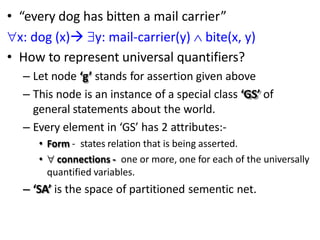
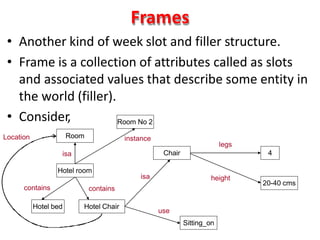
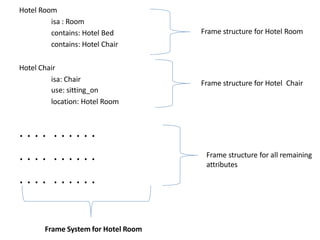
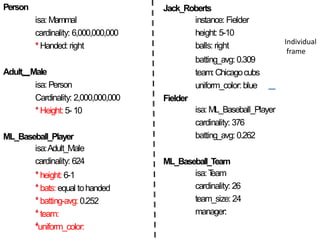
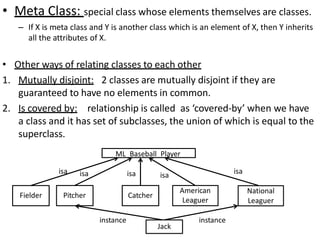
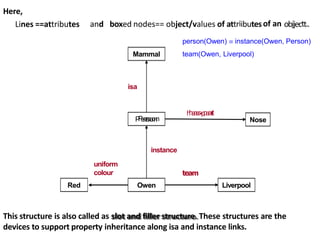
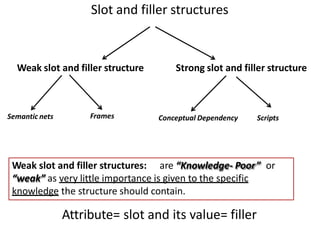
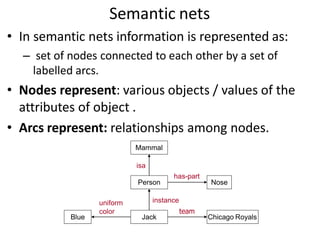
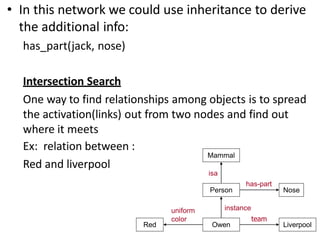
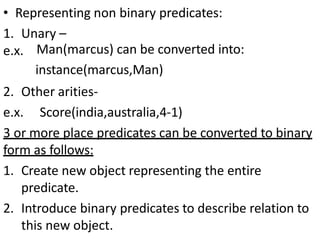
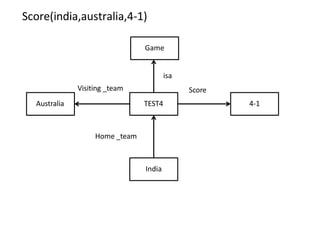
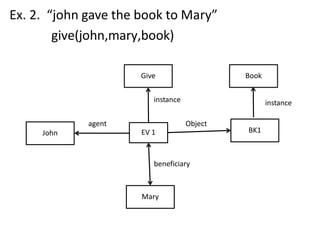
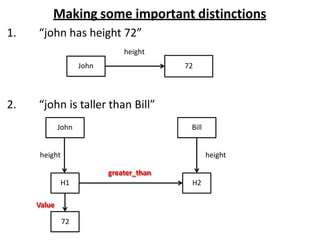
Weak slot and filler structures are knowledge representation structures that organize objects into classes with attributes and values. They allow for property inheritance along "isa" and "instance" links. Semantic nets represent information as nodes connected by labeled arcs, where nodes are objects/attribute values and arcs are relationships. Frames represent entities as collections of slots (attributes) and associated values (fillers). Frames, semantic nets, and slot-filler structures allow knowledge to be organized and property inheritance to be performed, supporting reasoning.
![Partitioned semantic nets
• Used to represent quantified expressions in
semantic nets.
• One way to do this is to partition the semantic net
into a hierarchical set of spaces each of which
corresponds to the scope of one or more variable.
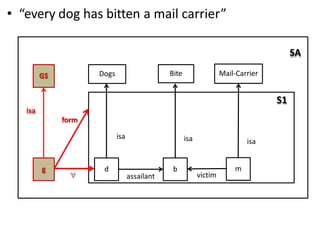
• “the dog bit the mail carrier” [partitioning not required]
d
Dogs
b
Bite
m
Mail-Carrier
isa isa isa
assailant victim](https://image.slidesharecdn.com/fillerstructures-231006031638-e5d2de31/85/filler-structures-pptx-13-320.jpg)