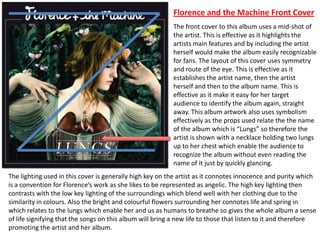
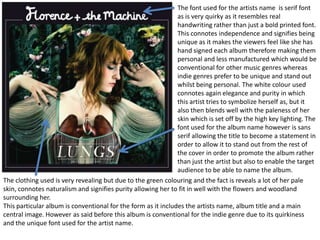
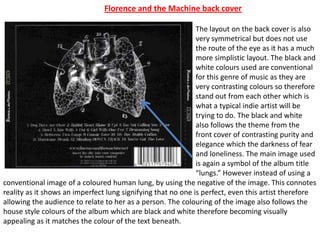
This album cover uses effective visual elements to identify the artist and album title. It features a mid-shot photo of the artist with symbolic props relating to the album name "Lungs." The layout follows conventions of the indie genre through its quirky handwritten font and symmetrical design that draws the eye to key details. Symbolism in the lighting, clothing, and background elements portray themes of innocence, purity, and new life represented in the album's songs. While conforming to standard elements like the artist name and track listing, the cover stands out through its unique visual style.