Embed presentation
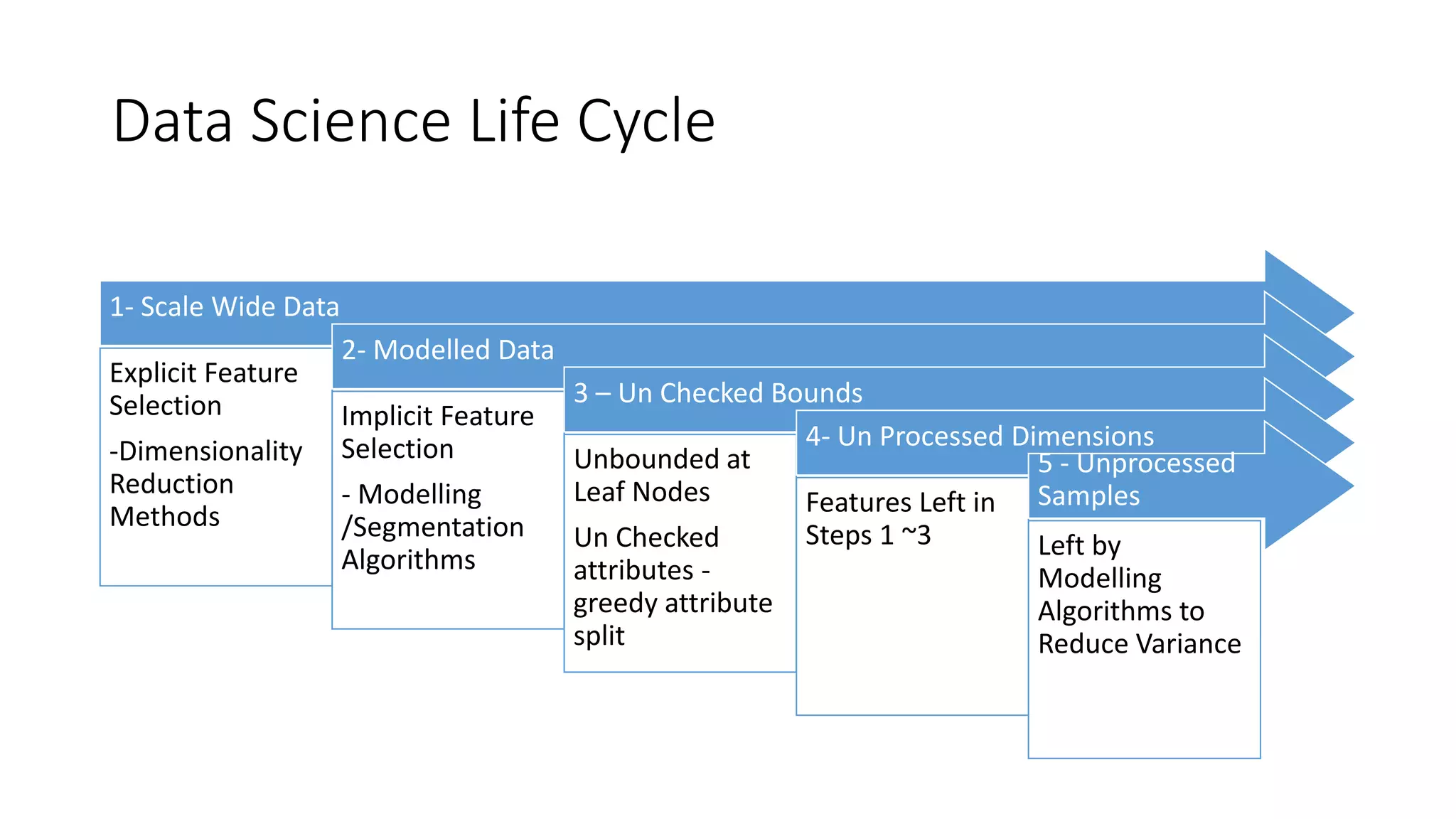
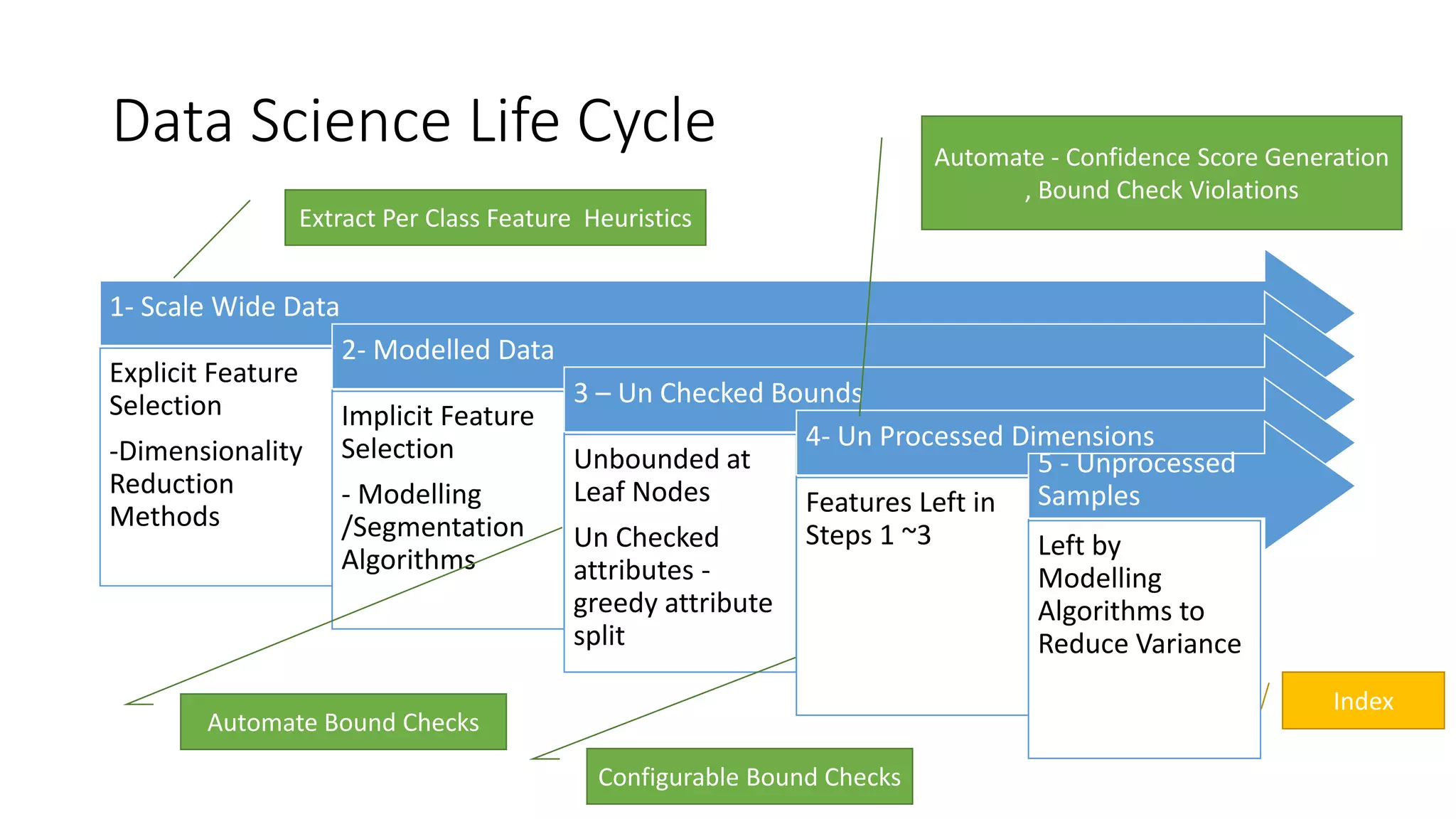
