Facebook tutorial
•
1 like•512 views
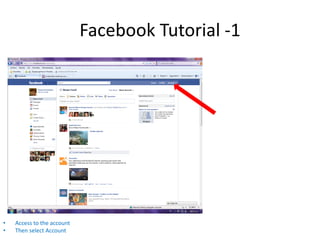
This document provides instructions for accessing and deactivating a Facebook account by first accessing the account, then selecting account settings, choosing to deactivate the account, and finally confirming the deactivation.
Report
Share
Report
Share
Download to read offline
Recommended
Conversion Tracking Tutorial

This document provides instructions for setting up conversion tracking on Facebook. It explains that conversion tracking allows you to see what actions people take on your website after seeing or clicking your Facebook ads. It then outlines how to generate a conversion tracking tag, implement the tag by copying it into your website code, and view conversion data in your reports on Facebook. The document provides examples of common conversion events that can be tracked, such as page views, purchases, and registrations.
PilotLabs IBS - Facebook analysis rankings

The document analyzes 246 Facebook pages of universities from the Netherlands, Germany and Great Britain. Criteria for evaluation included findability, user interaction, photos, videos, program/admission information, testimonials, housing, university city, and social media presence. Universities were ranked based on scores in these areas. The top university in the Netherlands was Wageningen University, which scored highly across most criteria. Smaller schools generally had less developed Facebook presences. The analysis was conducted by prospective students to reflect what information is important to this audience.
Facebook Privacy Setting Tutorial 

Hi guys, here is a tutorial about Facebook Privacy setting, hope it may help you.
Here is my video version of Facebook Privacy Tutorial on YouTube channel:
https://www.youtube.com/watch?v=GSQLJ1CL_yw
For my information, do visit my Facebook Profile:
https://www.facebook.com/karmunlee12
Facebook Usage Stats

This document contains statistics about Facebook usage broken down by gender, demographics, age, education level, and income. It shows that women use Facebook more than men, with usage rates highest among whites, younger age groups, those with at least some college education, and higher income levels. Across all categories presented, between 65-85% of US adults in each group use Facebook.
After 55 facebook_tutorial

This document provides an overview of the key features and terminology for beginners using Facebook. It explains how to sign up and set up your profile, privacy settings, and how to find and connect with friends. It also describes how to post updates on your timeline and friends' walls, and how to use notifications and messages to interact with your Facebook network. Common terms like friends, likes, news feed, and timeline are defined to help new users understand the basic functionality and vocabulary of the Facebook platform.
Facebook Tutorial

An overview of Facebook; plus, a step-by-step guide to creating an account on Facebook. http://www.queenslibrary.org/
http://www.facebook.com/queenslibrarynyc
Tutorial on Twitter

The document provides guidance for teachers and school library media specialists on using Twitter. It outlines 20 specific ways Twitter can be used, such as asking other educators for book or lesson recommendations, sharing resources and events, and promoting the school library. The document then reviews how to set up a Twitter account, create a profile, post tweets, reply to other tweets, and share links, photos and videos through other applications. The overall purpose is to demonstrate how Twitter can be harnessed to help educators connect, collaborate and promote their work.
Facebook 101 personal usage

Facebook 101 presentation for personal use. Slides do not explain all as this presentation was used with verbal accompaniment by instructor at Gulf Coast State College as part of the winter enrichment series.
Course can be offered for businesses wanting to educate their staff on how best to use social media (2-part) course. First part personal usage - second part business application.
Contact Answer Marketing for availability. 850-215-7667
Recommended
Conversion Tracking Tutorial

This document provides instructions for setting up conversion tracking on Facebook. It explains that conversion tracking allows you to see what actions people take on your website after seeing or clicking your Facebook ads. It then outlines how to generate a conversion tracking tag, implement the tag by copying it into your website code, and view conversion data in your reports on Facebook. The document provides examples of common conversion events that can be tracked, such as page views, purchases, and registrations.
PilotLabs IBS - Facebook analysis rankings

The document analyzes 246 Facebook pages of universities from the Netherlands, Germany and Great Britain. Criteria for evaluation included findability, user interaction, photos, videos, program/admission information, testimonials, housing, university city, and social media presence. Universities were ranked based on scores in these areas. The top university in the Netherlands was Wageningen University, which scored highly across most criteria. Smaller schools generally had less developed Facebook presences. The analysis was conducted by prospective students to reflect what information is important to this audience.
Facebook Privacy Setting Tutorial 

