Gigamon Enables Cost-effective Monitoring Solution for Large Diversified Company
•
1 like•386 views
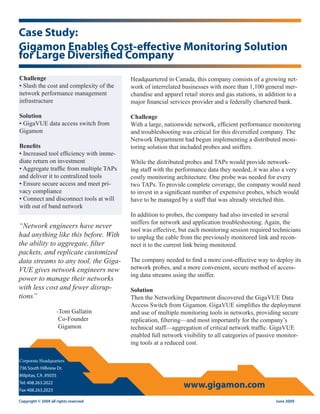
Challenge • Slash the cost and complexity of the network performance management infrastructure Solution • GigaVUE data access switch from Gigamon Benefits • Increased tool efficiency with immediate return on investment • Aggregate traffic from multiple TAPs and deliver it to centralized tools • Ensure secure access and meet privacy compliance • Connect and disconnect tools at will with out of band network
Report
Share
Report
Share
Download to read offline
Recommended
RUCKUS Technical Family Day: Migrating to RUCKUS Cloud

Ruckus Cloud: CommScope RUCKUS portfolio, positioning, pros and cons migration from ZoneDirector to RUCKUS Cloud.
During this workshop we will show you how to position Cloud next to Unleashed and SmartZone platforms, explain benefits and opportunities of moving to Cloud and demonstrate how easy migrating to RUCKUS Cloud is!
WatchGuard Integrates with CommScope RUCKUS: Full Solutions for 2021

We will be exploring the current issues on Wi-Fi security by identifying how safe is the end-user from existing and new Wi-Fi threats emerging daily, why we cannot depend on a standalone access point to detect and prevent all new threats from hackers.
Also, look into WatchGuard's solutions. How it automatically acts as an overlay on existing access points and not only provides safe Wi-Fi traffic but, also delivers unprecedented WIPS security protection that is 100% dedicated to scanning the air and protecting your business from wireless threats 24/7.
Join us as Alex Claro (Head of Technical) and Paul Summerland (Major Account Manager) - take us through the most fundamental security solutions for your access points.
5G & Edge: High Performance with Zero-Trust Security

Watch the webinar to learn more - https://www.brighttalk.com/webcast/17278/509468
CommScope RUCKUS Technical Family

Unified Management of Wi-Fi & LAN with Ruckus Unleashed and Cloud Solutions
During this webinar we covered three major technologies under unified management umbrella:
• Fast, efficient, low-latency wired infrastructure able to support most demanding customer environments.
• Cutting edge best on the market Wi-Fi including new Wi-Fi6 (802.11ax) standard that is recently gaining its market momentum and becomes available in easy to deploy,
scalable networks with robust security and unified wired and wireless management.
• Cloud Management built upon SmartZone controller and taking everything best out of it.
All this with an intuitive interface making administrative tasks fast and efficient without the complexity of typical controller-based deployments.
Telus - Network as a service

TELUS’ Network-as-as-Service (previously known as TELUS Smart Networks) a new set of services that is built on Software Defined WAN (SD-WAN) and Network Function Virtualization (NFV) technologies. When combined with process automation it transforms the way TELUS offers and provides services. NaaS is composed of three broad categories: network connectivity, on-premises capabilities such as Wi-Fi, and cloud-based value added services.
Recommended
RUCKUS Technical Family Day: Migrating to RUCKUS Cloud

Ruckus Cloud: CommScope RUCKUS portfolio, positioning, pros and cons migration from ZoneDirector to RUCKUS Cloud.
During this workshop we will show you how to position Cloud next to Unleashed and SmartZone platforms, explain benefits and opportunities of moving to Cloud and demonstrate how easy migrating to RUCKUS Cloud is!
WatchGuard Integrates with CommScope RUCKUS: Full Solutions for 2021

We will be exploring the current issues on Wi-Fi security by identifying how safe is the end-user from existing and new Wi-Fi threats emerging daily, why we cannot depend on a standalone access point to detect and prevent all new threats from hackers.
Also, look into WatchGuard's solutions. How it automatically acts as an overlay on existing access points and not only provides safe Wi-Fi traffic but, also delivers unprecedented WIPS security protection that is 100% dedicated to scanning the air and protecting your business from wireless threats 24/7.
Join us as Alex Claro (Head of Technical) and Paul Summerland (Major Account Manager) - take us through the most fundamental security solutions for your access points.
5G & Edge: High Performance with Zero-Trust Security

Watch the webinar to learn more - https://www.brighttalk.com/webcast/17278/509468
CommScope RUCKUS Technical Family

Unified Management of Wi-Fi & LAN with Ruckus Unleashed and Cloud Solutions
During this webinar we covered three major technologies under unified management umbrella:
• Fast, efficient, low-latency wired infrastructure able to support most demanding customer environments.
• Cutting edge best on the market Wi-Fi including new Wi-Fi6 (802.11ax) standard that is recently gaining its market momentum and becomes available in easy to deploy,
scalable networks with robust security and unified wired and wireless management.
• Cloud Management built upon SmartZone controller and taking everything best out of it.
All this with an intuitive interface making administrative tasks fast and efficient without the complexity of typical controller-based deployments.
Telus - Network as a service

