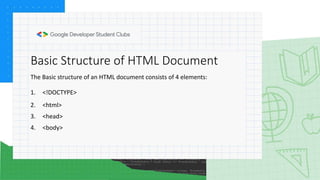
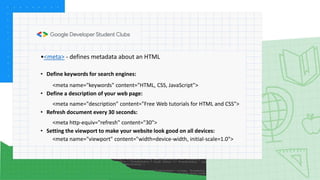
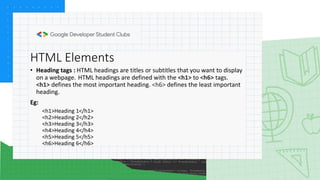
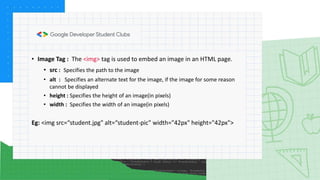
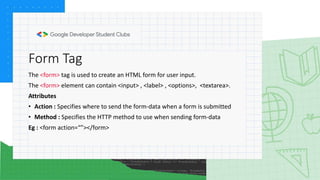
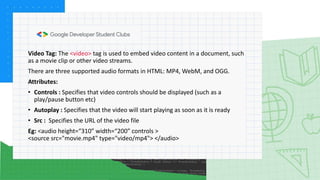
This document provides an introduction and overview of HTML (Hypertext Markup Language). It discusses key concepts like the basic structure of an HTML document which includes elements like <DOCTYPE>, <html>, <head>, and <body>. It also covers common HTML elements and tags for text formatting, links, images, lists, tables, forms, audio, video, and iframes. The document concludes with sample questions to test HTML knowledge.