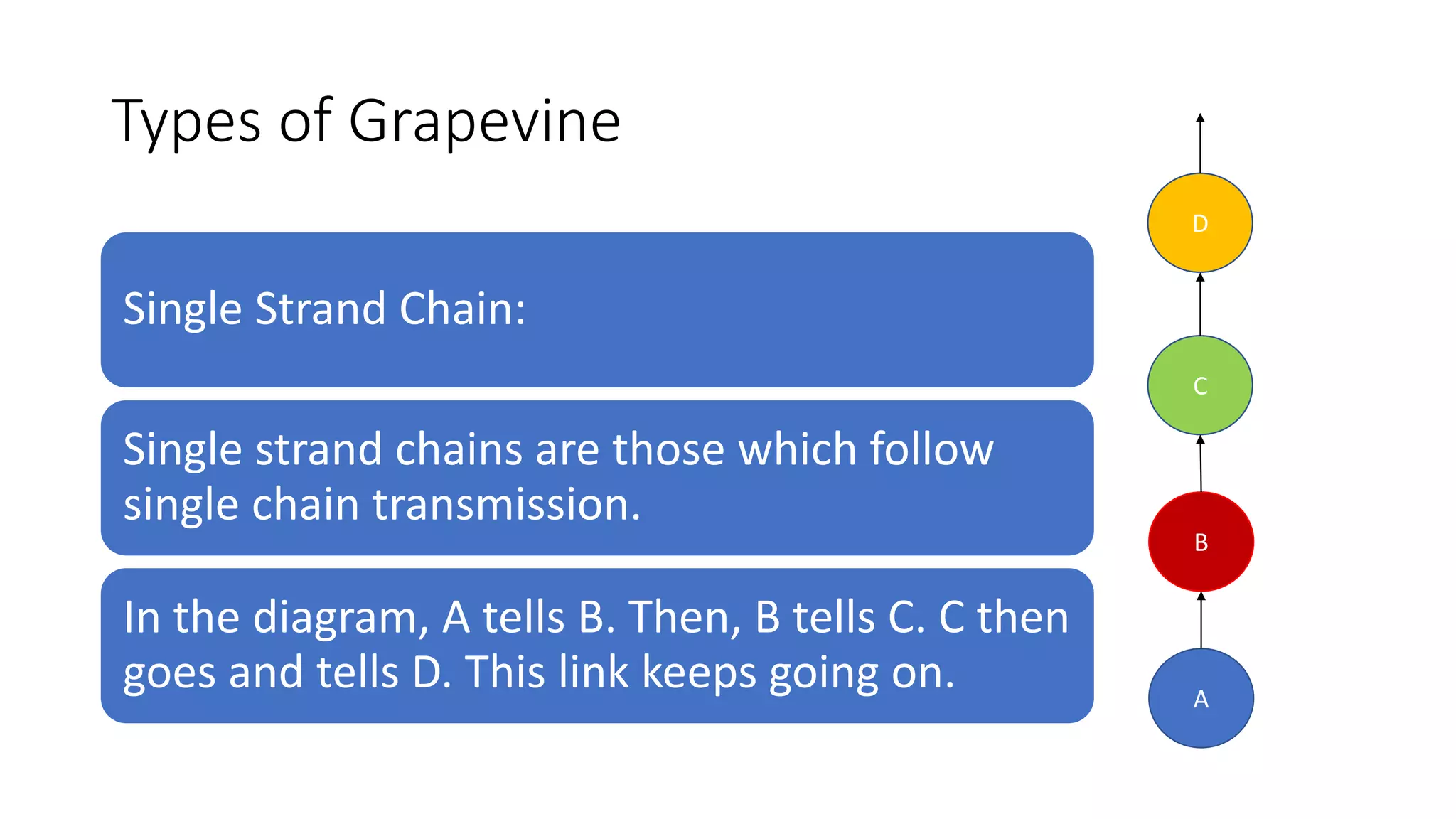
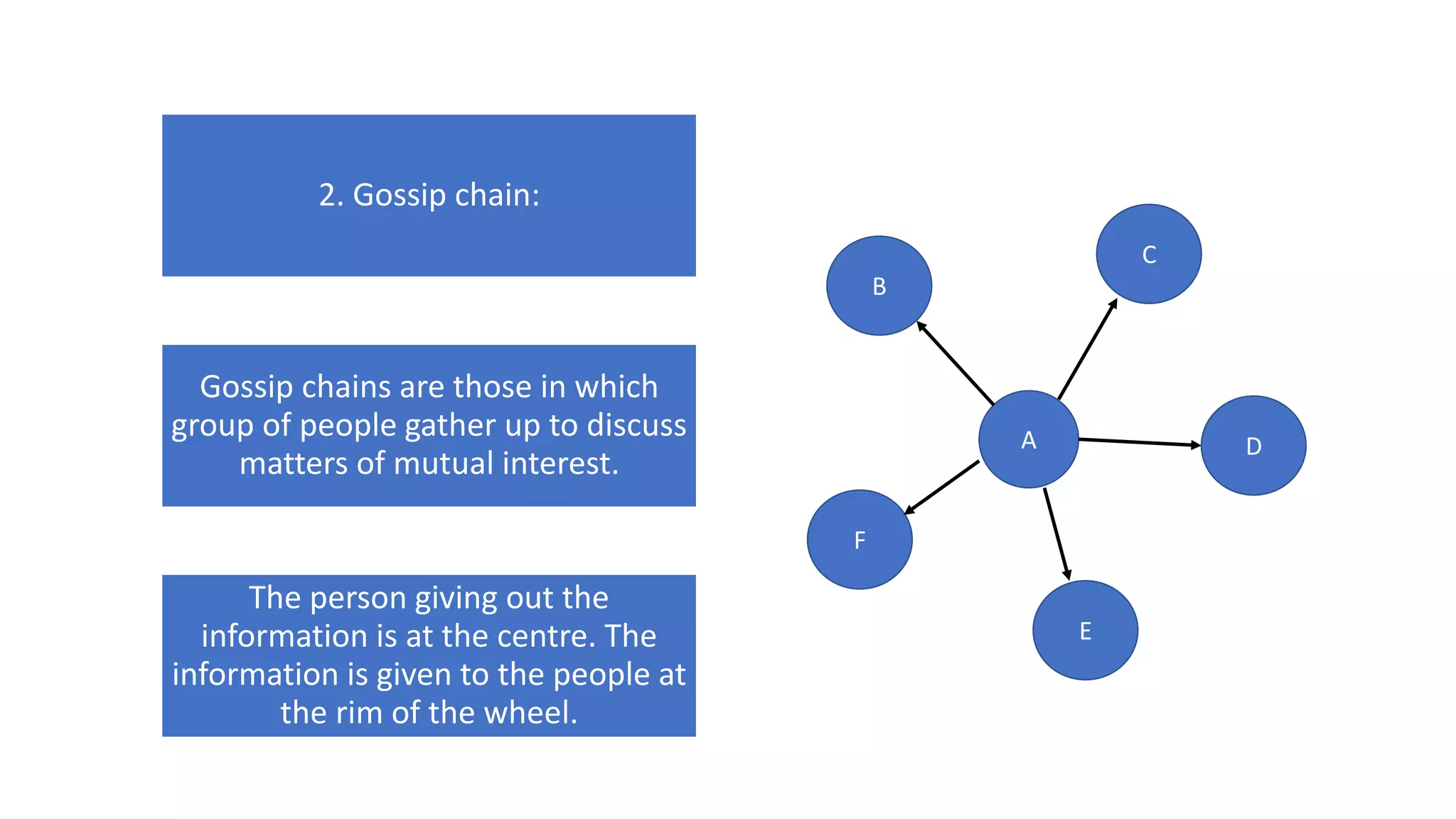
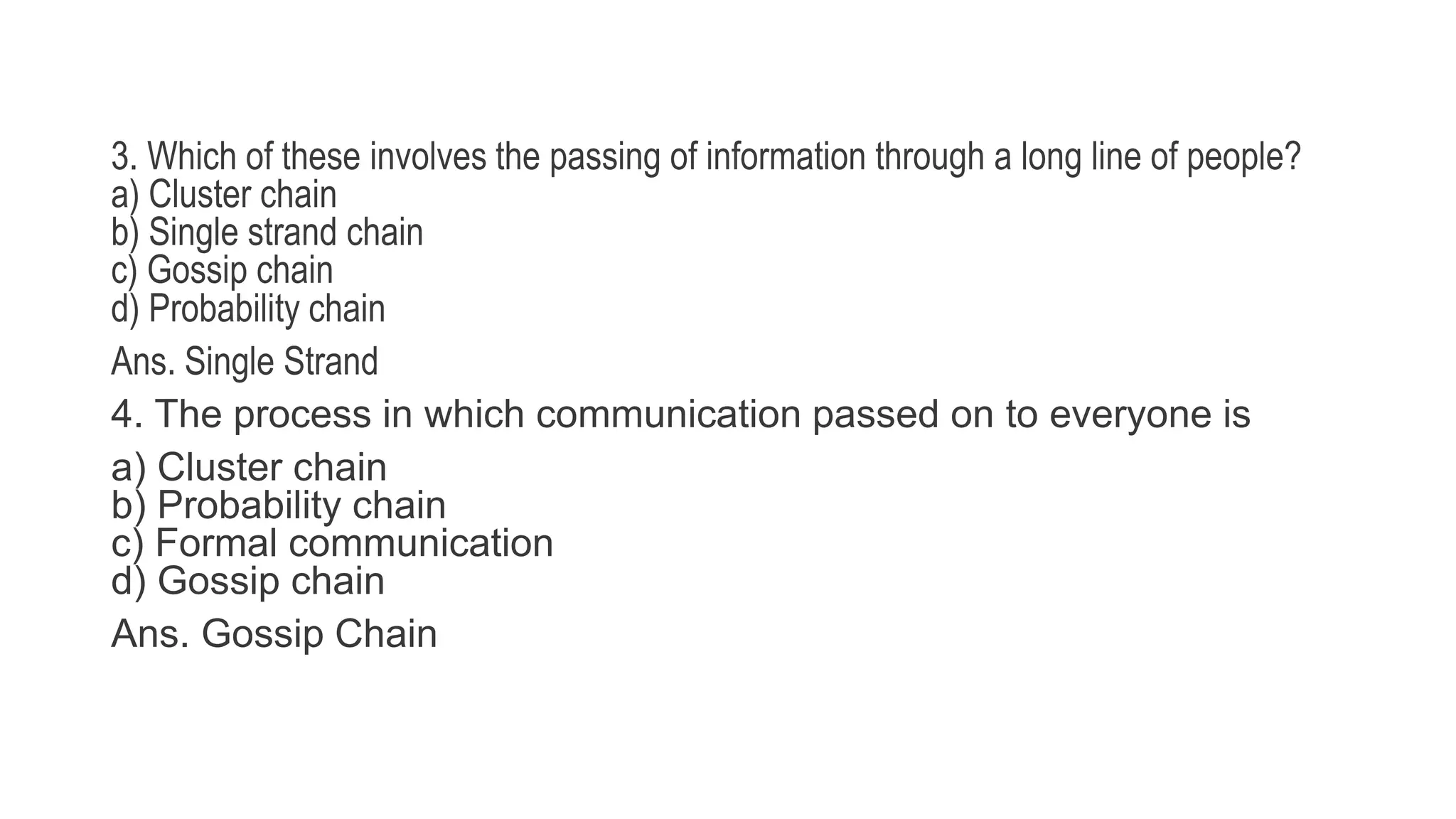
Grapevine communication is an informal way for information to spread throughout an organization. It gets its name from spreading in all directions like a grapevine. There are different types of grapevines including single strand chains, gossip chains, and probability chains. Grapevines exist because of employee emotions, informal groups, organizational environment, and atypical information sharing. While they can spread information quickly, grapevines can also distort meanings and lead to misunderstandings. Managing grapevines involves keeping staff informed through open communication and addressing issues directly.