TELUS’ Network-as-as-Service (previously known as TELUS Smart Networks) a new set of services that is built on Software Defined WAN (SD-WAN) and Network Function Virtualization (NFV) technologies. When combined with process automation it transforms the way TELUS offers and provides services. NaaS is composed of three broad categories: network connectivity, on-premises capabilities such as Wi-Fi, and cloud-based value added services.
Cambium Networks - Intro into cnPilot and cnMaestro 

cnMaestro is a powerful and free to use cloud network management platform that enables you to manage all your networks from one pane of glass. cnPilot is a uniquely positioned Wi-Fi solution providing high-specification access points at an unbelievably competitive price point. Both technologies come courtesy of Cambium Networks and we can't wait to show you all the benefits of these technologies.
This webinar is ideal for all resellers, VARs and especially MSPs where management and on-going revenue generation sits alongside providing your customers with excellent networks and support.
Harry provides an introduction to the technology, walks you through a live demonstration and then provides you with a Q&A platform. Find out what offers we can provide on these products, including extended credit terms, free APs and a three months money-back guarantee (amongst many).
Unleash the Power of 5G and Enhance Your SD-WAN Experience

Enterprises around the world are anticipating the imminent rollout of 5G connectivity as a complete solution to current network challenges. As applications and services move to the cloud, leveraging 5G provides a reliable way to stay connected and ensure mission-critical deliverables are met.
White Box Hardware Challenges in the 5G & IoT Hyperconnected Era

The development of an agile mobile network that supports a massive number of connected devices, low latencies, broadband speeds, network slicing, and edge intelligence is the result of a number of technologies that form the 5G vision. Advantech 5G Edge Servers and Universal Edge Appliances have been designed for the network edge to meet high availability network needs providing an open virtual infrastructure for seamless network transformation toward cloud native 5G architectures. From SD-WAN and private networks to virtual RAN, Central Office and Edge Cloud, Advantech is enabling the co-creation of products and services that will form the backbone of the new 5G & IoT economy.
www.advantech.com/nc/spotlight/5G
Panduit Enteprise Network Infrastructure Security Solution

Deck provides an overview of Panduit's Enterprise Network Infrastructure security solution, plus a summary of how Panduit achieved cost savings while deploying secure Enterprise solution in its own World Headquarters building. Go to http://www.panduit.com/NetKey for more information.
BSI approval and what it means for network security

The cost to a business of a cyberattack can be severe, including damage to reputation and regulatory penalties. Layer 1 encryption offers a robust and cost-efficient security solution for data in motion. But how can you be sure that a security system lives up to its claims? Discover more about BSI approval and how it guarantees the most robust and reliable transport layer encryption on the market.
Deliver the ultimate network edge protection with the ADVA FSP 150-XG118Pro (...

Our FSP 150-XG118Pro (CSH) enables business data to pass safely and seamlessly across untrusted public networks and empowers communication service providers to offer fully encrypted bandwidth services. With its enhanced MACsec encryption, the newest member of our FSP 150 programmable demarcation and edge compute portfolio, provides comprehensive security as well as precise synchronization and support for 10Gbit/s MEF 3.0 Carrier Ethernet and IP services.
Stop Doing These 5 Things with Your SD-WAN

It's time to scale way back on those support tickets from your branch users. Security shouldn’t come at the cost of performance. Register now to attend a live demo. You may be eligible to receive a free SRX!
https://www.juniper.net/sdwan-thursdays
The Enterprise Unlocked webinar

With many qualified and capable system integrators already installing Enterprise Wi-Fi, we ask if this could be extended to self-installed Enterprise Small Cells to enable rapid take-up of Small Cells while solving the issue of poor indoor coverage? We look at the business case, the technology options and the tools and capabilities required to make this happen.
Presented by David Chambers/ThinkSmallCell, Alan McNab/Cisco and Benoit Fleury/iBwave, this webinar examines these issues and discusses practical experience from the field.
After short presentations from each presenter, we answer a varied range of questions from the audience which can be listened to on the video recording linked to this slide deck.
Evolving Infrastructure and Management for Business Agility

Evolving Infrastructure and Management for Business Agility - Sukanta Biswas, Consulting Solution Architect, Infrastructure & Cloud Practice, Red Hat India
8 October 2015
Forwarding Plane Opportunities: How to Accelerate Deployment

Intel® Select Solution for NFVI Forwarding Platform (NFVI FP) is an enhanced NFVI solution for 4G or 5G core User Plane Functions (UPF), broadband use cases, such as virtual Broadband Network Gateway (vBNG), network services such as virtual Evolved Packet Core (vEPC), IPsec Gateways (vSecGW), and cable use cases such as virtual Cable Modem Termination System (vCMTS) that demand high performance and packet processing throughput. The Advantech SKY-8101D server is a verified Intel Select Solution for NFVI FP plus, base and controller node with Red Hat Enterprise Linux and Red Hat OpenStack tuned to meet a performance threshold capable of serving large numbers of subscribers thanks to a more efficient use of the infrastructure for lower TCO.
Live demo of low-latency and timing-accurate mobile x-haul based on SDN-enabl...

At ECOC 2018 in Rome, we presented a joint demo with our partners that addressed key challenges facing today’s network operators as they look to support emerging 5G use cases such as augmented reality and mission-critical communication. The showcase, which involved pioneering SDN-based Ethernet technology capable of delivering ultra-low and deterministic latency for time-sensitive mobile services, was selected by ECOC judges for as the winner of the Best Demo Award.
Pushing the boundaries of AI research

Artificial Intelligence (AI) is revolutionizing industries, products, and core capabilities by delivering dramatically enhanced experiences. However, this is just the start of the AI revolution. The field of AI, especially deep learning, is still in its infancy with tremendous opportunity for exploration and improvement. For instance, deep neural networks of today are rapidly growing in size and use too much memory, compute, and energy. To make AI truly ubiquitous, it needs to run on the end device within a tight power and thermal budget. New approaches and fundamental research in AI, as well as applying that research, is required to advance machine learning further and speed up adoption. View this presentation to learn about select research topics that Qualcomm AI Research is investigating, including:
o AI model optimization research for power efficiency, including our latest quantization research
o Applied AI research, such as using deep learning for improved radar functionality
o Fundamental AI research, such as source compression and quantum AI
40 100 gigabit ethernet for virtualized data center and campus networks

