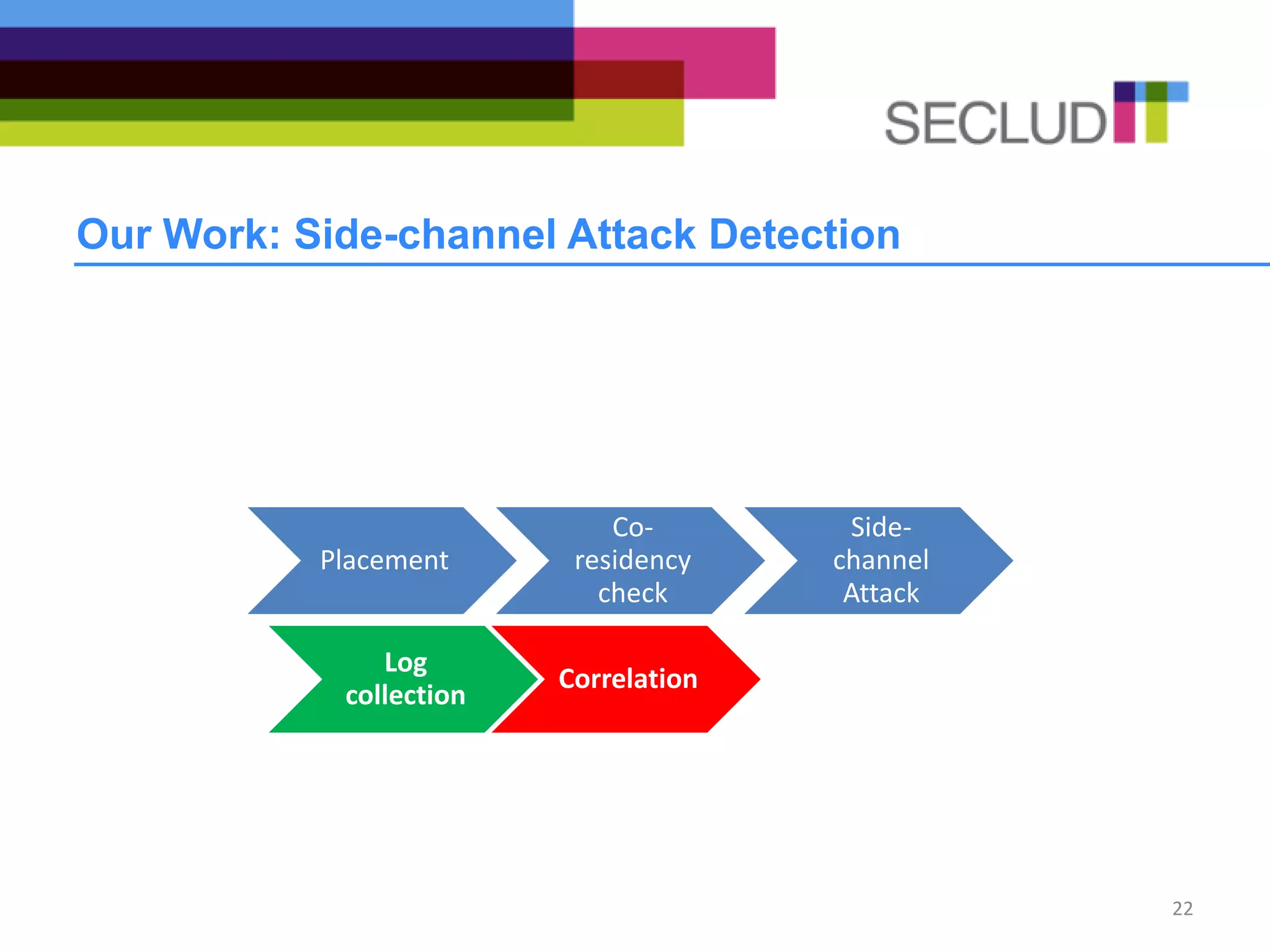
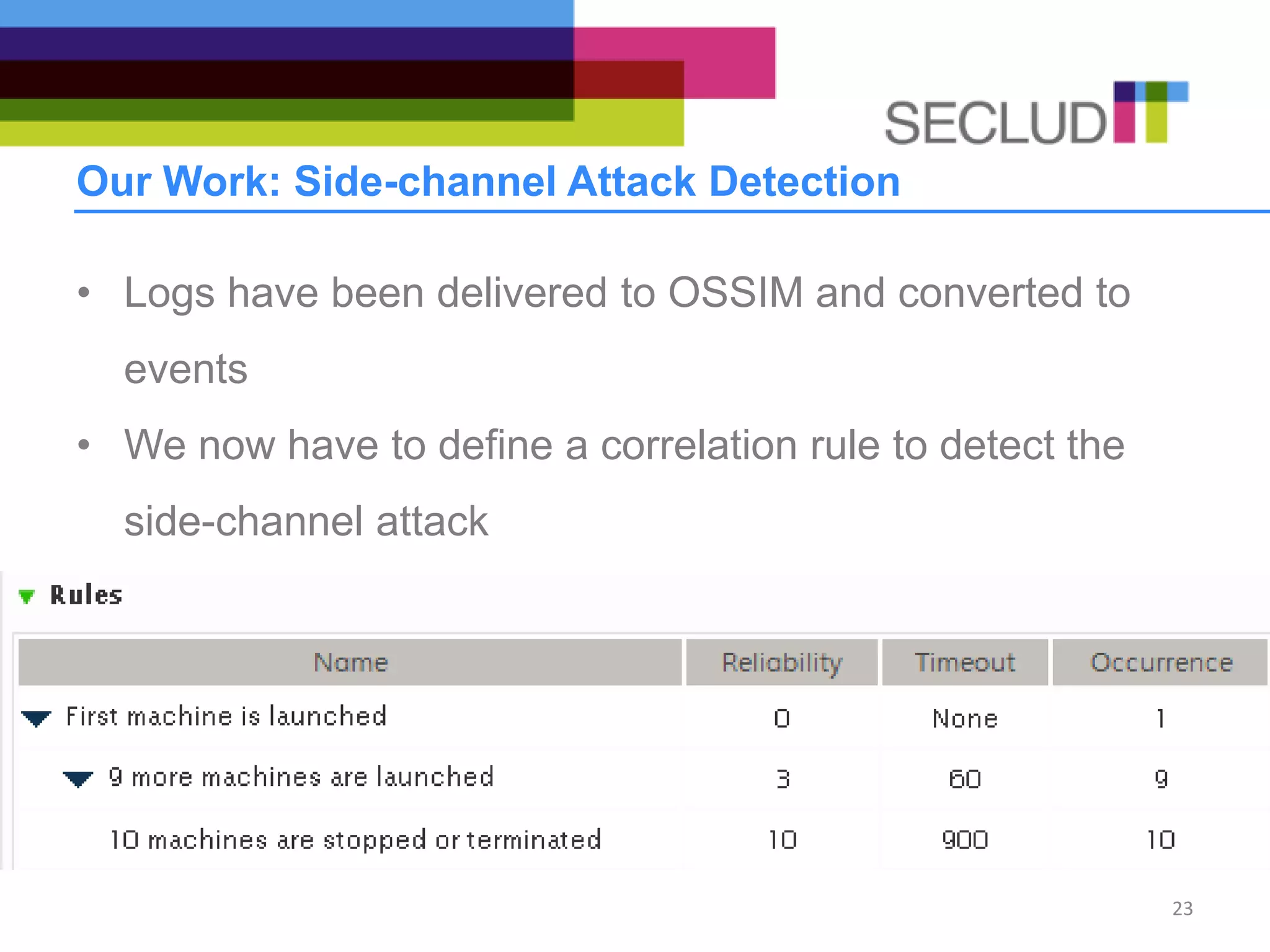
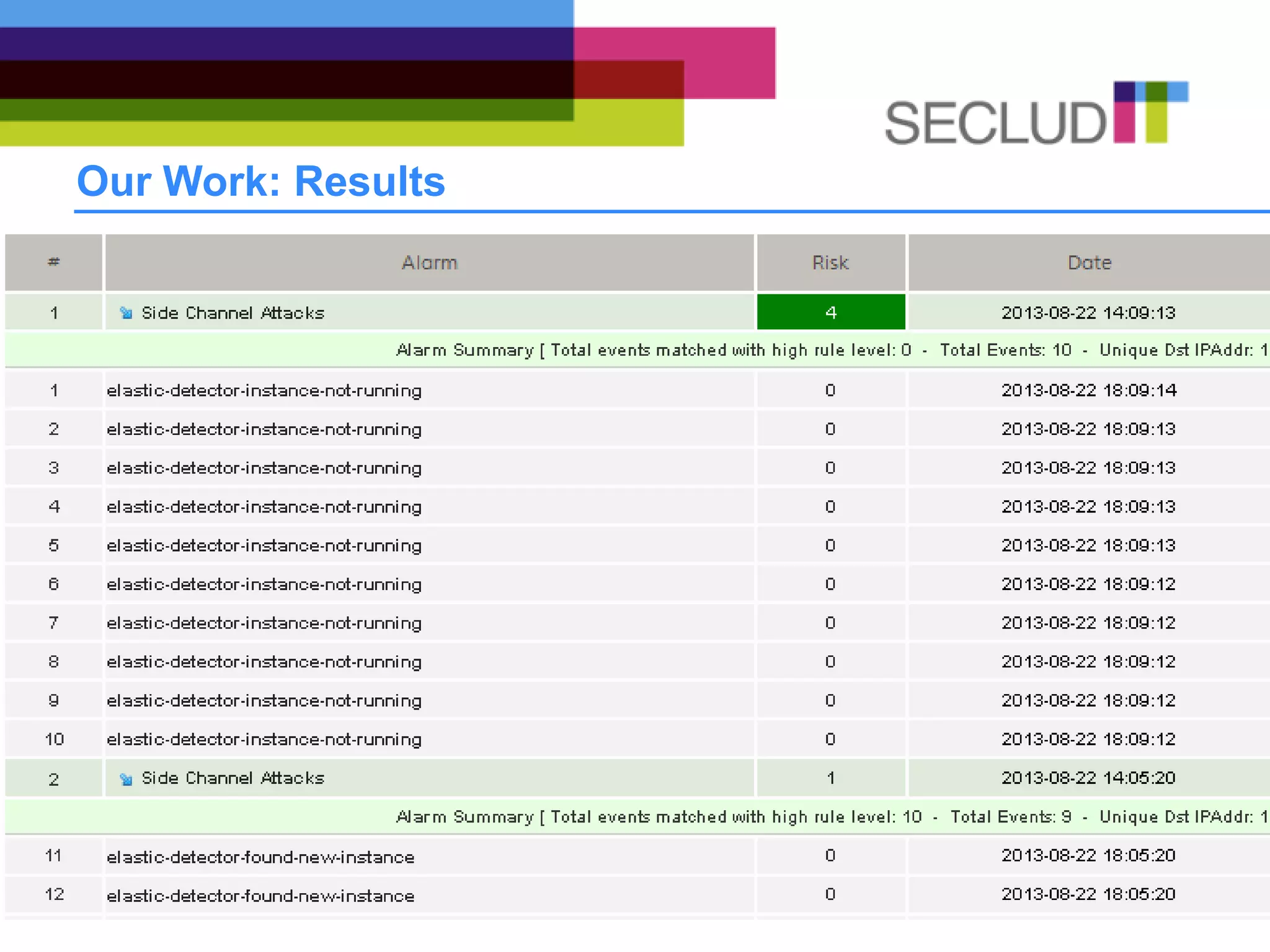
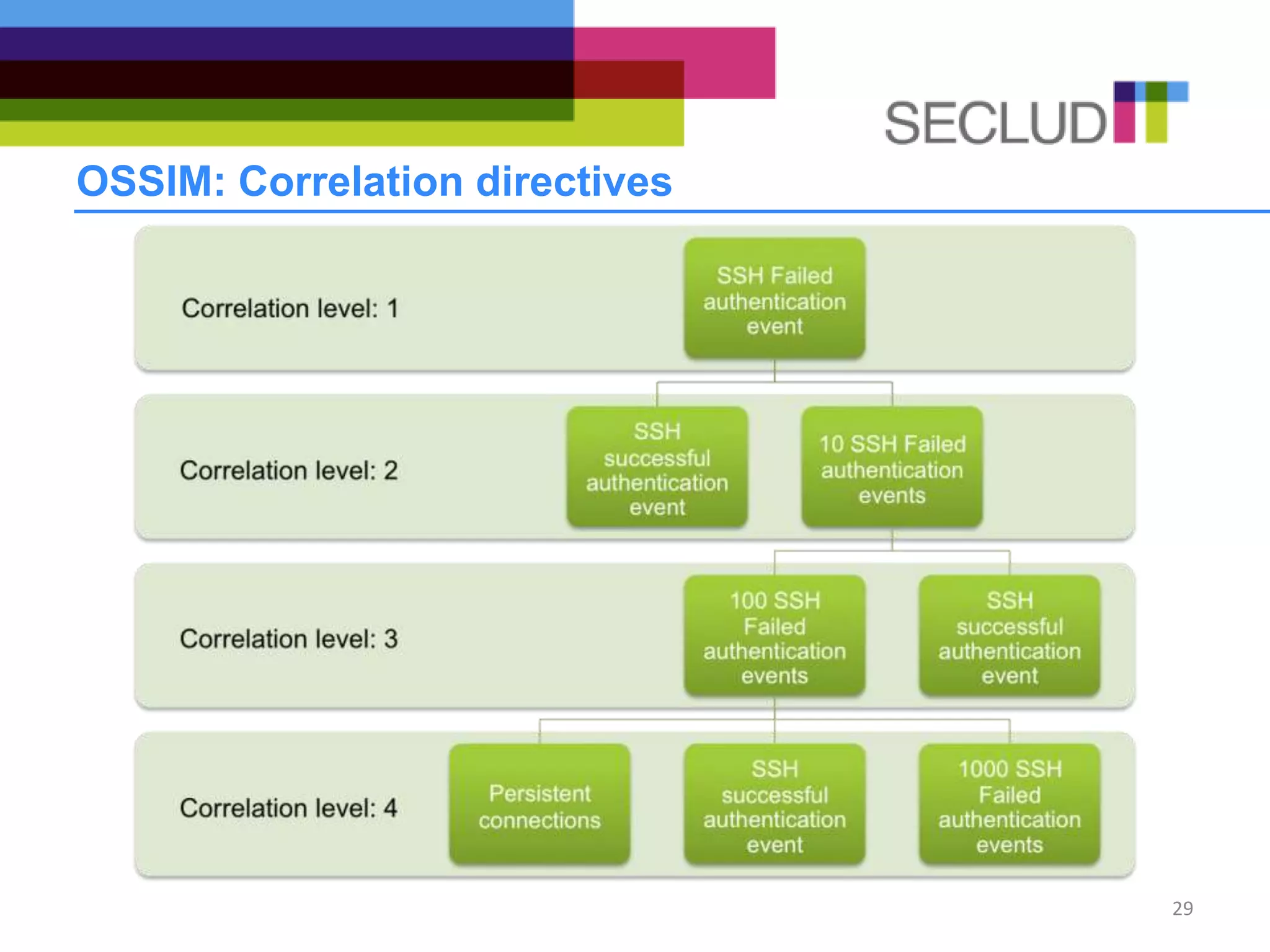
