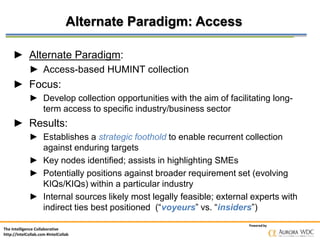
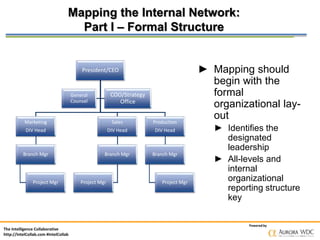
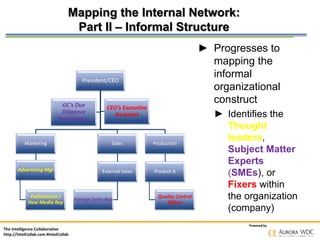
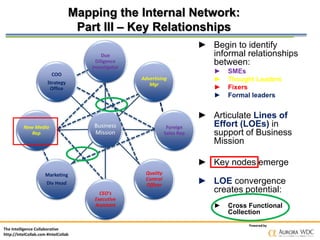
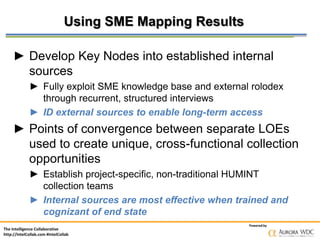
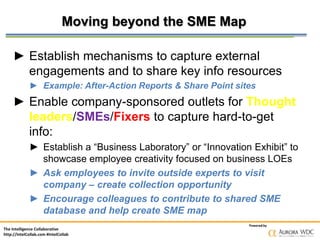
The document discusses how companies can develop internal human intelligence (HUMINT) networks to gather external information from primary sources. It recommends that companies map their internal subject matter experts and key relationships to identify information collection opportunities. Companies should establish structured interview processes with willing internal sources and identify external sources to facilitate long-term access to information. The goal is to efficiently employ HUMINT collection methods like passive, research-enabled, and targeted approaches to address business information needs.
![The Intelligence Collaborative
http://IntelCollab.com #IntelCollab
Powered by
Effective & Efficient Employment
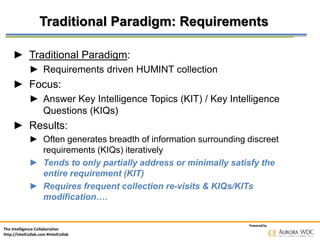
► Effective employment of HUMNT means:
► A HUMINT capability that is both arrayed against external
entities and aligned with internal entities
► Remember Sun Tzu’s dictum: “Thus it is said if you know
them and know yourself, your victory will not be
imperiled.” [The Complete Art of War, translated by Ralph D. Sawyer]
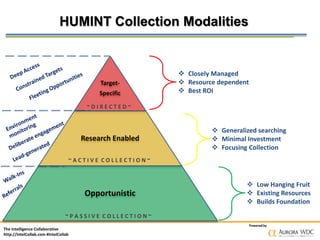
► Efficient employment of HUMINT resources:
► Using a combination of three HUMINT
collection modalities:
► Passive: Opportunistic
► Active: Research enabled
► Directed: Target-specific](https://image.slidesharecdn.com/20140430intelcollab-140501090159-phpapp01/85/How-Internal-Human-Intelligence-Networks-HUMINT-Develop-External-Primary-Sources-7-320.jpg)