40 100 gigabit ethernet for virtualized data center and campus networks。 More...
Sled local gov pov october 2016 v2

We see the need for IT to use best of breed applications in an open standards network, but often times lacking the unified management or staff to efficiently maintain a complex network.
I am fortunate enough to speak with CIOs and IT Directors like yourself, and they tell me that while they may be happy with their current vendor situation they face challenges such as
· We help our customers transform their network architecture as a strategic business asset
· Difficult and complex to gain strategically valuable insight into network usage
· Implementing and controlling BYOD
· Increased volume of devices on the network
· Poor correlation of data and management solutions between third party technologies
· Frustration due to lack of network visibility and application analytics
· Controlling guest and rogue devices on-boarding the network
· Bad user experience causing a poor perception of IT competence
As I mentioned, I’m with Extreme Networks. We are a global leader in high performance wired and wireless networking hardware and software solutions, presently working with ABC University on their stadium wi-fi.
Ericsson Technology Review: 5G network programmability for mission-critical a...

5G will make it possible for mobile network operators to support enterprises in a wide range of industry segments by providing cellular connectivity to mission-critical applications. The ability to expose policy control to enterprise verticals will create new business opportunities for mobile network operators by enabling a new value chain through the integration of telecom with other industries.
VMworld 2013: Network Function Virtualization in the Cloud: Case for Enterpri...

VMworld 2013
Alka Gupta, VMware
Sanjay Aiyagari, VMware
Allon Dafner, Amdocs
Iain Woolf, Alcatel-Lucent
Artur Tyloch, Nokia Solutions and Networks
Learn more about VMworld and register at http://www.vmworld.com/index.jspa?src=socmed-vmworld-slideshare
Gigamon Ensures Privacy of Data in Multi-tenant Network and Enables Near Real...

Challenge
• Protect the privacy of client data in a shared network environment
• Reduce change control intervals
Solution
• GigaVUE® Data Access Switch from Gigamon
Benefits
• Ensure privacy of data among clients
• Enable near real-time response to client
requests for changes
• Eliminate port contention
• Extend life of existing lower-speed monitoring tools
Gigamon Systems Case Studies

Data Access Network (DAN) is a newly emerging "best practice" for passive monitoring of mission critical networks that solves real access problems, improves network performance and uptime, and saves capital, operation and maintenance costs. A DAN is a combination of out-of-band data access switching plus passive monitoring instrumentation to enable required security, compliance, forensics review, application performance, VoIP QoS, uptime and other network management tasks. Data is acquired from multiple SPAN ports or taps and multicast to multiple tools, aggregated to a few consolidated tools, and filtered or divided across many instances of the same tools. This Podcast recommends the DAN as a solution to those who suffer real problems like too many tools and not enough span ports, too many links to monitor and not enough money to deploy distributed tools, or too much traffic that threatens to overflow even the highest capacity tool.
More Related Content
What's hot
Cambium Networks - Intro into cnPilot and cnMaestro 

cnMaestro is a powerful and free to use cloud network management platform that enables you to manage all your networks from one pane of glass. cnPilot is a uniquely positioned Wi-Fi solution providing high-specification access points at an unbelievably competitive price point. Both technologies come courtesy of Cambium Networks and we can't wait to show you all the benefits of these technologies.
This webinar is ideal for all resellers, VARs and especially MSPs where management and on-going revenue generation sits alongside providing your customers with excellent networks and support.
Harry provides an introduction to the technology, walks you through a live demonstration and then provides you with a Q&A platform. Find out what offers we can provide on these products, including extended credit terms, free APs and a three months money-back guarantee (amongst many).
Unleash the Power of 5G and Enhance Your SD-WAN Experience

Enterprises around the world are anticipating the imminent rollout of 5G connectivity as a complete solution to current network challenges. As applications and services move to the cloud, leveraging 5G provides a reliable way to stay connected and ensure mission-critical deliverables are met.
White Box Hardware Challenges in the 5G & IoT Hyperconnected Era

The development of an agile mobile network that supports a massive number of connected devices, low latencies, broadband speeds, network slicing, and edge intelligence is the result of a number of technologies that form the 5G vision. Advantech 5G Edge Servers and Universal Edge Appliances have been designed for the network edge to meet high availability network needs providing an open virtual infrastructure for seamless network transformation toward cloud native 5G architectures. From SD-WAN and private networks to virtual RAN, Central Office and Edge Cloud, Advantech is enabling the co-creation of products and services that will form the backbone of the new 5G & IoT economy.
www.advantech.com/nc/spotlight/5G
Panduit Enteprise Network Infrastructure Security Solution

Deck provides an overview of Panduit's Enterprise Network Infrastructure security solution, plus a summary of how Panduit achieved cost savings while deploying secure Enterprise solution in its own World Headquarters building. Go to http://www.panduit.com/NetKey for more information.
BSI approval and what it means for network security

The cost to a business of a cyberattack can be severe, including damage to reputation and regulatory penalties. Layer 1 encryption offers a robust and cost-efficient security solution for data in motion. But how can you be sure that a security system lives up to its claims? Discover more about BSI approval and how it guarantees the most robust and reliable transport layer encryption on the market.
Deliver the ultimate network edge protection with the ADVA FSP 150-XG118Pro (...