Hi guys, here is a tutorial about Facebook Privacy setting, hope it may help you.
Here is my video version of Facebook Privacy Tutorial on YouTube channel:
https://www.youtube.com/watch?v=GSQLJ1CL_yw
For my information, do visit my Facebook Profile:
https://www.facebook.com/karmunlee12
Facebook Usage Stats

This document contains statistics about Facebook usage broken down by gender, demographics, age, education level, and income. It shows that women use Facebook more than men, with usage rates highest among whites, younger age groups, those with at least some college education, and higher income levels. Across all categories presented, between 65-85% of US adults in each group use Facebook.
After 55 facebook_tutorial

This document provides an overview of the key features and terminology for beginners using Facebook. It explains how to sign up and set up your profile, privacy settings, and how to find and connect with friends. It also describes how to post updates on your timeline and friends' walls, and how to use notifications and messages to interact with your Facebook network. Common terms like friends, likes, news feed, and timeline are defined to help new users understand the basic functionality and vocabulary of the Facebook platform.
Facebook Tutorial

An overview of Facebook; plus, a step-by-step guide to creating an account on Facebook. http://www.queenslibrary.org/
http://www.facebook.com/queenslibrarynyc
Tutorial on Twitter

The document provides guidance for teachers and school library media specialists on using Twitter. It outlines 20 specific ways Twitter can be used, such as asking other educators for book or lesson recommendations, sharing resources and events, and promoting the school library. The document then reviews how to set up a Twitter account, create a profile, post tweets, reply to other tweets, and share links, photos and videos through other applications. The overall purpose is to demonstrate how Twitter can be harnessed to help educators connect, collaborate and promote their work.
Facebook 101 personal usage

Facebook 101 presentation for personal use. Slides do not explain all as this presentation was used with verbal accompaniment by instructor at Gulf Coast State College as part of the winter enrichment series.
Course can be offered for businesses wanting to educate their staff on how best to use social media (2-part) course. First part personal usage - second part business application.
Contact Answer Marketing for availability. 850-215-7667
Facebook Timeline Tutorial by Leapdog 

The changes Facebook made to business pages in March 2012 require some attention to make sure your business page is displaying optimally.
Infographic: UK social media usage - Facebook

This infographic confirms Facebook's dominant position in the UK social media arena right now. And points to why mobile will be increasingly important for the platform in future.
SocialLife is Harris Interactive's regular tracking survey offering the most comprehensive insights available on the UK social media scene. We investigate which platforms consumers have heard of, which they are signed up to, how often they use them and a lot more besides... these findings first published 19th May 2014
Facebook privacy setting

This document provides instructions for setting privacy settings on Facebook. It explains how to control who can see posts, how to review past posts and tags, how to block users, and other privacy and security settings. Key settings include choosing the privacy of posts, reviewing past activities, selecting who can find your profile, send messages or friend requests, and blocking specific users if needed. The document emphasizes setting privacy to "friends" for safety, and checking settings regularly as Facebook can change things.
Facebook Tutorial Video

This document provides instructions for three Facebook skills: blocking people, grouping friends, and changing email settings. The blocking people skill is a two step process of accessing the privacy settings and selecting people to block. The grouping friends skill involves creating lists and assigning friends to groups. The email settings skill allows customizing notifications by accessing the notifications tab and selecting notification preferences.
Tutorial on twitter in the lmc

The document discusses how school library media specialists and teachers can use Twitter. It provides 20 specific ways they can use Twitter, such as asking other librarians for book recommendations, promoting the library or classroom, and connecting with students and colleagues. It also explains how to set up a Twitter account, create a profile, tweet, reply to tweets, and share links, photos and videos on Twitter.
Facebook Privacy Settings Tutorial (2015)

Troubled by Facebook privacy settings? Here is a beginner's tutorial on how to adjust the settings according to your preference.
Click this link for video tutorial:
https://www.youtube.com/watch?v=m7Prpeu9V5A
Facebook tutorial