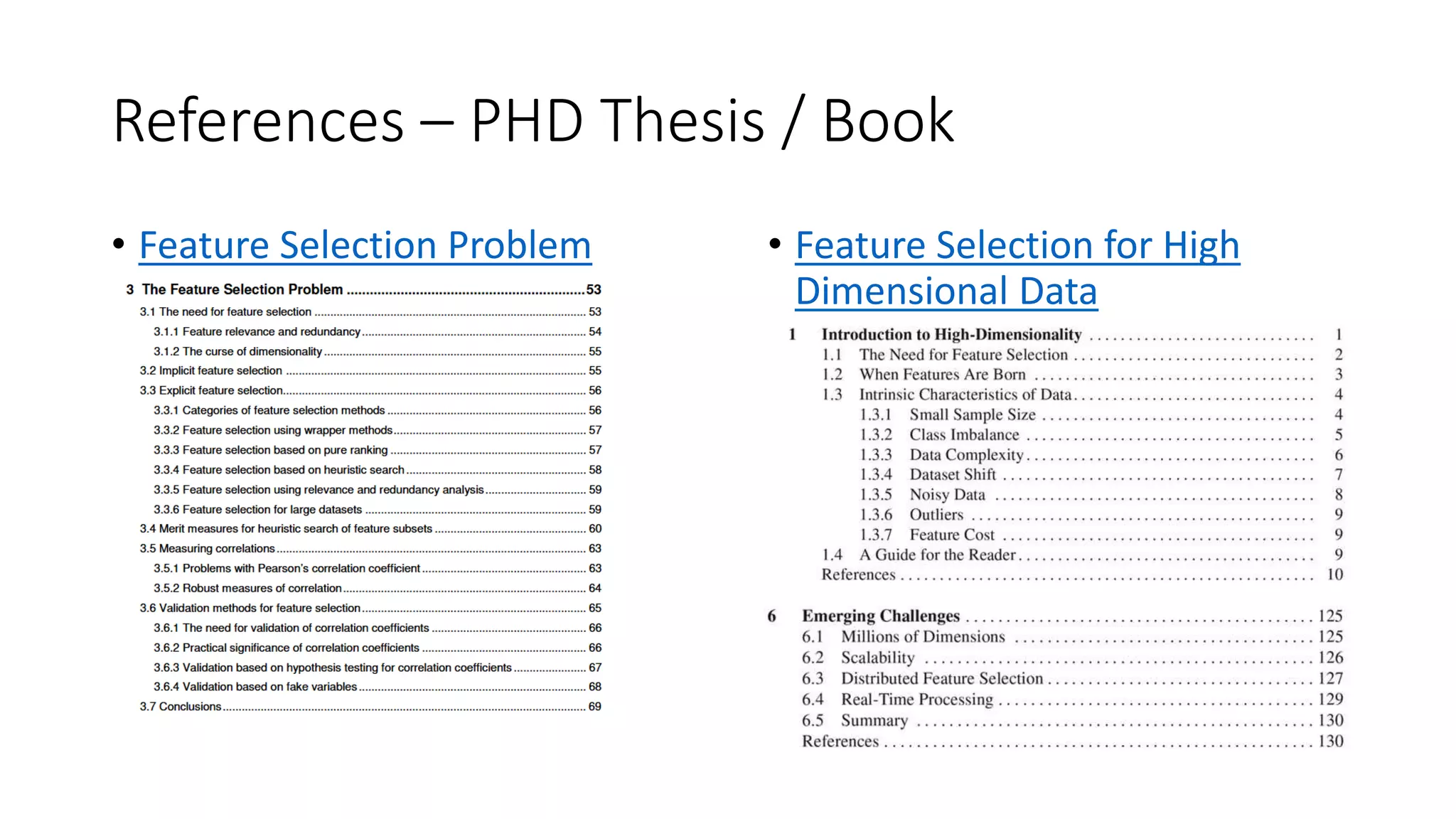
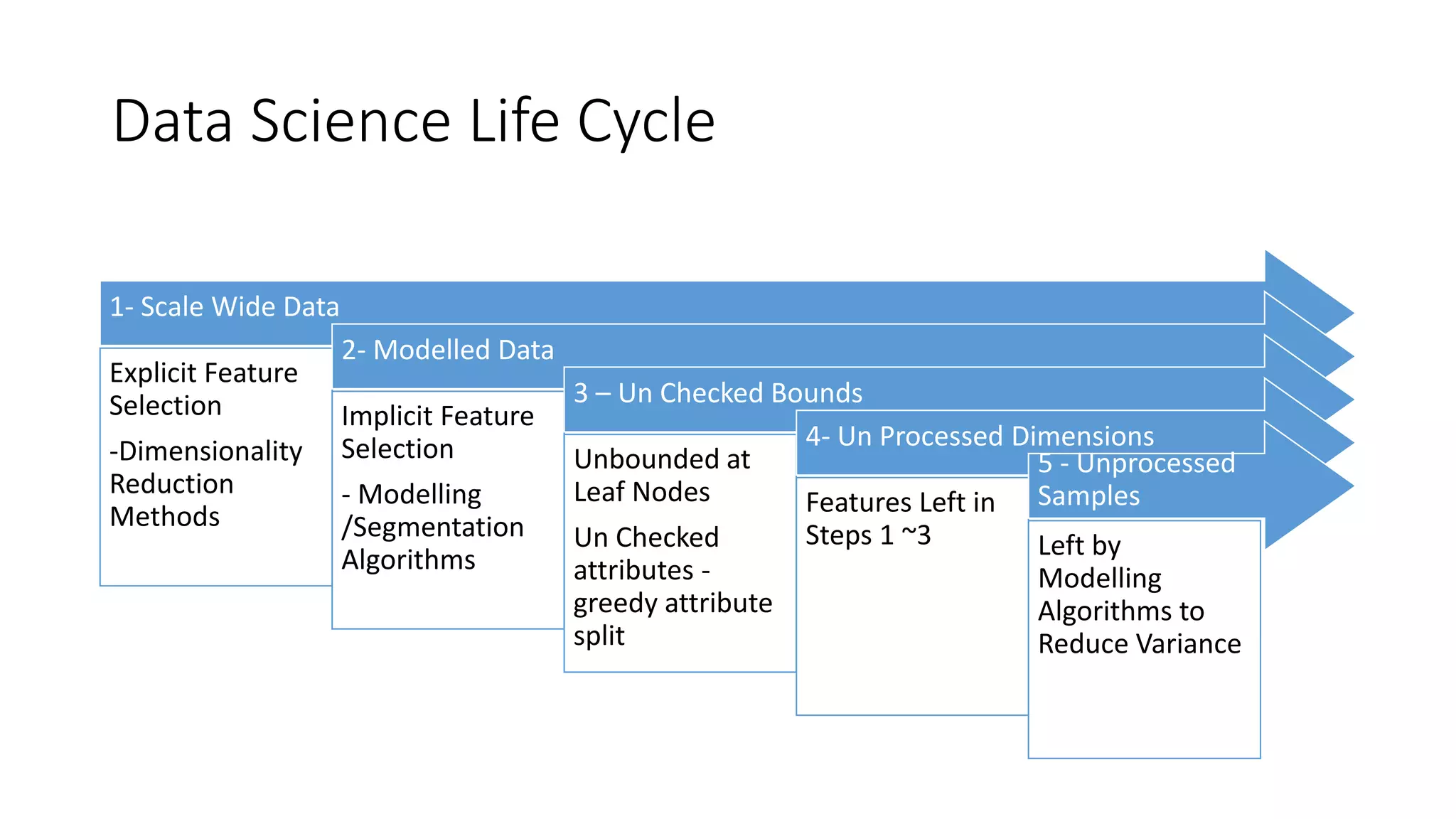
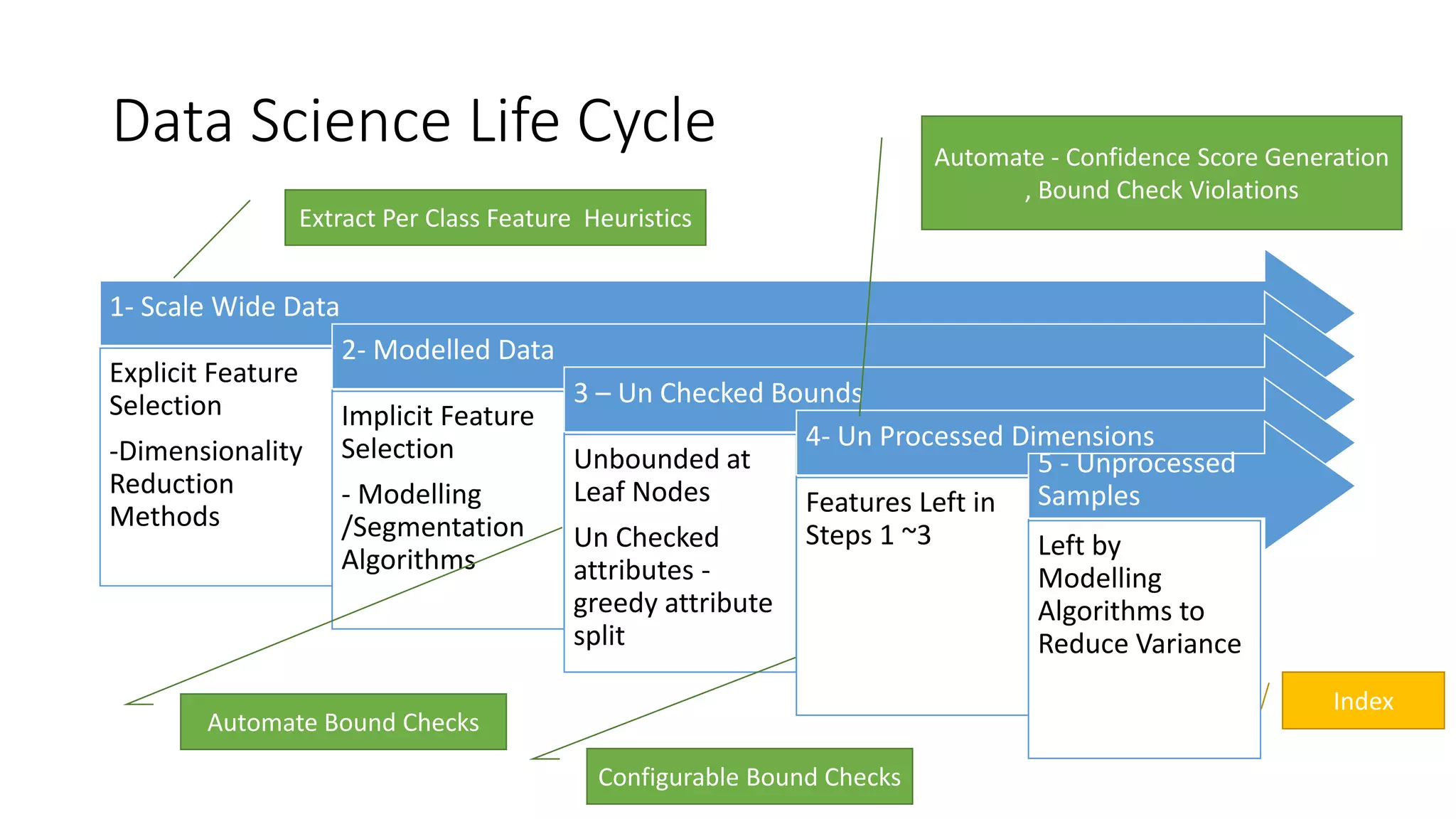