Our FSP 150-XG118Pro (CSH) enables business data to pass safely and seamlessly across untrusted public networks and empowers communication service providers to offer fully encrypted bandwidth services. With its enhanced MACsec encryption, the newest member of our FSP 150 programmable demarcation and edge compute portfolio, provides comprehensive security as well as precise synchronization and support for 10Gbit/s MEF 3.0 Carrier Ethernet and IP services.
Stop Doing These 5 Things with Your SD-WAN

It's time to scale way back on those support tickets from your branch users. Security shouldn’t come at the cost of performance. Register now to attend a live demo. You may be eligible to receive a free SRX!
https://www.juniper.net/sdwan-thursdays
The Enterprise Unlocked webinar

With many qualified and capable system integrators already installing Enterprise Wi-Fi, we ask if this could be extended to self-installed Enterprise Small Cells to enable rapid take-up of Small Cells while solving the issue of poor indoor coverage? We look at the business case, the technology options and the tools and capabilities required to make this happen.
Presented by David Chambers/ThinkSmallCell, Alan McNab/Cisco and Benoit Fleury/iBwave, this webinar examines these issues and discusses practical experience from the field.
After short presentations from each presenter, we answer a varied range of questions from the audience which can be listened to on the video recording linked to this slide deck.
Evolving Infrastructure and Management for Business Agility

Evolving Infrastructure and Management for Business Agility - Sukanta Biswas, Consulting Solution Architect, Infrastructure & Cloud Practice, Red Hat India
8 October 2015
Forwarding Plane Opportunities: How to Accelerate Deployment

Intel® Select Solution for NFVI Forwarding Platform (NFVI FP) is an enhanced NFVI solution for 4G or 5G core User Plane Functions (UPF), broadband use cases, such as virtual Broadband Network Gateway (vBNG), network services such as virtual Evolved Packet Core (vEPC), IPsec Gateways (vSecGW), and cable use cases such as virtual Cable Modem Termination System (vCMTS) that demand high performance and packet processing throughput. The Advantech SKY-8101D server is a verified Intel Select Solution for NFVI FP plus, base and controller node with Red Hat Enterprise Linux and Red Hat OpenStack tuned to meet a performance threshold capable of serving large numbers of subscribers thanks to a more efficient use of the infrastructure for lower TCO.
Live demo of low-latency and timing-accurate mobile x-haul based on SDN-enabl...

At ECOC 2018 in Rome, we presented a joint demo with our partners that addressed key challenges facing today’s network operators as they look to support emerging 5G use cases such as augmented reality and mission-critical communication. The showcase, which involved pioneering SDN-based Ethernet technology capable of delivering ultra-low and deterministic latency for time-sensitive mobile services, was selected by ECOC judges for as the winner of the Best Demo Award.
Pushing the boundaries of AI research

Artificial Intelligence (AI) is revolutionizing industries, products, and core capabilities by delivering dramatically enhanced experiences. However, this is just the start of the AI revolution. The field of AI, especially deep learning, is still in its infancy with tremendous opportunity for exploration and improvement. For instance, deep neural networks of today are rapidly growing in size and use too much memory, compute, and energy. To make AI truly ubiquitous, it needs to run on the end device within a tight power and thermal budget. New approaches and fundamental research in AI, as well as applying that research, is required to advance machine learning further and speed up adoption. View this presentation to learn about select research topics that Qualcomm AI Research is investigating, including:
o AI model optimization research for power efficiency, including our latest quantization research
o Applied AI research, such as using deep learning for improved radar functionality
o Fundamental AI research, such as source compression and quantum AI
40 100 gigabit ethernet for virtualized data center and campus networks

40 100 gigabit ethernet for virtualized data center and campus networks。 More...
Sled local gov pov october 2016 v2

We see the need for IT to use best of breed applications in an open standards network, but often times lacking the unified management or staff to efficiently maintain a complex network.
I am fortunate enough to speak with CIOs and IT Directors like yourself, and they tell me that while they may be happy with their current vendor situation they face challenges such as
· We help our customers transform their network architecture as a strategic business asset
· Difficult and complex to gain strategically valuable insight into network usage
· Implementing and controlling BYOD
· Increased volume of devices on the network
· Poor correlation of data and management solutions between third party technologies
· Frustration due to lack of network visibility and application analytics
· Controlling guest and rogue devices on-boarding the network
· Bad user experience causing a poor perception of IT competence
As I mentioned, I’m with Extreme Networks. We are a global leader in high performance wired and wireless networking hardware and software solutions, presently working with ABC University on their stadium wi-fi.
Ericsson Technology Review: 5G network programmability for mission-critical a...

5G will make it possible for mobile network operators to support enterprises in a wide range of industry segments by providing cellular connectivity to mission-critical applications. The ability to expose policy control to enterprise verticals will create new business opportunities for mobile network operators by enabling a new value chain through the integration of telecom with other industries.
VMworld 2013: Network Function Virtualization in the Cloud: Case for Enterpri...

VMworld 2013
Alka Gupta, VMware
Sanjay Aiyagari, VMware
Allon Dafner, Amdocs
Iain Woolf, Alcatel-Lucent
Artur Tyloch, Nokia Solutions and Networks
Learn more about VMworld and register at http://www.vmworld.com/index.jspa?src=socmed-vmworld-slideshare
What's hot (20)
Cambium Networks - Intro into cnPilot and cnMaestro 

Cambium Networks - Intro into cnPilot and cnMaestro
93136540 spider-cloud-small-cell-cluster-case-study-091911-final

93136540 spider-cloud-small-cell-cluster-case-study-091911-final
Unleash the Power of 5G and Enhance Your SD-WAN Experience

Unleash the Power of 5G and Enhance Your SD-WAN Experience
White Box Hardware Challenges in the 5G & IoT Hyperconnected Era

White Box Hardware Challenges in the 5G & IoT Hyperconnected Era
Panduit Enteprise Network Infrastructure Security Solution

Panduit Enteprise Network Infrastructure Security Solution
BSI approval and what it means for network security

BSI approval and what it means for network security
Deliver the ultimate network edge protection with the ADVA FSP 150-XG118Pro (...

