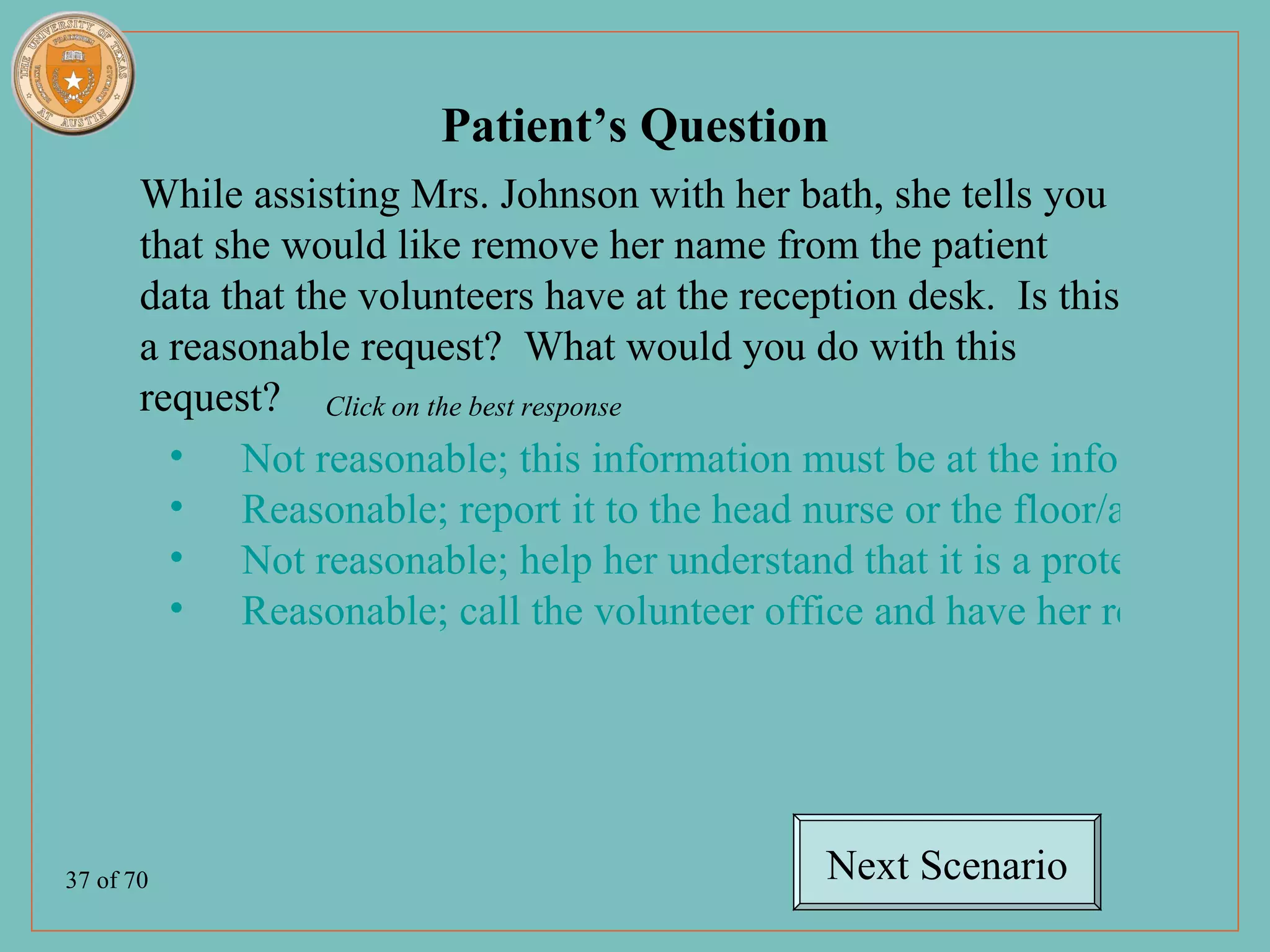
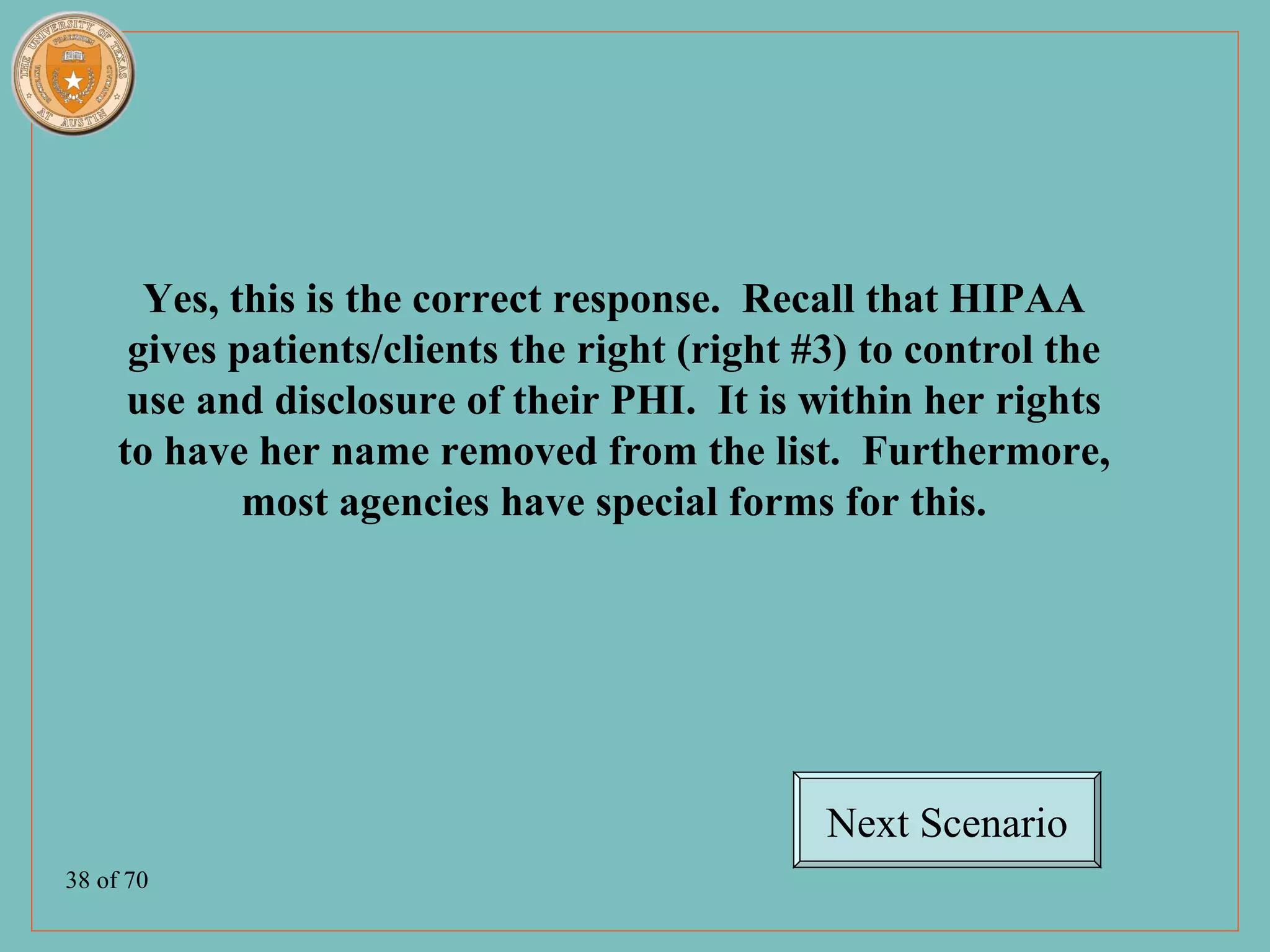
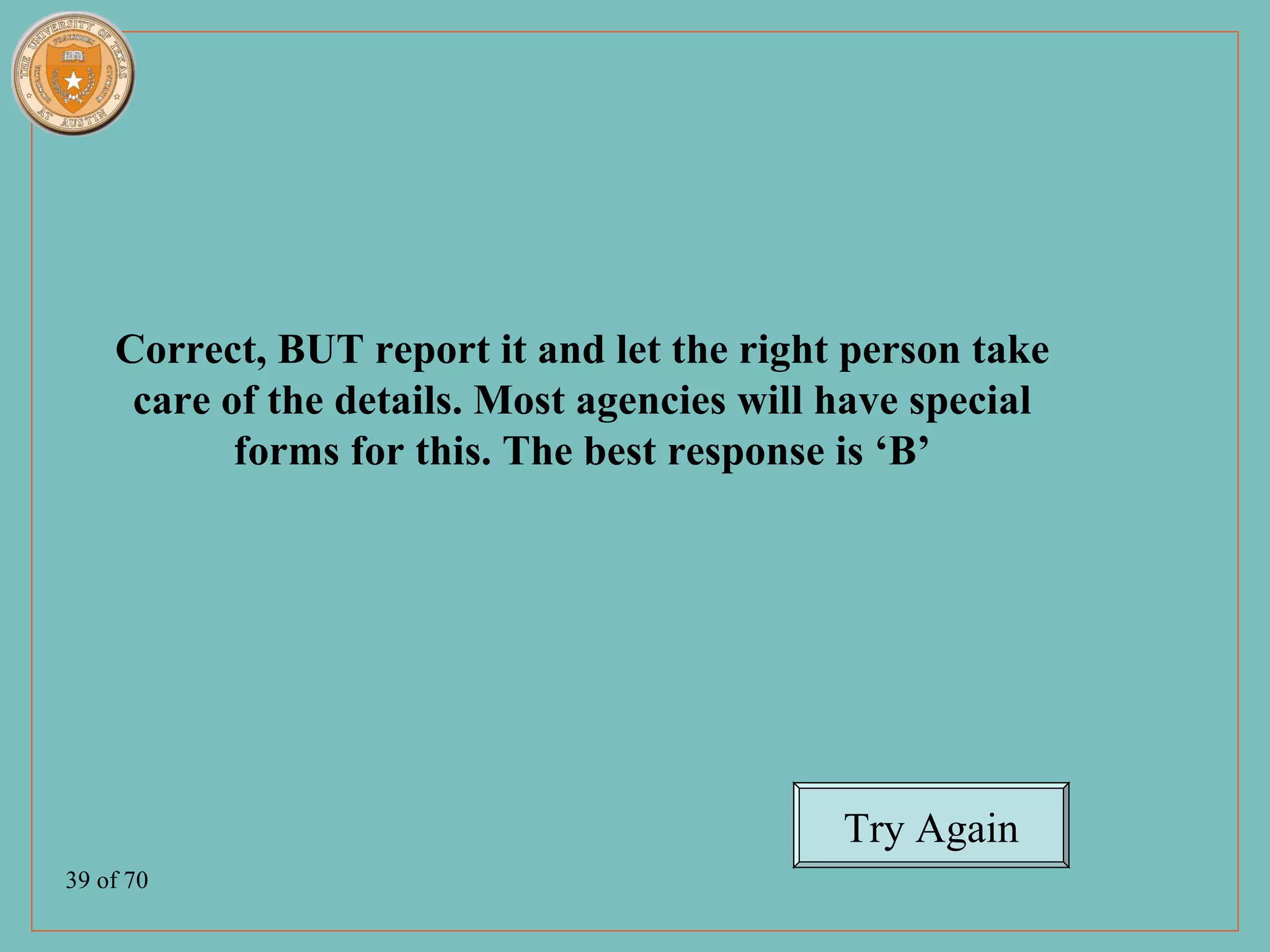
You're right, my previous response of just calling the volunteer office directly was not the best approach. The most appropriate response is to report the patient's reasonable request to have her name removed from the directory to the head nurse or facility privacy officer, as option B stated. They would be able to ensure the request is properly documented and handled according to the facility's policies and procedures. Thank you for the feedback to help improve my understanding.