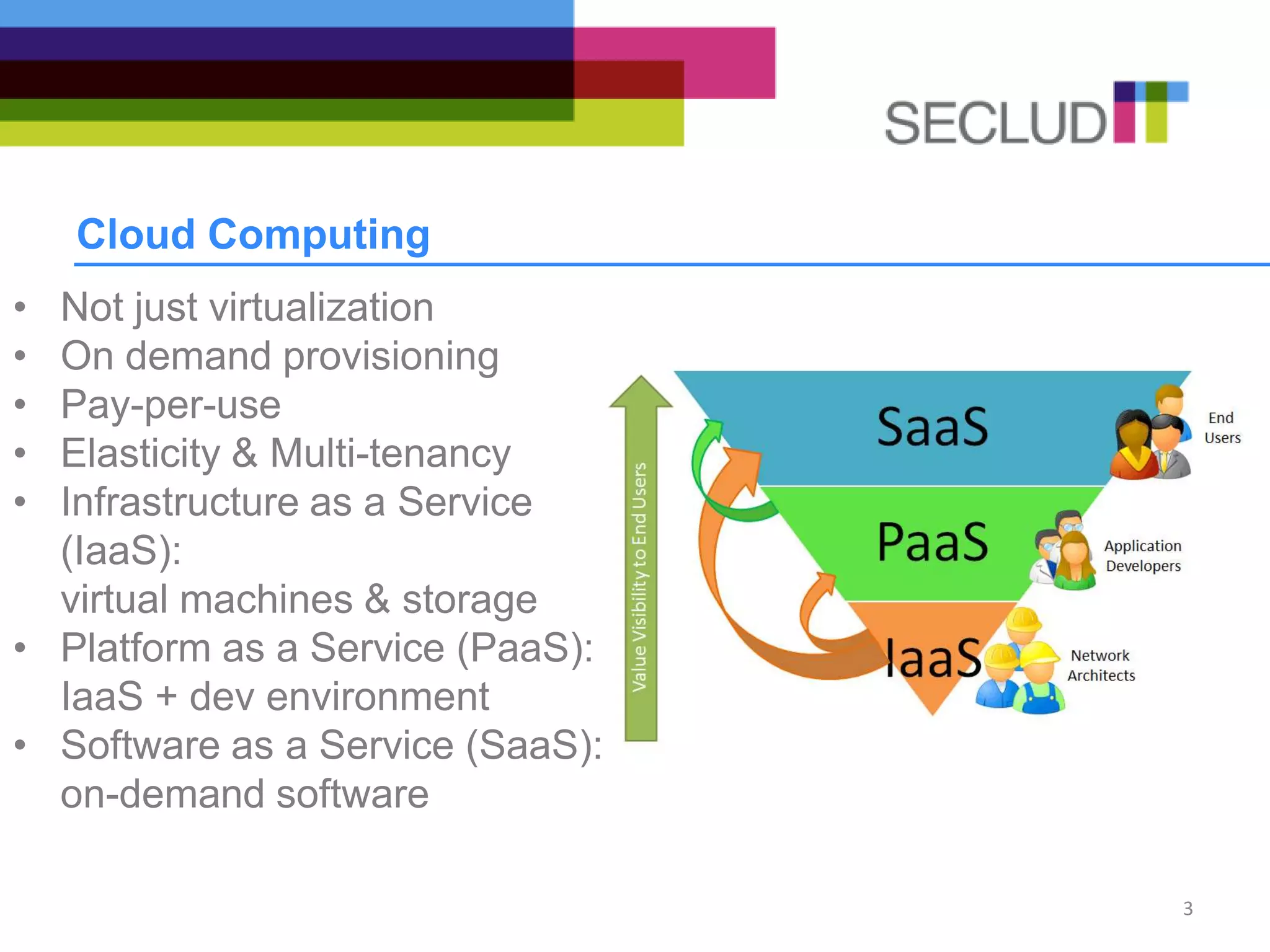
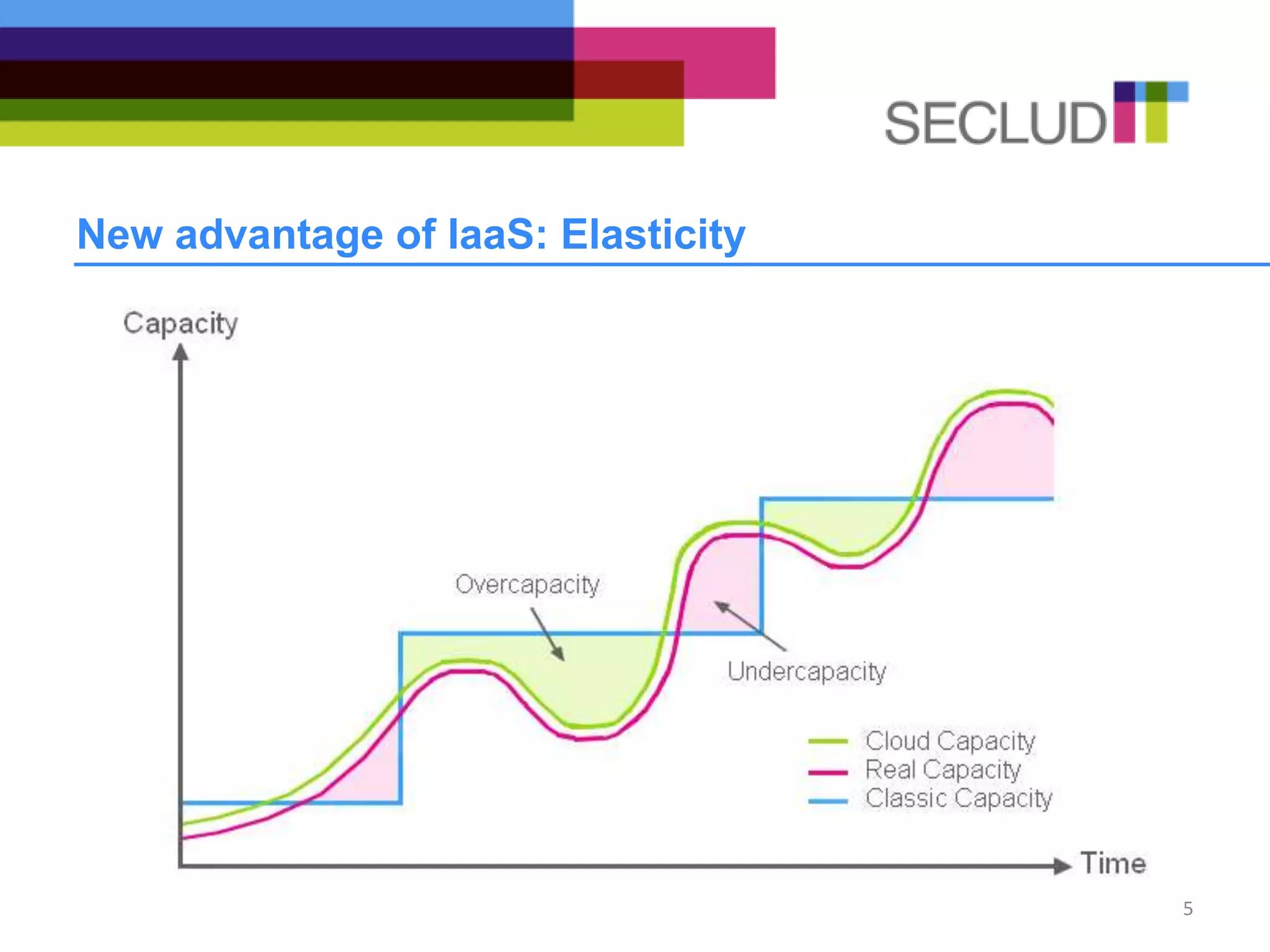
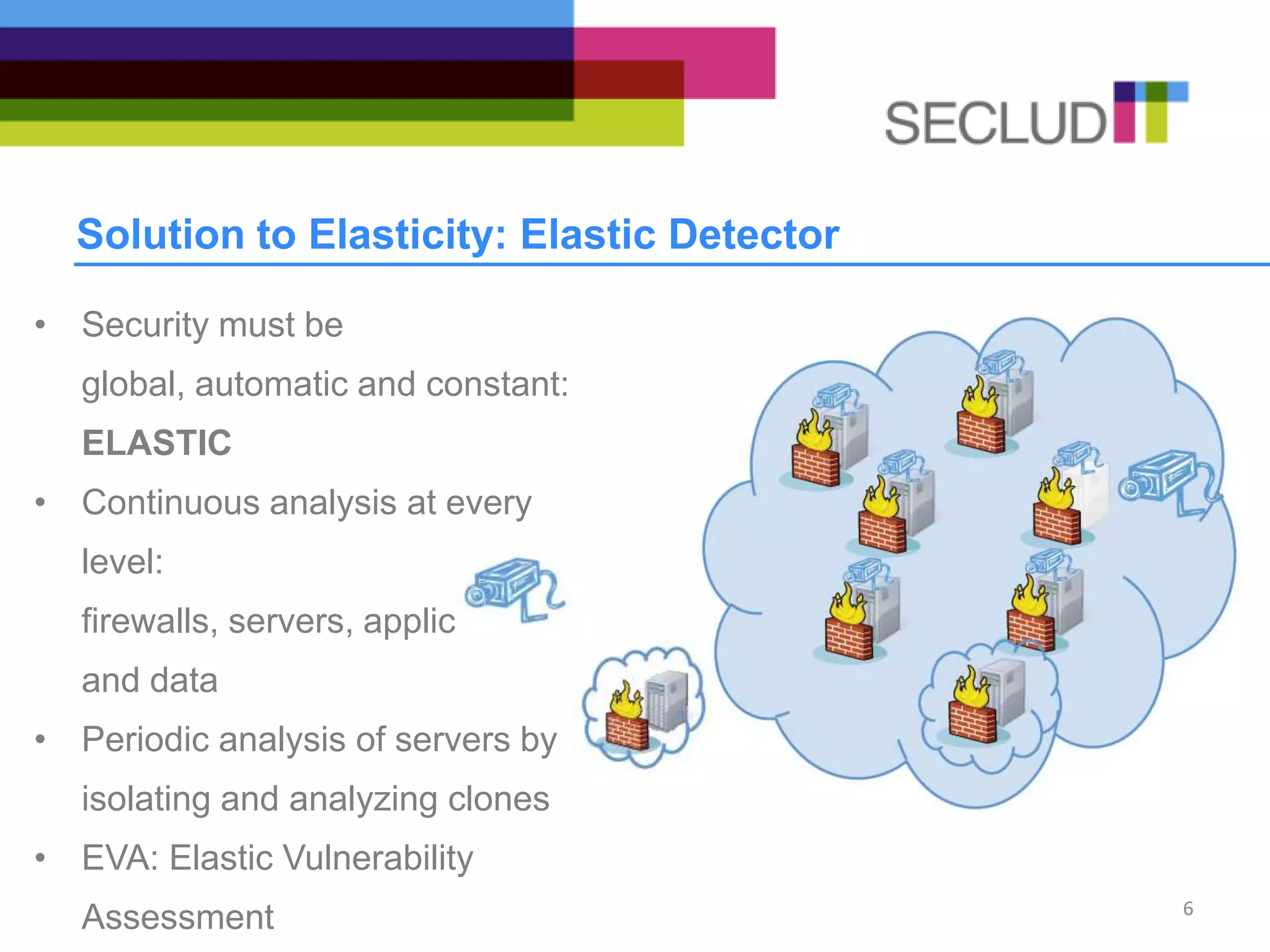
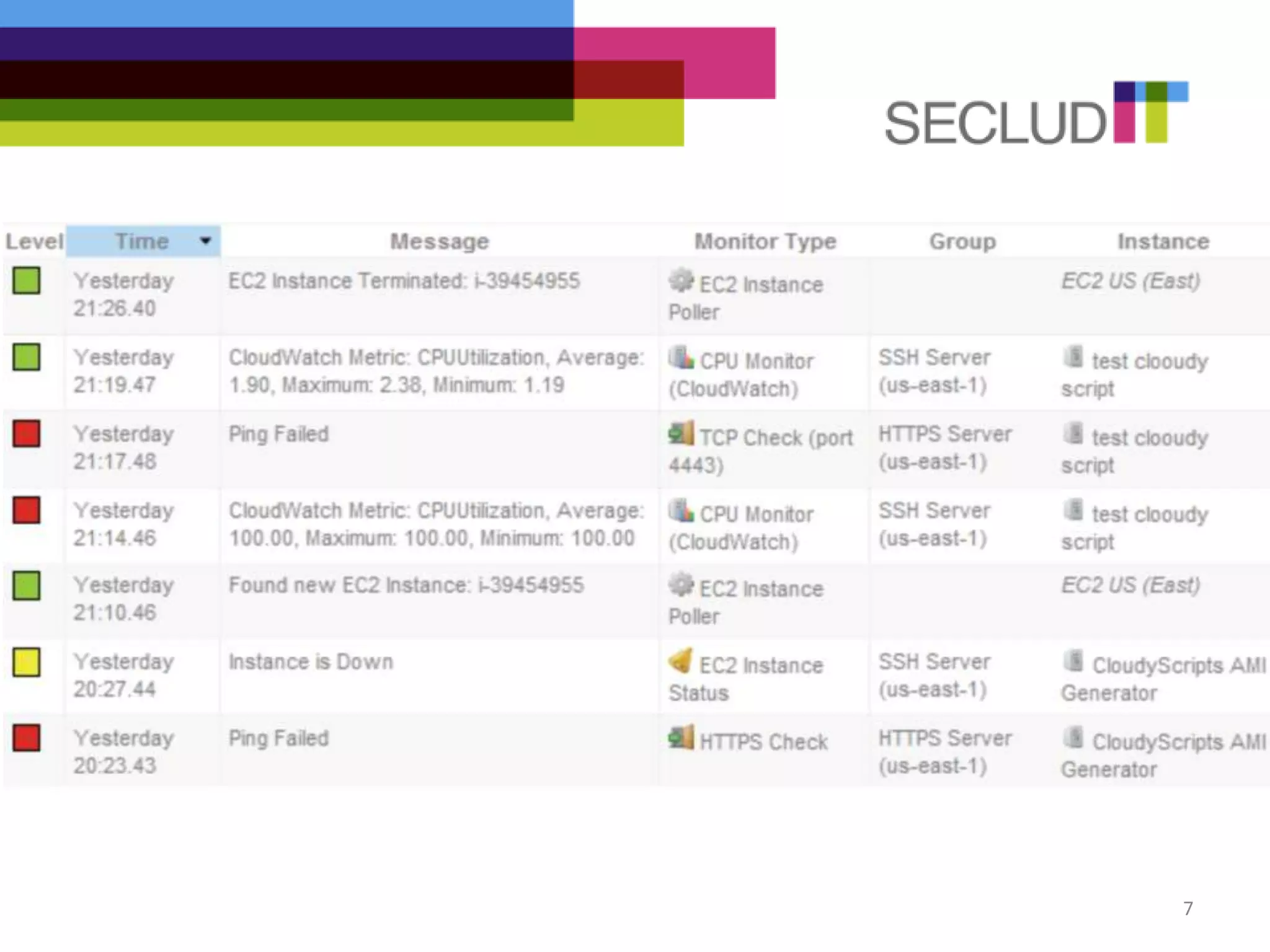