Deliver the ultimate network edge protection with the ADVA FSP 150-XG118Pro (...
ServusNet, Operational Intelligence for Renewable Energy

ServusNet, Operational Intelligence for Renewable Energy
Evolving Infrastructure and Management for Business Agility

Evolving Infrastructure and Management for Business Agility
Forwarding Plane Opportunities: How to Accelerate Deployment

Forwarding Plane Opportunities: How to Accelerate Deployment
Live demo of low-latency and timing-accurate mobile x-haul based on SDN-enabl...

Live demo of low-latency and timing-accurate mobile x-haul based on SDN-enabl...
40 100 gigabit ethernet for virtualized data center and campus networks

40 100 gigabit ethernet for virtualized data center and campus networks
Ericsson Technology Review: 5G network programmability for mission-critical a...

Ericsson Technology Review: 5G network programmability for mission-critical a...
VMworld 2013: Network Function Virtualization in the Cloud: Case for Enterpri...

VMworld 2013: Network Function Virtualization in the Cloud: Case for Enterpri...
Similar to Gigamon Enables Cost-effective Monitoring Solution for Large Diversified Company
Gigamon Ensures Privacy of Data in Multi-tenant Network and Enables Near Real...

Challenge
• Protect the privacy of client data in a shared network environment
• Reduce change control intervals
Solution
• GigaVUE® Data Access Switch from Gigamon
Benefits
• Ensure privacy of data among clients
• Enable near real-time response to client
requests for changes
• Eliminate port contention
• Extend life of existing lower-speed monitoring tools
Gigamon Systems Case Studies

Data Access Network (DAN) is a newly emerging "best practice" for passive monitoring of mission critical networks that solves real access problems, improves network performance and uptime, and saves capital, operation and maintenance costs. A DAN is a combination of out-of-band data access switching plus passive monitoring instrumentation to enable required security, compliance, forensics review, application performance, VoIP QoS, uptime and other network management tasks. Data is acquired from multiple SPAN ports or taps and multicast to multiple tools, aggregated to a few consolidated tools, and filtered or divided across many instances of the same tools. This Podcast recommends the DAN as a solution to those who suffer real problems like too many tools and not enough span ports, too many links to monitor and not enough money to deploy distributed tools, or too much traffic that threatens to overflow even the highest capacity tool.
Network Visibility Operating System Software - GigaVUE-OS Product Brief 

GigaVUE-OS is an operating system software that enables active visibility into business infrastructure on selected white box hardware and in core and edge nodes in Gigamon’s Unified Visibility Fabric™ .
Visit www.gigamon.com/products/gigavue-os-white-box to learn how enable cost effective, highly scalable network TAPs in your data center).
Democratize Observability with Software Defined Packet Brokers

These slides—based on the research webinar from leading IT research firm EMA and Pluribus Networks—dive into how software defined packet brokers can close the visibility gap on your network.
Gigamon Pervasive Visibility into SDDC/NSX Deployments

GET THE ORIGINAL: http://www.vmware.com/files/pdf/products/nsx/Gigamon-NSX-SolutionBrief.pdf
Advanced Network Traffic Intelligence with GigaSmart - Product Brief

GigaSMART combines network monitoring, line-packet filtering & modification into a single platform enabling advanced network traffic intelligence.
Visit https://www.gigamon.com/products/gigasmart to boost your network monitoring infrastructure and intelligence.
No More Global Configuration Drift: Achieved Multi-Cloud Standardization With Re

Trademo empowers customers to take critical supply chain decisions backed with deep insights, find new commercial opportunities, ensure compliance with trade regulations, and build operational supply chain resilience.
You can check more info about:
- AWS Consulting(https://opstree.com/aws-consulting-partner/).
- DevOps Consulting Company(https://opstree.com/).
-Security Service Provider(https://opstree.com/security-as-a-service/).
- Cloud Consulting Services(https://opstree.com/cloud-platform-).
A New Approach to Continuous Monitoring in the Cloud

In this #CLUS 2019 session, you will learn how NETSCOUT’s smart data platform enables continuous monitoring in hybrid cloud environments to minimize risk and accelerate customer migration to the Cloud. You will review real-life examples of how businesses optimized their Cloud migration gaining visibility and deep insights, in both physical and virtual worlds, to maintain continuity and security of the services throughout the migration process.
Simplify and secure your path to the multicloud future

Prezentace Juniper Networks z konference Virtualization Forum 2018
Clarion Congress Hotel Prague, 25.10.2018
Importance of Network Performance Monitoring

Learn the challenges of monitoring networks at high speeds and why packet brokers need real-time visibility in the network.
Alfa Banking Group enhances Network Performance Monitoring| Gigamon Case Study

How GigaVUE-420 fabric node and network visibility solutions enabled Alfa Banking Group to centralize, streamline and extend the network performance monitoring & analysis capabilities.
Visit https://www.gigamon.com/ to get the best visibility and security for your network traffic.
9th SDN Expert Group Seminar - Session1

지난 2015년 7월 9일 진행된 제9차 Korea SDN Expert Group Seminar의 발표 자료 입니다.
SnappyFlow Presentation.pdf

SnappyFlow is a full stack observability platform providing DevOps and SRE practitioners and Application Developers with a comprehensive solution bringing together metrics, logs, traces, profiling, alerts, and synthetics in a unified platform.
Visibility and Automation for Enhanced Security

Presentation from Scalar-Gigamon Roundtable, March 10th Toronto, "Visibility and Automation for Enhanced Security".
Empower Your Defense: SecurityGen's Comprehensive Approach to DDoS Attack Pre...

