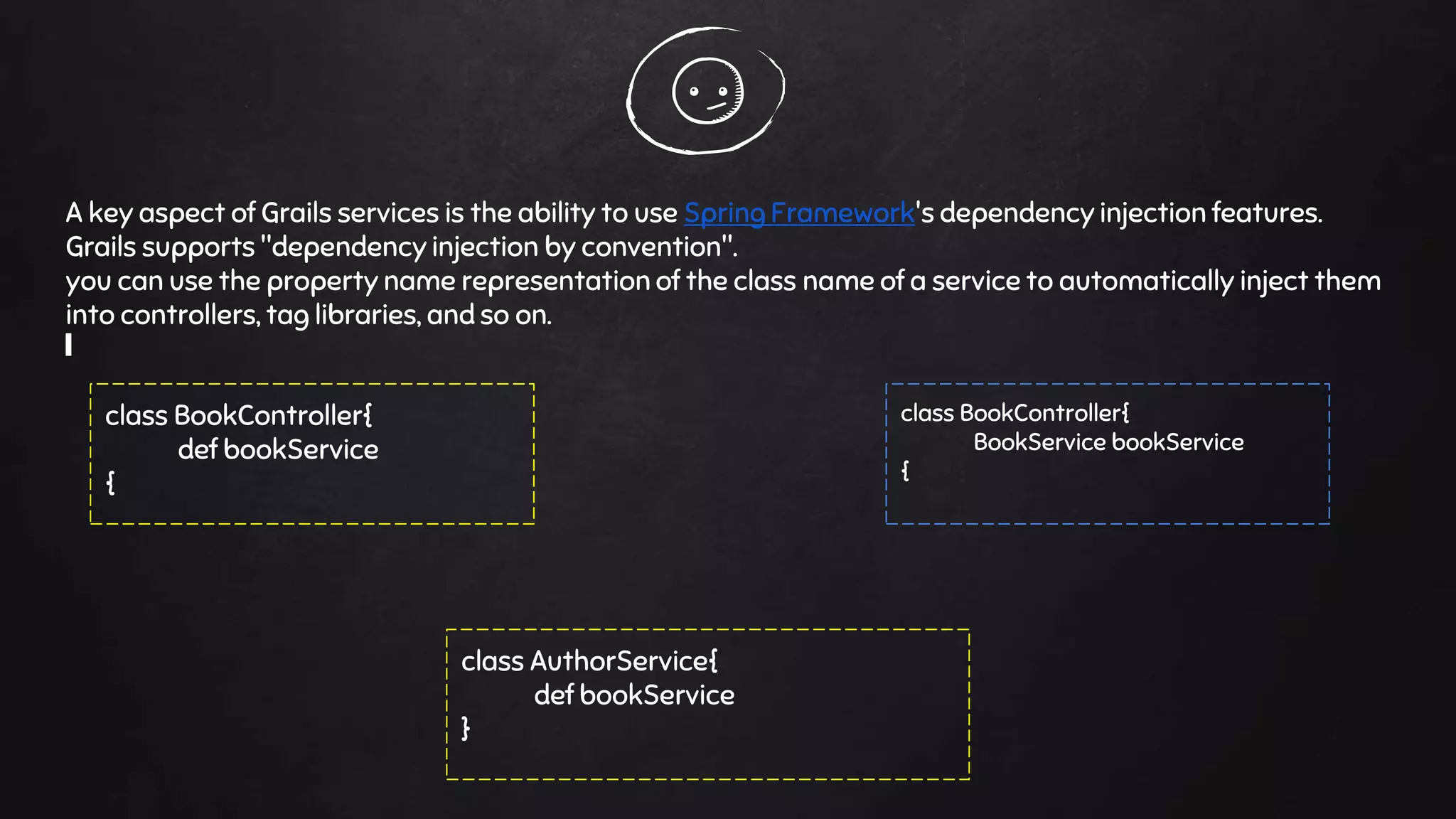
The document outlines the key concepts of Grails services, emphasizing separation of concerns, controller responsibilities, and the service layer's role in handling business logic. It explains how to create services, manage declarative transactions, and implement dependency injection. Additionally, it discusses transaction management, scoped services, and strategies to ensure data consistency during operations.









![grails create-service [package_name] [service_name]
A service's name ends with the convention Service,
other than that a service is a plain Groovy class
package com
class PublicService{
}
It will create two files:-
PublicService (Inside service folder)
PublicServiceSpec (Inside test folder)
grails create-service com Public
def publicService](https://image.slidesharecdn.com/grailsservices-160524113807/75/Grails-services-11-2048.jpg)