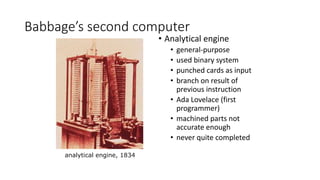
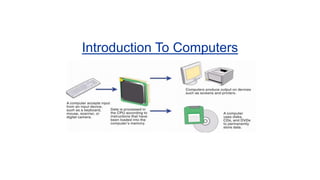
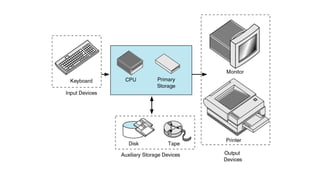
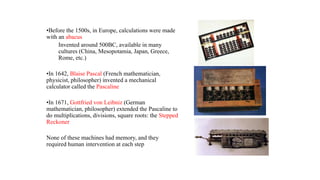
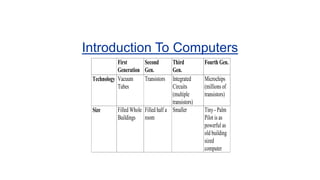
Charles Babbage invented the first mechanical computer in the early 1800s to automate complex calculations. His analytical engine design included general purpose programmability, stored programs in memory, and a branching capability. Ada Lovelace wrote algorithms for the analytical engine, making her the first computer programmer. Later computers were developed using vacuum tubes, transistors, integrated circuits and microprocessors. Computer generations progressed from mechanical to vacuum tube, transistor-based, integrated circuit-based and today's microprocessor-based computers. Hardware refers to physical components like the case, CPU, memory and I/O devices. Software includes operating systems and application programs that run on hardware.