Empower your defense against DDoS attacks with SecurityGen's comprehensive approach to prevention. Beyond merely blocking attacks, SecurityGen focuses on understanding the unique challenges your business faces. Our DDoS Attack Prevention goes beyond traditional measures, incorporating real-time threat intelligence and behavioral analysis. By choosing SecurityGen, businesses gain a holistic defense strategy that adapts to emerging threats. With SecurityGen's comprehensive approach, organizations can confidently navigate the digital landscape, knowing that their digital assets are protected against the evolving nature of DDoS attacks.
Securing Private 5G Networks (1).pdf

Wi-Fi has been ubiquitous on Enterprise and Industrial environments. Fast evolution
a great promise in fact made some MNOs and Fixed Service Providers to build their
own “complementary” Wi-Fi networks, especially due to the high costs on 3G
deployment.
During the 4G rollout, technology evolution has tilted the scale back for MNOs, but
Wi-Fi was still the standard for enterprises. Enhanced-LTE and 5G are now
challenging this reality.
The specifications for reliability, high speed, low latency, high density, and powe
Securing Private 5G Networks (1).pdf

Wi-Fi has been ubiquitous on Enterprise and Industrial environments. Fast evolution
a great promise in fact made some MNOs and Fixed Service Providers to build their
own “complementary” Wi-Fi networks, especially due to the high costs on 3G
deployment.
During the 4G rollout, technology evolution has tilted the scale back for MNOs, but
Wi-Fi was still the standard for enterprises. Enhanced-LTE and 5G are now
challenging this reality.
The specifications for reliability, high speed, low latency, high density, and powe
IBM InterConnect 2013 Expert Integrated Systems Keynote: Sotiropoulos & Wieck

http://ibm.com/interconnect
Similar to Gigamon Enables Cost-effective Monitoring Solution for Large Diversified Company (20)
Gigamon Ensures Privacy of Data in Multi-tenant Network and Enables Near Real...

Gigamon Ensures Privacy of Data in Multi-tenant Network and Enables Near Real...
Network Visibility Operating System Software - GigaVUE-OS Product Brief 

Network Visibility Operating System Software - GigaVUE-OS Product Brief
Democratize Observability with Software Defined Packet Brokers

Democratize Observability with Software Defined Packet Brokers
Gigamon Pervasive Visibility into SDDC/NSX Deployments

Gigamon Pervasive Visibility into SDDC/NSX Deployments
Advanced Network Traffic Intelligence with GigaSmart - Product Brief

Advanced Network Traffic Intelligence with GigaSmart - Product Brief
No More Global Configuration Drift: Achieved Multi-Cloud Standardization With Re

No More Global Configuration Drift: Achieved Multi-Cloud Standardization With Re
A New Approach to Continuous Monitoring in the Cloud

A New Approach to Continuous Monitoring in the Cloud
Simplify and secure your path to the multicloud future

Simplify and secure your path to the multicloud future
Alfa Banking Group enhances Network Performance Monitoring| Gigamon Case Study

Alfa Banking Group enhances Network Performance Monitoring| Gigamon Case Study
Empower Your Defense: SecurityGen's Comprehensive Approach to DDoS Attack Pre...

Empower Your Defense: SecurityGen's Comprehensive Approach to DDoS Attack Pre...
IBM InterConnect 2013 Expert Integrated Systems Keynote: Sotiropoulos & Wieck

IBM InterConnect 2013 Expert Integrated Systems Keynote: Sotiropoulos & Wieck
More from Grant Swanson
Gigamon U - Network Rules, Distributed Network Analysis Architecture

Enterprise IT administrators at transaction and data-driven corporations deal with intricate network issues while continuing to worry about computer hacking, intellectual property theft, and complying with industry regulations. To solve these problems, administrators need the ability to capture hours, days, or even weeks worth of network traffic directly to disk for comprehensive analysis. The GigaStor provides massive data collection and a unique time-based analysis that eliminates the need to recreate problems, rapidly increasing time to resolution.
Gigamon U - Net Scouts Honor, Integrated Performance Monitoring & Forensic An...

NetScout's nGenius Application Fabric Monitor (AFMon) combines deep packet analysis and enterprise data monitoring into a single appliance specially designed to deliver high-performance and high-capacity monitoring. nGenius Application Fabric Monitor consists of nGenius Flow Record (nFR) software combined with the nGenius Common Data Model (CDM) functionality of NetScout probes. Users can now have the best of both worlds in one integrated and highly available package. AFMon is delivered on a security-hardened, Linux-based appliance that extends nGenius Flow Recorder capabilities by providing significantly higher storage capabilities (5TB and 8TB) in a high performance, highly available platform.
Gigamon U - Eye Of The Fire, Network Malware Control System

FireEye, Inc. is the leader in network malware control, dedicated to eradicating malware from the world's networks. FireEye provides the world's only malware control system designed to secure networks from targeted malware. Our solutions bring advanced network security together with state-of-the-art virtualization technology to combat crimeware and protect customer data, intellectual property and company resources, solving critical business needs without taxing your IT administration. FireEye is based in Menlo Park, CA and backed by Sequoia Capital & Norwest Venture Partners.
Gigamon U - Web Performance Monitoring