This document provides an introduction to using Facebook for both individuals and businesses/organizations. It explains that Facebook allows users to share information through posts containing text, audio, video, pictures or links. Both individuals and businesses/organizations can use Facebook to connect with others who have similar interests. The document then outlines the steps to sign up for an individual Facebook account or to create a Facebook page for a business/organization, and provides instructions for editing the page and making different types of posts.
Creating facebook page tutorial 2014 

Do you have a business and you don't know how to make a fan page for your business? This tutorial is for you.
Twitter tutorial

Getting started with Twitter is easy. You first need to create an account by providing a username, email address, and password. Once your account is created, you can start following other accounts, posting your own tweets of 280 characters or less, and engaging with the Twitter community. Twitter is a great way to stay connected with what's happening in the world and interact with others in a short-form, real-time manner.
Overview prolog

Prolog is a logic programming language well-suited for problems involving structured objects and relations. The document discusses how Prolog represents relations through facts and rules. Facts unconditionally declare true instances of a relation, like "parent(tom, bob)". Rules specify relations that are true if certain conditions hold, written as "head :- body". For example, the offspring relation is defined by the rule "offspring(Y, X) :- parent(X, Y)". Questions can then be asked and answered based on the defined facts and rules.
An Exploratory Study of Problematic Facebook Use Using Qualitative Methods 

This document summarizes a study that explored problematic Facebook use using qualitative methods. It defines problematic Facebook use and uses internet addiction as a theoretical basis. The study employed online surveys and focus groups to examine how problematic Facebook use compares to internet addiction. Key themes identified included preference for online social interaction, mood alteration when not on Facebook, preoccupation with Facebook, withdrawal symptoms, loss of control, and negative life consequences. The study also identified Facebook-specific issues like using it to avoid feelings of disconnection from offline social interactions.
Twitter tutorial

The document provides instructions for setting up a Twitter account and making initial posts. It outlines registering for an account by providing a name, email, and password. It then guides the user through confirming the account via email, following suggested accounts, listing interests, and importing contacts. Finally, it demonstrates how to compose and send an initial tweet by typing a message into the "what's happening" field and clicking tweet.
AthleteTrax Marketing Strategy 2015

The document outlines Athletrax's marketing strategy for 2015. It identifies strengths such as being targeted towards athletes, weaknesses like only targeting athletes and lacking a digital app, and opportunities in the growing digital app and social media spaces. Recommendations include using gamification and rewarding team members. A calendar of events is proposed for February including social media promotions, networking events, and celebrity interviews. The target market of 18-24 year olds in Pittsburgh is identified along with how Athletrax can effectively use Instagram given its popularity among that demographic.
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
Leveraging the Graph for Clinical Trials and Standards

Katja Glaß
OpenStudyBuilder Community Manager - Katja Glaß Consulting
Marius Conjeaud
Principal Consultant - Neo4j
Northern Engraving | Nameplate Manufacturing Process - 2024

Manufacturing custom quality metal nameplates and badges involves several standard operations. Processes include sheet prep, lithography, screening, coating, punch press and inspection. All decoration is completed in the flat sheet with adhesive and tooling operations following. The possibilities for creating unique durable nameplates are endless. How will you create your brand identity? We can help!
Apps Break Data

How information systems are built or acquired puts information, which is what they should be about, in a secondary place. Our language adapted accordingly, and we no longer talk about information systems but applications. Applications evolved in a way to break data into diverse fragments, tightly coupled with applications and expensive to integrate. The result is technical debt, which is re-paid by taking even bigger "loans", resulting in an ever-increasing technical debt. Software engineering and procurement practices work in sync with market forces to maintain this trend. This talk demonstrates how natural this situation is. The question is: can something be done to reverse the trend?
Dandelion Hashtable: beyond billion requests per second on a commodity server

This slide deck presents DLHT, a concurrent in-memory hashtable. Despite efforts to optimize hashtables, that go as far as sacrificing core functionality, state-of-the-art designs still incur multiple memory accesses per request and block request processing in three cases. First, most hashtables block while waiting for data to be retrieved from memory. Second, open-addressing designs, which represent the current state-of-the-art, either cannot free index slots on deletes or must block all requests to do so. Third, index resizes block every request until all objects are copied to the new index. Defying folklore wisdom, DLHT forgoes open-addressing and adopts a fully-featured and memory-aware closed-addressing design based on bounded cache-line-chaining. This design offers lock-free index operations and deletes that free slots instantly, (2) completes most requests with a single memory access, (3) utilizes software prefetching to hide memory latencies, and (4) employs a novel non-blocking and parallel resizing. In a commodity server and a memory-resident workload, DLHT surpasses 1.6B requests per second and provides 3.5x (12x) the throughput of the state-of-the-art closed-addressing (open-addressing) resizable hashtable on Gets (Deletes).
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

