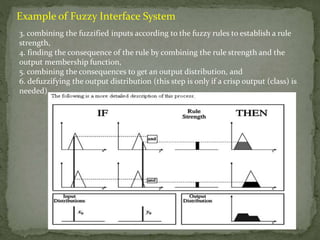
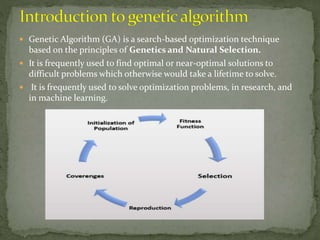
The document provides an overview of fuzzy set theory and its operations, distinguishing between crisp sets and fuzzy sets, and detailing their properties, including membership functions and fuzzy rules. It also introduces genetic algorithms as a search-based optimization technique, discussing their advantages, such as efficiency and parallel capabilities, alongside their limitations. Key concepts include fuzzy reasoning, inference systems (Mamdani and Sugeno), and the compositional rule of inference.
![ Let the universal set be denoted by X and its elements by x
i.e. X= {x}. We define a set A on X such that 𝐴 ⊂ 𝑋. We
define the term grade of membership denoted by fA(x)
which represents the information regarding the extent of
belongingness of x to set A.
If 𝑥 ∈ 𝑋, if fA(x)= 0 or 1 only and no intermediate value,
then the set A is called the crisp set and if the value of fA x
belongs to the closed interval [0, 1], then A is called the
Fuzzy set. Eg: For the set X= set of real numbers close to 1,
we have fA 0 = 0; fA 10 = 0.2; fA 500 = 1](https://image.slidesharecdn.com/fuzzysetsabsarqureshi0801it193d01-201218160346/85/Fuzzy-sets-4-320.jpg)
![ Fuzzy rules are used within fuzzy logic systems to
infer an output based on input variables. Modus
ponens and modus tollens are the most important
rules of inference.[1]A modus ponens rule is in the form
Premise: x is AImplication: IF x is A THEN y is
BConsequent: y is B
In crisp logic, the premise x is A can only be true or
false. However, in a fuzzy rule, the premise x is A and
the consequent y is B can be true to a degree, instead
of entirely true or entirely false](https://image.slidesharecdn.com/fuzzysetsabsarqureshi0801it193d01-201218160346/85/Fuzzy-sets-10-320.jpg)