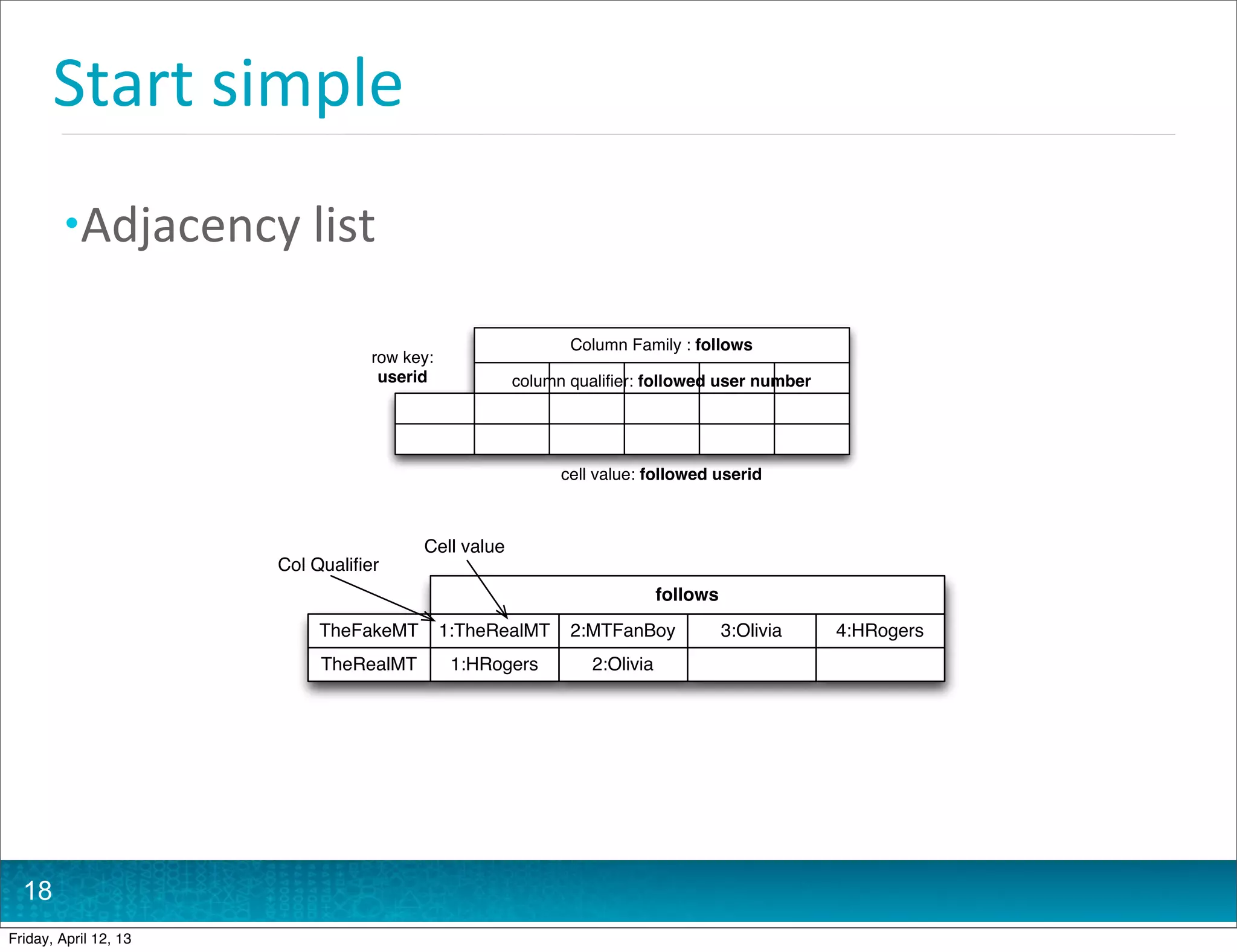
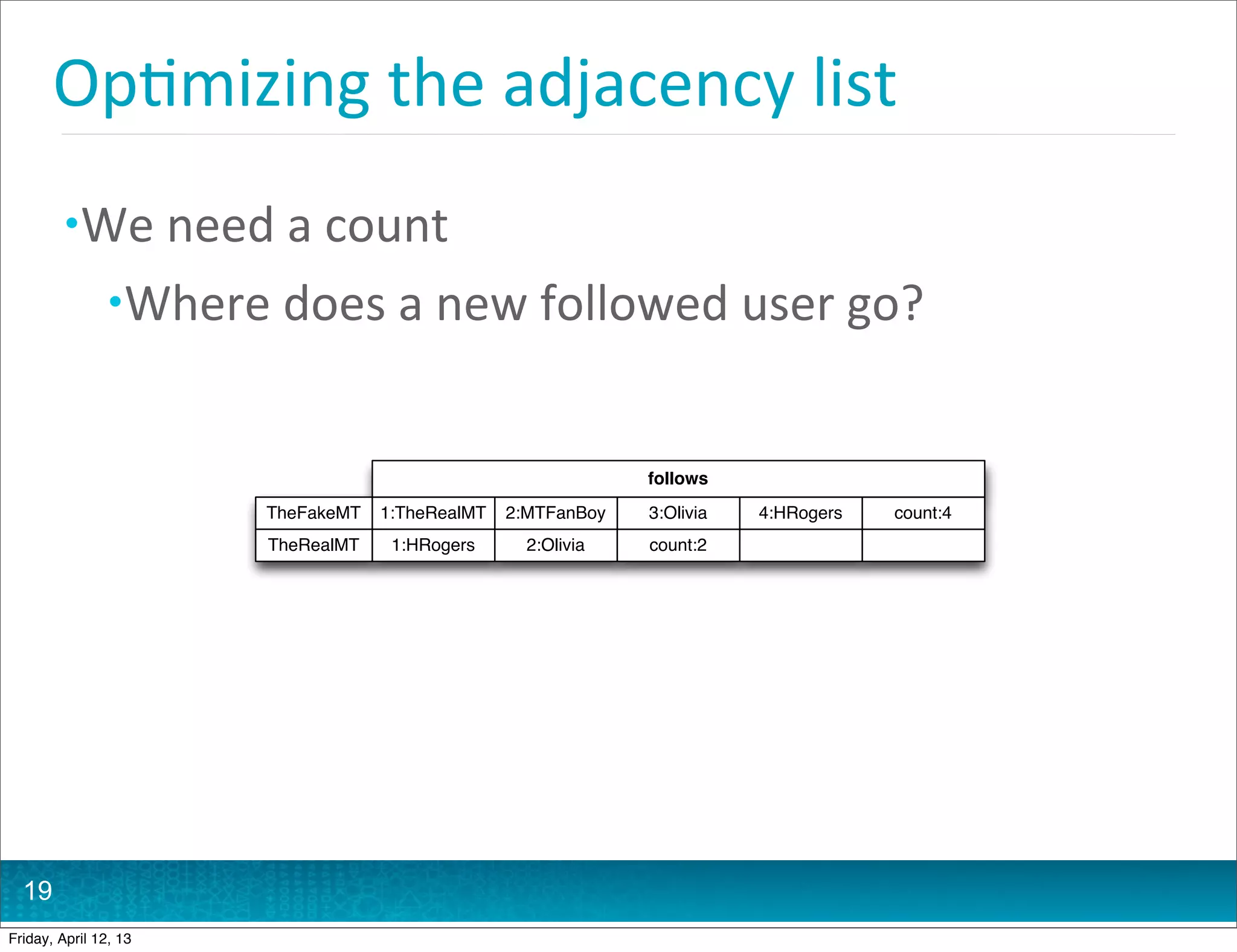
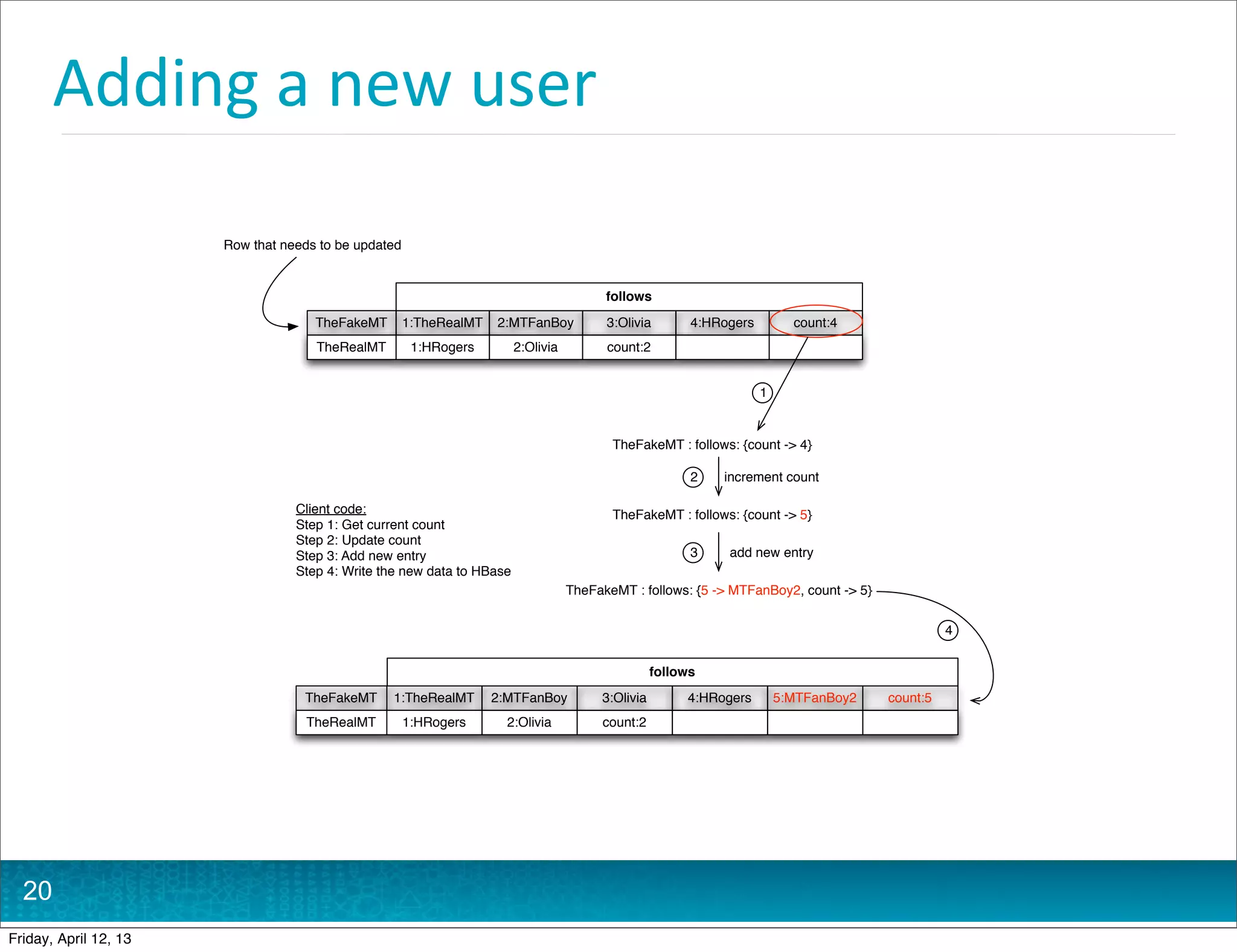
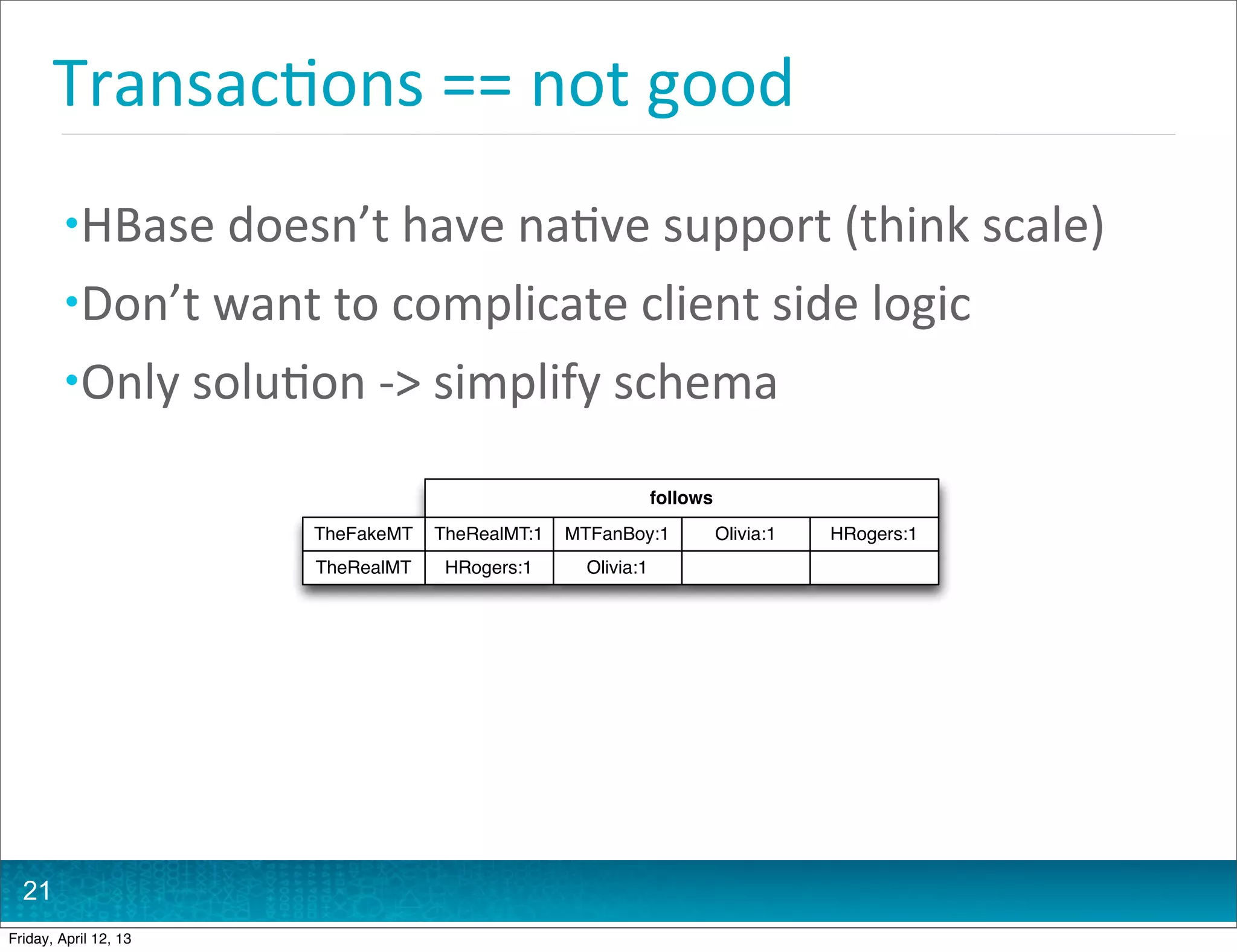
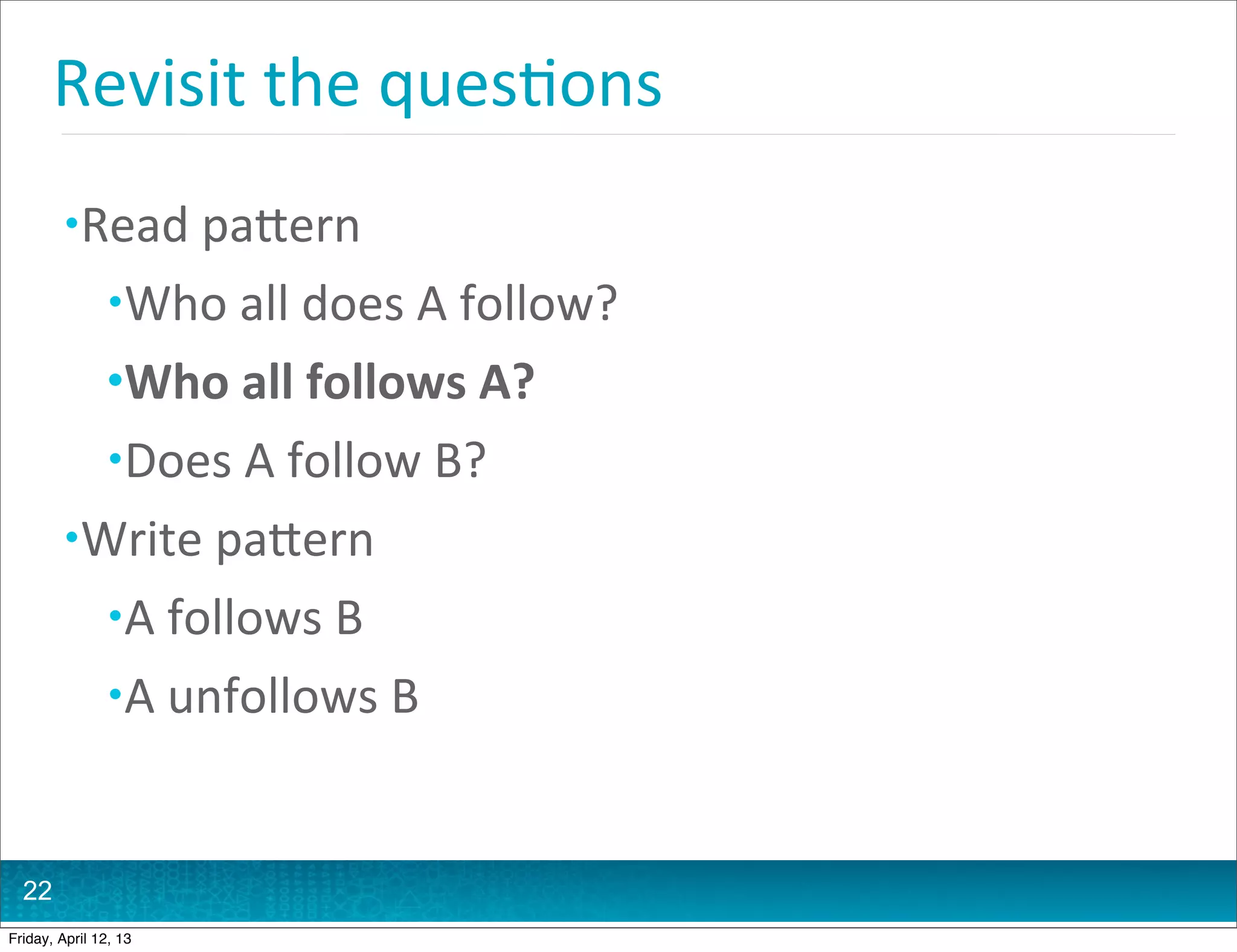
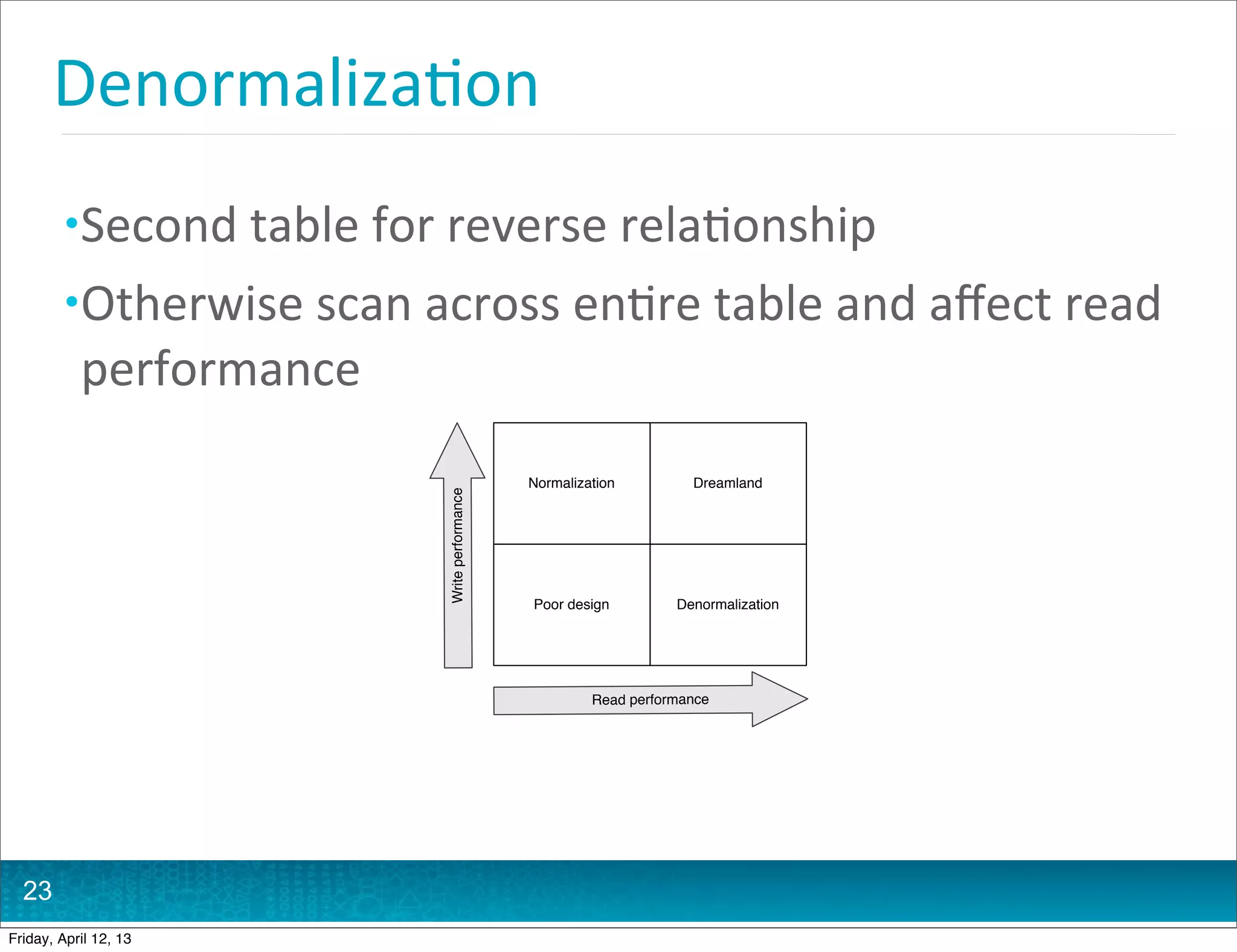
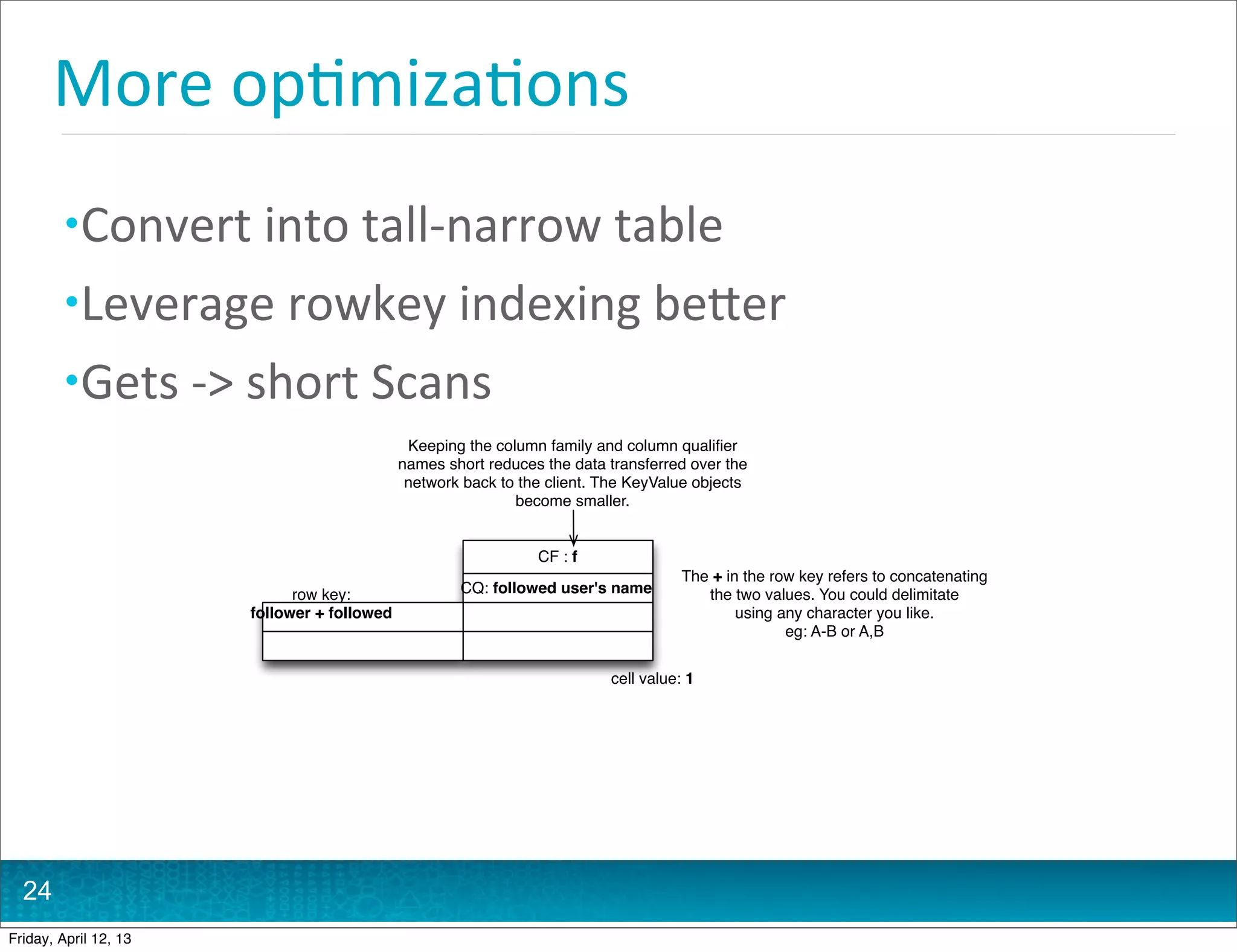
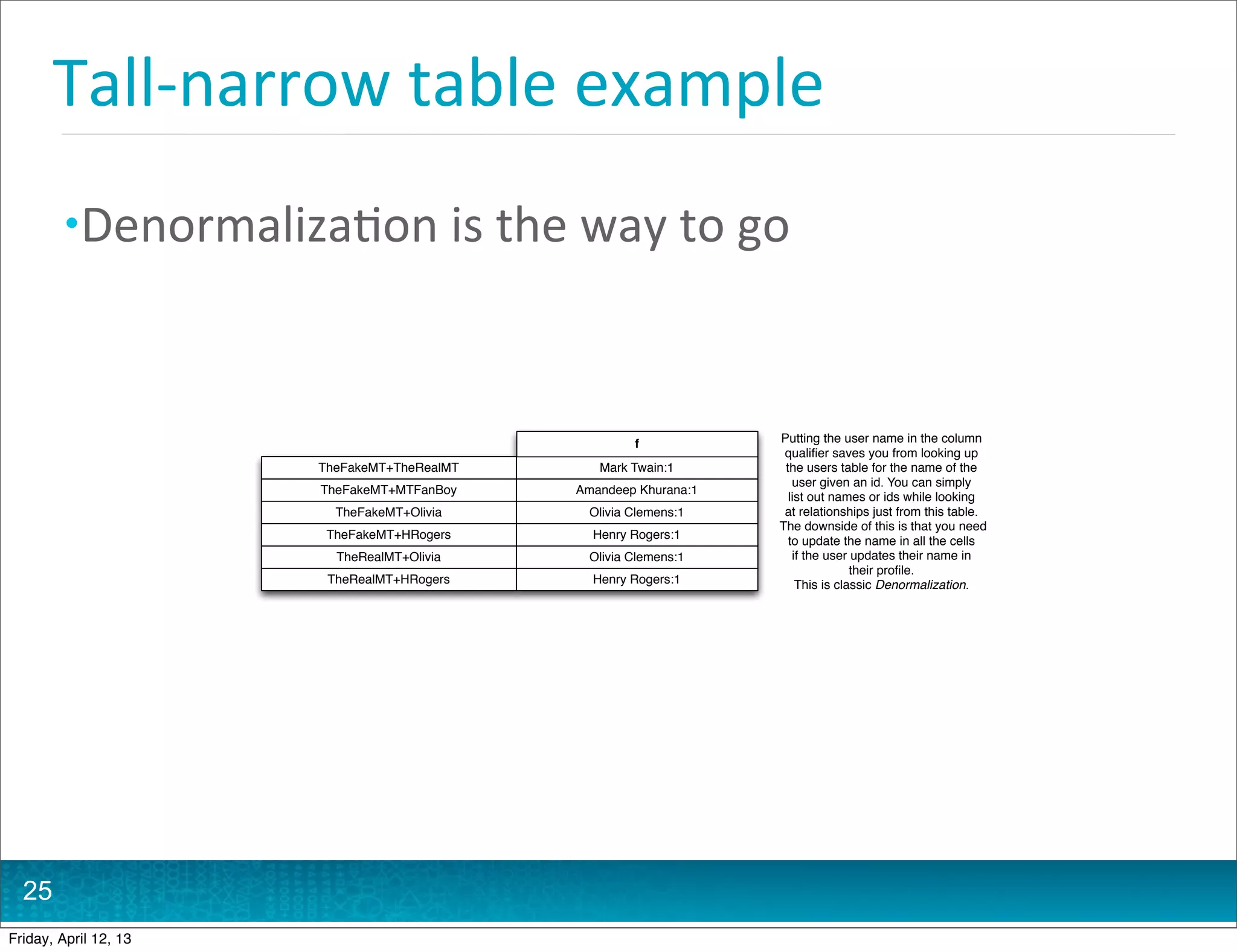
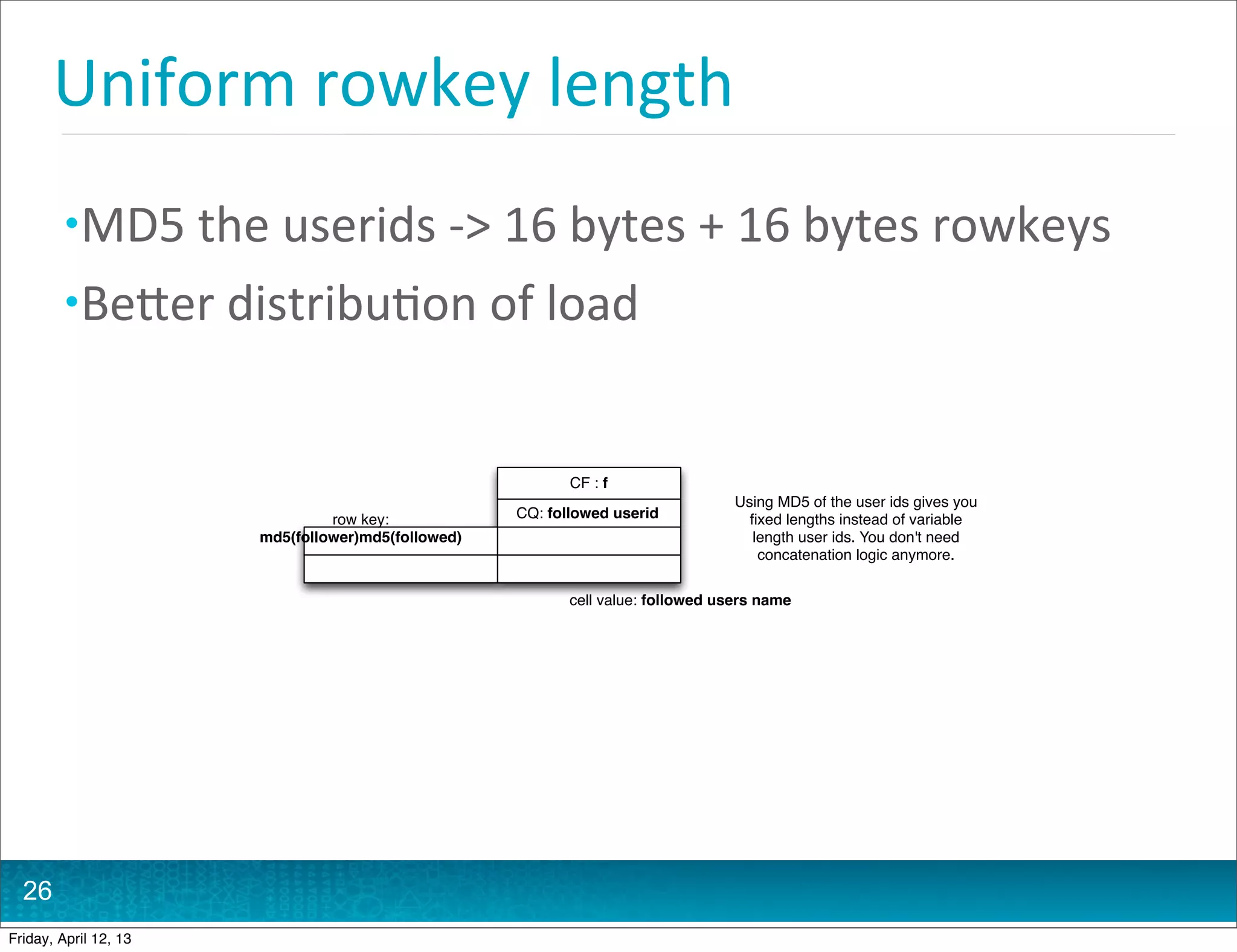
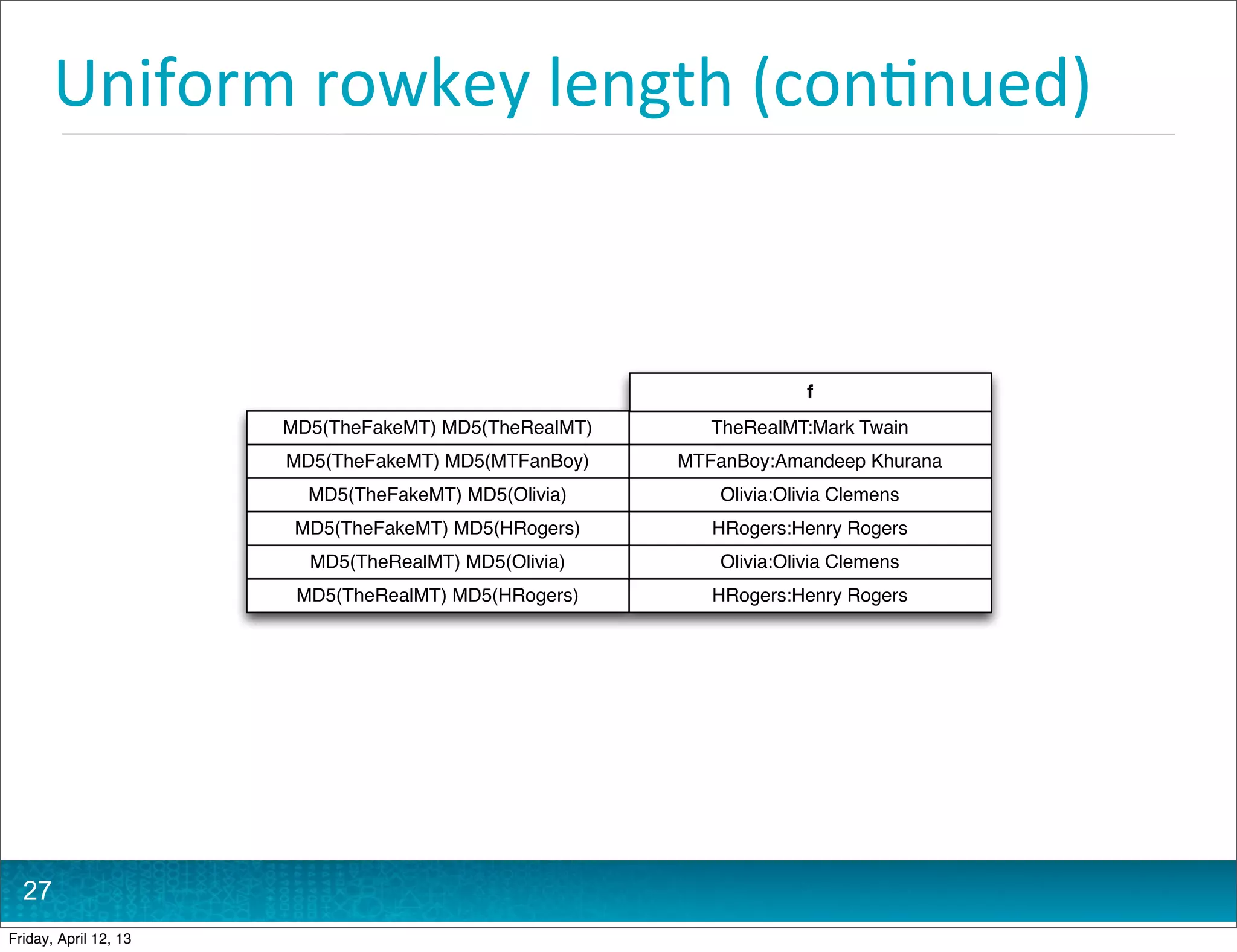