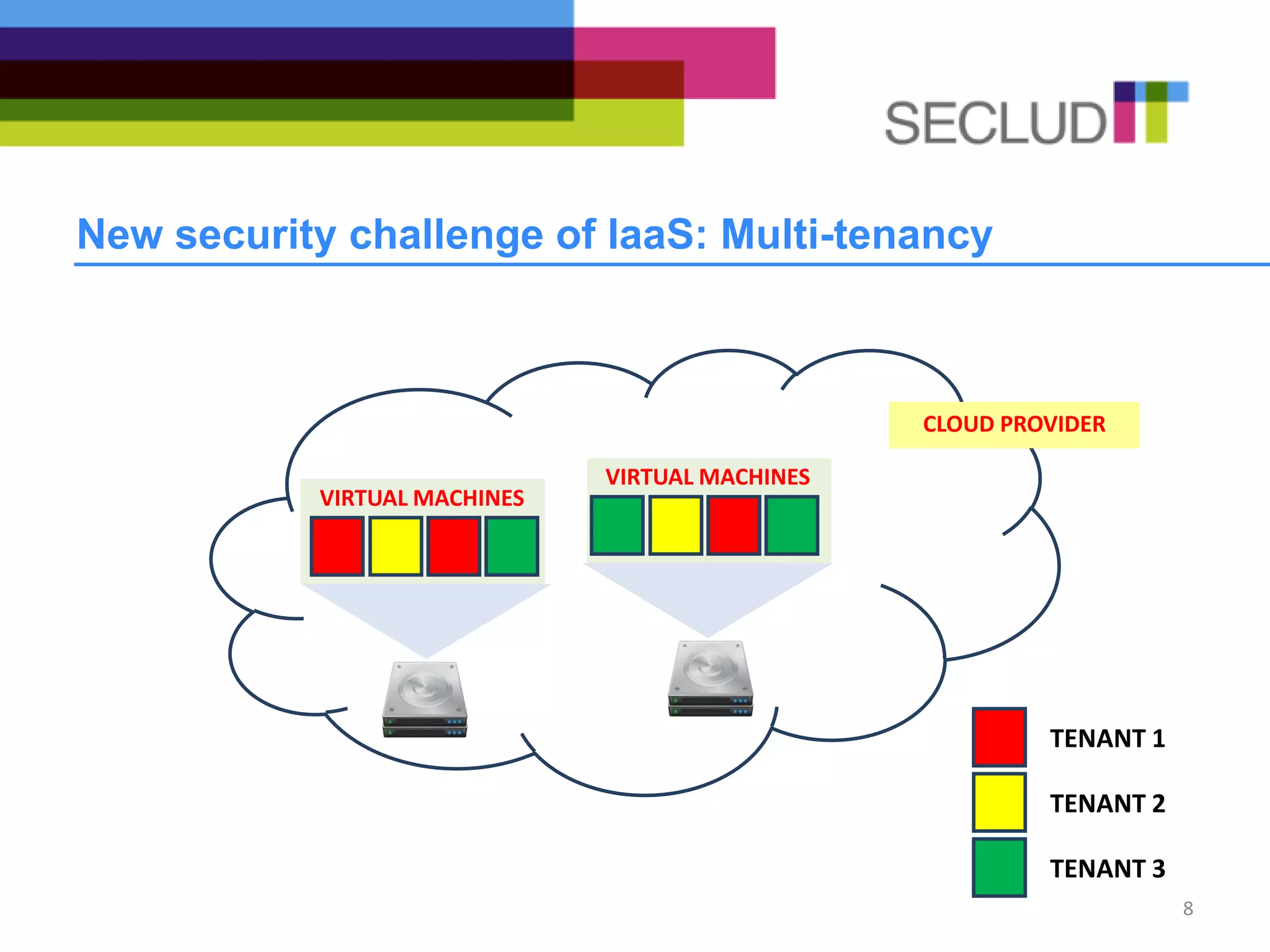
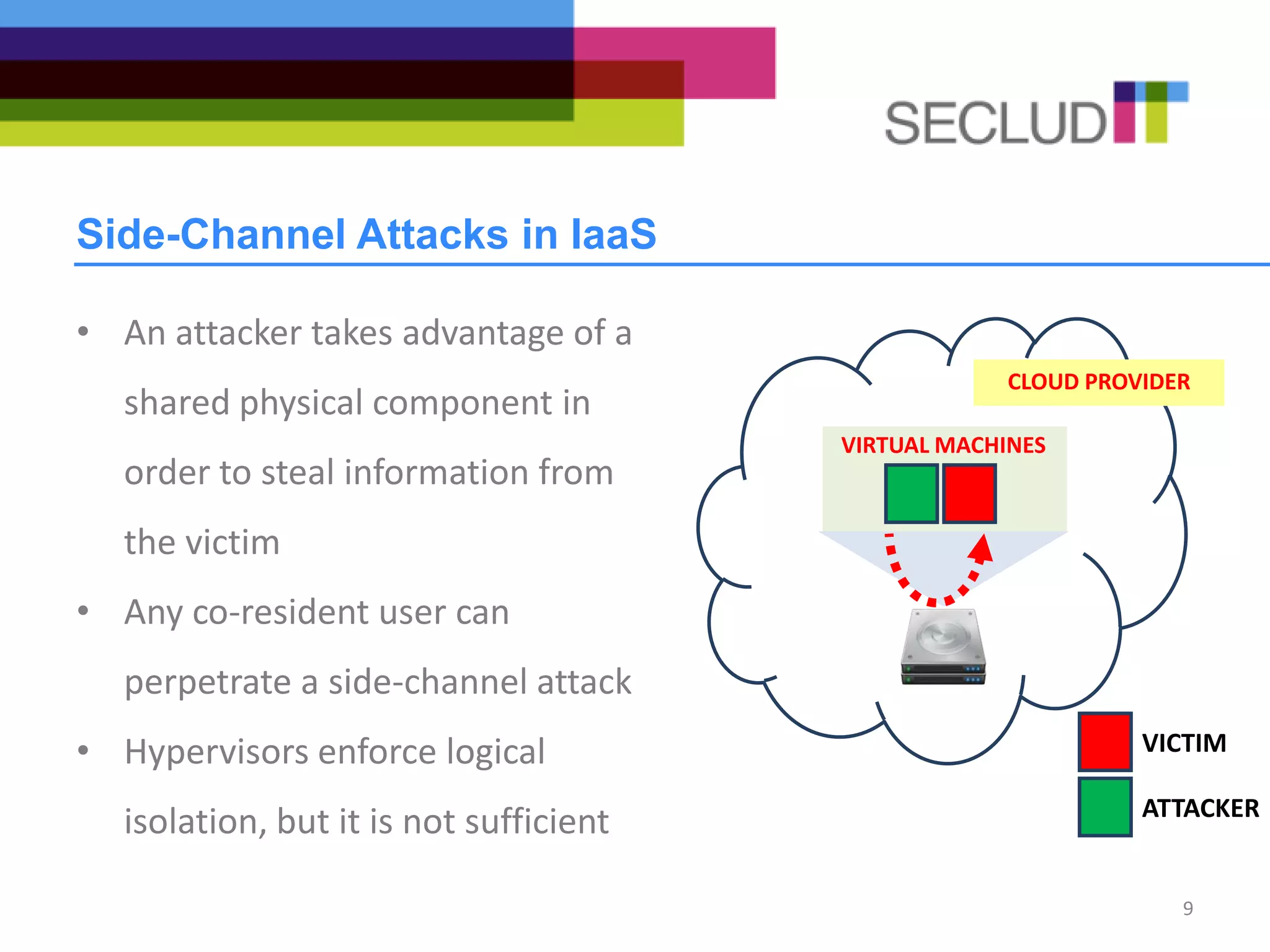
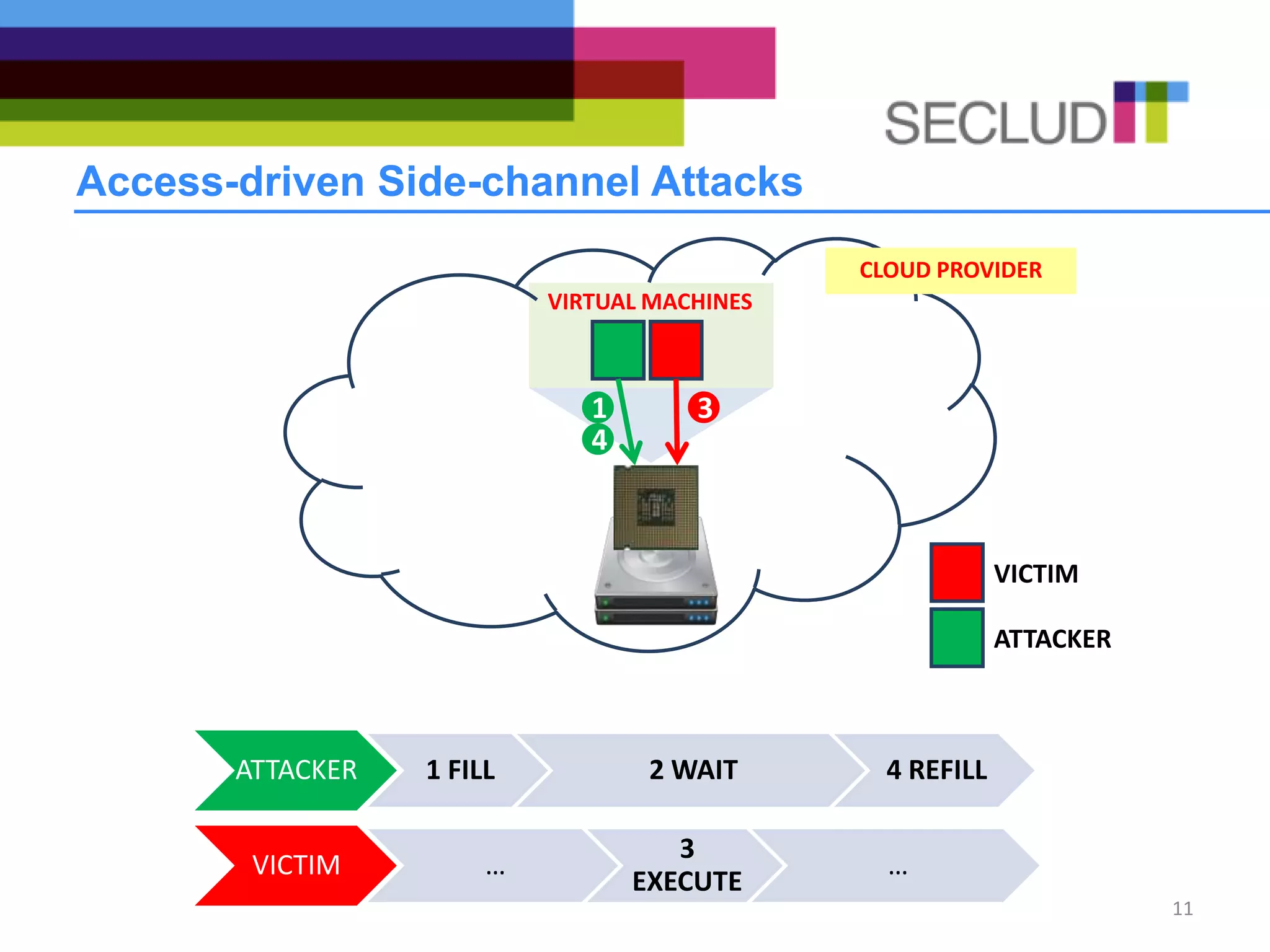
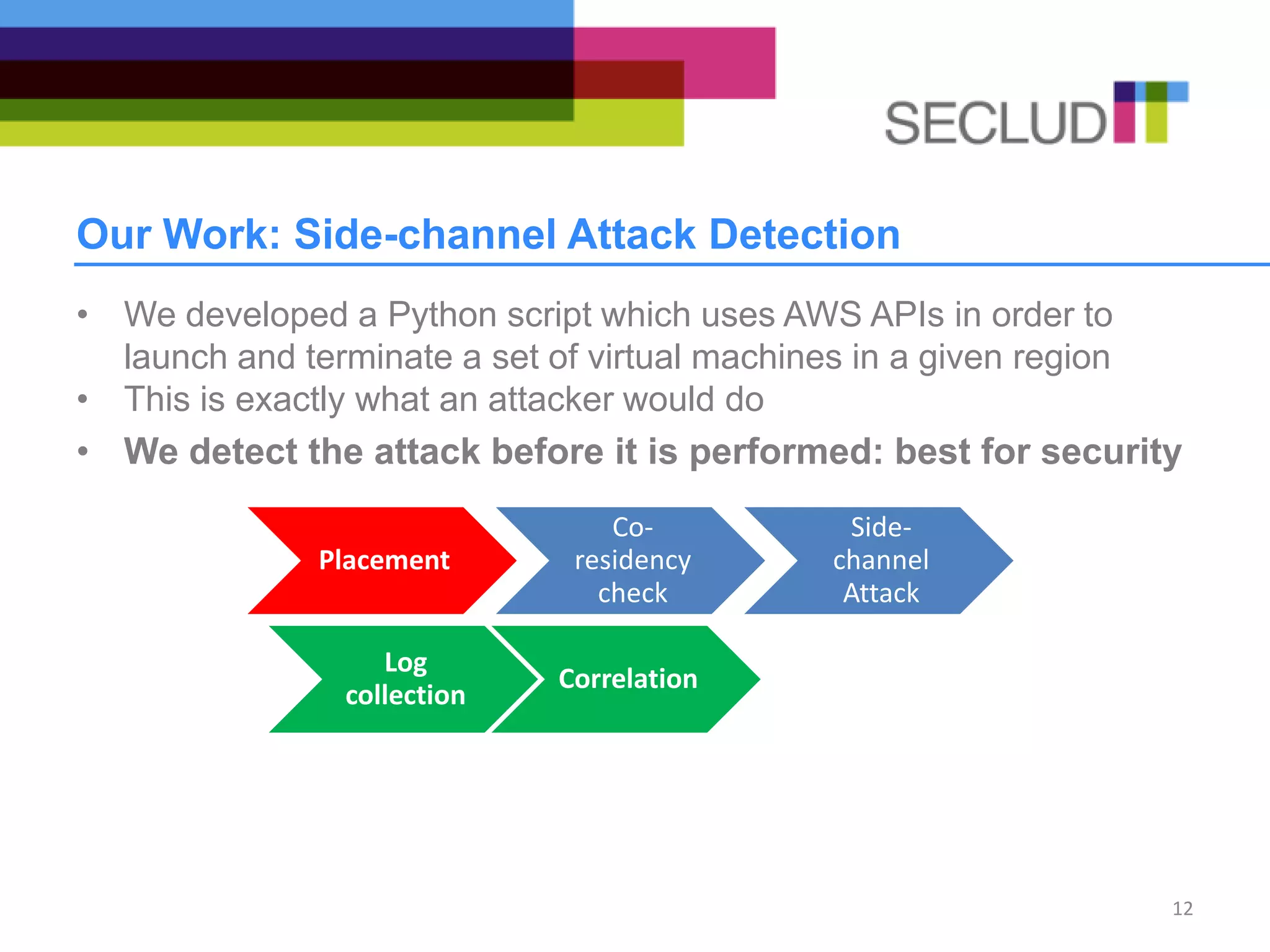