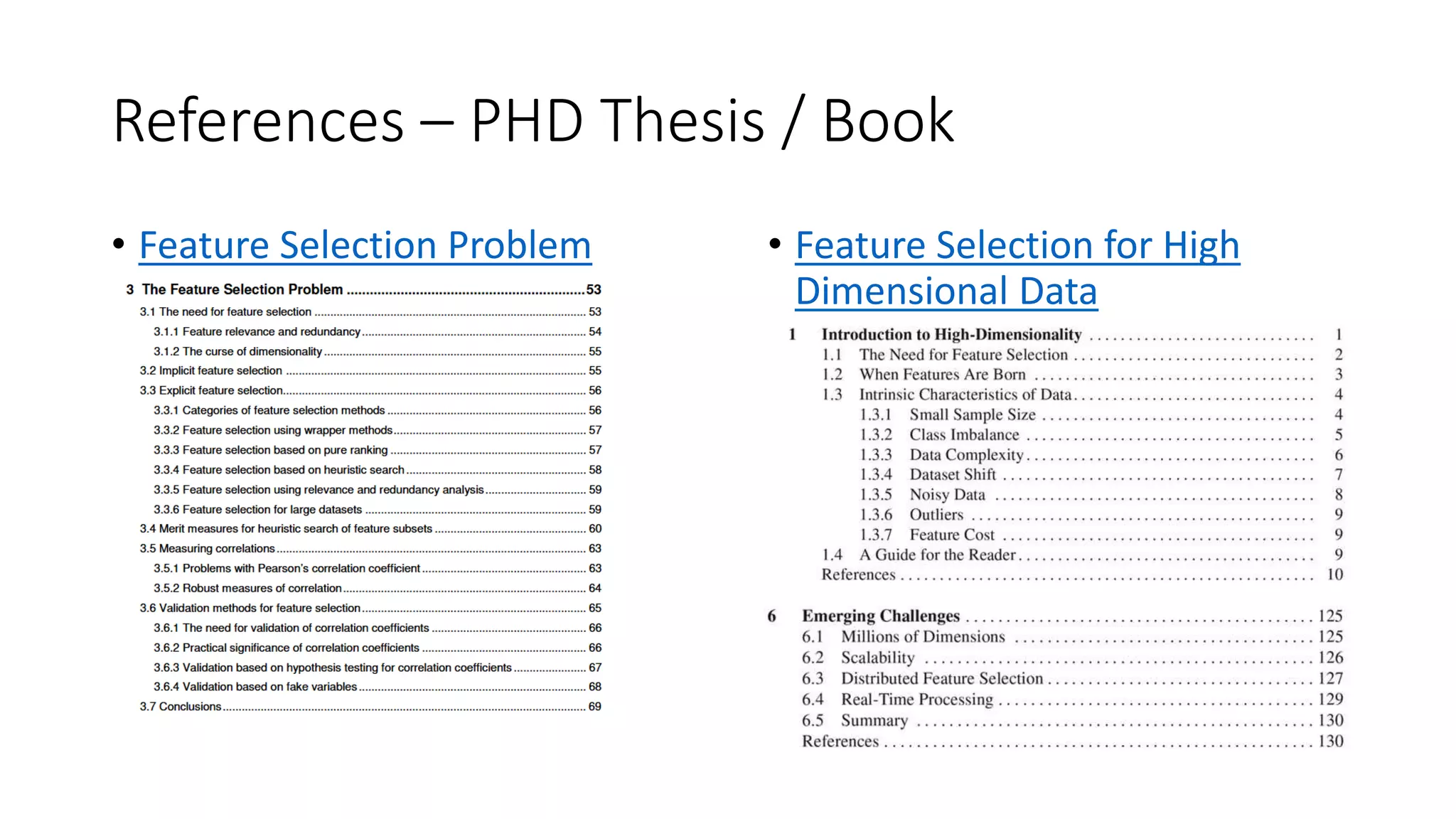
The document discusses predictive modeling in data science, focusing on explicit and implicit feature selection and the various challenges faced, such as unchecked bounds and unprocessed dimensions. It emphasizes the need for automation in bound checks and confidence score generation. Additionally, it references a PhD thesis or book related to feature selection problems in high dimensional data.