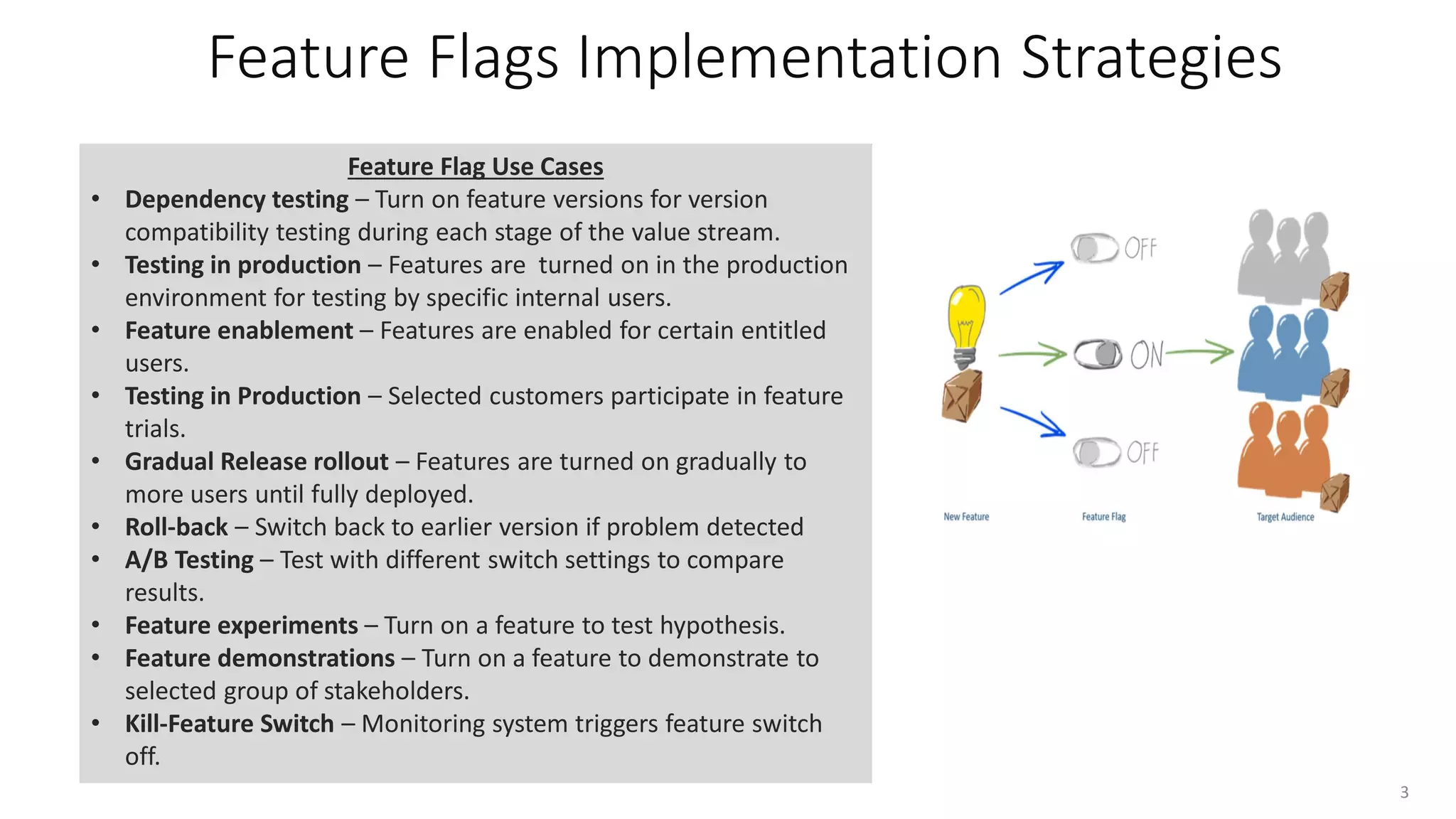
Feature flags, or feature toggles, are runtime switches that control user access to specific features without needing code deployments. They facilitate various use cases like dependency testing, gradual rollouts, and A/B testing, while supporting development pipelines and enabling monitoring. Organizations must prioritize use cases and decide between in-house and third-party solutions based on multiple factors, including usability and cost.