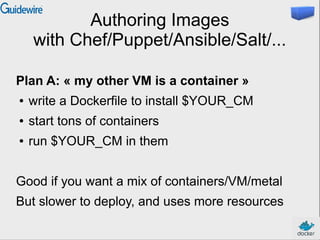
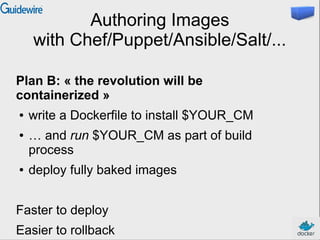
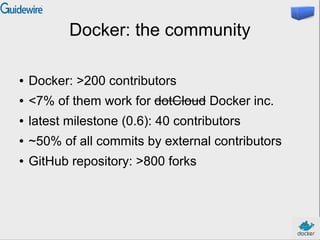
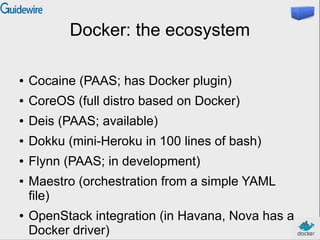
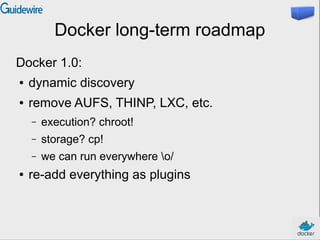
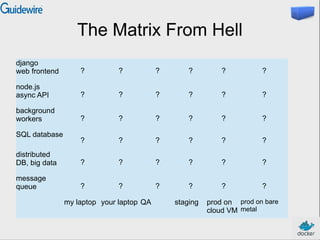
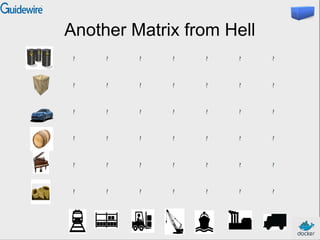
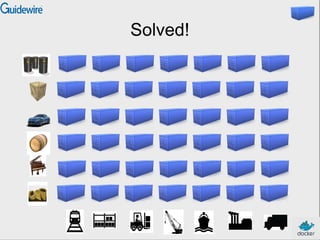
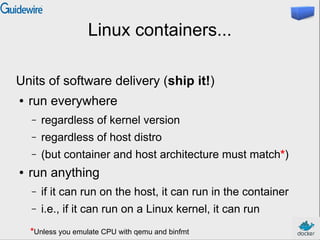
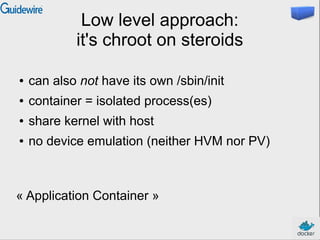
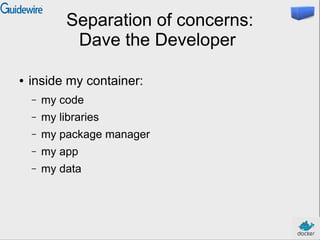
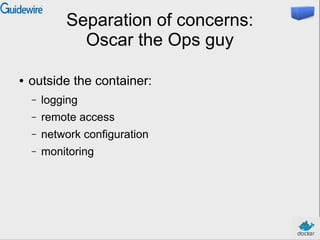
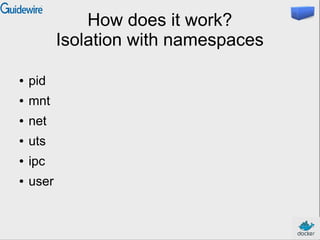
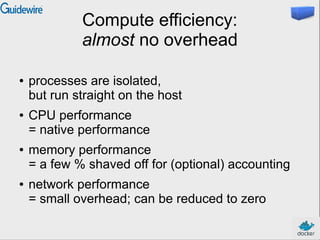
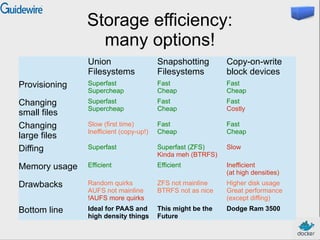
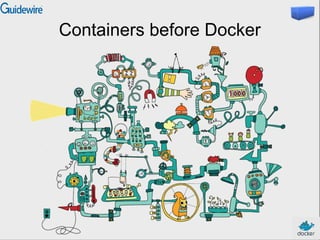
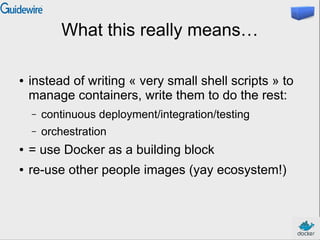
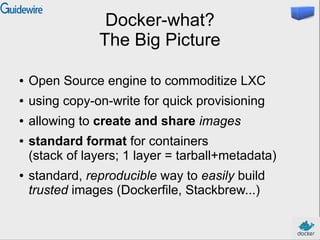
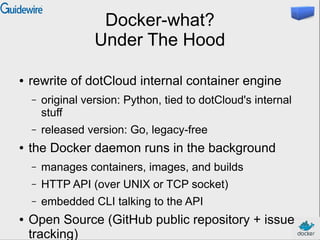
This document introduces Docker and containers. It discusses that Docker provides a way to easily deploy applications by using lightweight virtualization to isolate applications into containers. These containers can then be easily shared between systems. The document outlines what problem containers solve, provides an overview of how Docker works, and discusses how to author Docker images using Dockerfiles or by committing changes to containers. It also discusses the Docker community and ecosystem and Docker's long term roadmap to further simplify deployment of applications.


![Authoring images
with a Dockerfile
FROM ubuntu
RUN apt-get -y update
RUN apt-get install -y g++
RUN apt-get install -y erlang-dev erlang-manpages
erlang-base-hipe ...
RUN apt-get install -y libmozjs185-dev libicu-dev
libtool ...
RUN apt-get install -y make wget
RUN wget http://.../apache-couchdb-1.3.1.tar.gz | tar
-C /tmp -zxf-
RUN cd /tmp/apache-couchdb-* && ./configure && make
install
RUN printf "[httpd]nport = 8101nbind_address =
0.0.0.0" >](https://image.slidesharecdn.com/guidewire-2013-maintalk-131120112908-phpapp01-140801195254-phpapp02/85/Introduction-to-Docker-and-Containers-37-320.jpg)