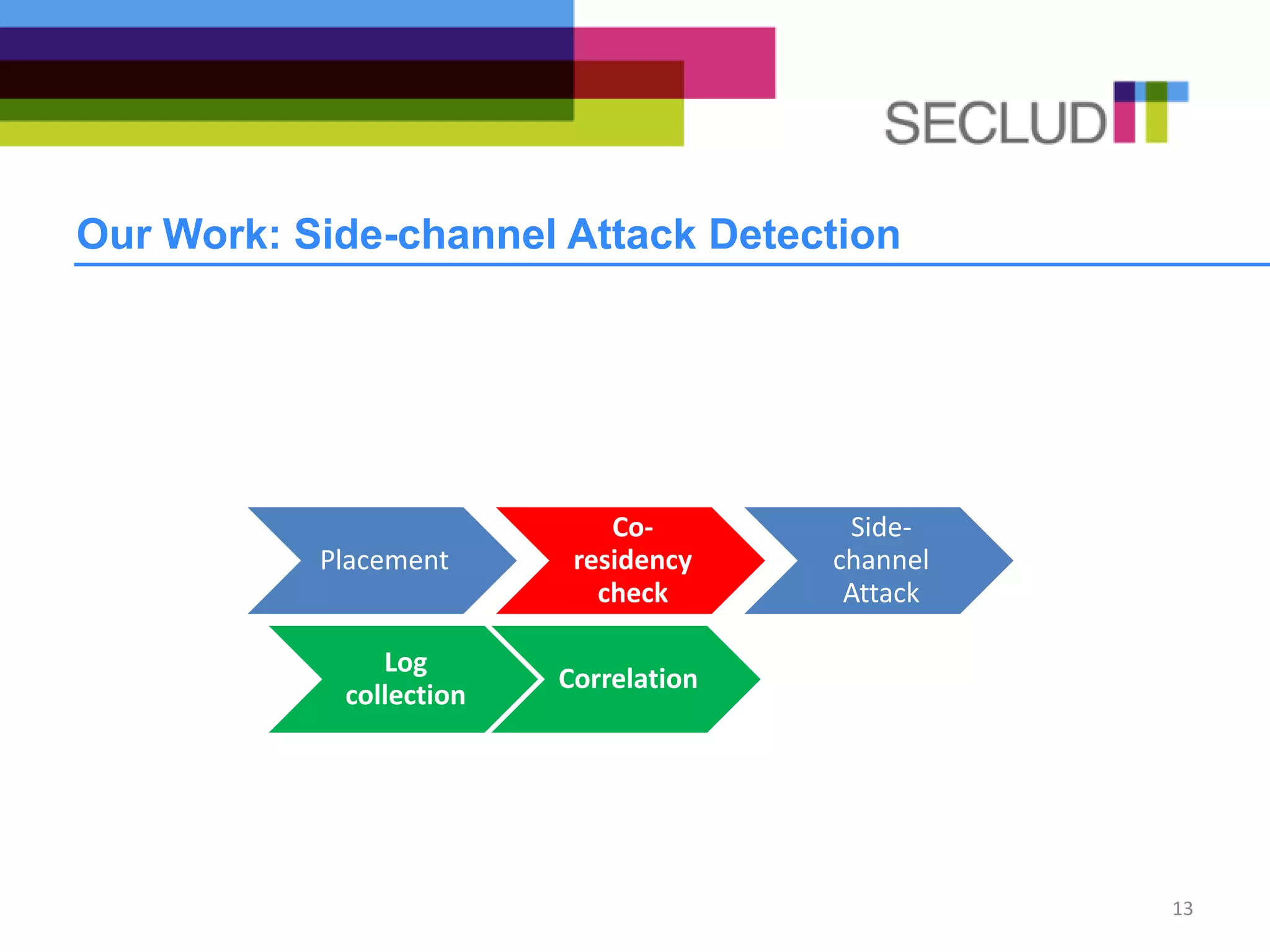
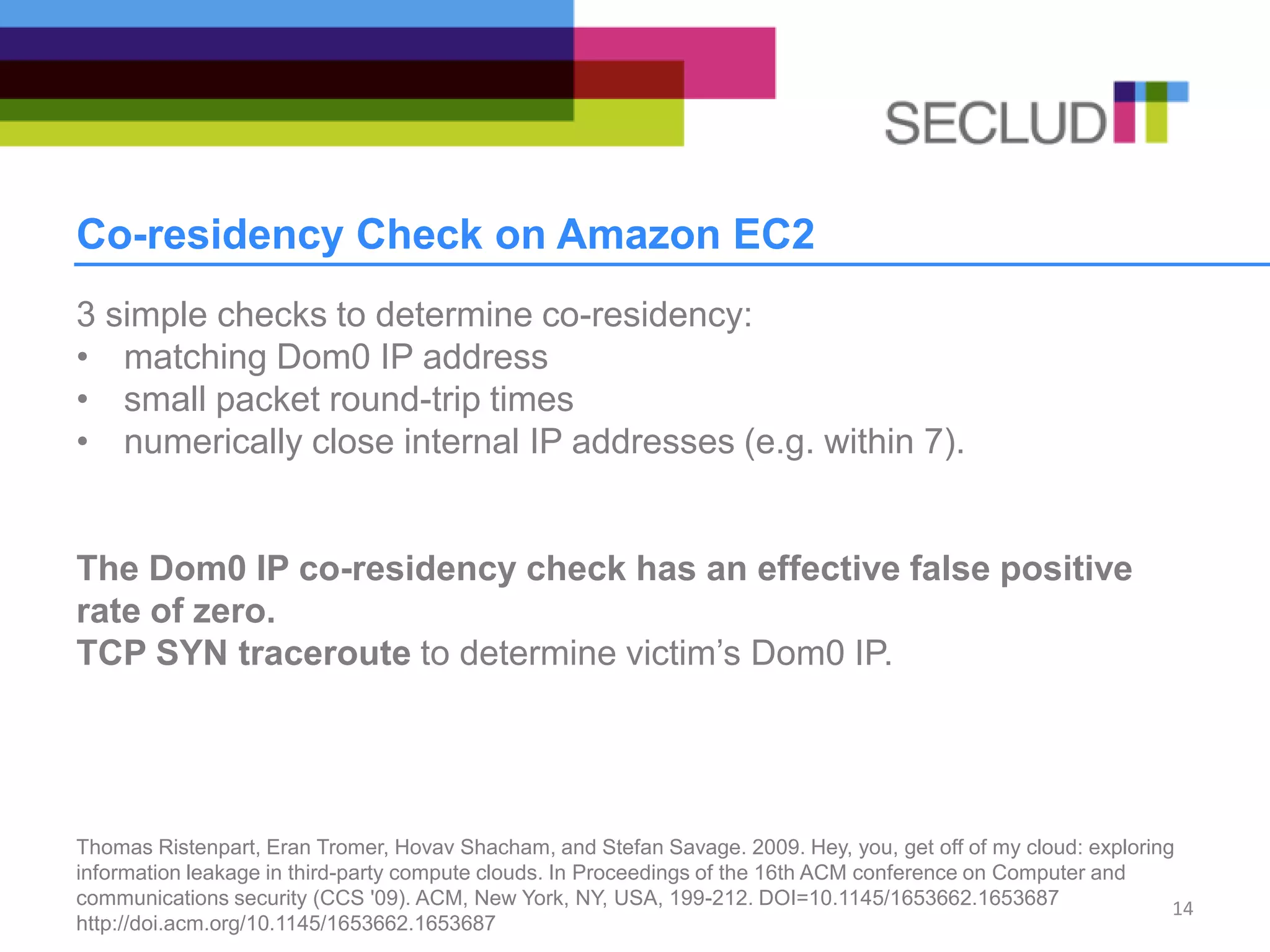
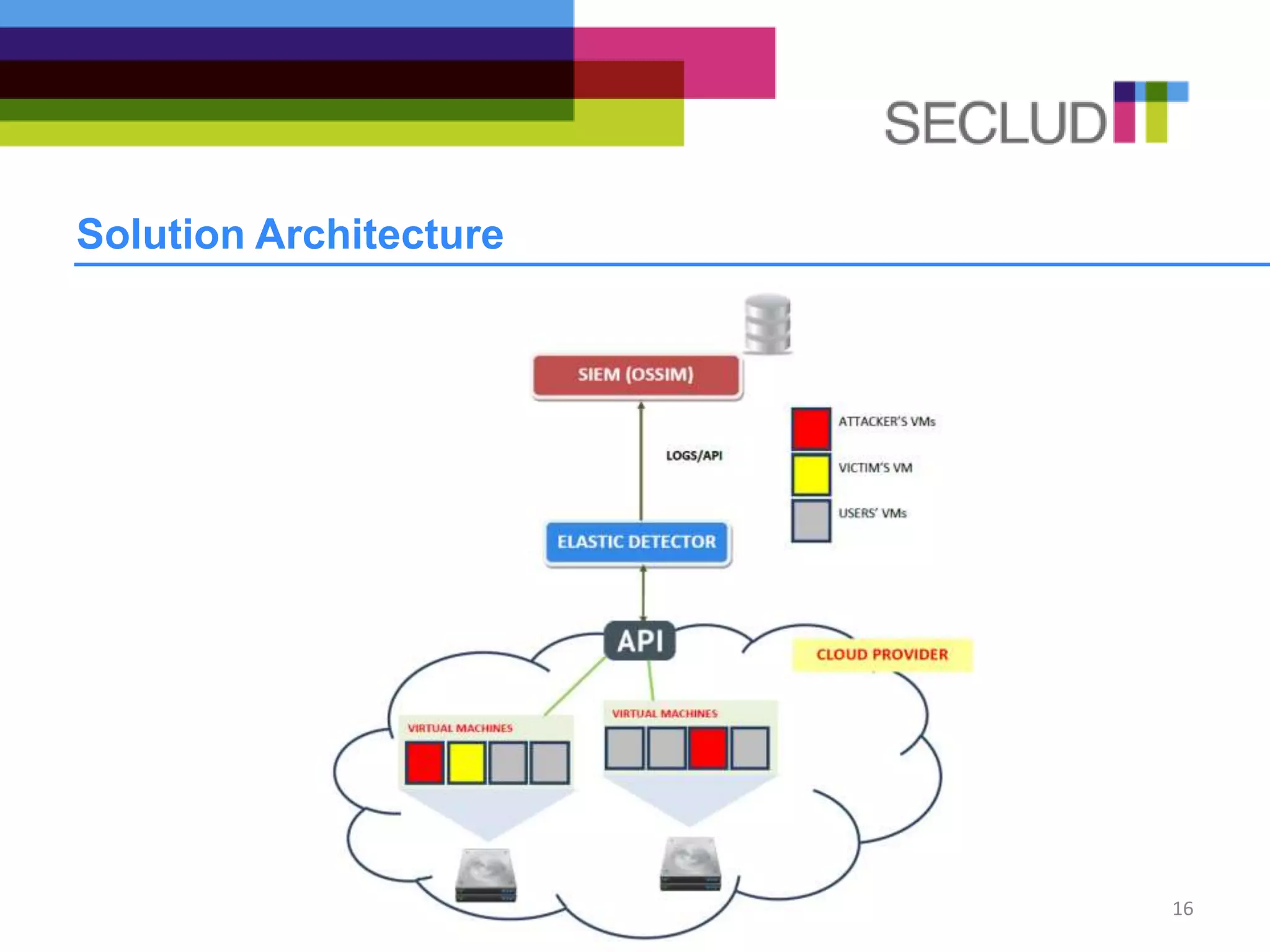
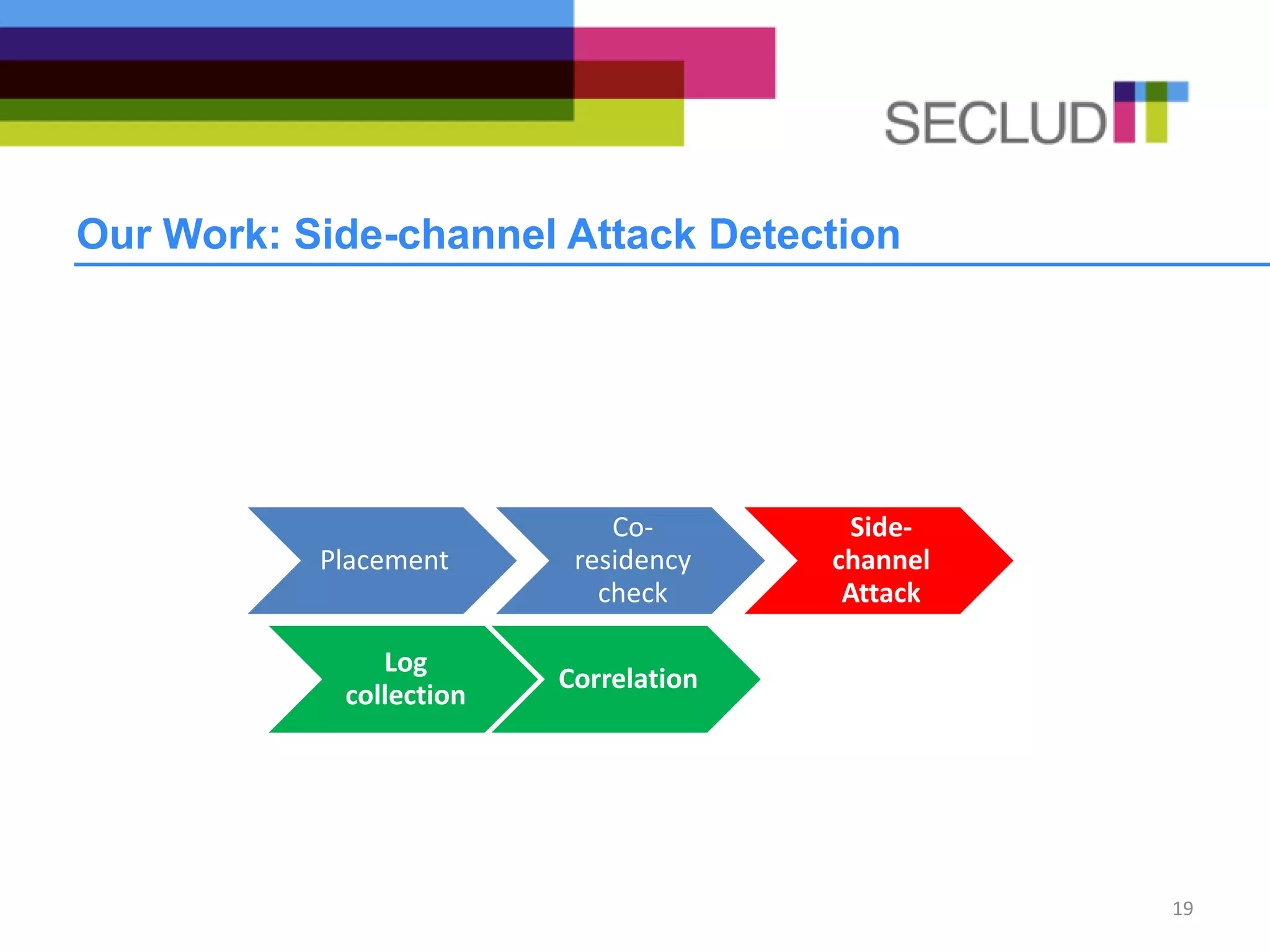
The document discusses the use of elastic SIEM for detecting side-channel attacks in cloud infrastructures, emphasizing the challenges posed by multi-tenancy in IaaS environments. It presents a solution combining co-residency checks and log analysis to enhance security and prevent information leakage from shared physical components. Additionally, it outlines the integration of its detection system with the OSSIM tool to monitor and correlate events effectively.