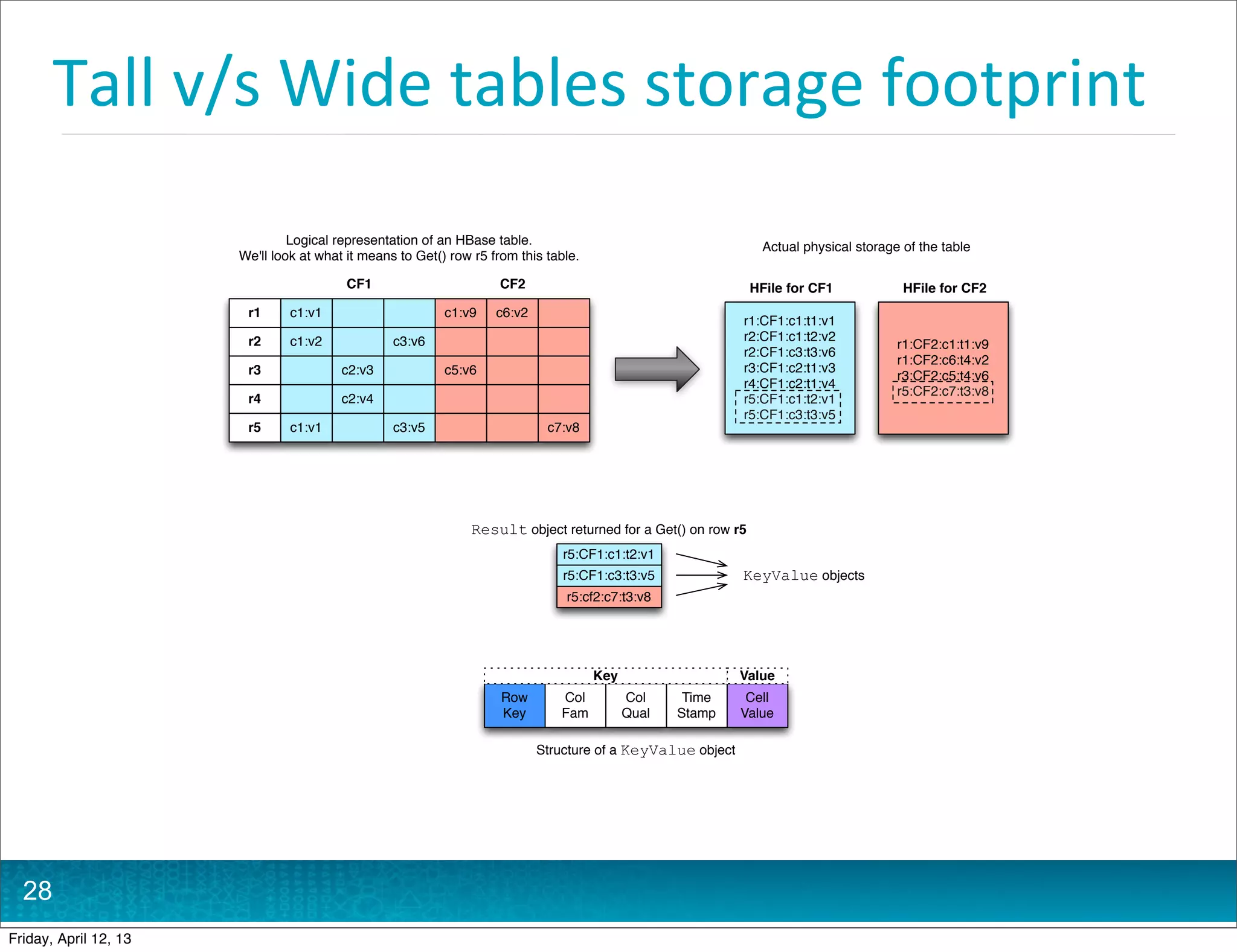
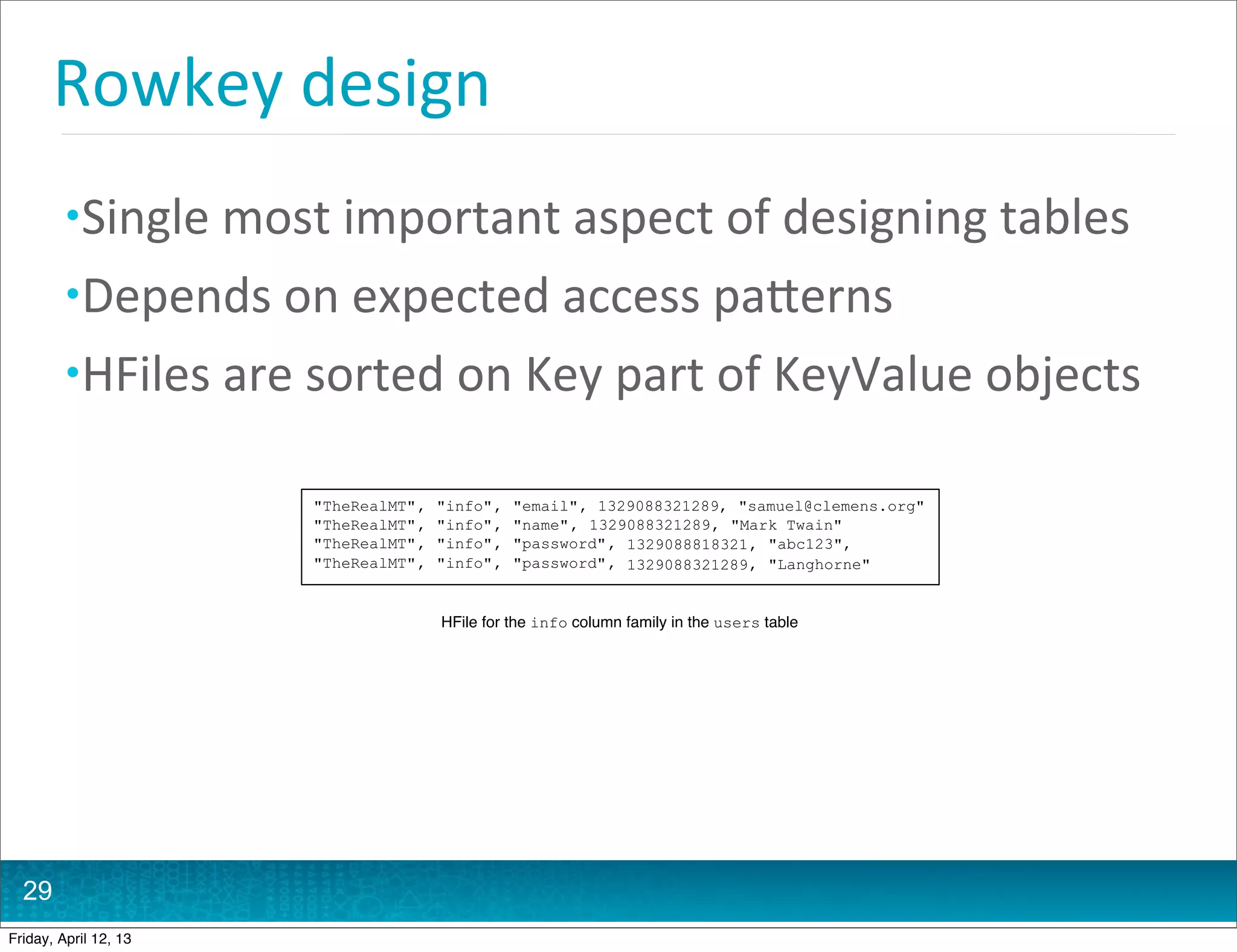
The document summarizes a presentation about HBase schema design. It discusses key aspects of HBase schema design including row keys, column families, and data modeling techniques. It provides an example of modeling user follow relationships in HBase and optimizing the schema to simplify transactions and queries.
![HBase
is
...
• Column
family
oriented
