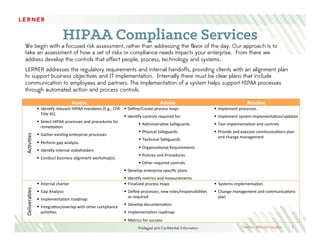
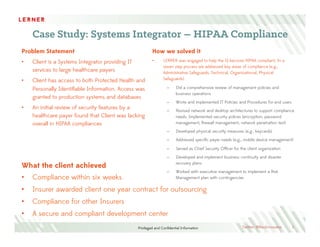
Lerner Consulting provides comprehensive HIPAA compliance services aimed at helping organizations address their security and privacy needs through proactive risk assessments and the development of tailored controls. Their process includes detailed evaluations of policies, technology, and compliance requirements, ultimately leading to improved security measures and client operations. A case study highlights successful compliance implementation for a systems integrator, resulting in a secure environment and a renewed contract with insurers.