Alistair Croll, Interop conference faculty and Coradiant's VP of product management gives an unbiased, top down view of Web performance monitoring. This informative look at Web measurement business goals, operating processes, tools and metrics will give you a solid understanding of the issues, without a product pitch. Coradiant is the leader in Web Performance Monitoring. The award-winning TrueSight Real-User Monitor allows organizations to watch what matters to their business, by delivering accurate, detailed information on the performance and integrity of Web applications in real time. Incident management, service-level management and change-impact management are three key capabilities. TrueSight watches any web or enterprise web application and lets site operators identify problems more quickly, isolate root-cause faster, and effect fixes more quickly than anything else on the market.
Gigamon U - Packets Gone Wild

In every industry, real-time network monitoring and rapid troubleshooting have become mission-critical. Network disruptions are now business disruptions, with financial and sometimes even legal consequences. From the desktop to the datacenter, from wireless LANs to Gigabit backbones, on local segments and across distributed networks, WildPackets products enable IT organizations to quickly find and fix problems affecting mission-critical network services. WildPackets products are sold in over 60 countries through a broad network of channel and strategic partners. More than 5,000 customers across all industrial sectors use WildPackets products daily to troubleshoot networks and maximize network uptime.
Gigamon U - Real Time Real Clear, Real Time Solutions for Today’s Application...

ClearSight Networks is the first company to offer real time Network Analysis and Application Monitoring tools for troubleshooting today's dynamic networks. In one real time view we can show you if there is a Network, Server, Application or a User issue in a graphically rich format, supported by deep statistics and clear reports. This simple slide show will show you examples of how easy it is to see issues. The graphically rich views from ClearSight's solutions not only help you solve complex problems but also makes it easy for network personnel to understand and learn about their network and applications. ClearSight has received numerous awards for product ingenuity, ease of use, real time information and creativity.
Gigamon U - Missing Link TAP Technology

One of the most difficult challenges facing Security, VoIP, and Network Management Solutions is how to implement network tools onto enterprise networks. Enterprise networks are becoming more complex when looking at how to monitor and capture data. It can be difficult or impossible to gain access to network SPAN Ports or inserting In-line Devices like Intrusion Prevention Systems into enterprise networks. Contention for network access is a major problem. Learn how to design a network access solution that meets the requirements for security, network monitoring, and overall network access solutions. We help solve the questions, How do I get secure access to the network for capturing data or monitoring data traffic? Why TAP your network?
Gigamon U - You Will See, Content Monitoring, Alerting, and Forensic Analysis

Reconnex is the leader in information monitoring and protection appliances designed for any organization, including enterprises, government agencies or education institutions that want to protect their brands, maintain compliance, or protect sensitive information. A privately-held company based in Silicon Valley, Calif., Reconnex protects information for companies such as Cadence, WebEx Communications, The George Washington University, SIRVA and Maimonides Medical Center.
Gigamon U - Its Not The Network

Network Physics helps you defend your network against that too-familiar claim: "the network is slow!" Learn how the NP-2000 can solve your problems, without the hassle of SNMP, RMON2, agents, or synthetic transactions. The NetSensory solution operates across the most complex networks, WAN, VPN, MPLS, LAN, that delivers detailed real-time and historical information about performance, utilization, route quality, ISP performance, and end-user experience using Insight interface, a step-by-step Best Practice action guide. The result is radically simplified network troubleshooting, easier deployment of new applications and services, and reduced operating expenses.
GigamonU - Solera Blend Riches, Packet Record and Playback Appliances

Solera Networks delivers full network packet record and stream-to-disk technology to enhance security, improve network forensics, enforce compliance, and insure overall network availability. Think of it as TiVo for your network. In today's 10Gb environment, polling or sampling strategies are simply too incomplete for network management. Solera Networks' patented technology captures 100% of your network packet traffic. Unlike other solutions, our solutions can continuously stream-to-disk at unprecedented speeds (up to 6.4 Gbps), making comprehensive network recording and playback a reality. With Solera Networks' open platform you can choose which network tool to use. The Solera Networks appliance supports literally 100's of commercial, custom, and open-source applications via our virtual interface technology and live regeneration capabilities.
Data Access Network for Monitoring and Troubleshooting

The Data Access Network is a critical network infrastructure element for network monitoring and troubleshooting. Gigamon, the leading provider of intelligent data access solutions, ensures network integrity including performance, security and compliance by enabling your monitoring tools to operate at maximum efficiency.
More from Grant Swanson (11)
Gigamon U - Network Rules, Distributed Network Analysis Architecture

Gigamon U - Network Rules, Distributed Network Analysis Architecture
Gigamon U - Net Scouts Honor, Integrated Performance Monitoring & Forensic An...

Gigamon U - Net Scouts Honor, Integrated Performance Monitoring & Forensic An...
Gigamon U - Eye Of The Fire, Network Malware Control System

Gigamon U - Eye Of The Fire, Network Malware Control System
Gigamon U - Real Time Real Clear, Real Time Solutions for Today’s Application...