database
• Column
family
oriented
• Tables
consis@ng
of
rows
and
columns
• Persisted
Map
• Sparse
• Mul@
dimensional
• Sorted
• Indexed
by
rowkey,
column
and
@mestamp
• Key
Value
store
• [rowkey,
col
family,
col
qualifier,
@mestamp]
-‐>
cell
value
4
Friday, April 12, 13](https://image.slidesharecdn.com/hbaseschemadesignbigdatatechconboston-130412122915-phpapp01/75/HBase-schema-design-Big-Data-TechCon-Boston-4-2048.jpg)
![Data
coordinates
• Row
is
addressed
using
rowkey
• Cell
is
addressed
using
[rowkey
+
family
+
qualifier]
8
Friday, April 12, 13](https://image.slidesharecdn.com/hbaseschemadesignbigdatatechconboston-130412122915-phpapp01/75/HBase-schema-design-Big-Data-TechCon-Boston-8-2048.jpg)
![Key-‐Value
store
Keys Values
[TheRealMT, info, password, 1329088818321] abc123
[TheRealMT, info, password, 1329088321289] Langhorne
A single KeyValue instance
10
Friday, April 12, 13](https://image.slidesharecdn.com/hbaseschemadesignbigdatatechconboston-130412122915-phpapp01/75/HBase-schema-design-Big-Data-TechCon-Boston-10-2048.jpg)
![Key-‐Value
store
[TheRealMT, info, password, 1329088818321] abc123
1 Start with coordinates of full precision
{
1329088818321 : "abc123",
[TheRealMT, info, password]
1329088321289 : "Langhorne"
}
