strategies [8]. These issues have been explored within the traditional web-based systems in numerous well-known projects. ELM-ART is an intelligent learning website environment that supports example based programming [9]. Museum tour guide is another research used mobile devices personal museum expert which is mainly concerned with user location [10].](https://image.slidesharecdn.com/al-hmouz-090822183634-phpapp02/85/ICWL-2009-9-320.jpg)
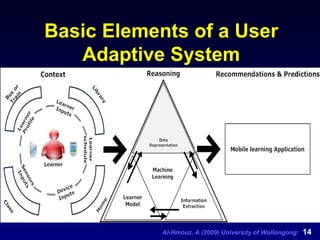
![Framework Foundation (1) User adaptive systems aim to adapt learning content , location and presentation to each individual user’s characteristics or behavior in order to improve the interaction between users and the system. The process is based on storing and exploiting information about the user. However, users differ in traits such as skills, aptitudes and preferences for processing information, constructing meaning from information, and applying it to real-world situations. Modelling the users’ behavior is a fundamental mechanism for providing personalization [11]. Depending on the application, user profiles are generated to store information about user preferences, interests, goals, usage data and interactive behavior.](https://image.slidesharecdn.com/al-hmouz-090822183634-phpapp02/85/ICWL-2009-11-320.jpg)
![Framework Foundation (2) User preference is an important concept to predict user behaviors and make appropriate adaptation actions. Preferences can be explicitly supplied by the user [12]. A Personalization Engine is usually employed to infer adaptation actions on the basis of identified user characteristics, for retrieving or filtering appropriate content and adapting the content presentation, and to match the navigation support and the interface attributes to the user needs. Adaptive system uses the knowledge given by learner models to implement the following tasks [13]: Recommendation and Classification.](https://image.slidesharecdn.com/al-hmouz-090822183634-phpapp02/85/ICWL-2009-12-320.jpg)
![6- Reasoning Layer The output of this layer is a set of structural descriptions of what has been learned about user behavior and user interests. Any machine learning techniques based on adaptation should consider the following conditions to provide a wide range of possibilities on m-learning [5]: the amount of effort required to provide the system with necessary background knowledge, the amount of time (computational time) required, the amount of input data required to be able to make useful decisions, the appropriate handling of noise and uncertainty , and validity . The details of machine learning based adaptation are beyond the scope of this paper and will be addressed in future research.](https://image.slidesharecdn.com/al-hmouz-090822183634-phpapp02/85/ICWL-2009-28-320.jpg)