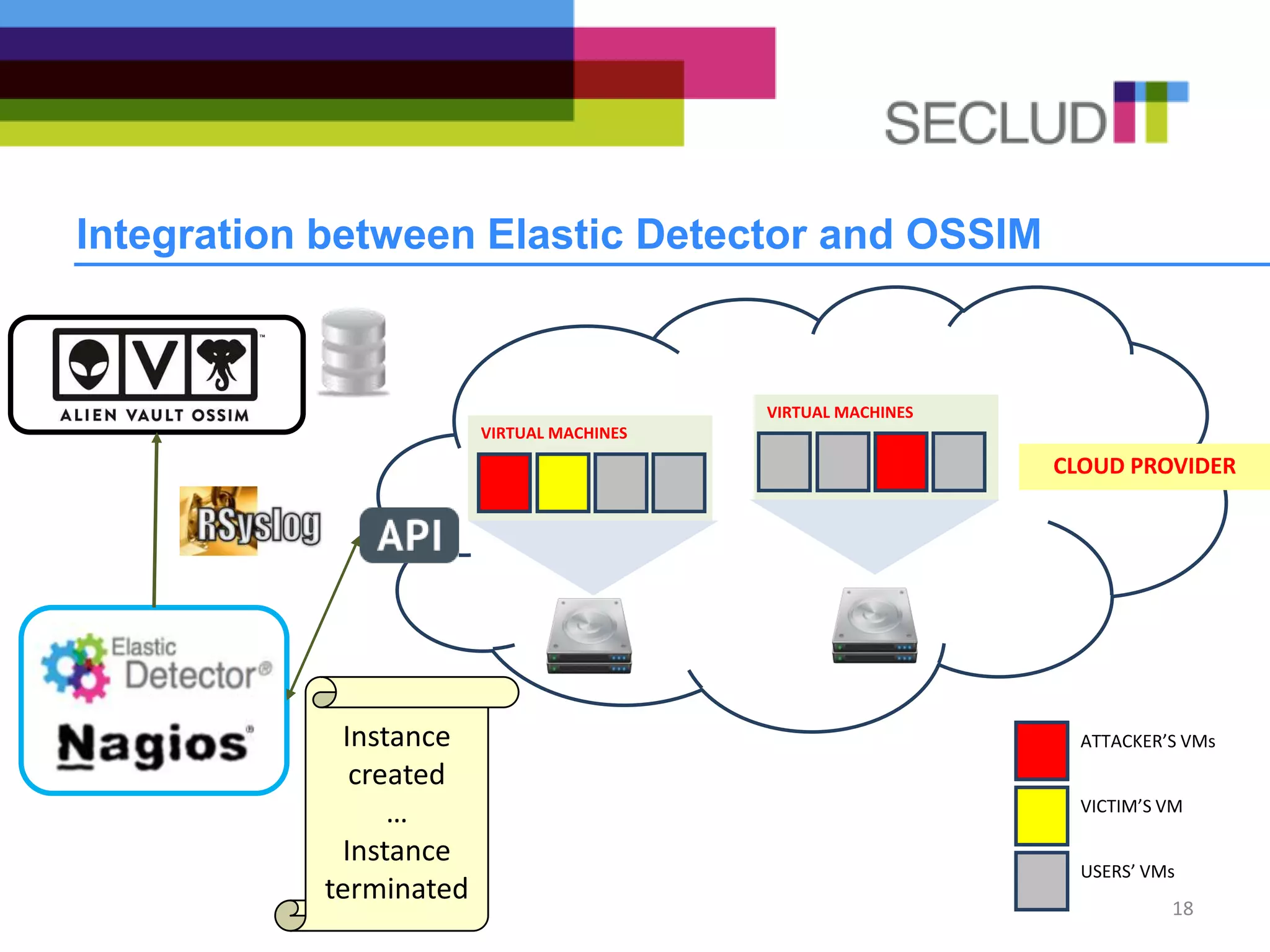
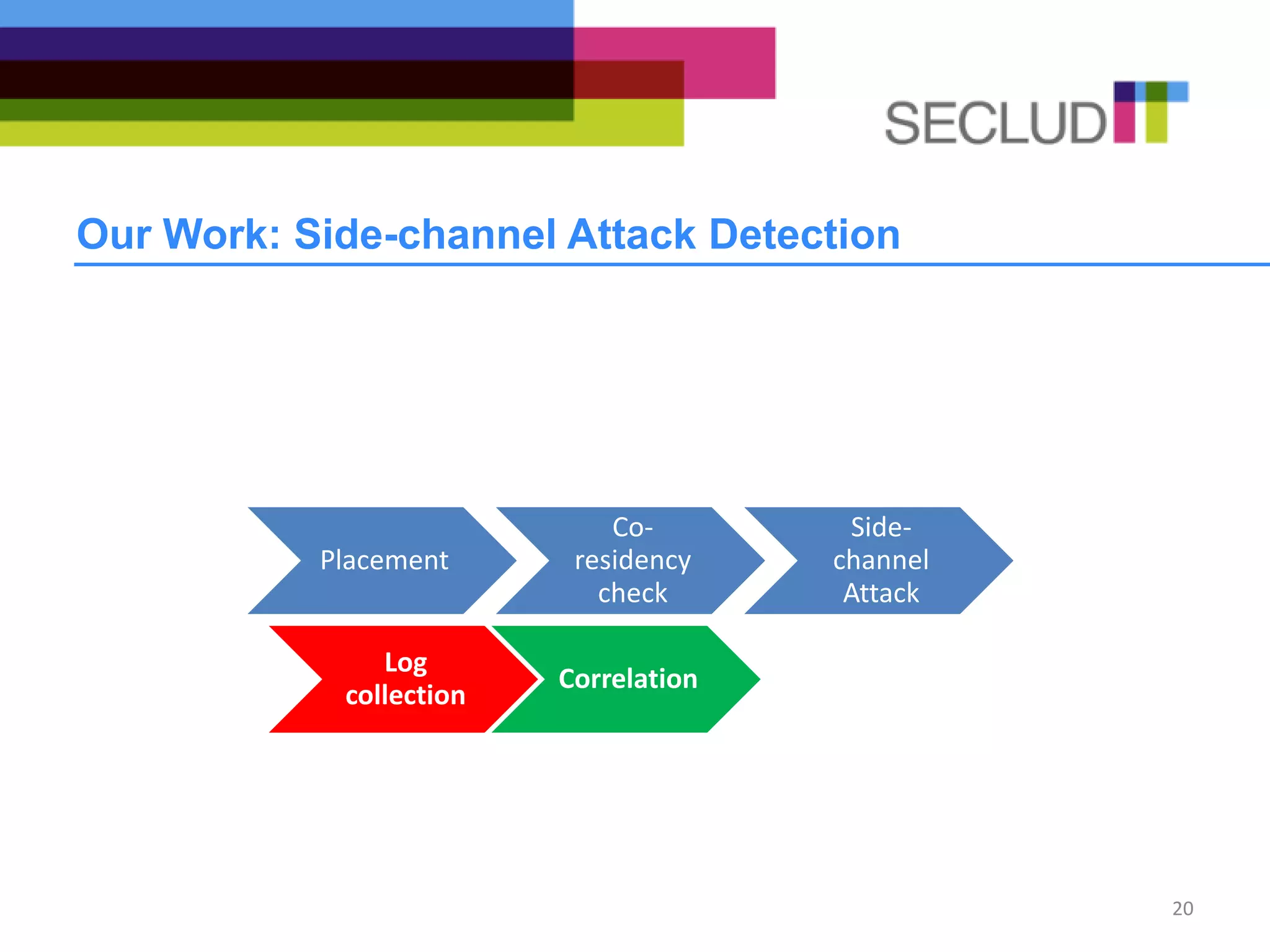
![Our Work: Plugin for Parsing Remote Logs
• Nagios logs forwarded to OSSIM need to be parsed and converted
to events
• Logs are filtered by defining a regular expression for each event
LOG:
Aug 19 15:51:32 debian-secludit nagios3: SERVICE NOTIFICATION:
event@551;72-us-east-1;722;notify-service-by-cloutomate;Found new
Instance: i-f0ad689c
REGULAR EXPRESSION:
^(?P<date>w{3}sd{1,2}sdd:dd:dd)sdebian-
secluditsnagios3:sSERVICEsNOTIFICATION:sevent@d{3};(?P<account>d
{2,3})-(?P<region>w{2}-w{4,9}-d);d{3};notify-service-by-
cloutomate;FoundsnewsInstance:s(?P<instanceid>i-[a-z,0-9]{8})$
21
Account
Region
Instance id](https://image.slidesharecdn.com/ares2013-ossim-130910100129-phpapp01/75/How-to-detect-side-channel-attacks-in-cloud-infrastructures-21-2048.jpg)