2 Drop version and you're left with a map of version to values
Keys {
"email" : {
1329088321289 : "samuel@clemens.org"
},
"name" : {
[TheRealMT, info] 1329088321289 : "Mark Twain"
},
Values
"password" : {
1329088818321 : "abc123",
1329088321289 : "Langhorne"
}
}
3 Omit qualifier and you have a map of qualifiers to the previous maps
{
"info" : {
"email" : {
1329088321289 : "samuel@clemens.org"
},
"name" : {
1329088321289 : "Mark Twain"
[TheRealMT]
},
"password" : {
1329088818321 : "abc123",
1329088321289 : "Langhorne"
}
}
}
4 Finally, drop the column family and you have a row, a map of maps
11
Friday, April 12, 13](https://image.slidesharecdn.com/hbaseschemadesignbigdatatechconboston-130412122915-phpapp01/75/HBase-schema-design-Big-Data-TechCon-Boston-11-2048.jpg)
![Write
op@mized
• Distribute
writes
across
the
cluster
• Issue
most
pronounced
with
@me
series
data
• Hashing
hash("TheRealMT") -> random byte[]
• Sal@ng
int salt = new Integer(new Long(timestamp).hashCode()).shortValue()
% <number of region servers>;
byte[] rowkey = Bytes.add(Bytes.toBytes(salt) + Bytes.toBytes("|") +
Bytes.toBytes(timestamp));
30
Friday, April 12, 13](https://image.slidesharecdn.com/hbaseschemadesignbigdatatechconboston-130412122915-phpapp01/75/HBase-schema-design-Big-Data-TechCon-Boston-31-2048.jpg)