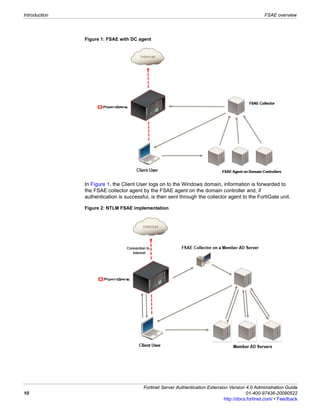
Fortinet Server Authentication Extension (FSAE) allows FortiGate units to authenticate users against Microsoft Active Directory (AD) or Novell eDirectory servers. This document provides instructions on installing and configuring FSAE components on your network, including Windows AD domain controllers, Novell agents, FortiGate units, and collector agents. It also includes directions for testing the FSAE configuration and troubleshooting.