Tomaz Bratanic
Graph ML and GenAI Expert - Neo4j
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
A Deep Dive into ScyllaDB's Architecture

This talk will cover ScyllaDB Architecture from the cluster-level view and zoom in on data distribution and internal node architecture. In the process, we will learn the secret sauce used to get ScyllaDB's high availability and superior performance. We will also touch on the upcoming changes to ScyllaDB architecture, moving to strongly consistent metadata and tablets.
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

Direct losses from downtime in 1 minute = $5-$10 thousand dollars. Reputation is priceless.
As part of the talk, we will consider the architectural strategies necessary for the development of highly loaded fintech solutions. We will focus on using queues and streaming to efficiently work and manage large amounts of data in real-time and to minimize latency.
We will focus special attention on the architectural patterns used in the design of the fintech system, microservices and event-driven architecture, which ensure scalability, fault tolerance, and consistency of the entire system.
More Related Content
Viewers also liked
Facebook Timeline Tutorial by Leapdog 

The changes Facebook made to business pages in March 2012 require some attention to make sure your business page is displaying optimally.
Infographic: UK social media usage - Facebook

This infographic confirms Facebook's dominant position in the UK social media arena right now. And points to why mobile will be increasingly important for the platform in future.
SocialLife is Harris Interactive's regular tracking survey offering the most comprehensive insights available on the UK social media scene. We investigate which platforms consumers have heard of, which they are signed up to, how often they use them and a lot more besides... these findings first published 19th May 2014
Facebook privacy setting

This document provides instructions for setting privacy settings on Facebook. It explains how to control who can see posts, how to review past posts and tags, how to block users, and other privacy and security settings. Key settings include choosing the privacy of posts, reviewing past activities, selecting who can find your profile, send messages or friend requests, and blocking specific users if needed. The document emphasizes setting privacy to "friends" for safety, and checking settings regularly as Facebook can change things.
Facebook Tutorial Video

This document provides instructions for three Facebook skills: blocking people, grouping friends, and changing email settings. The blocking people skill is a two step process of accessing the privacy settings and selecting people to block. The grouping friends skill involves creating lists and assigning friends to groups. The email settings skill allows customizing notifications by accessing the notifications tab and selecting notification preferences.
Tutorial on twitter in the lmc

The document discusses how school library media specialists and teachers can use Twitter. It provides 20 specific ways they can use Twitter, such as asking other librarians for book recommendations, promoting the library or classroom, and connecting with students and colleagues. It also explains how to set up a Twitter account, create a profile, tweet, reply to tweets, and share links, photos and videos on Twitter.
Facebook Privacy Settings Tutorial (2015)

Troubled by Facebook privacy settings? Here is a beginner's tutorial on how to adjust the settings according to your preference.
Click this link for video tutorial:
https://www.youtube.com/watch?v=m7Prpeu9V5A
Facebook tutorial

This document provides an introduction to using Facebook for both individuals and businesses/organizations. It explains that Facebook allows users to share information through posts containing text, audio, video, pictures or links. Both individuals and businesses/organizations can use Facebook to connect with others who have similar interests. The document then outlines the steps to sign up for an individual Facebook account or to create a Facebook page for a business/organization, and provides instructions for editing the page and making different types of posts.
Creating facebook page tutorial 2014 

Do you have a business and you don't know how to make a fan page for your business? This tutorial is for you.
Twitter tutorial

Getting started with Twitter is easy. You first need to create an account by providing a username, email address, and password. Once your account is created, you can start following other accounts, posting your own tweets of 280 characters or less, and engaging with the Twitter community. Twitter is a great way to stay connected with what's happening in the world and interact with others in a short-form, real-time manner.
Overview prolog

Prolog is a logic programming language well-suited for problems involving structured objects and relations. The document discusses how Prolog represents relations through facts and rules. Facts unconditionally declare true instances of a relation, like "parent(tom, bob)". Rules specify relations that are true if certain conditions hold, written as "head :- body". For example, the offspring relation is defined by the rule "offspring(Y, X) :- parent(X, Y)". Questions can then be asked and answered based on the defined facts and rules.
An Exploratory Study of Problematic Facebook Use Using Qualitative Methods 

