HIPAA training provides an overview of the Health Insurance Portability and Accountability Act (HIPAA) and requirements for protecting patient health information. Key points include:
- HIPAA aims to standardize electronic health data exchange and protect privacy/security of patient information.
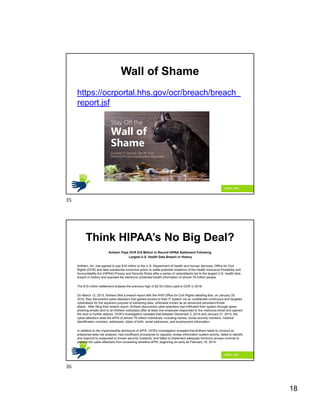
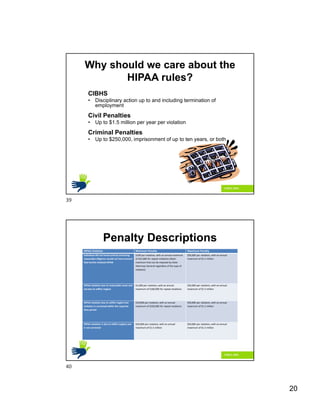
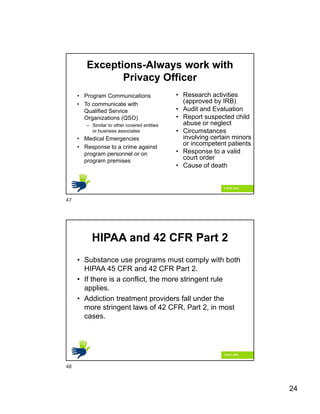
- It regulates use and disclosure of protected health information and sets penalties for violations.
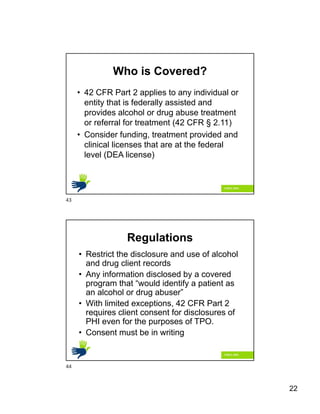
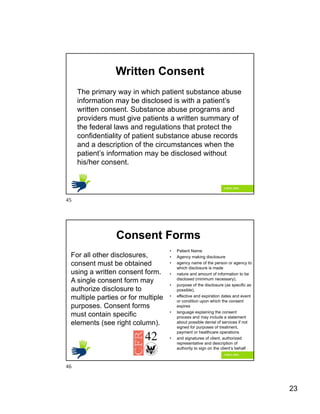
- Covered entities like health plans and providers must follow HIPAA rules regarding privacy, security, breach notification and other standards when handling patient information.
- Protected health information includes identifiable health data and must be kept confidential and secured as required by HIPAA.