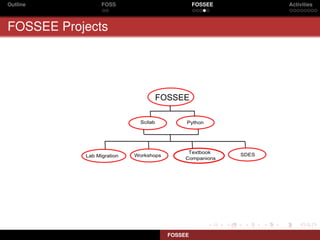
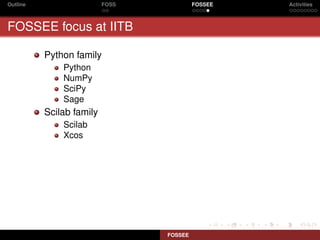
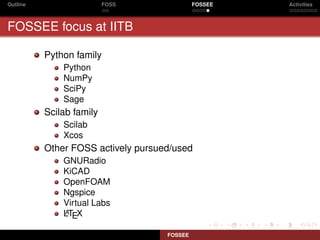
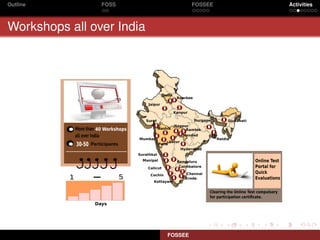
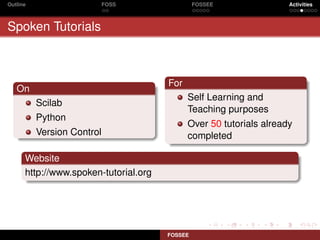
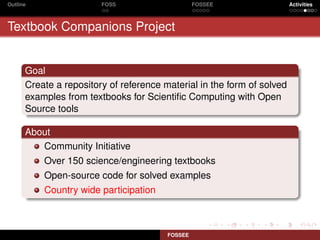
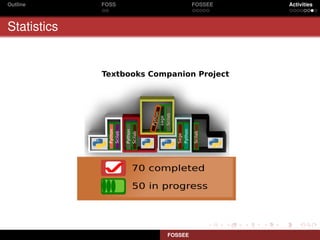
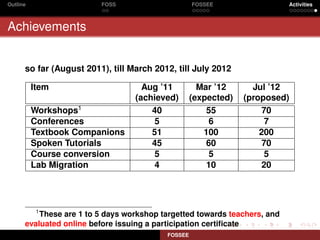
FOSSEE (Free and Open Source Software for Science and Engineering Education) is an initiative at IIT Bombay aimed at promoting the use of open-source software in education across various sectors including academic institutions and industries. The program includes activities such as workshops, spoken tutorials, and textbook companion projects to enhance the understanding and application of FOSS tools. FOSSEE is funded by the MHRD and is part of the national mission on education through ICT, focusing on reducing reliance on commercial software in scientific education.