This document summarizes a study that explored problematic Facebook use using qualitative methods. It defines problematic Facebook use and uses internet addiction as a theoretical basis. The study employed online surveys and focus groups to examine how problematic Facebook use compares to internet addiction. Key themes identified included preference for online social interaction, mood alteration when not on Facebook, preoccupation with Facebook, withdrawal symptoms, loss of control, and negative life consequences. The study also identified Facebook-specific issues like using it to avoid feelings of disconnection from offline social interactions.
Twitter tutorial

The document provides instructions for setting up a Twitter account and making initial posts. It outlines registering for an account by providing a name, email, and password. It then guides the user through confirming the account via email, following suggested accounts, listing interests, and importing contacts. Finally, it demonstrates how to compose and send an initial tweet by typing a message into the "what's happening" field and clicking tweet.
AthleteTrax Marketing Strategy 2015

The document outlines Athletrax's marketing strategy for 2015. It identifies strengths such as being targeted towards athletes, weaknesses like only targeting athletes and lacking a digital app, and opportunities in the growing digital app and social media spaces. Recommendations include using gamification and rewarding team members. A calendar of events is proposed for February including social media promotions, networking events, and celebrity interviews. The target market of 18-24 year olds in Pittsburgh is identified along with how Athletrax can effectively use Instagram given its popularity among that demographic.
Viewers also liked (13)
An Exploratory Study of Problematic Facebook Use Using Qualitative Methods 

An Exploratory Study of Problematic Facebook Use Using Qualitative Methods
Recently uploaded
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
Leveraging the Graph for Clinical Trials and Standards

Katja Glaß
OpenStudyBuilder Community Manager - Katja Glaß Consulting
Marius Conjeaud
Principal Consultant - Neo4j
Northern Engraving | Nameplate Manufacturing Process - 2024

Manufacturing custom quality metal nameplates and badges involves several standard operations. Processes include sheet prep, lithography, screening, coating, punch press and inspection. All decoration is completed in the flat sheet with adhesive and tooling operations following. The possibilities for creating unique durable nameplates are endless. How will you create your brand identity? We can help!
Apps Break Data

How information systems are built or acquired puts information, which is what they should be about, in a secondary place. Our language adapted accordingly, and we no longer talk about information systems but applications. Applications evolved in a way to break data into diverse fragments, tightly coupled with applications and expensive to integrate. The result is technical debt, which is re-paid by taking even bigger "loans", resulting in an ever-increasing technical debt. Software engineering and procurement practices work in sync with market forces to maintain this trend. This talk demonstrates how natural this situation is. The question is: can something be done to reverse the trend?
Dandelion Hashtable: beyond billion requests per second on a commodity server

This slide deck presents DLHT, a concurrent in-memory hashtable. Despite efforts to optimize hashtables, that go as far as sacrificing core functionality, state-of-the-art designs still incur multiple memory accesses per request and block request processing in three cases. First, most hashtables block while waiting for data to be retrieved from memory. Second, open-addressing designs, which represent the current state-of-the-art, either cannot free index slots on deletes or must block all requests to do so. Third, index resizes block every request until all objects are copied to the new index. Defying folklore wisdom, DLHT forgoes open-addressing and adopts a fully-featured and memory-aware closed-addressing design based on bounded cache-line-chaining. This design offers lock-free index operations and deletes that free slots instantly, (2) completes most requests with a single memory access, (3) utilizes software prefetching to hide memory latencies, and (4) employs a novel non-blocking and parallel resizing. In a commodity server and a memory-resident workload, DLHT surpasses 1.6B requests per second and provides 3.5x (12x) the throughput of the state-of-the-art closed-addressing (open-addressing) resizable hashtable on Gets (Deletes).
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

Tomaz Bratanic
Graph ML and GenAI Expert - Neo4j
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
A Deep Dive into ScyllaDB's Architecture

This talk will cover ScyllaDB Architecture from the cluster-level view and zoom in on data distribution and internal node architecture. In the process, we will learn the secret sauce used to get ScyllaDB's high availability and superior performance. We will also touch on the upcoming changes to ScyllaDB architecture, moving to strongly consistent metadata and tablets.
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