Gigamon U - Real Time Real Clear, Real Time Solutions for Today’s Application...
Gigamon U - You Will See, Content Monitoring, Alerting, and Forensic Analysis

Gigamon U - You Will See, Content Monitoring, Alerting, and Forensic Analysis
GigamonU - Solera Blend Riches, Packet Record and Playback Appliances

GigamonU - Solera Blend Riches, Packet Record and Playback Appliances
Data Access Network for Monitoring and Troubleshooting

Data Access Network for Monitoring and Troubleshooting
Recently uploaded
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

In this insightful webinar, Inflectra explores how artificial intelligence (AI) is transforming software development and testing. Discover how AI-powered tools are revolutionizing every stage of the software development lifecycle (SDLC), from design and prototyping to testing, deployment, and monitoring.
Learn about:
• The Future of Testing: How AI is shifting testing towards verification, analysis, and higher-level skills, while reducing repetitive tasks.
• Test Automation: How AI-powered test case generation, optimization, and self-healing tests are making testing more efficient and effective.
• Visual Testing: Explore the emerging capabilities of AI in visual testing and how it's set to revolutionize UI verification.
• Inflectra's AI Solutions: See demonstrations of Inflectra's cutting-edge AI tools like the ChatGPT plugin and Azure Open AI platform, designed to streamline your testing process.
Whether you're a developer, tester, or QA professional, this webinar will give you valuable insights into how AI is shaping the future of software delivery.
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
ODC, Data Fabric and Architecture User Group

Let's dive deeper into the world of ODC! Ricardo Alves (OutSystems) will join us to tell all about the new Data Fabric. After that, Sezen de Bruijn (OutSystems) will get into the details on how to best design a sturdy architecture within ODC.
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Recently uploaded (20)
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Gigamon Enables Cost-effective Monitoring Solution for Large Diversified Company
- 1. Case Study: Gigamon Enables Cost-effective Monitoring Solution for Large Diversified Company Challenge Headquartered in Canada, this company consists of a growing net- • Slash the cost and complexity of the work of interrelated businesses with more than 1,100 general mer- network performance management chandise and apparel retail stores and gas stations, in addition to a infrastructure major financial services provider and a federally chartered bank. Solution Challenge • GigaVUE data access switch from With a large, nationwide network, efficient performance monitoring Gigamon and troubleshooting was critical for this diversified company. The Network Department had begun implementing a distributed moni- Benefits toring solution that included probes and sniffers. • Increased tool efficiency with imme- diate return on investment While the distributed probes and TAPs would provide network- • Aggregate traffic from multiple TAPs ing staff with the performance data they needed, it was also a very and deliver it to centralized tools costly monitoring architecture. One probe was needed for every • Ensure secure access and meet pri- two TAPs. To provide complete coverage, the company would need vacy compliance to invest in a significant number of expensive probes, which would • Connect and disconnect tools at will have to be managed by a staff that was already stretched thin. with out of band network In addition to probes, the company had also invested in several sniffers for network and application troubleshooting. Again, the “Network engineers have never tool was effective, but each monitoring session required technicians had anything like this before. With to unplug the cable from the previously monitored link and recon- the ability to aggregate, filter nect it to the current link being monitored. packets, and replicate customized data streams to any tool, the Giga- The company needed to find a more cost-effective way to deploy its VUE gives network engineers new network probes, and a more convenient, secure method of access- ing data streams using the sniffer. power to manage their networks with less cost and fewer disrup- Solution tions” Then the Networking Department discovered the GigaVUE Data Access Switch from Gigamon. GigaVUE simplifies the deployment -Tom Gallatin and use of multiple monitoring tools in networks, providing secure Co-Founder replication, filtering—and most importantly for the company’s Gigamon technical staff—aggregation of critical network traffic. GigaVUE enabled full network visibility to all categories of passive monitor- ing tools at a reduced cost. Corporate Headquarters 736 South Hillview Dr. Milpitas, CA ,95035 Tel: 408.263.2022 Fax 408.263.2023 www.gigamon.com Copyright © 2009 all rights reserved June 2009
- 2. Based on initial research, the technical staff conducted a trial of the GigaVUE [2404 high-density] Data Access Switch, which proved a resounding success. The company decided to initially deploy three GigaVUE Data Access Switch- es—one for a test environment and two for the production network. Additional GigaVUE Data Access Switches are expected to be deployed in the near future. Benefits Without Gigamon, one probe was needed for every two TAPs. With Gigamon, each GigaVUE chassis aggregates data from multiple TAPs. This enables each probe to support up to 12 TAPs, reducing the number of probes required by as much as 87 percent. The company estimates a savings of $120,000—a day one return on investment. GigaVUE gives networking staff flexibility in connecting and disconnecting probes and sniffers remotely in a production environment without touching a wire or leaving their desks. The solution streamlines network operation by dramatically reducing the need for change management and scheduling mainte- nance windows. With financial data traversing the network on a regular basis, unplugging and plugging sniffers into unsecured TAP monitor ports as needed (i.e., “crash cart” troubleshooting) posed a potential security risk as well as a compliance issue. GigaVUE provides a highly secure solution that confines tools to a central- ized location with controlled access. Sniffer cables are “always connected” and specific data is selected through the GigaVUE configuration. GigaVUE has enabled this company to do more with less, reducing the cost and complexity of its network monitoring infrastructure. Simplified manage- ment has allowed staff to focus more effort on managing the network and less on managing the tools, which translates into improved network uptime, perfor- mance and higher customer satisfaction. About Gigamon Gigamon is the inventor and leading provider of Data-Access Switches. Its flagship product, GigaVUE®, can replicate packets from one span or TAP to many tools to solve the span port sharing problem. It also can aggregate and intelligently filter packets from many spans or TAPs to one or multiple tools to solve the problem of monitoring flows across complex mesh topologies and virtual networks. GigaVUE® facilitates unobtrusive parallel tool deployment with network-wide coverage, significantly reducing customers’ capital budgets. Corporate Headquarters 736 South Hillview Dr. Milpitas, CA ,95035 Tel: 408.263.2022 Fax 408.263.2023 www.gigamon.com Copyright © 2009 all rights reserved June 2009