Direct losses from downtime in 1 minute = $5-$10 thousand dollars. Reputation is priceless.
As part of the talk, we will consider the architectural strategies necessary for the development of highly loaded fintech solutions. We will focus on using queues and streaming to efficiently work and manage large amounts of data in real-time and to minimize latency.
We will focus special attention on the architectural patterns used in the design of the fintech system, microservices and event-driven architecture, which ensure scalability, fault tolerance, and consistency of the entire system.
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Essentials of Automations: Exploring Attributes & Automation Parameters

Building automations in FME Flow can save time, money, and help businesses scale by eliminating data silos and providing data to stakeholders in real-time. One essential component to orchestrating complex automations is the use of attributes & automation parameters (both formerly known as “keys”). In fact, it’s unlikely you’ll ever build an Automation without using these components, but what exactly are they?
Attributes & automation parameters enable the automation author to pass data values from one automation component to the next. During this webinar, our FME Flow Specialists will cover leveraging the three types of these output attributes & parameters in FME Flow: Event, Custom, and Automation. As a bonus, they’ll also be making use of the Split-Merge Block functionality.
You’ll leave this webinar with a better understanding of how to maximize the potential of automations by making use of attributes & automation parameters, with the ultimate goal of setting your enterprise integration workflows up on autopilot.
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
AppSec PNW: Android and iOS Application Security with MobSF

Mobile Security Framework - MobSF is a free and open source automated mobile application security testing environment designed to help security engineers, researchers, developers, and penetration testers to identify security vulnerabilities, malicious behaviours and privacy concerns in mobile applications using static and dynamic analysis. It supports all the popular mobile application binaries and source code formats built for Android and iOS devices. In addition to automated security assessment, it also offers an interactive testing environment to build and execute scenario based test/fuzz cases against the application.
This talk covers:
Using MobSF for static analysis of mobile applications.
Interactive dynamic security assessment of Android and iOS applications.
Solving Mobile app CTF challenges.
Reverse engineering and runtime analysis of Mobile malware.
How to shift left and integrate MobSF/mobsfscan SAST and DAST in your build pipeline.
Must Know Postgres Extension for DBA and Developer during Migration

Mydbops Opensource Database Meetup 16
Topic: Must-Know PostgreSQL Extensions for Developers and DBAs During Migration
Speaker: Deepak Mahto, Founder of DataCloudGaze Consulting
Date & Time: 8th June | 10 AM - 1 PM IST
Venue: Bangalore International Centre, Bangalore
Abstract: Discover how PostgreSQL extensions can be your secret weapon! This talk explores how key extensions enhance database capabilities and streamline the migration process for users moving from other relational databases like Oracle.
Key Takeaways:
* Learn about crucial extensions like oracle_fdw, pgtt, and pg_audit that ease migration complexities.
* Gain valuable strategies for implementing these extensions in PostgreSQL to achieve license freedom.
* Discover how these key extensions can empower both developers and DBAs during the migration process.
* Don't miss this chance to gain practical knowledge from an industry expert and stay updated on the latest open-source database trends.
Mydbops Managed Services specializes in taking the pain out of database management while optimizing performance. Since 2015, we have been providing top-notch support and assistance for the top three open-source databases: MySQL, MongoDB, and PostgreSQL.
Our team offers a wide range of services, including assistance, support, consulting, 24/7 operations, and expertise in all relevant technologies. We help organizations improve their database's performance, scalability, efficiency, and availability.
Contact us: info@mydbops.com
Visit: https://www.mydbops.com/
Follow us on LinkedIn: https://in.linkedin.com/company/mydbops
For more details and updates, please follow up the below links.
Meetup Page : https://www.meetup.com/mydbops-databa...
Twitter: https://twitter.com/mydbopsofficial
Blogs: https://www.mydbops.com/blog/
Facebook(Meta): https://www.facebook.com/mydbops/
LF Energy Webinar: Carbon Data Specifications: Mechanisms to Improve Data Acc...

This LF Energy webinar took place June 20, 2024. It featured:
-Alex Thornton, LF Energy
-Hallie Cramer, Google
-Daniel Roesler, UtilityAPI
-Henry Richardson, WattTime
In response to the urgency and scale required to effectively address climate change, open source solutions offer significant potential for driving innovation and progress. Currently, there is a growing demand for standardization and interoperability in energy data and modeling. Open source standards and specifications within the energy sector can also alleviate challenges associated with data fragmentation, transparency, and accessibility. At the same time, it is crucial to consider privacy and security concerns throughout the development of open source platforms.
This webinar will delve into the motivations behind establishing LF Energy’s Carbon Data Specification Consortium. It will provide an overview of the draft specifications and the ongoing progress made by the respective working groups.
Three primary specifications will be discussed:
-Discovery and client registration, emphasizing transparent processes and secure and private access
-Customer data, centering around customer tariffs, bills, energy usage, and full consumption disclosure
-Power systems data, focusing on grid data, inclusive of transmission and distribution networks, generation, intergrid power flows, and market settlement data
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Demystifying Knowledge Management through Storytelling

The Department of Veteran Affairs (VA) invited Taylor Paschal, Knowledge & Information Management Consultant at Enterprise Knowledge, to speak at a Knowledge Management Lunch and Learn hosted on June 12, 2024. All Office of Administration staff were invited to attend and received professional development credit for participating in the voluntary event.
The objectives of the Lunch and Learn presentation were to:
- Review what KM ‘is’ and ‘isn’t’
- Understand the value of KM and the benefits of engaging
- Define and reflect on your “what’s in it for me?”
- Share actionable ways you can participate in Knowledge - - Capture & Transfer
Session 1 - Intro to Robotic Process Automation.pdf

👉 Check out our full 'Africa Series - Automation Student Developers (EN)' page to register for the full program:
https://bit.ly/Automation_Student_Kickstart
In this session, we shall introduce you to the world of automation, the UiPath Platform, and guide you on how to install and setup UiPath Studio on your Windows PC.
📕 Detailed agenda:
What is RPA? Benefits of RPA?
RPA Applications
The UiPath End-to-End Automation Platform
UiPath Studio CE Installation and Setup
💻 Extra training through UiPath Academy:
Introduction to Automation
UiPath Business Automation Platform
Explore automation development with UiPath Studio
👉 Register here for our upcoming Session 2 on June 20: Introduction to UiPath Studio Fundamentals: https://community.uipath.com/events/details/uipath-lagos-presents-session-2-introduction-to-uipath-studio-fundamentals/
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks creates AI-boosted business software that helps employees work more efficiently and effectively. Managing data across multiple RDBMS and NoSQL databases was already a challenge at their current scale. To prepare for 10X growth, they knew it was time to rethink their database strategy. Learn how they architected a solution that would simplify scaling while keeping costs under control.
Recently uploaded (20)
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...
Leveraging the Graph for Clinical Trials and Standards

Leveraging the Graph for Clinical Trials and Standards
Northern Engraving | Nameplate Manufacturing Process - 2024

Northern Engraving | Nameplate Manufacturing Process - 2024
Dandelion Hashtable: beyond billion requests per second on a commodity server

Dandelion Hashtable: beyond billion requests per second on a commodity server
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph
"$10 thousand per minute of downtime: architecture, queues, streaming and fin...

"$10 thousand per minute of downtime: architecture, queues, streaming and fin...
Essentials of Automations: Exploring Attributes & Automation Parameters

Essentials of Automations: Exploring Attributes & Automation Parameters
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
AppSec PNW: Android and iOS Application Security with MobSF

AppSec PNW: Android and iOS Application Security with MobSF
Must Know Postgres Extension for DBA and Developer during Migration

Must Know Postgres Extension for DBA and Developer during Migration
LF Energy Webinar: Carbon Data Specifications: Mechanisms to Improve Data Acc...

LF Energy Webinar: Carbon Data Specifications: Mechanisms to Improve Data Acc...
Demystifying Knowledge Management through Storytelling

Demystifying Knowledge Management through Storytelling
Session 1 - Intro to Robotic Process Automation.pdf

Session 1 - Intro to Robotic Process Automation.pdf
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency
Facebook tutorial
- 1. Facebook Tutorial -1 • Access to the account • Then select Account
- 2. Facebook Tutorial -2 • Then select Account • Selec Account Settings
- 3. Facebook Tutorial -3 • Select Deactivate Account
- 4. Facebook Tutorial -4 • Answer the reason of leaving • Confirm